Professional Documents
Culture Documents
Private-Key Cryptography: Hence Does Not Protect Sender From Receiver Forging A Message & Claiming Is Sent by Sender
Uploaded by
ashrafhaja0 ratings0% found this document useful (0 votes)
78 views21 pagesrsa algorithm
Original Title
Rsa
Copyright
© © All Rights Reserved
Available Formats
PPT, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this Documentrsa algorithm
Copyright:
© All Rights Reserved
Available Formats
Download as PPT, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
78 views21 pagesPrivate-Key Cryptography: Hence Does Not Protect Sender From Receiver Forging A Message & Claiming Is Sent by Sender
Uploaded by
ashrafhajarsa algorithm
Copyright:
© All Rights Reserved
Available Formats
Download as PPT, PDF, TXT or read online from Scribd
You are on page 1of 21
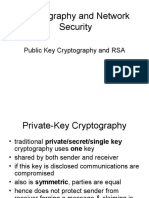
Private-Key Cryptography
traditional private/secret/single key cryptography
uses one key
Key is shared by both sender and receiver
if the key is disclosed communications are
compromised
also known as symmetric, both parties are equal
hence does not protect sender from receiver forging a
message & claiming is sent by sender
Public-Key Cryptography
probably most significant advance in the 3000
year history of cryptography
uses two keys a public key and a private key
asymmetric since parties are not equal
uses clever application of number theory concepts
to function
complements rather than replaces private key
cryptography
Public-Key Cryptography
public-key/two-key/asymmetric cryptography
involves the use of two keys:
a public-key, which may be known by anybody, and
can be used to encrypt messages, and verify
signatures
a private-key, known only to the recipient, used to
decrypt messages, and sign (create) signatures
is asymmetric because
those who encrypt messages or verify signatures
cannot decrypt messages or create signatures
Public-Key Cryptography
Why Public-Key Cryptography?
developed to address two key issues:
key distribution how to have secure
communications in general without having to
trust a KDC with your key
digital signatures how to verify a message
comes intact from the claimed sender
public invention due to Whitfield Diffie &
Martin Hellman at Stanford U. in 1976
known earlier in classified community
Public-Key Characteristics
Public-Key algorithms rely on two keys
with the characteristics that it is:
computationally infeasible to find decryption
key knowing only algorithm & encryption key
computationally easy to en/decrypt messages
when the relevant (en/decrypt) key is known
either of the two related keys can be used for
encryption, with the other used for decryption
(in some schemes)
Public-Key Cryptosystems
Public-Key Applications
can classify uses into 3 categories:
encryption/decryption (provide secrecy)
digital signatures (provide authentication)
key exchange (of session keys)
some algorithms are suitable for all uses,
others are specific to one
Security of Public Key Schemes
like private key schemes brute force exhaustive
search attack is always theoretically possible
but keys used are too large (>512bits)
security relies on a large enough difference in
difficulty between easy (en/decrypt) and hard
(cryptanalyse) problems
more generally the hard problem is known, its just
made too hard to do in practise
requires the use of very large numbers
hence is slow compared to private key schemes
RSA
by Rivest, Shamir & Adleman of MIT in 1977
