Professional Documents
Culture Documents
ITA503 Mobile Computing
Uploaded by
khadarnawas0 ratings0% found this document useful (0 votes)
114 views215 pagesITA503-Mobile Computing Summer Course Slot C Mode of evaluation - Quiz - Assignments - CAT1 – CAT2 - Term end Text Book:"wireless communication" Schiller 2ed pearson education - "Computer networks"
Original Description:
Copyright
© © All Rights Reserved
Available Formats
PPT, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentITA503-Mobile Computing Summer Course Slot C Mode of evaluation - Quiz - Assignments - CAT1 – CAT2 - Term end Text Book:"wireless communication" Schiller 2ed pearson education - "Computer networks"
Copyright:
© All Rights Reserved
Available Formats
Download as PPT, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
114 views215 pagesITA503 Mobile Computing
Uploaded by
khadarnawasITA503-Mobile Computing Summer Course Slot C Mode of evaluation - Quiz - Assignments - CAT1 – CAT2 - Term end Text Book:"wireless communication" Schiller 2ed pearson education - "Computer networks"
Copyright:
© All Rights Reserved
Available Formats
Download as PPT, PDF, TXT or read online from Scribd
You are on page 1of 215
ITA503-Mobile Computing
Summer Course Slot C
Mode of evaluation
Quiz
Assignments
CAT1
CAT2
Term end
Text Book:Mobile communication Schiller
2ed Pearson education
Computer networks A Tanenbaum 4ed
Reference:wireless communications T S
Rappaport 2ed pearson
Types of mobility
1)User mobility
eg: vodofone service
2)Device mobility
eg:mobile phones
Characteristic of communication devices
Fixed & wired eg:Desktop
Mobile & wireless eg:Laptop
Fixed & wireless eg:wireless on historical
buildings
Mobile and wireless eg:GSM
Applications
Vehicles
Emergencies
Business
Replacement of wired networks- sensor
networks
Infotainment
Mobile & wireless devices
Sensors
Embedded Controllers
Pagers
Mobile phones
Personal digital assistance
Pocket computers
Notepad/lap tops
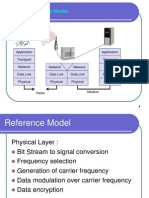
Simple n/w & reference Model
Frequency Spectrum
Frequency Allocations(in MHz)
Signals
Signals are function of time & location
Carrier signals
Periodic signals(sine waves)
A-amplitude
F-frequency
-phase swift
Time domain
Signal reconstruction by Fourier
C-determine direct current component of
signal
a
n
& b
n
amplitudes of nth sine & cosine
functions
Frequency domain &Phase domain
M-amplitude of signal
I-in phase(phase 0)
Q-Quadrature(90 phase shift)
Antennas
It couples electromagnetic energy to and from
space to and from a wire or a coaxial cable
Theoretical reference : it is isotropic radiator
i.e a point in a space radiating equal power
in all directions
Radiation pattern is symmetric in all directions
Isotropic antennas does not exist in reality
Real antennas exhibit directive effect(intensity
is not same in all directions)
Types of antennas
Dipole
Omni directional
Directional
Sectorized
diversity
Dipole antennas
Consist of two collinear conductors of equal
length , separated by small gap
Omni directional
Radiation pattern in one plane
This is used to overcome environmental
challenges by boosting power level of signal
Challenges could be mountains, valley, building etc
Directional antennas
Radiation pattern only in x-axis
Special eg: Satellite dishes
Sectorized antennas
Several directional antennas combined on a single
pole
Diversity combining
Constitutes a power of all signals to produce gain
Phase is corrected to avoid cancellation
Signal propagation
One can determine the behavior of a signal
travelling along wire, e.g., received power
depending on the length of wire
For wireless ,the above prediction is valid only
in vacuum
Transmission Range: with this radius of the sender
transmission is possible
Detection range: within a second radius , detection
of transmission is possible.
i.e transmitted power is large enough to differ from
background noise
Interference range:background noise is added with
the transmission.
Path Loss of radio signals
Line-of-sight
Path loss in vacuum
Received energy p
r
=1/d
2
d is distance between sender & receiver
Sender in a space radiate energy in spherical
shape,surface area is s=4d
2
increasing results
loss
Received power depends on the wavelength,
gain of the receiver & transmitter antennas
Penetration of signal on object depends on
the frequency
Lower frequency better penetration
3 fundamental behavior of radio waves
Ground waves
Sky waves
Line of sight
Ground waves(<2MHz)
It follows earths surface and propagate long distance
Sky waves (2-30 MHz)-(short waves)
Reflected by ionosphere
Line of sight (>30MHz)
Follows straight line of sight
No reflection in ionosphere
Cable of bending due to refraction
Mobile phone system, satellite system, cordless phone
Additional Signal propagation effects
Blocking or shadowing of radio signals due to
large obstacles
Reflection
Refraction-bending effect of signal
Scattering :size of obstacle is in order of the
wavelength or less,radio waves get scattered
Diffraction: Deflection at the edge of object
and propagate in different direction
Multi-path propagation
Along with direct transmission from a sender
to a receiver the propagation effects like
scattering, reflection,difraction leads to one of
the severe effect called Multi-path
propagation
signals travelling along different paths with
different lengths arrive at the receiver at
different times
This effect is called delay spread
Typical values for delay spread are
approximately 3 s in cities, up to 12 s
GSM, for example, can tolerate up to 16 s of
delay spread, i.e., almost a 5 km path
difference
Effects of spread delay
a short impulse will be smeared out into a
broader impulse, or rather into several weaker
impulses.
Intersymbol Interference(ISI) -At the receiver,
both impulses interfere, i.e., they overlap in
time
Avoiding ISI
Knowing the channel characteristic
If sender knows the delay of different path ,it
can compensate the distortion caused by the
channel
How?
sender may first transmit a training sequence
known by the receiver. The receiver then
compares the received signal to the original
training sequence and programs an equalizer that
compensates for the distortion
Fading
The power of the received signal changes
considerably over time
Short time fading-quick changes in the
received power are called short-term fading
signals may have a different phase due to different
paths and cancel each other
Long term fading:
The average power over time, is caused by, for
example, varying distance to the sender
senders can compensate for long-term fading by
increasing/decreasing sending power
MULTIPLEXING
Multiplexing describes how several users can
share a medium with minimum or no
interference
For wireless communication, multiplexing can
be carried out in four dimensions:
space, time, frequency, and code
Space Division Multiplexing (SDM)
Guard Space
Frequency Division Multiplexing(TDM)
Adjacent channel interference
Guard Space
Time Division Multiplexing(TDM)
Co-Channel Interference
Mix of FDM & TDM
Code Division Multiplexing (CDM)
Secure
Codes are used
Orthogonal code
Guard space as codes
Modulation
g(t) = A
t
cos(2 f
t
t +
t
)
3 parameters
A
t
amplitude
f
t
frequency
t
Phase
Can be varied in accordance with data or
another signal
Digital Modulation
Digital data (0 and 1) is translated into an
analog signal (base band)
Digital modulation is required if digital data
has to be transmitted over a medium that only
allows for analog transmission
the binary bit-stream has to be translated into
an analog signal first
Three basic digital modulation
Amplitude shift keying (ASK)
frequency shift keying (FSK) and
phase shift keying (PSK).
