Professional Documents
Culture Documents
Industry Report - 1
Uploaded by
api-3702531Original Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Industry Report - 1
Uploaded by
api-3702531Copyright:
Available Formats
MARKET AN ALYSIS
www.idc.com
Worldwide Security Software 2004–2008 Forecast and
2003 Vendor Shares
F.508.935.4015
Brian E. Burke Charles J. Kolodgy
Christian A. Christiansen Sally Hudson
IDC OPINION
P.508.872.8200
Security software spending remains a top priority in many organizations, and the
security software market achieved $8.4 billion in revenue in 2003, representing 17.5%
growth over 2002. IDC currently forecasts this market to reach $16.3 billion in
revenue in 2008, representing a compound annual growth rate (CAGR) of 14%.
Highlights are as follows:
Global Headquarters: 5 Speen Street Framingham, MA 01701 USA
! The growing reliance on IT for corporate operations and increasing government
and industry regulation is elevating security policy, adherence to best practices,
and measurement to a critical component of corporate governance. To meet
these needs, security and vulnerability management (SVM) products are being
released that can assist enterprises in handling policy creation, compliance
measurements and audits, and reporting.
! The costs associated with integrating heterogeneous authentication and
authorization systems have driven demand for a more comprehensive and
integrated identity and access management (IAM) solution that would help to not
only reduce costs, but also increase security and productivity.
! Viruses and worms continue to be the most serious threat facing corporations.
However, new threats like spyware and phishing attacks are quickly moving up
the priority list of corporate security concerns.
! Intrusion detection and prevention (ID&P) technology remains an important
component of an in-depth defense enterprise security program. ID&P products
have been gaining acceptance as a way to eliminate Internet worms and
maintain control over the internal working of enterprise networks and
applications.
! The enterprise software firewall market continues to shrink as more vendors
move to a pure appliance distribution model. As the network perimeter becomes
less defined, corporations will turn to desktop firewalls.
Filing Information: December 2004, IDC #32391, Volume: 1, Tab: Markets
Security Products: Market Analysis
T ABLE OF CONT ENT S
In This Study 1
Executive Summary.................................................................................................................................. 1
Methodology ............................................................................................................................................. 1
Security Software Market Definition.......................................................................................................... 1
S i t u a t i o n O ve r v i e w 5
Key Trends ............................................................................................................................................... 6
Leading Vendors in 2003.......................................................................................................................... 9
Future Outlook 16
Forecast and Assumptions ....................................................................................................................... 16
Essential Guidance 24
Learn More 25
Related Research ..................................................................................................................................... 25
#32391 ©2004 IDC
LIST OF T ABLES
P
1 Worldwide Security Software Revenue by Market, 2003–2008.................................................... 16
2 Worldwide Security Software Revenue by Region, 2003–2008 ................................................... 17
3 Key Forecast Assumptions for the Worldwide Security Software Market, 2004–2008 ................. 17
©2004 IDC #32391
LIST OF FIGURES
P
1 Threats to Enterprise Security...................................................................................................... 5
2 Worldwide Security Software Revenue for Top 10 Vendors, 2003............................................... 9
3 Worldwide Secure Content Management Software Revenue for Top 10 Vendors, 2003............. 10
4 Worldwide Identity and Access Management Software Revenue for Top 10 Vendors, 2003....... 11
5 Worldwide Security and Vulnerability Management Software Revenue for Top 10 Vendors,
2003 ............................................................................................................................................. 12
6 Worldwide Intrusion Detection and Prevention Software Revenue for Top 10 Vendors, 2003..... 13
7 Worldwide Firewall/VPN Software Revenue for Top 10 Vendors, 2003....................................... 14
8 Worldwide Other Security Software Revenue for Top 10 Vendors, 2003..................................... 15
#32391 ©2004 IDC
IN THIS STUDY
Executive Summary
This IDC study examines the worldwide security software market for the period 2003–
2008. Worldwide market sizes and trends are provided for 2003, and a five-year
growth forecast for this market is shown for 2004–2008. Vendor competitive analysis,
with vendor revenues and market shares of the leading vendors, is provided for 2003.
