Professional Documents
Culture Documents
File System: Faculty of Computer Science & Engineering
Uploaded by
DongOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
File System: Faculty of Computer Science & Engineering
Uploaded by
DongCopyright:
Available Formats
Chapter 11
FILE SYSTEM
BK
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 1
Chapter’s Content
File Concept
Access Methods
Directory Structure
File System Mounting
File Sharing
Protection
BK
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 2
File Concept
File with a name is a collection of related
information on secondary storage
A smallest portion of logical storage.
Contiguous logical address space
Types of information in a file:
Data
numeric
character
binary
Program
BK
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 3
File Attributes
Name – only information kept in human-readable
form.
Type – needed for systems that support different
types.
Location – pointer to file location on device.
Size – current file size.
Protection – controls who can do reading, writing,
executing.
Time, date, and user identification – data for
protection, security, and usage monitoring.
Information about files are kept in the directory
structure, which is maintained on the disk.
BK
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 4
File Operations
A file is an abstract data type, so that operations
can be done on file:
Create: search for space; new entry for the file
Write: file name; file write pointer
Read : file name; file read pointer
Reposition within file – file seek
Delete
Truncate: erase the content of file.
Open(Fi) – search the directory structure on disk
for entry Fi, and move the content of entry to
memory.
Close (Fi) – move the content of entry Fi in memory
BK
to directory structure on disk.
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 5
File Types – Name, Extension
BK
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 6
File Structure
None - sequence of words, bytes
Simple record structure
Lines
Fixed length
Variable length
Complex Structures
Formatted document
Relocatable load file
Can simulate last two with first method by inserting
appropriate control characters.
Who decides:
Operating system
Program
BK
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 7
Access Methods
Sequential Access
read next
write next
reset
no read after last write
(rewrite)
Direct Access
read n
write n
position to n
read next
write next
rewrite n
n = relative block number
BK
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 8
Sequential-access File
BK
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 9
Simulation of Sequential Access
on a Direct-access File
BK
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 10
Other Access Methods
Example of Index and Relative Files
BK
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 11
Directory Structure
A collection of nodes containing information about all
files.
Directory
Files
F1 F2 F4
F3
Fn
Both the directory structure and the files reside on disk.
BK
Backups of these two structures are kept on tapes.
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 12
A Typical File-system Organization
BK
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 13
Information in a Device Directory
Name
Type
Address
Current length
Maximum length
Date last accessed (for archival)
Date last updated (for dump)
Owner ID (who pays)
Protection information (discuss later)
BK
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 14
Operations Performed on Directory
Search for a file
Create a file
Delete a file
List a directory
Rename a file
Traverse the file system
BK
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 15
Main Purpose of File Directory
Efficiency – locating a file quickly.
Naming – convenient to users.
Two users can have same name for
different files.
The same file can have several different
names.
Grouping – logical grouping of files by
properties, (e.g., all Java programs, all
games, …)
BK
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 16
Single-Level Directory
A single directory for all users.
Naming problem
Grouping problem
BK
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 17
Two-Level Directory
Separate directory for each user.
•Path name
•Can have the same file name for different user
•Efficient searching
•No grouping capability
BK
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 18
Tree-Structured Directories
BK
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 19
Tree-Structured Directories (Cont.)
Efficient searching
Grouping Capability
Current directory (working directory)
cd /spell/mail/prog
type list
BK
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 20
Tree-Structured Directories (Cont.)
Absolute or relative path name
Creating a new file is done in current mail
directory.
Delete a file prog copy prt exp count
rm <file-name>
Creating a new subdirectory is done
in current directory. Deleting “mail”
mkdir <dir-name> deleting the entire
subtree rooted by “mail”.
Example: if in current directory
/mail
mkdir count
BK
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 21
Acyclic-Graph Directories
Have shared subdirectories and files.
BK
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 22
Acyclic-Graph Directories (Cont.)
Two different names (aliasing)
If dict deletes list dangling pointer.
Solutions:
Backpointers, so we can delete all pointers.
Variable size records a problem.
Backpointers using a daisy chain
organization.
Entry-hold-count solution.
BK
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 23
General Graph Directory
BK
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 24
General Graph Directory (Cont.)
How do we guarantee no cycles?
Allow only links to file not subdirectories.
Garbage collection.
Every time a new link is added use a cycle
detection
algorithm to determine whether it is OK.
BK
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 25
File System Mounting
A file system must
be mounted before
it can be accessed.
A unmounted file
system (I.e. Fig. 11-
11(b)) is mounted
at a mount point.
BK (a) Existing. (b) Unmounted Partition
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 26
Mount Point
BK
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 27
File Sharing
Sharing of files on multi-user systems is
desirable.