best known & widely used public-key scheme
based on exponentiation in a finite (Galois) field
over integers modulo a prime
nb. exponentiation takes O((log n)
3
) operations (easy)
uses large integers (eg. 1024 bits)
security due to cost of factoring large numbers
nb. factorization takes O(e
log n log log n
) operations (hard)
RSA Key Setup
each user generates a public/private key pair by:
selecting two large primes at random - p, q
computing their system modulus N=p.q
note (N)=(p-1)(q-1)
selecting at random the encryption key e
where 1<e<(N), gcd(e,(N))=1
solve following equation to find decryption key d
e.d=1 mod (N) and 0dN
publish their public encryption key: KU={e,N}
keep secret private decryption key: KR={d,p,q}
RSA Use
to encrypt a message M the sender:
obtains public key of recipient KU={e,N}
computes: C=M
e
mod N, where 0M<N
to decrypt the ciphertext C the owner:
uses their private key KR={d,p,q}
computes: M=C
d
mod N
note that the message M must be smaller
than the modulus N (block if needed)
Why RSA Works
because of Euler's Theorem:
a
(n)
mod N = 1
where gcd(a,N)=1
in RSA have:
N=p.q
(N)=(p-1)(q-1)
carefully chosen e & d to be inverses mod (N)
hence e.d=1+k.(N) for some k
hence :
C
d
= (M
e
)
d
= M
1+k.(N)
= M
1
.(M
(N)
)
q
= M
1
.(1)
q
= M
1
= M mod N
RSA Example
1. Select primes: p=17 & q=11
2. Compute n = pq =1711=187
3. Compute (n)=(p1)(q-1)=1610=160
4. Select e : gcd(e,160)=1; choose e=7
5. Determine d: de=1 mod 160 and d < 160
Value is d=23 since 237=161= 10160+1
6. Publish public key KU={7,187}
7. Keep secret private key KR={23,17,11}
RSA Example cont
sample RSA encryption/decryption is:
given message M = 88 (nb. 88<187)
encryption:
C = 88
7
mod 187 = 11
decryption:
M = 11
23
mod 187 = 88
Exponentiation
can use the Square and Multiply Algorithm
a fast, efficient algorithm for exponentiation
concept is based on repeatedly squaring base
and multiplying in the ones that are needed to
compute the result
look at binary representation of exponent
only takes O(log
2
n) multiples for number n
eg. 7
5
= 7
4
.7
1
= 3.7 = 10 mod 11
eg. 3
129
= 3
128
.3
1
= 5.3 = 4 mod 11
Exponentiation
RSA Key Generation
users of RSA must:
determine two primes at random - p, q
select either e or d and compute the other
primes p,q must not be easily derived from
modulus N=p.q
means must be sufficiently large
typically guess and use probabilistic test
exponents e, d are inverses, so use Inverse
algorithm to compute the other
RSA Security
three approaches to attacking RSA:
brute force key search (infeasible given size of
numbers)
mathematical attacks (based on difficulty of
computing (N), by factoring modulus N)
timing attacks (on running of decryption)
Factoring Problem
mathematical approach takes 3 forms:
factor N=p.q, hence find (N) and then d
determine (N) directly and find d
find d directly
currently believe all equivalent to factoring
have seen slow improvements over the years
as of Aug-99 best is 130 decimal digits (512) bit with GNFS
biggest improvement comes from improved algorithm
cf Quadratic Sieve to Generalized Number Field Sieve
barring dramatic breakthrough 1024+ bit RSA secure
ensure p, q of similar size and matching other constraints
Timing Attacks
developed in mid-1990s
exploit timing variations in operations
eg. multiplying by small vs large number
or IF's varying which instructions executed
infer operand size based on time taken
RSA exploits time taken in exponentiation
countermeasures