This study also identifies the characteristics that vendors will need to be successful in
the future.
Methodology
Please note the following:
! The information contained in this study was derived from the IDC Software
Market Forecaster database as of July 6, 2004.
! Total software revenue is defined as license revenue plus subscription
maintenance fees plus other software function–related services fees such as the
implicit or stated value of software included in an application service provider's
(ASP's) or other hosted software arrangement.
! IDC's revenue information for companies and software markets is based on
recognized revenue as defined in U.S. practice rather than on bookings. IDC
bases its reporting of, and forecasts for, the software market based on revenue
as defined by GAAP.
! All numbers in this document may not be exact due to rounding.
For more information on IDC's software definitions and methodology, see IDC's
Software Taxonomy, 2004 (IDC #30838, February 2004).
Security Software Market Definition
Secure Content Management
SCM is a market that reflects corporate customers' need for policy-based Internet
management tools that manage Web content, messaging security, virus protection,
and malicious code. SCM is a superset of three specific product areas:
! Antivirus software identifies and/or eliminates harmful software and macros.
Antivirus software scans hard drives, email attachments, floppy disks, Web
pages, and other types of electronic traffic (e.g., instant messaging [IM] and short
message service [SMS]) for any known or potential viruses, malicious code,
trojans, or spyware.
©2004 IDC #32391 1
! Web filtering software is used to screen and exclude from access or availability
Web pages that are deemed objectionable or not business related. Web filtering
is used by corporations to enforce corporate policy as well as by schools and
universities and home computer owners (for parental controls).
! Messaging security software is used to monitor, filter, and/or block messages
from different messaging applications (e.g., email, IM, SMS, and peer to peer)
containing spam, company confidential information, and objectionable content.
Messaging security is also used by certain industries to enforce compliance with
privacy regulations (e.g., HIPAA, Gramm-Leach-Bliley, and SEC) by monitoring
electronic messages for compliance violations. This market also includes secure
(encrypted) email.
Firewall/VPN Software
The firewall/VPN market consists of software that identifies and blocks access to
certain applications and data. These products may also include virtual private network
(VPN) encryption as an option. Software firewalls fall into two distinct categories:
enterprise and desktop. The desktop firewall is itself divided into corporate and
consumer categories. In more detail:
! Enterprise firewall/VPN software is robust enterprise-class software that
inspects IP packets as they enter a network. The inspection is to determine if the
packet conforms to a policy (i.e., an acceptable protocol). The result of the
inspection will be to allow the packet or to reject the packet.
! Desktop firewalls cost less than $100 and are used to determine if a given IP
packet should be passed to the desktop device. Generally, the products are used
to control what desktop applications can communicate with the Internet. They are
also evolving to control the functionality of the Web browser. The desktop firewall
market is divided into those sold to the corporate customer and those sold to
consumers.
! Corporate desktop firewalls are generally used to maintain the corporate
desktop security policy. Many of the corporate desktop firewalls incorporate
remote management and policy. Through the use of a central management
console, enterprises or service providers can manage the firewall to ensure that it
remains within a stated policy, receives software updates, and has virtual private
network management. Revenue in this market includes any management servers
used to serve the corporate policy.
! Consumer desktop firewalls are generally used to protect home and small
business offices that have a high-speed, always-on connection through a cable
or DSL modem. These products have the same technology as those of the
corporate desktop firewall, but remote management of these products is not
possible.
2 #32391 ©2004 IDC
Intrusion Detection and Prevention Software
! Intrusion detection products provide continuous monitoring of devices or
networks and react to malicious activity. A device or agent on a network or a
system, respectively, will compare current activity with a list of signatures known
to represent malicious activity, or it will use other detection methods such as
protocol analysis, anomaly, behavioral, or heuristics to discover unauthorized
network activity. Intrusion detection products are passive systems that do not
interact directly with the datastream or application calls. They can direct other
security products such as firewalls to activate a preestablished automated
response to policy-violating activities.