Analog Modulation
wireless transmission requires an additional
modulation, an analog modulation
Baseband signal is connected to radio carrier
Reasons for why baseband cannot send directly
Antennas
Frequency Division Multiplexing
Medium Characteristic (path loss, penetration of
obstacles, reflection, scattering & diffraction)
(short waves for handheld device, VSW for microwave
& Long waves for submarines)
Block Diagram of radio transmitter and receiver
Amplitude shift keying
The two binary values, 1 and 0, are
represented by two different amplitudes
This simple scheme only requires low
bandwidth
very susceptible to interference
Effects like multi-path propagation, noise, or
path loss heavily influence the amplitude
the wired transmission scheme with the
highest performance, namely optical
transmission, uses ASK
ASK can also be applied to wireless infra red
transmission
Frequency shift keying
The simplest form of FSK is called binary FSK
assigns one frequency f1 to the binary 1
another frequency f2 to the binary 0
How to implement
to switch between two oscillators, one with
the frequency f1 and the other with f2,
depending on the input
To avoid sudden changes in phase, continuous
phase modulation (CPM) can be used
demodulation is by using two bandpass filters,
one for f1 the other for f2.
Phase shift keying
shifts in the phase of a signal to represent
data
shifting the phase by 180 each time the value
of data changes, is also called binary PSK
(BPSK)
modulator could multiply a frequency f with
+1 if the binary data is 1 and with 1 if the
binary data is 0.
the receiver must synchronize in frequency
and phase with the transmitter
Compared to FSK, PSK is more resistant to
interference
Advanced frequency shift keying
Minimum shift keying(MSK)
First step:
Data bit is separated into even and odd bits,
Duration of each bit being doubled
The scheme also uses two frequencies: f1, the
lower frequency, and f2, the higher frequency,
with f2 = 2f1
MSK
if the even and the odd bit are both 0, then the higher
frequency f2 is inverted (i.e., f2 is used with a phase
shift of 180)
if the even bit is 1, the odd bit 0, then the lower
frequency f1 is inverted. This is the case, e.g., in the
fifth to seventh columns
if the even bit is 0 and the odd bit is 1, as in columns 1
to 3, f1 is taken without changing the phase
if both bits are 1 then the original f2 is taken
A high frequency is always chosen if even and
odd bits are equal
The signal is inverted if the odd bit equals 0
Advance Phase shift keying
BPSK scheme only uses one possible phase
shift of 180
Above figure shows BPSK in the phase domain
Quadrature PSK (QPSK)
coding two bits into one phase shift
phase shift can always be relative to a
reference signal
If this scheme is used, a phase shift of 0 means
that the signal is in phase with the reference
signal
phase shift of 45 for the data 11
135 for 10
225 for 00
315 for 01
with all phase shifts being relative to the
reference signal
The transmitter selects parts of the signal as
shown below and concatenates them.
To reconstruct data, the receiver has to compare
the incoming signal with the reference signal
One problem of this scheme involves
producing a reference signal at the receiver
Transmitter and receiver have to be
synchronized very often
differential QPSK (DQPSK)
the phase shift is not relative to a reference
signal
but phase shift is relative to phase of the
previous two bits
In this case, the receiver does not need the
reference signal but only compares two
signals to reconstruct data
quadrature amplitude modulation
(QAM)
The PSK scheme could be combined with ASK
Here three different amplitudes and 12 angles
are combined coding 4 bits per
phase/amplitude change
Multi-carrier modulation
used in the European digital radio system DAB
and the WLAN standards IEEE 802.11a and
HiperLAN2
The main attraction of MCM is its good ISI
mitigation property
MCM splits the high bit rate stream into many
lower bit rate streams , each stream being
sent using an independent carrier frequency
for example, n symbols/s have to be
transmitted, each subcarrier transmits n/c
symbols/s with c being the number of
subcarriers
frequency selective fading only influences
some subcarriers,and not the whole signal
an additional benefit of MCM
Spread spectrum
techniques involve spreading the bandwidth
needed to transmit data
The main advantage is the resistance to
narrowband interference
i) shows an idealized narrowband signal from
a sender of user data
The sender now spreads the signal in step ii)
i.e., converts the narrowband signal into a
broadband signal
During transmission, narrowband and
broadband interference add to the signal in
step iii).
The sum of interference and user signal is
received
The receiver now knows how to despread the
signal, converting the spread user signal into a
narrowband signal again
v) the receiver applies abandpass filter to cut
off frequencies left and right of the
narrowband signal
Finally, the receiver can reconstruct the
original data because the power level of the
user signal is high enough
Consider the situation shown in Figure below
Six different channels use FDM for
multiplexing, which means that each channel
has its own narrow frequency band for
transmission
Depending on receiver characteristics,
channels 1, 2, 5, and 6 could be received
while the quality of channels 3 and 4 is too
bad to reconstruct transmitted data.
Narrowband interference destroys the
transmission of channels 3 and 4.
How can spread spectrum help in such a
situation?
narrowband signals are now spread into
broadband signals using the same frequency
range
To separate different channels, CDM is now
used instead of FDM
Each channel is allotted its own code, which
the receivers have to apply to recover the
signal
One disadvantage is the increased complexity
of receivers that have to despread a signal
Direct sequence spread spectrum (DSSS)
DSSS systems take a user bit stream and
perform an (XOR) with a so-called chipping
sequence
The example shows that the result is either
the sequence 0110101 if data bit is 0
its complement 1001010 (if data bit equals 1).
User bit has a duration tb, the chipping
sequence consists of smaller pulses, called
chips, with a duration tc.
spreading factor s = tb/tc determines the
bandwidth
original signal needs a bandwidth w then the
resulting signal needs sw after spreading.
civil applications use spreading factors
between 10 and 100, military applications use
factors of up to 10,000.
Wireless LANs use, for example, the sequence
10110111000, a so-called Barker code
Barker codes exhibit a good robustness
against interference and insensitivity to multi-
path propagation
Other known Barker codes are 11, 110,1110,
11101, 1110010, and 1111100110101
DSSS transmitter
DSSS receiver
Calculating the products of chips and signal, and
adding the products in an integrator is also called
correlation, the device a correlator.