use constant exponentiation time
add random delays
blind values used in calculations
You might also like
- Elective 5 Mathematical Systems PDFDocument54 pagesElective 5 Mathematical Systems PDFAlan Peter100% (3)
- Basics of Digital Signatures and PKI SDocument4 pagesBasics of Digital Signatures and PKI SPramedicaPerdanaPutraNo ratings yet
- Network security title under 40 charactersDocument14 pagesNetwork security title under 40 charactersmadeti gouthamNo ratings yet
- Kerberos Network Authentication Protocol ExplainedDocument15 pagesKerberos Network Authentication Protocol ExplainedMaestroanon100% (1)
- Lab3 CryptographyDocument5 pagesLab3 CryptographyKenshiNo ratings yet
- Assignment No.5 Question No.1:: What Is The Difference Between A Block Cipher and A Stream Cipher? AnswerDocument2 pagesAssignment No.5 Question No.1:: What Is The Difference Between A Block Cipher and A Stream Cipher? Answersameer khanNo ratings yet
- Bletchley List UvDocument4 pagesBletchley List UveliahmeyerNo ratings yet
- Fingerprint Recognition Using MATLAB PDFDocument74 pagesFingerprint Recognition Using MATLAB PDFshakil0% (1)
- Digital Signature: Presented by K.ANITHA (19065) T.DIVYA (19074) T.PAVAN (19082) P.Venu Gopal Reddy (19104)Document19 pagesDigital Signature: Presented by K.ANITHA (19065) T.DIVYA (19074) T.PAVAN (19082) P.Venu Gopal Reddy (19104)Divya TammineediNo ratings yet
- Kerberos X509Document31 pagesKerberos X509GeorgeStenNo ratings yet
- Chapter 04Document30 pagesChapter 04crazz1No ratings yet
- Crypto Key ManagementDocument31 pagesCrypto Key ManagementFachrizal Rizky FerdiansyahNo ratings yet
- Exercise 1Document28 pagesExercise 1Kien Nguyen TrungNo ratings yet
- Chapter 1-4Document135 pagesChapter 1-4WONDYE DESTANo ratings yet
- CrypTool BookDocument552 pagesCrypTool BookInteramericano ArequipaNo ratings yet
- Crypto DigitalSignatureDocument35 pagesCrypto DigitalSignaturefraspiNo ratings yet
- Ch09 Public-Key CryptosystemsDocument20 pagesCh09 Public-Key CryptosystemsShashi SinghNo ratings yet
- Chapter 18 Network Security and ProtocolsDocument62 pagesChapter 18 Network Security and Protocolshclraj406No ratings yet
- Digital SignatureDocument4 pagesDigital SignatureMuskan BhagiaNo ratings yet
- Introduction to Cryptography: Encryption Techniques and Security ServicesDocument21 pagesIntroduction to Cryptography: Encryption Techniques and Security ServicesRadhika SridharNo ratings yet
- Cryptography and Network Security: Sixth Edition by William StallingsDocument40 pagesCryptography and Network Security: Sixth Edition by William Stallingsاحمد ميسر فتحي كموشNo ratings yet
- Java XML Digital SignaturesDocument16 pagesJava XML Digital SignaturesmkiitdNo ratings yet
- Digital SignaturesDocument20 pagesDigital SignaturesKiran George ChennattucherryNo ratings yet
- Digital SignatureDocument31 pagesDigital SignatureAnupam BaliNo ratings yet
- L1 - Introduction To Security Attacks, Services & Mechanism, A Model For Network SecurityDocument7 pagesL1 - Introduction To Security Attacks, Services & Mechanism, A Model For Network SecurityYash TrivediNo ratings yet
- DS-DIGITAL SIGNATURE BENEFITSDocument10 pagesDS-DIGITAL SIGNATURE BENEFITSSahil MiglaniNo ratings yet
- Unit 2 CRYPTOGRAPHYDocument7 pagesUnit 2 CRYPTOGRAPHYdev chauhanNo ratings yet
- Introduction to Cryptography ToolsDocument35 pagesIntroduction to Cryptography ToolsManish AeronNo ratings yet
- Digital Signature ProjectDocument87 pagesDigital Signature ProjectSuresh Neharkar100% (1)