! Intrusion prevention is a subset of intrusion detection because you must be
able to detect before you can prevent. Prevention products perform the same
tasks as detection products; however, to qualify as a prevention product, they
must be inline (have direct access to traffic and commands) and have the ability
to proactively prohibit malicious activity. Although prevention products are
considerably different in function than pure intrusion detection, the two categories
are being tracked together because they compete for the same budget.
Security and Vulnerability Management Software
(SVM) is a comprehensive set of solutions that includes the following:
! Security information and event management (SIM/SEM): Security event
management collects and correlates events, and security information
management adds security intelligence to the mix, provides proactive alerts, and
suggests fixes. Vendors in this market include Computer Associates, NetIQ, IBM,
netForensics, ArcSight, Symantec, eSecurity, Network Intelligence, OpenService,
Intellitactics, and Guardednet.
! Patch and remediation management (PRM): PRM solutions automate or
semiautomate the process of discovering systems on the network, identifying
missing patches and installing those patches across the enterprise immediately
or on a scheduled basis. Vendors in this market include Patchlink, Shavlik, St.
Bernard Software, Computer Associates, NetIQ, Microsoft, and Citadel Security.
! Policy and compliance management (PCM): Policy and compliance products
are designed to allow organizations to quickly create, assess, update, and, in
some cases, enforce security policy. PCM products generally provide best
practices and regulation templates to help create and measure policy for
compliance. Vendors in this market include IBM, NetIQ, Consul Risk
Management, BindView, Citadel Security Software, Intellitactics, Meta Security
Group, Preventsys, Polivec, Pedestal Software, and Securify.
! Security systems and configuration management: Security systems and
configuration management products are established products that contain
security elements and include vendors such as HP OpenView, Computer
Associates (Unicenter), IBM/Tivoli, BMC Software, Evidian, VeriSign, Cisco,
Ubizen, Utimaco, Sun Microsystems, Enterasys, Candle, and MicroMuse. These
©2004 IDC #32391 3
security solutions have traditionally dominated the security management market
by leveraging the strength of their network and system management products
into this area.
! Network forensics: Network forensics solutions capture real-time network data
and identify how business assets are affected by network exploits, internal data
theft, and security or HR policy violations. Vendors in this market include
Guidance Software, Computer Associates, and Network Intelligence.
! Vulnerability assessment: Vulnerability assessment products are batch-level
products that determine the configuration, structure, security attributes, network
user accounts, directories, servers, workstations, and other devices. This
information is compared with a database of known security holes and best
practices for security configuration management. More sophisticated vulnerability
assessment products can test for both known and unknown vulnerabilities by
looking at both the common Web vulnerabilities and application-specific
vulnerabilities of those defects that exist in the actual business logic of the site.
! Vulnerability management: Vulnerability management products expand upon
vulnerability scanning by integrating additional features to provide risk
management and policy compliance. The additional features often integrate
security policy creation, maintenance, and enforcement. Vulnerability
management solutions also assist in patching activities, provide data to other
security devices, and provide detailed audit reports for compliance with
government regulations.
Identity and Access Management
Identity and access management software is a comprehensive set of solutions used
to identify users in a system (employees, customers, contractors, etc.) and control
their access to resources within that system by associating user rights and restrictions
with the established identity.
Web SSO, host SSO, user provisioning, advanced authentication, legacy
authorization, public key infrastructure (PKI), and directory services are all critical
components of identity and access management.
Other Security Software
Other security software covers emerging security functions that do not fit well into an
existing category. It also covers some of the underlying functions, such as encryption
tools and algorithms, that are the basis for many security capabilities found in other
software and hardware products. Also included in this category will be products that fit
a specific need but have yet to become established in the marketplace.
Products in this category will grow into their own categories or eventually be
incorporated into the other market segments. For 2003, areas covered by other
security software include, but are not restricted to, encryption toolkits, file encryption
products, database security, storage security, standalone VPN and VPN clients,
wireless security, Web services security, and secure operating systems. In addition,
4 #32391 ©2004 IDC
readers should be aware that the products that are covered here (especially for
wireless and Web services) are only those that do not qualify for one of the more
established categories.
SITUATION OVERVIEW
Viruses and worms continue to be the most serious threat facing corporations today.