Case
If transmitter and receiver are perfectly
synchronized and the signal is not too
distorted by noise or multi-path propagation,
DSSS works perfectly
Sending the user data 01 and applying the
11-chip Barker code 10110111000 results in
the spread signal
1011011100001001000111.
the sum of products equal to 0 for the first bit
and to 11 for the second bit
The decision unit can now map the first sum
(=0) to a binary 0
second sum (=11) to a binary 1
Frequency hopping spread
spectrum(FHSS)
the total available bandwidth is split into
many channels of smaller bandwidth +guard
spaces
Transmitter and receiver stay on one of these
channels for a certain time and then hop to
another channel
system implements FDM and TDM
The pattern of channel usage is called the
hopping sequence
time spend on a channel with a certain
frequency is called the dwell time
FHSS comes in two variants, slow and fast
hopping
Slow Hopping
one frequency is used for several bit periods
user bits with a bit period t
b
first three bits during the dwell time t
d
frequency f
2
is used
Then, the transmitter hops to the next
frequency f
3
Fast Hopping
The transmitter changes the frequency several
times during the transmission of a single bit
Transmitter hops three times during a bit
period
example of an FHSS system is Bluetooth,it
performs 1,600 hops per second and uses 79
hop carriers equally spaced with 1 MHz in the
2.4 GHz ISM band.
FHSS Transmitter
first step, the modulation of user data according to one
of the digital-to-analog modulation schemes, e.g., FSK
or BPSK,this results in a narrowband signal
next step, frequency hopping is performed, based on a
hopping sequence
frequency synthesizer generating the carrier
frequencies f
i
A second modulation uses the modulated narrowband
signal and the carrier frequency to generate a new
spread signal with frequency of f
i
+f
0
(Zero) & f
i
+f
1
(one)
FHSS Receiver
Medium access control -MAC
Medium access control comprises all
mechanisms that regulate user access to a
medium using SDM, TDM, FDM, or CDM
MAC algorithms which are specifically
adapted to the wireless domain
Which layer it belongs to?
Specialized MAC
It has to differ from the MAC of wires netwoks
Why?
Consider CSMA / CD
How it works in a wired networks?
Why does this scheme fail in wireless
networks?
Example CSMA/CD
Carrier Sense Multiple Access with Collision Detection
send when medium is free, listen to medium if collision
occurs (IEEE 802.3)
Problems in wireless networks
signal strength decreases with distance
sender applies CS and CD, but collisions happen at
receiver
sender may not hear collision, i.e., CD does not
work
Hidden terminal: CS might not work
In wired network collision is detected at the
sender.
Collision detection is very difficult in wireless
scenarios as the transmission power in the
area of the transmitting antenna is several
magnitudes higher than the receiving power.
So, this very common MAC scheme from
wired network fails in a wireless scenario
Hidden and exposed terminals
Near and far terminals
SDMA
Space Division Multiple Access (SDMA) is
used for allocating a separated space to users
in wireless networks.
Cellular systems for mobile communications
implement SDM
Advantages of cellular systems with small cells
Higher capacity
Less transmission power
Local interference only
Robustness
Small cells also have some disadvantages
Infrastructure needed
Handover needed
Frequency planning
FDMA
Duplex Channel (Simultaneous transmission
in both direction
Use two different frequencies for Uplink and
Downlink
This scheme is called Frequency Division
Duplex (FDD)
TDMA
allocate certain time slots for communication
synchronization between sender and receiver
has to be achieved in the time domain
Fixed Pattern
Dynamic
Fixed TDMA
allocating a certain time slot for a channel
this results in a fixed bandwidth
is the typical solution for wireless phone
systems
each mobile station knows its turn and no
interference will happen if synchronization is
assured
The fixed pattern can be assigned by the base
station
these patterns guarantee a fixed delay
one can transmit, e.g., every 10 ms as this is the
case for standard DECT systems.
IS-54, IS-136, GSM, DECT, PHS, and PACS uses
fixed TDMA
Assigning different slots for uplink and
downlink using the same frequency is called
time division duplex (TDD).
For eg: DECT cordless phone system, the
pattern is repeated every 10 ms, i.e., each slot
has a duration of 417 s
repetition guarantees access to the medium
every 10 ms
fixed access patterns, are perfectly apt for
connections with a constant data rate(Voice
data)
they are very inefficient for bursty data or
asymmetric connections
Dynamic TDMA -Classical Aloha
TDM is applied without controlling access
Aloha neither coordinates medium access
each station can access the medium at any
time
without a central arbiter controlling access
without coordination among the stations
If two or more stations access the medium at
the same time, a collision occurs and the
transmitted data is destroyed
Resolving this problem is left to higher layers
(e.g., retransmission of data)
simple Aloha works fine for a light load
Classical Aloha
Slotted Aloha
Aloha scheme is provided by the introduction
of time slots (slotted Aloha)
transmission can only start at the beginning of
a time slot
all senders have to be synchronized
Slotted Aloha
Demand assigned multiple access
Reservation mechanisms and combinations
with some (fixed) TDM patterns are used
a reservation period followed by a
transmission period
During the reservation period, stations can
reserve future slots in the transmission period
collisions occur during the reservation period
transmission period accessed without collision
demand assigned multiple access (DAMA) a
scheme typical for satellite systems
It is Explicit (Reservation initiated ground
station )
PRMA packet reservation multiple
access
implicit reservation scheme
Satellite broadcasts the status of each TDM
slot
All stations receiving this vector will then
know which slot is occupied and which slot is
currently free
For example, the base station broadcasts the
reservation status ACDABA-F to all stations,
here A to F.
Reservation TDMA
Fixed TDM pattern with random access
N- mini slots followed by N.K data slots form a
frame ,is repeated
Each station is allocated with minislot ,this
guarantees certain band with & delay
Other station can use unused slots in round
robin scheme or Aloha scheme
Reservation TDMA
Multiple access with collision
avoidance-Hidden Terminal Soln
Exposed Terminal Solution
State Machines-Seder & receiver
CDMA
example explains the basic function of CDMA
Two senders, A and B, want to send data.
CDMA assigns the following unique and
orthogonal key sequences:
key Ak = 010011 for sender A,
key BK = 110101 for sender B.
Sender A wants to send the bit Ad = 1, sender B
sends Bd = 0. To illustrate this example, let us
assume that we code a binary 0 as 1, a binary 1
as +1.
We can then apply the standard addition
and multiplication rules.
Both senders spread their signal using their
key as chipping sequence
As = Ad*Ak = +1*(1, +1, 1, 1, +1, +1)
= (1, +1, 1, 1, +1, +1)
Bs = Bd*Bk = 1*(+1, +1, 1, +1, 1, +1)
= (1, 1, +1, 1, +1, 1).
Both signals are then transmitted at the same
time using the same frequency,so, the signals
superimpose in space
C is received at a receiver: C = As + Bs = (2, 0,
0, 2, +2, 0)
The receiver now wants to receive data from
sender A and, therefore, tunes in to the code
of A, i.e., applies As code for despreading:
C*Ak = (2, 0, 0, 2, +2, 0)*(1, +1, 1, 1, +1,
+1) = 2 + 0 + 0 + 2 + 2 + 0 = 6
As the result is much larger than 0, the
receiver detects a binary 1
sender B, i.e., applying Bs code gives C*Bk =
(2, 0, 0, 2, +2, 0)*(+1, +1, 1, +1, 1, +1) =
2 + 0 + 0 2 2 + 0 = 6. The result is
negative, so a 0 has been detected.
Coding and spreading
of data from sender A
Coding and spreading
of data from sender B
Super Impose As+Bs
Receiver
Comparison of S/T/F/CDMA
GSM: Mobile Services
GSM offers
several types of connections
voice connections, data connections, short message service
multi-service options (combination of basic services)
Three service domains
Bearer Services
Telematic Services
Supplementary Services
GSM-PLMN
transit
network
(PSTN, ISDN)
source/
destination
network
TE TE
bearer services
R, S (U, S, R) U
m
MT
MS
GSM ARCHITECTURE
The components of the tree GSM network
subsystems
Radio Subsystem (RSS) consisting of the BSSs
and all BSS connected MS devices .