- Main Presentation (Digital Signature Certificates)Document26 pagesMain Presentation (Digital Signature Certificates)eeshasinghNo ratings yet
- Digital SignatureDocument26 pagesDigital SignatureNeha Dabhi100% (1)
- Department of Electronics and Communication Engineering: Project Phase I PresentationDocument18 pagesDepartment of Electronics and Communication Engineering: Project Phase I PresentationArun ManojNo ratings yet
- Chapter 1 Computer SecurityDocument22 pagesChapter 1 Computer SecurityAjay GuptaNo ratings yet
- Aes Algorithm For Encryption: Radhika D.BajajDocument6 pagesAes Algorithm For Encryption: Radhika D.BajajamrinNo ratings yet
- Digital SignatureDocument19 pagesDigital SignatureRanu SharmaNo ratings yet
- Seminar Digital SignatureDocument11 pagesSeminar Digital Signaturegarima_gaur27No ratings yet
- Osi ModelDocument36 pagesOsi Modelejednakomc2100% (1)
- Digital Signature Standard and DSA AlgorithmDocument4 pagesDigital Signature Standard and DSA AlgorithmSajendra KumarNo ratings yet
- CNS - Unit IDocument60 pagesCNS - Unit IAyush GandhiNo ratings yet
- Implementation of Aes and Blowfish AlgorithmDocument4 pagesImplementation of Aes and Blowfish AlgorithmInternational Journal of Research in Engineering and TechnologyNo ratings yet
- L4 Cipher SystemsDocument47 pagesL4 Cipher SystemsMinhajul IslamNo ratings yet
- Digital SignatureDocument3 pagesDigital SignatureMd shabbir ahmedNo ratings yet
- Ch15Crypto6e Userauth Nemo2Document43 pagesCh15Crypto6e Userauth Nemo2highway2prakasNo ratings yet
- Case Study Digital SignatureDocument7 pagesCase Study Digital Signaturedaveharshil31100% (2)
- Osi Model: by A. Bathsheba Parimala Department of BCA and NetworkingDocument14 pagesOsi Model: by A. Bathsheba Parimala Department of BCA and NetworkingSheba ParimalaNo ratings yet
- Security ManagementDocument28 pagesSecurity ManagementAnkit PawarNo ratings yet
- Digital Signature Seminar ReportDocument15 pagesDigital Signature Seminar ReportAshish RajNo ratings yet
- PGP and S/MIME Email Security StandardsDocument20 pagesPGP and S/MIME Email Security StandardsVasantha KumariNo ratings yet
- Cryptography and Network Security: Sixth Edition by William StallingsDocument26 pagesCryptography and Network Security: Sixth Edition by William Stallingsco caNo ratings yet
- Data Sharing Security in Cloud ComputingDocument18 pagesData Sharing Security in Cloud ComputingGaba StudioNo ratings yet
- Course Code: CSE 606 Course Title: Cryptography & Information SecurityDocument6 pagesCourse Code: CSE 606 Course Title: Cryptography & Information SecurityNazmul HaqueNo ratings yet
- COMPTIA Security+ Cuestionario Semana 5Document5 pagesCOMPTIA Security+ Cuestionario Semana 5cristian Jahaziel Mariano SalomónNo ratings yet
- IMDA IoT Cyber Security GuideDocument19 pagesIMDA IoT Cyber Security Guideioqse ioqseNo ratings yet
- CH 13Document22 pagesCH 13co caNo ratings yet
- Key Management Techniques and Life Cycle in CryptographyDocument20 pagesKey Management Techniques and Life Cycle in CryptographyDevashish NigamNo ratings yet
- What Is HTTPS - Why Secure A Web Site: Use HTTPS For Storefronts and Ecommerce Web SitesDocument5 pagesWhat Is HTTPS - Why Secure A Web Site: Use HTTPS For Storefronts and Ecommerce Web SitesvgprasadNo ratings yet
- A Comprehensive Evaluation of Cryptographic Algorithms Des 3des Aes Rsa and Blowfish PDFDocument8 pagesA Comprehensive Evaluation of Cryptographic Algorithms Des 3des Aes Rsa and Blowfish PDFHenry Fu KeatNo ratings yet