According to a 2004 IDC survey of 600 firms across North America, 31% of
respondents indicated that viruses, trojans, and malicious code were the single
greatest threat, and another 10% indicated that network worms were the greatest
threat, as shown in Figure 1. The interesting finding in the study was that spyware
ranked fourth on the list of single greatest threats in 2004. This clearly shows that
spyware is moving up the priority list of corporate security concerns.
FIGURE 1
Threats to Enterprise Security
Trojans, viruses, and other
malicious code
Employee error (unintentional)
Internet worms
Spyware
Hackers
Sabotage by current employee
or business partner
Application vulnerabilities
Spam
Cyberterrorism
Inability to meet government
regulatory mandates
Other
0 5 10 15 20 25 30 35
(% of respondents)
n = 606
Source: IDC, 2004
©2004 IDC #32391 5
Key Trends
Security and Vulnerability Management Market Trends
IDC believes there were several key factors that drove the need for more
comprehensive security and vulnerability management solutions, not the least of
which are improved security and lower administration costs. Integration of security
with current system and network management systems, assurance of high uptime for
network and applications, administrative cost reduction (help desk), and a singular
view of the IT environment were all key factors in the convergence of security and
vulnerability management solutions.
The problem of coordinating and managing multiple security technologies across the
enterprise is a major obstacle facing organizations today. A growing number of
security products across the enterprise require frequent upgrades and
reconfigurations as new threats and vulnerabilities are detected. The time and costs
associated with coordinating and managing the updates and upgrades for the various
security technologies are overwhelming IS departments and corporate executives
alike. In the past, organizations commonly standardized on a "short list" of best-of-
breed antivirus, firewall, VPN, vulnerability assessment, and intrusion detection
technologies. Since the best-of-breed products often came from different vendors, the
technologies worked independently of one another and each technology had its own
individual management console. As security technologies became more complex,
manageability of large networks that integrated a variety of point products became
significantly more difficult and more costly.
Today's ebusiness world requires fully integrated and more comprehensive security
management solutions to deal with the multiple security products implemented across
the enterprise. Consolidated consoles for managing various security solutions along
with aggregated reporting, analysis, and control functions can reduce IT
administration chores and costs as well as personnel costs.
Identity and Access Management Market Trends
In the past, the mix of in-house, open source, and partner software was presented to
customers as 3A, but these disparate products had little affinity for one another. As a
result, system integration costs were very high. Customers soon began to demand a
more comprehensive set of solutions to not just reduce costs, but also increase
security and productivity. Three or four years ago, systems integration (SI) costs for
3A solutions were a multiple of the initial purchase price of the license and annual
software support contract. In fact, this SI multiple often reached 7–10x the purchase
price of the software. Over the last year, customers pushed vendors for greater
integration within their own products and their partners. As a result, IDC saw the shift
toward IAM solutions and the SI multiples fall to 3–5x in large corporate
environments. In small and medium-sized businesses (SMBs), however, customers
will only tolerate a 1.5x multiple because they worry about their reseller's ability to
6 #32391 ©2004 IDC
handle large integration projects and they lack budget for this kind of work. Overall,
customers increasingly demanded a high level of integration right out of the box. This
drove 3A vendors to develop more integrated IAM solutions.
IDC expects to see more and more hardware in the identity management area.
Tokens, smart cards, and biometrics, to a lesser extent, will become parts of
comprehensive identity and access management solutions.
Secure Content Management Market Trends
Spyware is the newest pest wreaking havoc of corporate and consumer users alike.
Spyware is no longer just a consumer nuisance; it is quickly becoming a major
concern in the corporate environment. The fact that spyware can gather information
about an employee or organization without their knowledge is causing corporate
security departments to take notice. Spyware is often installed without the user's
consent, as a drive-by download, or as the result of clicking some option in a
deceptive pop-up window. What concerns corporate security departments is that
spyware can also be used to monitor keystrokes, scan files, install additional
spyware, reconfigure Web browsers, and snoop email and other applications. Some
of the more sophisticated spyware can even capture screenshots or turn on
Webcams.