Network and Switching Subsystem (NSS)
Operation Subsystem (OSS)
Radio Substation
comprises all radio specific entities like the
mobile stations (MS) and the base station
subsystem (BSS)
RSS connected to NSS via the A interface
RSS connected to OSS via the O interface
A intefaced is based on circuit-switched PCM-30
systems
the O interface uses the Signalling System No. 7
(SS7) based on X.25
Base station subsystem (BSS)
controlled by a base station controller (BSC)
Functions necessary to maintain radio
connections to an MS, coding/decoding of
voice, and rate adaptation to/from the
wireless network part
Base transceiver station (BTS):
comprises all radio equipment like antennas,
signal processing, amplifiers
Forms a radio cell using sectorized antennas
It is connected to MS via the Um interface
It is connected to the BSC via the Abis interface
The Um interface contains
all the mechanisms necessary for wireless
transmission (TDMA, FDMA etc.)
Abis interface consists of 16 or 64 kbit/s
connections
Base station controller (BSC):
manages the BTSs
reserves radio frequencies, handles the
handover
Mobile station
subscriber identity module (SIM)
international mobile equipment identity
(IMEI)
NSS
The NSS connects the wireless network with
standard public networks, performs handovers
between different BSSs
functions for worldwide localization of users
and supports charging, accounting, and
roaming
The NSS consists of switches and databases
Mobile services switching center
(MSC):
Digital ISDN switches set up connections to
other MSCs and to the BSCs via the A interface
Gateway MSC (GMSC) has additional
connections to other fixed networks, such as
PSTN and ISDN
handles all signaling needed for connection
setup
connection release and handover of
connections to other MSCs
The standard signaling system No. 7 (SS7)
Features of SS7 are number portability,free
phone/toll/credit calls, call forwarding etc
Home location register (HLR): information,
such as the mobile subscriber ISDN number
(MSISDN), subscribed services
Operation subsystem
It contains functions for network operation
and maintenance
Operation and maintenance center (OMC)
functions are traffic monitoring, status reports
of network entities, subscriber and security
management, or accounting and billing
Authentication centre (AuC):
protect user identity and data transmission
Contains algorithms for authentication and
encryption
Equipment identity register (EIR):
is a database for all IMEIs
it stores all device identifications registered for
this network
Radio interface
GSM implements SDMA,FDD, TDMA and FDMA
In GSM 900, 124 channels, each 200 kHz wide,
are used for FDMA
GSM 1800 uses, 374 channels
In GSM 900 channels 1 and 124 are not used
for transmission, 32 channels are reserved for
Organizational data the remaining 90 are used for
customers
Example GSM 900
tail are all set to 0 and used to enhance the
receiver performance
training sequence in the middle of a slot is
used to adapt the parameters of the receiver
to the current path propagation characteristics
to select strongest path in multipath
propagation
S indicates whether the data field contains
user or network control data.
Localization and calling
The HLR always contains information about
the current location
the VLR currently responsible for the MS
informs the HLR about location changes
MS moves into the range of a new VLR (a new
location area), the HLR sends all user data
needed to the new VLR
Mobile station international ISDN number
(MSISDN):
Number consists of the country code (CC)
(e.g., +49 179 1234567 with 49 for Germany),
the national destination code (NDC) (i.e., the
address of the network provider, e.g., 179),
and the subscriber number (SN)
Mobile Terminated Call
In step 1, a user dials the phone number of a
GSM subscriber
(2)GSM network forwards the call setup to the
Gateway MSC
identifies the HLR signals the call setup to the HLR
(3)
requests an MSRN from the current VLR (4)
receiving the MSRN (5), the HLR can determine
the MSC responsible for the MS
forwards this information to the GMSC (6)
The GMSC can now forward the call setup
request to the MSC indicated (7)
MSC requests the current status of the MS
from the VLR (8)
BTSs of all BSSs transmit this paging signal to
the MS (11)
If the MS answers (12 and 13)
the VLR has to perform security checks then
signals to the MSC to set up a connection to
the MS (steps 15 to 17).
Mobile Originated Call
MS transmits a request for a new connection
(1)
the BSS forwards this request to the MSC (2).
The MSC then checks if this user is allowed to
set up a call with the requested service (3 and
4)
802.11 Wireless LAN
Types
Infrastructure based
Ad-hoc
Advantages
Flexible deployment
Minimal wiring difficulties
More robust against disasters (earthquake etc)
Historic buildings, conferences, trade shows,
Disadvantages
Low bandwidth compared to wired networks (1-10 Mbit/s)
Proprietary solutions
Need to follow wireless spectrum regulations
Comparison: infrared vs. radio
transmission
Infrared
uses IR diodes, diffuse light, multiple
reflections (walls, furniture etc.)
Advantages
simple, cheap, available in many mobile
devices
no licenses needed
simple shielding possible
Disadvantages
interference by sunlight, heat sources etc.
many things shield or absorb IR light
low bandwidth
Example
IrDA (Infrared Data Association) interface
available everywhere
Radio
typically using the license free ISM band at
2.4 GHz
Advantages
experience from wireless WAN and mobile
phones can be used
coverage of larger areas possible (radio can
penetrate walls, furniture etc.)