Sharing may be done through a
protection scheme.
On distributed systems, files may be
shared across a network.
Network File System (NFS) is a common
distributed file-sharing method.
BK
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 28
Protection
File owner/creator should be able to control:
what can be done
by whom
Types of access
Read
Write
Execute
Append
Delete
List
BK
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 29
Access Lists and Groups
Mode of access: read, write, execute
Three classes of users
RWX
a) owner access 7 111
RWX
b) group access 6 110
RWX
c) public access 1 001
Ask manager to create a group (unique name), say G,
and add some users to the group.
For a particular file (say game) or subdirectory, define
an appropriate access.
owner group public
chmod 761 game
Attach a group to a file
chgrp G game
BK
TP.HCM
5/9/2019 Faculty of Computer Science & Engineering 30
You might also like
- Lab 11 Fa10Document2 pagesLab 11 Fa10MazMoh50% (2)
- File System: Faculty of Computer Science & EngineeringDocument30 pagesFile System: Faculty of Computer Science & EngineeringTân Đinh NhưNo ratings yet
- Chapter Five C#Document30 pagesChapter Five C#Gofere TubeNo ratings yet
- Module-1 Introduction To File StructuresDocument50 pagesModule-1 Introduction To File StructuresVarshitha GanigaNo ratings yet
- Programming Techniques: Binary File I/ODocument20 pagesProgramming Techniques: Binary File I/OPhước Nguyên HoàngNo ratings yet
- Operating Systems: Syed Mansoor SarwarDocument27 pagesOperating Systems: Syed Mansoor SarwarIbrahim ChoudaryNo ratings yet
- File Organization and Processing Lecture 1Document45 pagesFile Organization and Processing Lecture 1Mohamed AliNo ratings yet
- Ch9 FilesystemsDocument52 pagesCh9 FilesystemsKevin MhutsiwaNo ratings yet
- Linux File Systems and Structure ExplainedDocument16 pagesLinux File Systems and Structure ExplainedRDxR10No ratings yet
- OS Unit - 5 NotesDocument34 pagesOS Unit - 5 NoteshahahaNo ratings yet
- L E C T U R E: Windows Server 2022: Understanding Active DirectoryDocument24 pagesL E C T U R E: Windows Server 2022: Understanding Active Directoryjunxiong13022005No ratings yet
- M 317: Operating Systems: OutlineDocument26 pagesM 317: Operating Systems: OutlineMomen abd ElrazekNo ratings yet
- Lesson 2-4 File Processing2 Fundamental File Processing Operations.Document31 pagesLesson 2-4 File Processing2 Fundamental File Processing Operations.Russel PonferradaNo ratings yet
- Lab Manual 10Document2 pagesLab Manual 10VERMA JINo ratings yet
- UnixEditionZero-reset TroffDocument26 pagesUnixEditionZero-reset TrofftertohertoNo ratings yet
- Chapter 8Document30 pagesChapter 8KaranNo ratings yet
- Benchmarking Performance of EXT4, XFS and BTRFS as Guest File SystemsDocument6 pagesBenchmarking Performance of EXT4, XFS and BTRFS as Guest File Systemskastevifyo vusraNo ratings yet
- CH 10Document41 pagesCH 10Rohit PaulNo ratings yet
- File - Google SearchDocument3 pagesFile - Google SearchTemp2020No ratings yet
- Operating System Lab 2: Linux Overview and Shell CommandsDocument34 pagesOperating System Lab 2: Linux Overview and Shell CommandsAmna SumbalNo ratings yet
- CS3307 PA Unit5 PDFDocument6 pagesCS3307 PA Unit5 PDFstudyjunkyNo ratings yet
- Second Term ss 2 file organization comparisonDocument18 pagesSecond Term ss 2 file organization comparisonangus ogwucheNo ratings yet
- Ebook C For Engineers and Scientists 4Th Edition Bronson Solutions Manual Full Chapter PDFDocument31 pagesEbook C For Engineers and Scientists 4Th Edition Bronson Solutions Manual Full Chapter PDFShannonRussellapcx100% (10)
- Chap 13 1Document25 pagesChap 13 1RadhikaNo ratings yet
- Unit IV Fundamental File Processing Unit IV Fundamental File Processing OperationsDocument39 pagesUnit IV Fundamental File Processing Unit IV Fundamental File Processing Operationsduvvuru familyNo ratings yet