The challenge of controlling electronic communications as they flow into and out of an
organization is becoming increasingly more critical. Government and industry
regulations such as HIPAA, Sarbanes-Oxley, Gramm-Leach-Bliley, and SEC have
placed unprecedented pressure on corporations to secure the use of their electronic
communications. Each of these regulations can carry criminal penalties and/or civil
penalties.
The convenience and efficiency of electronic mail has been dramatically reduced by
the extremely rapid growth in the volume of unsolicited commercial electronic mail.
Spam has become more than just a nuisance; it is quickly becoming both a major
productivity drain and potential legal liability in organizations across the globe. Spam
fills networks, servers and inboxes with unwanted and often offensive content. The
business impact of spam only grows more serious as the volume of spam continues
to rise. The volume of spam sent worldwide every day will jump from 7 billion in 2002
to 23 billion in 2004, according to IDC estimates.
Firewall/VPN Market Trends
Software firewall/VPN products have considerable challenges brought on by the
popularity of appliances and new infrastructures and technologies. The market will
need to transform to remain a central part of an enterprise security posture. There are
two directions, caused by the segmentation of the market, that the firewall market will
take.
The first is that enterprise firewall/VPN software will gradually become part of a threat
management security market. This market will incorporate the firewall/VPN software,
along with firewall/VPN security appliances, and intrusion detection and prevention.
This is already happening in that all enterprise-level firewalls (both software and
hardware) are incorporating more sophisticated intrusion and worm protection
©2004 IDC #32391 7
capabilities. The creation of a threat management market will allow security vendors
more opportunity to develop the products that best support enterprise network
security needs. The second major impact is that desktop firewalls are also more
involved in threat management. The desktop products are becoming complete
endpoint security solutions that incorporate intrusion prevention (especially at the
application layer), worm protection, and being tied to antivirus and other content
security capabilities.
Intrusion Detection and Prevention Market Trends
The ID&P market is slowly making a transition from pure detection to prevention. As
IDC has stated, the technologies are complementary — prevention requires
detection. What is happening is the technology is advancing to the point that
customers are more comfortable using the prevention capabilities of the products.
Host intrusion prevention has been successful because its use does not shut down a
network. However, network intrusion prevention is increasing in acceptance as false
alerts are reduced and attacks become more damaging. IDC research estimates that
about 80% of those purchasing intrusion prevention–capable products are using
some of the blocking features in the product. Only a fraction (about a third) of the total
prevention features are being used at this time, but as confidence levels grow, so
should the level of prevention enabled. Vendors are not missing this adoption curve.
Many vendors are releasing prevention within their detection products. In this way a
customer can purchase a product for detection now and eventually and gradually
institute prevention.
To increase ID&P performance and manageability, vendors and customers are
turning to appliance-based network ID&P products. IDC expects that the usage of
dedicated appliances will dwarf the software-only market. The software will probably
only be that delivered to appliance vendors under an OEM arrangement.
8 #32391 ©2004 IDC
Leading Vendors in 2003
Figure 2 shows the top 10 vendors in the security software market for 2003.
FIGURE 2
Worldwide Security Software Revenue for Top 10 Vendors, 2003
Symantec
McAfee
Computer
Associates
Check Point
Software
Trend Micro
IBM
VeriSign
Internet Security
Systems
Microsoft
RSA Security
0 200 400 600 800 1,000 1,200 1,400 1,600
($M)
Secure content management
Firewall/VPN
Intrustion detection and prevention
Identity and access management
Security and vulnerability management
Other
Source: IDC, 2004
©2004 IDC #32391 9
Secure Content Management Software
Figure 3 shows vendor market shares in the secure content management software
market for 2003.
FIGURE 3
Worldwide Secure Content Management Software Revenue for
Top 10 Vendors, 2003
Symantec
McAfee
Trend Micro
Sophos
Websense
SurfControl
Computer Associates
Panda Software
Sybari Software
F-Secure
0 200 400 600 800 1,000 1,200
($M)
Source: IDC, 2004
10 #32391 ©2004 IDC
Identity and Access Management Software
Figure 4 shows vendor market shares in the identity and access management
software market for 2003.