Disadvantages
very limited license free frequency bands
shielding more difficult, interference with other
electrical devices
Example
WaveLAN, HIPERLAN, Bluetooth
Architecture of WLAN IEEE802.11
Access Points (APs)
Similar to base stations in cellular networks
Perform wireless-to-wired bridging
Distribution System, or backbone network
(typically, Ethernet)
Basic Service Set (BSS)
Group of communicating stations in a basic
service area, similar to a cell in cellular networks
Extended Service Set (ESS)
All APs in ESS share the same network name,
Service Set IDentifier (SSID)
Architecture of Adhoc WLANS
IEEE standard 802.11
mobile terminal
access point
fixed
terminal
application
TCP
802.11 PHY
802.11 MAC
IP
802.3 MAC
802.3 PHY
application
TCP
802.3 PHY
802.3 MAC
IP
802.11 MAC
802.11 PHY
LLC
infrastructure
network
LLC LLC
802.11 - Layers and functions
PLCP Physical Layer Convergence Protocol
clear channel assessment signal
(carrier sense)
PMD Physical Medium Dependent
modulation, coding
PHY Management
channel selection, MIB
Station Management
coordination of all management
functions
PMD
PLCP
MAC
LLC
MAC Management
PHY Management
MAC
access mechanisms, fragmentation,
encryption
MAC Management
synchronization, roaming, MIB, power
management
P
H
Y
D
L
C
S
t
a
t
i
o
n
M
a
n
a
g
e
m
e
n
t
802.11 - Physical layer
3 versions: 2 radio (typ. 2.4 GHz), 1 IR
data rates 1 or 2 Mbit/s
FHSS (Frequency Hopping Spread Spectrum)
spreading, despreading, signal strength, typ. 1 Mbit/s
min. 2.5 frequency hops/s (USA), two-level GFSK modulation
DSSS (Direct Sequence Spread Spectrum)
DBPSK modulation for 1 Mbit/s (Differential Binary Phase Shift
Keying), DQPSK for 2 Mbit/s (Differential Quadrature PSK)
preamble and header of a frame is always transmitted with 1
Mbit/s, rest of transmission 1 or 2 Mbit/s
chipping sequence: +1, -1, +1, +1, -1, +1, +1, +1, -1, -1, -1
(Barker code)
max. radiated power 1 W (USA), 100 mW (EU), min. 1mW
Infrared
850-950 nm, diffuse light, typ. 10 m range
carrier detection, energy detection, synchonization
FHSS PHY packet format
synchronization SFD PLW PSF HEC payload
PLCP preamble PLCP header
80 16 12 4 16 variable
bits
Synchronization
synch with 010101... pattern
SFD (Start Frame Delimiter)
0000110010111101 start pattern
PLW (PLCP_PDU Length Word)
length of payload incl. 32 bit CRC of payload, PLW < 4096
PSF (PLCP Signaling Field)
data of payload (1 or 2 Mbit/s)
HEC (Header Error Check)
CRC with x
16
+x
12
+x
5
+1
DSSS PHY packet format
synchronization SFD signal service HEC payload
PLCP preamble PLCP header
128 16 8 8 16 variable
bits
length
16
Synchronization
synch., gain setting, energy detection, frequency offset compensation
SFD (Start Frame Delimiter)
1111001110100000
Signal
data rate of the payload (0A: 1 Mbit/s DBPSK; 14: 2 Mbit/s DQPSK)
Service Length
future use, 00: 802.11 compliant length of the payload
HEC (Header Error Check)
protection of signal, service and length, x
16
+x
12
+x
5
+1
802.11 - MAC layer I - DFWMAC
Traffic services
Asynchronous Data Service (mandatory)
exchange of data packets based on best-effort
support of broadcast and multicast
Time-Bounded Service (optional)
implemented using PCF (Point Coordination Function)
Access methods
DFWMAC-DCF CSMA/CA (mandatory)
collision avoidance via randomized back-off mechanism
minimum distance between consecutive packets
ACK packet for acknowledgements (not for broadcasts)
DFWMAC-DCF w/ RTS/CTS (optional)
Distributed Foundation Wireless MAC
avoids hidden terminal problem
DFWMAC- PCF (optional)
access point polls terminals according to a list
802.11 - MAC layer II
Priorities
defined through different inter frame spaces
no guaranteed, hard priorities
SIFS (Short Inter Frame Spacing)
highest priority, for ACK, CTS, polling response
PIFS (PCF IFS)
medium priority, for time-bounded service using PCF
DIFS (DCF, Distributed Coordination Function IFS)
lowest priority, for asynchronous data service
t
medium busy
SIFS
PIFS
DIFS DIFS
next frame contention
direct access if
medium is free DIFS
802.11 MAC
The basic services provided by the MAC layer
are the mandatory asynchronous data service
and an optional time-bounded service.
802.11 only offers the asynchronous service in
ad-hoc network
both service types can be offered using an
infrastructure-based network
the access point coordinates medium access
three basic access mechanisms
1. Basic method based on a version of CSMA/CA
2. Method avoiding the hidden terminal
problem
3. Contention free polling method for time-
bounded service
The first two methods are also summarized as
distributed coordination function (DCF)
the third method is called point coordination
function (PCF)
The MAC mechanisms are also called
distributed foundation wireless medium access
control (DFWMAC).
Medium access and inter-frame spacing
Short inter-frame spacing (SIFS): The shortest waiting time
for medium access (so the highest priority) is defined for short
control messages, such as acknowledgements of data packets
or polling responses .eg. For DSSS SIFS is 10 s and for FHSS it
is 28 s
PCF inter-frame spacing (PIFS): A waiting time between DIFS
and SIFS (and thus a medium priority) is used for a time-
bounded service.AP during polling the nodes wait PIFS
DCF inter-frame spacing (DIFS): This parameter denotes the
longest waiting time and has the lowest priority for medium
access.
Basic DFWMAC-DCF using CSMA/CA
a random access scheme with carrier sense
collision avoidance through random back off
Mechanism
If the medium is idle for at least the duration of
DIFS , a node can access the medium at once.
Results in less delay under light load if many
nodes try additional mechanism is needed
Many node are tying to access
medium
If the medium is busy, nodes have to wait for
the duration of DIFS then enter in to
contention phase
After this each node chooses a random back
off time
The node continues to sense the medium
If again the medium is busy ,he lost his cycle
and has to wait for next chance
If the waiting time for a node is over and the
medium is still idle, the node can access the
medium immediately
To provide fairness, IEEE 802.11 adds a backoff
timer.
each node selects a random waiting time,
If a certain station does not get access
it stops its backoff timer , starts the counter
again in next cycle.
five stations trying to send a packet at the
marked points in time
Station3 has the first request to send a packet
The station senses the medium, waits for DIFS
and accesses the medium, i.e.,sends the
packet
Station1, station2, and station5 have to wait at
least until the medium is idle for DIFS again
after station3 has stopped sending.
Now all three stations choose a backoff time
within the contention window
While above process describes the complete
access mechanism for broadcast frames,
additional feature is provided by the standard
for unicast data transfer
In unicast the receiver answers directly with
an acknowledgement (ACK)
receiver accesses the medium after waiting for
a duration of SIFS
DFWMAC-DCF with RTS/CTS extension
802.11 node has to implement the functions
to react on reception of RTS/CTS control
packets
The RTS packet includes the receiver and the
duration of the whole data transmission(Data
+ Ack time)
Every node receiving this RTS, set its net
allocation vector (NAV
Which specifies the earliest point at which
the station can try to access the medium
again.
Reciever answers with a CTS after waiting SIF
all stations receiving CTS adjust their NAV
fragmentation mode
bit error rates in transmission that are typically several orders of
magnitude higher than, e.g., fiber optics
Probability of error is high in longer frames
So the frames are fragmented in to small fragments which reduces the
frame error rate
First fragments contains the duration of the next fragment with ack time
So the other nodes can update the NAV
DFWMAC PCF with polling
(almost never used)
The two previous methods cannot guarantee a maximum delay or
minimum bandwidth
PCF provides time-bounded service
It requires an access point that control medium access and polls the single
nodes
Ad Hoc network cant use this function so it provides only best-effort
service
The point coordinator in the access point splits the access time into super
frame periods.