- Cryptography and Network Security: Fifth Edition by William StallingsDocument34 pagesCryptography and Network Security: Fifth Edition by William StallingsPraveen KumarNo ratings yet
- Key Management Distribution TechniquesDocument35 pagesKey Management Distribution TechniquesSoumak PoddarNo ratings yet
- What Is The OSI Security Architecture?Document5 pagesWhat Is The OSI Security Architecture?Elanor ElNo ratings yet
- 3d PasswordDocument20 pages3d PasswordReuben D'souzaNo ratings yet
- PRP PRFDocument17 pagesPRP PRFPktc BKNo ratings yet
- Implement Caesar Cipher in CDocument36 pagesImplement Caesar Cipher in CKrupa PatelNo ratings yet
- Multi-Keyword Searchable Encryption System For Distributed Systems in Cloud TechnologyDocument5 pagesMulti-Keyword Searchable Encryption System For Distributed Systems in Cloud TechnologyBaranishankarNo ratings yet
- Student Solution Chap 07Document8 pagesStudent Solution Chap 07priyapati21No ratings yet
- Data Masking GuideDocument57 pagesData Masking GuideRavindra Kumar PrajapatiNo ratings yet
- 5 Common Encryption Algorithms and The Unbreakables of The Future - StorageCraftDocument5 pages5 Common Encryption Algorithms and The Unbreakables of The Future - StorageCraftKavin CavinNo ratings yet
- NSA AmerCryptColdWarBk1Document301 pagesNSA AmerCryptColdWarBk1Peter WilliamsNo ratings yet
- DFDDocument14 pagesDFDapi-3739854100% (8)
- 2016-Mw-Subhajit Das Chaudhuri-Deep Dive Into SSL Implementation Scenarios For Oracle Apps-Praesentation PDFDocument52 pages2016-Mw-Subhajit Das Chaudhuri-Deep Dive Into SSL Implementation Scenarios For Oracle Apps-Praesentation PDFmaleemNo ratings yet
- Assignment 2Document4 pagesAssignment 2Princess TanuNo ratings yet
- White-Paper - Living in A Quantum-Safe WorldDocument4 pagesWhite-Paper - Living in A Quantum-Safe WorldSanti IndarjaniNo ratings yet
- Dr. Ramdas B. Sonawane's guide to classical cryptographyDocument35 pagesDr. Ramdas B. Sonawane's guide to classical cryptographyRamdas Sonawane100% (1)
- Journal of Computer Science IJCSIS June PDFDocument277 pagesJournal of Computer Science IJCSIS June PDFKalyan DasNo ratings yet
- Ch14: Key Distribution (Computer and Network Security)Document37 pagesCh14: Key Distribution (Computer and Network Security)DinaNo ratings yet
- GPC 2.3 D SCP03 v1.1.2 PublicReleaseDocument41 pagesGPC 2.3 D SCP03 v1.1.2 PublicReleasemohammedNo ratings yet
- Public Key Infrastructure: Jim HurstDocument5 pagesPublic Key Infrastructure: Jim HurstBARNALI GUPTANo ratings yet
- Unit 1 Introduction and Number Theory PDFDocument73 pagesUnit 1 Introduction and Number Theory PDFSwapnil NawaleNo ratings yet
- Diffie HelmanDocument15 pagesDiffie HelmanManal MustafaNo ratings yet
- BMSIT (Techincal Seminar)Document16 pagesBMSIT (Techincal Seminar)Manish ManiNo ratings yet
- Classical CryptographyDocument20 pagesClassical CryptographyBHAVPRITANo ratings yet
- Two-Factor Authentication ExplainedDocument14 pagesTwo-Factor Authentication ExplainedSanskriti MittalNo ratings yet
- Cryptography CS 555: Topic 10: Block Cipher Security & AESDocument26 pagesCryptography CS 555: Topic 10: Block Cipher Security & AESAswini KnairNo ratings yet
- Alfabetul NATO Şi PronunţiaDocument3 pagesAlfabetul NATO Şi PronunţiaMarian MarianNo ratings yet
- Alice and BobDocument3 pagesAlice and BobBasker PalaniSwamyNo ratings yet
- Introduction To CrypTool 2Document14 pagesIntroduction To CrypTool 2long Lưu HoàngNo ratings yet