FIGURE 4
Worldwide Identity and Access Management Software Revenue
for Top 10 Vendors, 2003
Computer Associates
IBM
VeriSign
RSA Security
Netegrity
Entrust
Novell
Fujitsu
Hitachi
AOL
0 50 100 150 200 250 300 350
($M)
Source: IDC, 2004
©2004 IDC #32391 11
Security and Vulnerability Management Software
Figure 5 shows vendor market shares in the security and vulnerability management
software market for 2003.
FIGURE 5
Worldwide Security and Vulnerability Management Software
Revenue for Top 10 Vendors, 2003
Computer Associates
Symantec
NetIQ
HP
BindView
Internet Security Systems
Cisco Systems
Enterasys Networks
Ubizen
Evidian (Groupe Bull)
0 20 40 60 80 100
($M)
Source: IDC, 2004
12 #32391 ©2004 IDC
Intrusion Detection and Prevention Software
Figure 6 shows vendor market shares in the intrusion detection and prevention
software market for 2003.
FIGURE 6
Worldwide Intrusion Detection and Prevention Software
Revenue for Top 10 Vendors, 2003
Internet Security Systems
Symantec
Tripwire
Cisco
Ubizen
Computer Associates
NFR
Secos
Enterasys Networks
AirDefense
0 20 40 60 80 100 120
($M)
Source: IDC, 2004
©2004 IDC #32391 13
Firewall/VPN Software
Figure 7 shows vendor market shares in the firewall/VPN software market for 2003.
FIGURE 7
Worldwide Firewall/VPN Software Revenue for Top 10 Vendors,
2003
Check Point Software
Microsoft
Symantec
ZoneLabs (acquired by Check Point)
Novell
Internet Security Systems
Secure Computing
Sun Microsystems
Sygate Technologies
StoneSoft
0 100 200 300 400 500
($M)
Source: IDC, 2004
14 #32391 ©2004 IDC
Other Security Software
Figure 8 shows vendor market shares in the "other" security software market for
2003.
FIGURE 8
Worldwide Other Security Software Revenue for Top 10
Vendors, 2003
Certicom
RSA Security
Hitachi
Network Associates
F-Secure
Fujitsu
Finsiel
SSH Communications Security
Oullim Information Technology
Gemplus International
0 5 10 15 20 25 30 35
($M)
Source: IDC, 2004
©2004 IDC #32391 15
FUTURE OUTLOOK
Forecast and Assumptions
The worldwide security software market achieved $8.4 billion in revenue in 2003, a
17.5% growth over 2002. IDC currently forecasts the security software market to
reach $16.3 billion in revenue in 2008, representing a compound annual growth rate
(CAGR) of 14% (see Tables 1 and 2). Key forecast assumptions for the security
software market are shown in Table 3.
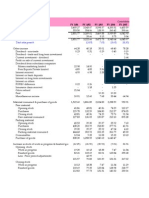
T ABLE 1
Worldwide Security Software Revenue by Market, 2003–2008 ($M)
2003 2008
Share 2003–2008 Share
2003 2004 2005 2006 2007 2008 (%) CAGR (%) (%)
Secure content 3,427 4,206 4,994 5,815 6,665 7,477 40.6 16.9 46.0
management
Identity and access 2,213 2,408 2,642 2,904 3,195 3,508 26.2 9.7 21.6
management
Security and 1,210 1,489 1,809 2,176 2,593 3,043 14.3 20.3 18.7
vulnerability
management
Intrusion detection 366 374 381 391 402 416 4.3 2.6 2.6
and prevention
Firewall/VPN 912 982 1,041 1,098 1,153 1,203 10.8 5.7 7.4
Other 307 354 412 476 548 623 3.6 15.2 3.8
Total 8,435 9,813 11,279 12,860 14,555 16,270 100.0 14.0 100.0
Note: See Table 3 for key forecast assumptions.