A super frame comprises an contention-free period and a contention
period
If only PCF is used and polling is distributed evenly, the bandwidth is also
distributed evenly static centrally controlled TDMA with TDD
transmission
Much overhead if nodes have nothing to send.
t
stations
NAV
wireless
stations
point
coordinator
D
3
NAV
PIFS
D
4
U
4
SIFS
SIFS
CF
end
contention
period
contention free period
t
2
t
3
t
4
PIFS
stations
NAV
wireless
stations
point
coordinator
D
1
U
1
SIFS
NAV
SIFS
D
2
U
2
SIFS
SIFS
SuperFrame
t
0
medium busy
t
1
802.11 - Frame format
Types: control frames, management frames, data frames
Sequence numbers
important against duplicated frames due to lost ACKs
Addresses
receiver, transmitter (physical), BSS identifier, sender/receiver (logical)
Miscellaneous
Duration (to set the NAV), checksum, frame control, data
Frame
Control
Duration/
ID
Address
1
Address
2
Address
3
Sequence
Control
Address
4
Data CRC
2
2 6 6 6 6 2 4 0-2312
bytes
Protocol
version
Type Subtype
To
DS
More
Frag
Retry
Power
Mgmt
More
Data
WEP
2 2 4 1
From
DS
1
Order
bits 1 1 1 1 1 1
Frame Control
Protocol version: 2 bits
Type (management 00, control 01, data 10)
Subtype (e.g. Management- association 0000, beacon 100
Control RTS 1011, CTS 1100)
More fragments: 1 if another fragment to follow
Retry: 1 if retransmission of an earlier frame
Power Management: 1 if the station will go to power save mode
More Data: A sender has more data to send
Wired Equivalent Privacy (WEP): Standard security mechanism applied
Order: frame must be processed in strict order
Frame
Control
Duration/
ID
Address
1
Address
2
Address
3
Sequence
Control
Address
4
Data CRC
2
2 6 6 6 6 2 4 0-2312
bytes
Protocol
version
Type Subtype
To
DS
More
Frag
Retry
Power
Mgmt
More
Data
WEP
2 2 4 1
From
DS
1
Order
bits 1 1 1 1 1 1
MAC address format
scenario to DS from
DS
address 1 address 2 address 3 address 4
ad-hoc network 0 0 DA SA BSSID -
infrastructure
network, from AP
0 1 DA BSSID SA -
infrastructure
network, to AP
1 0 BSSID SA DA -
infrastructure
network, within DS
1 1 RA TA DA SA
DS: Distribution System
AP: Access Point
DA: Destination Address
SA: Source Address
BSSID: Basic Service Set Identifier
RA: Receiver Address
TA: Transmitter Address
Network Protocols/Mobile IP
Motivation for Mobile IP
Transparency
mobile end-systems keep their IP address
continuation of communication after interruption of link possible
point of connection to the fixed network can be changed
Compatibility
support of the same layer 2 protocols as IP
no changes to current end-systems and routers required
mobile end-systems can communicate with fixed systems
Security
authentication of all registration messages
Efficiency and scalability
only little additional messages to the mobile system required (connection
typically via a low bandwidth radio link)
world-wide support of a large number of mobile systems in the whole Internet
Terminology
Mobile Node (MN)
system (node) that can change the point of connection
to the network without changing its IP address
Home Agent (HA)
system in the home network of the MN, typically a router
registers the location of the MN, tunnels IP datagrams to the COA
Foreign Network :is current subnet of the MN visits and which s not a
home network
Foreign Agent (FA)
system in the current foreign network of the MN, typically a router
forwards the tunneled datagrams to the MN, typically also the default
router for the MN
Care-of Address (COA)
address of the current tunnel end-point for the MN (at FA or MN)
actual location of the MN from an IP point of view
can be chosen, e.g., via DHCP
Correspondent Node (CN)
communication partner
IP packet Delivery
CN
router
HA
router
FA
Internet
router
1.
2.
3.
home
network
MN
foreign
network
4.
CN
router
HA
router
FA
Internet
router
home
network
MN
foreign
network
COA
Network integration
Agent Advertisement
HA and FA periodically send advertisement messages into their physical
subnets
MN listens to these messages and detects, if it is in the home or a foreign
network (standard case for home network)
MN reads a COA from the FA advertisement messages
Registration (always limited lifetime!)
MN signals COA to the HA via the FA, HA acknowledges via FA to MN
these actions have to be secured by authentication
Advertisement
HA advertises the IP address of the MN (as for fixed systems), i.e. standard
routing information
routers adjust their entries, these are stable for a longer time (HA
responsible for a MN over a longer period of time)
packets to the MN are sent to the HA,
independent of changes in COA/FA
type = 16
length = 6 + 4 * #COAs
R: registration required
B: busy, no more registrations
H: home agent
F: foreign agent
M: minimal encapsulation
G: GRE encapsulation
r: =0, ignored (former Van Jacobson compression)
T: FA supports reverse tunneling
reserved: =0, ignored
Agent advertisement
preference level 1
router address 1
#addresses
type
addr. size lifetime
checksum
COA 1
COA 2
type = 16 sequence number
length
0
7 8 15 16 31 24 23
code
preference level 2
router address 2
. . .
registration lifetime
. . .
R B H F M G r reserved T
ICMP part:
Type -9
Code: 0(non mobile nodes)
16 for mobile traffic
#address:no of addresses
Registration
t
MN
HA
t
MN
FA HA
Mobile IP registration
request
home agent
home address
type = 1 lifetime
0
7 8 15 16 31 24 23
T x
identification
COA
extensions . . .
S B D M G r
S: simultaneous bindings
B: broadcast datagrams
D: decapsulation by MN
M mininal encapsulation
G: GRE encapsulation
r: =0, ignored
T: reverse tunneling requested
x: =0, ignored
Mobile IP registration
reply
home agent
home address
type = 3 lifetime
0
7 8 15 16 31
code
identification
extensions . . .
Example codes:
registration successful
0 registration accepted
1 registration accepted, but simultaneous mobility bindings unsupported
registration denied by FA
65 administratively prohibited
66 insufficient resources
67 mobile node failed authentication
68 home agent failed authentication
69 requested Lifetime too long
registration denied by HA
129 administratively prohibited
131 mobile node failed authentication
133 registration Identification mismatch
135 too many simultaneous mobility bindings
Encapsulation
original IP header original data
new data new IP header
outer header inner header original data
Encapsulation I
Encapsulation of one packet into another as
payload
IP-in-IP-encapsulation,
minimal encapsulation
GRE (Generic Routing encapsulation)
IP-in-IP-encapsulation (mandatory, RFC 2003)
tunnel between HA and COA
length DS (TOS) ver. IHL
Care-of address COA
IP address of HA
TTL
IP identification
IP-in-IP IP checksum
flags fragment offset
IP address of MN
IP address of CN
TTL
IP identification
lay. 4 prot. IP checksum
flags fragment offset
length DS (TOS) ver. IHL
TCP/UDP/ ... payload
Ver-IP version 4
IHL-internet header length denotes length of the outer header
DS(TOS)-just copied form the inner header
Length covers the complete encapsulated packet
TTL no special meaning
IP-in-IP denotes the type of encapsulation
IP address of HA(tunnel entry address)
COA (tunnel exit point)
Encapsulation II
Minimal encapsulation (optional)
avoids repetition of identical fields
e.g. TTL, IHL, version, DS (RFC 2474, old: TOS)
only applicable for non fragmented packets, no space
left for fragment identification
care-of address COA
IP address of HA
TTL
IP identification
min. encap. IP checksum
flags fragment offset
length DS (TOS) ver. IHL
IP address of MN
original sender IP address (if S=1)
S lay. 4 protoc. IP checksum
TCP/UDP/ ... payload
reserved
Generic Routing Encapsulation
The previous two encapsulation works only for
IP.