- Object-Based Storage: IEEE Communications Magazine September 2003Document8 pagesObject-Based Storage: IEEE Communications Magazine September 2003Sachi N NerkarNo ratings yet
- A Review of Bioinformatic Pipeline FrameworksDocument7 pagesA Review of Bioinformatic Pipeline FrameworksVictor WolleckNo ratings yet
- C8 File ManagementDocument28 pagesC8 File ManagementBÁCH LÊNo ratings yet
- PL1 Lecture 09Document30 pagesPL1 Lecture 09mustfa khedrNo ratings yet
- OS - 2mark and 16 Mark (Unit-IV)Document6 pagesOS - 2mark and 16 Mark (Unit-IV)Kartheeban KamatchiNo ratings yet
- 7 A Taxonomy and Survey On Distributed File SystemsDocument6 pages7 A Taxonomy and Survey On Distributed File SystemsvikasbhowateNo ratings yet
- Here You'll Get: - PPT - Notes - Video Lecture - Ebook - Pyq - Experiment - Assignment - TutorialDocument27 pagesHere You'll Get: - PPT - Notes - Video Lecture - Ebook - Pyq - Experiment - Assignment - TutorialShrikant NavaleNo ratings yet
- File Management SystemDocument12 pagesFile Management SystemChair wazirNo ratings yet
- Os Lesson 3 File ManagementDocument9 pagesOs Lesson 3 File Managementmichellegichuhi94No ratings yet
- CH 101Document28 pagesCH 101younas125No ratings yet
- Distributed Data Systems ArchitectureDocument50 pagesDistributed Data Systems ArchitectureHome TVNo ratings yet
- File Structures and Operations GuideDocument41 pagesFile Structures and Operations GuideRaghuRamMullapudi100% (1)
- The Hideous Name - 1985 (Pike85hideous)Document8 pagesThe Hideous Name - 1985 (Pike85hideous)alastoridNo ratings yet
- C# Unit 2Document81 pagesC# Unit 2Sheraz Jabeen NNo ratings yet
- PDFX: Fully-Automated PDF-to-XML Conversion of Scientific LiteratureDocument4 pagesPDFX: Fully-Automated PDF-to-XML Conversion of Scientific LiteratureMike ReyesNo ratings yet
- The Ubiquitous B-Tree: Computer Sctence Department, Purdue Untverstty, West Lafayette, Indiana 47907Document17 pagesThe Ubiquitous B-Tree: Computer Sctence Department, Purdue Untverstty, West Lafayette, Indiana 47907Amith LankesarNo ratings yet
- Case Study Topic NameDocument23 pagesCase Study Topic NameV snehaNo ratings yet
- Lec9 CS604 PpsDocument30 pagesLec9 CS604 PpsIbrahim ChoudaryNo ratings yet
- Why Database?: Data Hierarchy File and File Systems and Their Problems An Overview of Database ModelsDocument23 pagesWhy Database?: Data Hierarchy File and File Systems and Their Problems An Overview of Database Modelsho kakitNo ratings yet
- C++ BasicsDocument10 pagesC++ BasicsBrainz on MobNo ratings yet
- Ss 2 Data Processing Second Term E-NoteDocument40 pagesSs 2 Data Processing Second Term E-NoteJesseNo ratings yet
- Chapter-11& 12 File SystemDocument52 pagesChapter-11& 12 File SystemKarthik KaranthNo ratings yet
- Lecture 7: Storage Management File System ManagementDocument37 pagesLecture 7: Storage Management File System ManagementvinayNo ratings yet
- Chapter XXDocument63 pagesChapter XXSam VNo ratings yet
- File Input and OutputDocument2 pagesFile Input and OutputMark Ven LambotNo ratings yet
- Case Study On BTRFS: A Fault Tolerant File SystemDocument6 pagesCase Study On BTRFS: A Fault Tolerant File Systemamit4gNo ratings yet
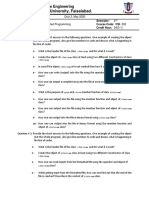
- Government College University, Faisalabad.: Department of Software EngineeringDocument3 pagesGovernment College University, Faisalabad.: Department of Software Engineeringawais mianNo ratings yet
- File Management: Inquiry & Thinking /21 Communication /5Document3 pagesFile Management: Inquiry & Thinking /21 Communication /5Annie TranNo ratings yet
- College DBMS PresentationDocument15 pagesCollege DBMS PresentationwelfareNo ratings yet
- Random-Access Files: ExampleDocument16 pagesRandom-Access Files: ExampleAaron BrownNo ratings yet