The GRE allows encapsulation of packets of
one protocol suit into payload of a packet of
another protocol suite
original
header
original data
new data new header
outer header
GRE
header
original data
original
header
Generic Routing Encapsulation
Care-of address COA
IP address of HA
TTL
IP identification
GRE IP checksum
flags fragment offset
length DS (TOS) ver. IHL
IP address of MN
IP address of CN
TTL
IP identification
lay. 4 prot. IP checksum
flags fragment offset
length DS (TOS) ver. IHL
TCP/UDP/ ... payload
routing (optional)
sequence number (optional)
key (optional)
offset (optional) checksum (optional)
protocol rec. rsv. ver. C R K S s
RFC 1701
Optimization of packet forwarding
Problem: Triangular Routing
sender sends all packets via HA to MN
higher latency and network load
Solutions
sender learns the current location of MN
direct tunneling to this location
HA informs a sender about the location of MN
big security problems!
Change of FA
packets on-the-fly during the change can be lost
new FA informs old FA to avoid packet loss, old FA now forwards remaining
packets to new FA
this information also enables the old FA to release resources for the MN
Binding Request: Any node needs the location of MN can send
binding request to the HA.If MN allows HA can reveal the
location by sending binding update
Binding Update: send by HA to CN.It contains the fixed IP
address of the MN and the COA.It can request the ack.
Binding Acknowledgement: on receiving binding update node
replies with ack
Binding Warning: If a node decapsulates a packet for an
MN,but it is not the current FA for this MN,This node sends a
binding warning
Change of foreign agent
CN HA FA
old
FA
new
MN
MN changes
location
t
Data
Data
Data
Update
ACK
Data
Data
Registration
Update
ACK
Data
Data
Data
Warning
Request
Update
ACK
Data
Data
Reverse tunneling (RFC 3024, was:
2344)
Internet
receiver
FA
HA
MN
home network
foreign
network
sender
3
2
1
1. MN sends to FA
2. FA tunnels packets to HA
by encapsulation
3. HA forwards the packet to the
receiver (standard case)
CN
Firewalls:
Multicast:foreign network cannot transmit
multi cast packets in a way like the home
network does
TTL:TTL might be low enough so that no
packet is transmitted outside a certain region.
DHCP: Dynamic Host Configuration
Protocol
Application
simplification of installation and maintenance of networked
computers
supplies systems with all necessary information, such as IP address,
DNS server address, domain name, subnet mask, default router etc.
enables automatic integration of systems into an Intranet or the
Internet, can be used to acquire a COA for Mobile IP
Client/Server-Model
the client sends via a MAC broadcast a request to the DHCP server
(might be via a DHCP relay)
client relay
client server
DHCPDISCOVER
DHCPDISCOVER
DHCP - protocol mechanisms
server
(not selected)
client
server
(selected)
initialization
collection of replies
selection of configuration
initialization completed
release
confirmation of
configuration
delete context
determine the
configuration
DHCPDISCOVER
DHCPOFFER
DHCPREQUEST
(reject)
DHCPACK
DHCPRELEASE
DHCPDISCOVER
DHCPOFFER
DHCPREQUEST
(options)
determine the
configuration
You might also like
- VHF Signal PropagationDocument18 pagesVHF Signal PropagationYacine KhlilNo ratings yet
- Wireless TransmissionDocument50 pagesWireless TransmissionRithulRaphelNo ratings yet
- Pirate Radio and Video: Experimental Transmitter ProjectsFrom EverandPirate Radio and Video: Experimental Transmitter ProjectsRating: 5 out of 5 stars5/5 (1)
- Modulation: Presented By-Nidhi Baranwal Mca 6 SemDocument30 pagesModulation: Presented By-Nidhi Baranwal Mca 6 SemDr. M. Karthigai Pandian Asso Prof ICENo ratings yet
- Aviation Electronics Technician 1 PDFDocument334 pagesAviation Electronics Technician 1 PDFIulian LoghinNo ratings yet
- EC1352 Antenna Wave PropagationDocument44 pagesEC1352 Antenna Wave Propagationjackdbomber100% (7)
- 05-Signal Encoding TechniquesDocument75 pages05-Signal Encoding Techniqueskazim razaNo ratings yet
- Super Dungeon Explore Rulebook OverviewDocument38 pagesSuper Dungeon Explore Rulebook OverviewAndy ClarkNo ratings yet
- Space Communication: Key ConceptsDocument17 pagesSpace Communication: Key ConceptsKashyap PatelNo ratings yet
- Wireless TransmissionDocument147 pagesWireless TransmissionAshraf EltholthNo ratings yet
- Lecture23 1233854096875992 3Document41 pagesLecture23 1233854096875992 3Mohammed RizwanNo ratings yet
- Frequencies For Communication: Frequency and Wave LengthDocument109 pagesFrequencies For Communication: Frequency and Wave LengthbibingeorgeNo ratings yet
- Wireless Data Communication Networks: Fundamentals of Wireless CommunicationsDocument37 pagesWireless Data Communication Networks: Fundamentals of Wireless Communicationsclaude bangoNo ratings yet
- Unit VDocument39 pagesUnit Vsnkarthik35No ratings yet
- Cwna Guide To Wireless Lans, Second Edition: Chapter ThreeDocument54 pagesCwna Guide To Wireless Lans, Second Edition: Chapter Threekoppala47No ratings yet
- WNLecture 2Document6 pagesWNLecture 2sarahz_2009No ratings yet
- William Stallings Data and Computer Communications 7 EditionDocument37 pagesWilliam Stallings Data and Computer Communications 7 EditionVeeravasantharao BattulaNo ratings yet
- Data TransmissionDocument96 pagesData Transmission2003315No ratings yet
- 04 TransmissionMediaDocument37 pages04 TransmissionMediaNikhil NayyarNo ratings yet
- C02 Wireless TransmissionDocument41 pagesC02 Wireless TransmissionSenthil RNo ratings yet
- Point To PointmicrowaveDocument83 pagesPoint To PointmicrowavesomcableNo ratings yet
- lecture_2 and 3 winter_2023_2024Document34 pageslecture_2 and 3 winter_2023_2024ritamonde4No ratings yet
- Wireless TransmissionDocument147 pagesWireless Transmissionepc_kiranNo ratings yet
- Unit-7-Wireless-Modulation-Techniques-And-Hardware Malini MamDocument40 pagesUnit-7-Wireless-Modulation-Techniques-And-Hardware Malini MamRoopa NayakNo ratings yet
- Point To Point Microwave TransmissionDocument83 pagesPoint To Point Microwave Transmissionfatmirz9448No ratings yet
- Signals: Types, Structures, and Transmission ImpairmentsDocument28 pagesSignals: Types, Structures, and Transmission ImpairmentsRahul AryanNo ratings yet
- Modulation Schemes: EEE 352 Analog Communication Systems Mansoor Khan EE Dept. CIIT Islamabad CampusDocument22 pagesModulation Schemes: EEE 352 Analog Communication Systems Mansoor Khan EE Dept. CIIT Islamabad Campusali_rehman87No ratings yet
- Week01 FundamentalsDocument43 pagesWeek01 FundamentalsSara El-GendyNo ratings yet
- Lecture 1Document35 pagesLecture 1Asad KhanNo ratings yet
- Lecture 2Document35 pagesLecture 2Asad KhanNo ratings yet
- ICASA Fundamental Skills Training Module: Spectrum PrinciplesDocument66 pagesICASA Fundamental Skills Training Module: Spectrum PrinciplesWilliam StuckeNo ratings yet
- Point To Point Microwave PDFDocument83 pagesPoint To Point Microwave PDFpr3m4n100% (1)
- Wirless ChannelDocument28 pagesWirless ChannelFahim IqbalNo ratings yet
- GSM Based Cellular - RF Level 2Document117 pagesGSM Based Cellular - RF Level 2Isaiah UnidaNo ratings yet
- Data and Computer Communications ExplainedDocument44 pagesData and Computer Communications ExplainedSaurav SenNo ratings yet
- Basics of Wireless Communications: Modulation, Multiplexing & LimitationsDocument15 pagesBasics of Wireless Communications: Modulation, Multiplexing & Limitationsgashawbeza tayeNo ratings yet
- Mobile Radio Propagation EffectsDocument63 pagesMobile Radio Propagation EffectsRutuja VartaleNo ratings yet
- Wireless Issues ExplainedDocument42 pagesWireless Issues ExplainedlifeNo ratings yet
- Chap 2Document38 pagesChap 2Maha IbrahimNo ratings yet
- Antennas PropagationDocument48 pagesAntennas Propagationradhakodirekka8732No ratings yet
- Unit1 (WIRELESSS Communication)Document69 pagesUnit1 (WIRELESSS Communication)Akshat GiriNo ratings yet
- Pulse Modulation and Multiplexing Techniques PDFDocument58 pagesPulse Modulation and Multiplexing Techniques PDFamrutha ammuNo ratings yet
- WDMWDMDocument40 pagesWDMWDMAbrar AhmadNo ratings yet
- Chapter 3 - Physical LayerDocument46 pagesChapter 3 - Physical Layerhenok metaferiaNo ratings yet
- Analog Communication: Gokaraju Rangaraju Institute of Engineering & Technology (Autonomous)Document51 pagesAnalog Communication: Gokaraju Rangaraju Institute of Engineering & Technology (Autonomous)HimaBindu ValivetiNo ratings yet
- Lecture 1Document26 pagesLecture 1কাশী নাথNo ratings yet
- Communication SystemsDocument15 pagesCommunication SystemsMuhammad AdeelNo ratings yet
- Unit 2 Modulation Demodulation Ppt (1)Document88 pagesUnit 2 Modulation Demodulation Ppt (1)vaishnavi biradarNo ratings yet
- Wireless Ad Hoc and Sensor Networks FundamentalsDocument374 pagesWireless Ad Hoc and Sensor Networks FundamentalsMadhavan Sam0% (1)
- Multiple Antenna Transmission & Reception: Chapter 3 of MODULE - 2Document35 pagesMultiple Antenna Transmission & Reception: Chapter 3 of MODULE - 2PradeepNo ratings yet
- Chapter 4 Transmission Media: Design FactorsDocument5 pagesChapter 4 Transmission Media: Design Factorssaumya04No ratings yet
- Fundamentals of Communications W SLIDESDocument47 pagesFundamentals of Communications W SLIDESShomakhmood BotirovNo ratings yet
- Fundamentals of CommunicationsDocument47 pagesFundamentals of CommunicationsKaniz Fatima LizaNo ratings yet
- Line Coding Techniques ExplainedDocument65 pagesLine Coding Techniques ExplainedGaneshVenkatachalamNo ratings yet
- IMC Unit 3Document25 pagesIMC Unit 3PJ DudeNo ratings yet
- CS 5813: Principles of Wireless Networks: Tingting Chen Department of Computer Science Fall 2013Document43 pagesCS 5813: Principles of Wireless Networks: Tingting Chen Department of Computer Science Fall 2013Sowmya KondapuramNo ratings yet
- Transmission MediaDocument39 pagesTransmission MediaKeyur MahantNo ratings yet
- 2 - Wireless ChannelDocument20 pages2 - Wireless Channelzco bilalNo ratings yet
- Chapter 3-Wireless Network PrinciplesDocument84 pagesChapter 3-Wireless Network PrinciplesEbisa Chemeda100% (1)
- Chapter 6Document39 pagesChapter 6Dhruvi PadmaniNo ratings yet
- Lec10 PDFDocument29 pagesLec10 PDFNaresh BirudalaNo ratings yet
- Link Budget MaximDocument10 pagesLink Budget MaximAkshay S NNo ratings yet
- My ReportDocument41 pagesMy ReportNishant ShahNo ratings yet
- Microwave Path Design ConsiderationsDocument6 pagesMicrowave Path Design Considerationssayys1390No ratings yet
- 4790 SeriesDocument124 pages4790 Serieskass_ecsNo ratings yet
- What is Microwave? Properties, Merits, Demerits and ApplicationsDocument2 pagesWhat is Microwave? Properties, Merits, Demerits and ApplicationsTeferi LemmaNo ratings yet
- Extended Cell ConfigurationDocument31 pagesExtended Cell Configurationrfabre76No ratings yet
- Radio Wave PropagationDocument81 pagesRadio Wave PropagationJoseph JeremyNo ratings yet
- Digital Com theory-Compiled-P.Nagaraju PDFDocument59 pagesDigital Com theory-Compiled-P.Nagaraju PDFprashanth_02No ratings yet
- Optical Properties of Radio WavesDocument5 pagesOptical Properties of Radio WavesJOSHUA NEIL CARIGONo ratings yet
- Microwave Link LOS SurveyDocument1 pageMicrowave Link LOS SurveySuneth MendisNo ratings yet
- 10Document13 pages10Henry TangNo ratings yet
- R Rec P.1812 1 200910 S!!PDF eDocument31 pagesR Rec P.1812 1 200910 S!!PDF emauweberNo ratings yet
- GPS Antenna Design and Performance Advancements: The Trimble ZephyrDocument10 pagesGPS Antenna Design and Performance Advancements: The Trimble ZephyrLiang ShaoNo ratings yet
- Final Microwave AntennaDocument13 pagesFinal Microwave AntennaHanilavMoraNo ratings yet
- Gloomhaven FAQDocument28 pagesGloomhaven FAQarkcaverNo ratings yet
- Chapter 18: Terrestrial Microwave Communication Systems: Multiple ChoiceDocument5 pagesChapter 18: Terrestrial Microwave Communication Systems: Multiple ChoiceJoy HicbanNo ratings yet
- Electronic Communication Systems - Kennedy and DavisDocument7 pagesElectronic Communication Systems - Kennedy and DavisJojet Tarantan100% (1)
- Cellular Mobile CommunicationDocument22 pagesCellular Mobile CommunicationChandraSudeepNo ratings yet
- Unit 8: 1. Derive The Fundamental Equation For Free Space Propagation? AnsDocument11 pagesUnit 8: 1. Derive The Fundamental Equation For Free Space Propagation? AnsRamya RammiNo ratings yet
- Signal Propagation BasicsDocument24 pagesSignal Propagation BasicsZeffrey AletaNo ratings yet
- Iec TS 61000-5-8-2009Document32 pagesIec TS 61000-5-8-2009Venkataramanan SNo ratings yet
- ASSMENT7Document2 pagesASSMENT7satoruheineNo ratings yet
- RF Drive Test Tutorial Demo VersionDocument32 pagesRF Drive Test Tutorial Demo Versionanupamkhanna100% (5)
- CBSE Class 12th PCM Sample EbookDocument70 pagesCBSE Class 12th PCM Sample EbookmisostudyNo ratings yet