- OS Chapter 5Document30 pagesOS Chapter 5Firomsa DineNo ratings yet
- Lec5 CS604 PpsDocument24 pagesLec5 CS604 PpsIbrahim ChoudaryNo ratings yet
- CSE-303 Compiler IntroductionDocument9 pagesCSE-303 Compiler IntroductionRafinNo ratings yet
- Computer Organization and Operating Systems - U5Document16 pagesComputer Organization and Operating Systems - U5Vanam SaikumarNo ratings yet
- Linux InterProcessCommunicationDocument13 pagesLinux InterProcessCommunicationyashwanth saiNo ratings yet
- EN CDSFIN Syllabus V1.0Document7 pagesEN CDSFIN Syllabus V1.0Daniel AasaNo ratings yet
- Javascript Cloud Slideshare 140210053940 Phpapp02Document60 pagesJavascript Cloud Slideshare 140210053940 Phpapp02Saint GreenNo ratings yet
- Less Known Solaris Features Book AlphaDocument220 pagesLess Known Solaris Features Book Alphakuba100% (3)
- Tune Your Custom Abap Code in HANA MigrationDocument10 pagesTune Your Custom Abap Code in HANA MigrationPartha Sarathi ChattopadhyayaNo ratings yet
- Design and Development of Personnel Information SystemDocument116 pagesDesign and Development of Personnel Information SystemJulie BArutNo ratings yet
- EISOO AnyBackup Operating ProceduresDocument63 pagesEISOO AnyBackup Operating ProceduresJohn WooNo ratings yet
- SteelEye DataKeeper OverviewDocument2 pagesSteelEye DataKeeper OverviewbcboseNo ratings yet
- CS2032 Unit I NotesDocument23 pagesCS2032 Unit I NotesRaj KumarNo ratings yet
- Business AnalyticsDocument9 pagesBusiness AnalyticsArjun TrehanNo ratings yet
- Database Management - Class NotesDocument6 pagesDatabase Management - Class NotesAnooja SajeevNo ratings yet
- Support search-as-you-type using SQL in databasesDocument15 pagesSupport search-as-you-type using SQL in databasesgowtham kNo ratings yet
- Internal Reqs Across SOB Jan 2009Document12 pagesInternal Reqs Across SOB Jan 2009Karthik Raj RajagopalNo ratings yet
- Chandralekha Rao YachamaneniDocument7 pagesChandralekha Rao YachamaneniKritika ShuklaNo ratings yet
- Performance Task 1 Prog 114 No. 2 BDocument4 pagesPerformance Task 1 Prog 114 No. 2 BJohn Dexter Lanot100% (1)
- Spotfire TDV 7.0.7 UsersGuideDocument680 pagesSpotfire TDV 7.0.7 UsersGuideIgor PNo ratings yet
- Definitions: - Lists and Arrays - Nodes and Pointers - Single Linked Lists - Double Linked Lists - Circular ListsDocument41 pagesDefinitions: - Lists and Arrays - Nodes and Pointers - Single Linked Lists - Double Linked Lists - Circular ListsRuthwik H ParamNo ratings yet
- Exiftool Tool Use CaseDocument30 pagesExiftool Tool Use CaseSantosh kumar beheraNo ratings yet
- NormalizationDocument48 pagesNormalizationRahinul Islam PollobNo ratings yet
- DBMS SuggestionsDocument17 pagesDBMS Suggestionssudarshan karkiNo ratings yet
- Cassandra 30Document259 pagesCassandra 30Anderson Faria SantosNo ratings yet
- Lecture 5 - Data TransformationDocument7 pagesLecture 5 - Data TransformationAvneet SinghNo ratings yet
- Advanced Certification in Data Analytics For BusinessDocument14 pagesAdvanced Certification in Data Analytics For BusinessAbil Mathew JohnNo ratings yet
- OA Framework - Dibyajyoti Koch - A Blog On Oracle ApplicationDocument44 pagesOA Framework - Dibyajyoti Koch - A Blog On Oracle ApplicationMostafa TahaNo ratings yet
- CECS 323: Mimi OpkinsDocument372 pagesCECS 323: Mimi OpkinsYun TatNo ratings yet
- Distributed File Systems: - Objectives - ContentsDocument34 pagesDistributed File Systems: - Objectives - Contentsramalingam_decNo ratings yet
- VDM Viewtype #ConsumptionDocument9 pagesVDM Viewtype #Consumptionappalaraju gompaNo ratings yet
- 16 SDocument8 pages16 SPratyushNo ratings yet
- r5410503 Data Warehousing and Data MiningDocument1 pager5410503 Data Warehousing and Data MiningsivabharathamurthyNo ratings yet
- Chapter 5: Overview of Query ProcessingDocument18 pagesChapter 5: Overview of Query ProcessingAnurag UpadhyayNo ratings yet