Source: IDC, 2004
16 #32391 ©2004 IDC
T ABLE 2
Worldwide Security Software Revenue by Region, 2003–2008 ($M)
2003 2008
Share 2003–2008 Share
2003 2004 2005 2006 2007 2008 (%) CAGR (%) (%)
North America 4,133 4,790 5,478 6,180 6,898 7,614 49.0 13.0 46.8
Western Europe 2,556 2,983 3,446 3,980 4,585 5,206 30.3 15.3 32.0
Asia/Pacific 1,324 1,548 1,787 2,049 2,333 2,619 15.7 14.6 16.1
ROW 422 493 568 651 739 830 5.0 14.5 5.1
Worldwide 8,435 9,813 11,279 12,860 14,555 16,270 100.0 14.0 100.0
Note: See Table 3 for key forecast assumptions.
Source: IDC, 2004
T ABLE 3
Key Forecast Assumptions for the Worldwide Security Software Market,
2004–2008
Accelerator/
Inhibitor/ Certainty of
Market Force IDC Assumption Impact Neutral Assumption
Macroeconomics
Economy Worldwide economic growth Moderate. Economic growth
will continue to recover slowly will begin to have a positive
↑
from 2001 levels to traditional impact on IT spending.
levels, which will be slightly
####$
below those in Consensus
Economics' April 4 forecast.
Policy Alan Greenspan is saying that Moderate. The deficit and
the deficit may be dangerous, rising interest rates could result
hinting that interest rates may in net-new IT spending if
rise. It is possible that the real
estate bubble will burst.
compliance projects don't
displace other IT projects on a
↓ ####$
Healthcare costs will continue 1:1 basis.
to rise.
Profits Pretax profits will be more than Moderate. IT spending will
↑
10% in the United States. begin to increase as individual
Consensus Economics' April 4 company profits improve.
####$
forecast will hold.
©2004 IDC #32391 17
T ABLE 3
Key Forecast Assumptions for the Worldwide Security Software Market,
2004–2008
Accelerator/
Inhibitor/ Certainty of
Market Force IDC Assumption Impact Neutral Assumption
Iraq The war in Iraq will continue, Low. Economic uncertainty
with Saddam Hussein deposed over Iraq will impact IT
and discredited. Travel spending.
restrictions will be lifted, and
the aura of uncertainty affecting
business decisions will
↓ ###$$
dissipate. The war is still being
financed with U.S. government
debt.
Post-Iraq There will be no Iraq-like war Low. There will be no impact.
and no abnormal activity one
way or the other.
↔ ###$$
Contagion There are no major contagions Low. The impact of any
on the immediate horizon. outbreaks will likely be limited
to small local areas. The
exception could be the
discovery of substantial mad
↔ ####$
cow disease in the United
States.
Other geopolitics The threat of terrorism at home Moderate. Business decisions
↔
and other potential armed and project initiation will begin
political conflict will neither in line with a better economic
###$$
escalate nor abate. outlook.
U.S. elections U.S. elections are a wild card Moderate. Traditionally,
↔
for the forecast period in the election years have been good
short term. for the economy; the issue will
####$
be what happens in 2005.
Energy Oil prices are on the rise. High. Oil prices are less
predictable, which is not so ↓ ####$
good for business.
18 #32391 ©2004 IDC
T ABLE 3
Key Forecast Assumptions for the Worldwide Security Software Market,
2004–2008
Accelerator/
Inhibitor/ Certainty of
Market Force IDC Assumption Impact Neutral Assumption
Inflation Inflation will remain under Moderate. Business
control. Over the next three confidence will be unaffected.
years (according to Consensus
Economics), expectations for
the United States, Western
↔
Europe, and Asia/Pacific are
that consumer prices will rise
####$
by less than 2%. Eastern
Europe and Latin America,
however, will continue to see
double-digit inflation. There will
be no deflation.
Unemployment Unemployment will slowly tail Moderate. More employment
off but remain above 5% in the will drive more need for IT
United States and flat in infrastructure and is a lagging
↑
Europe. There will not be a lot indicator of an economic
of job creation in the United recovery; job creation should
###$$
States. be accompanied by a
willingness to invest in other
areas.
↔
Telecom The telecom industry will begin Low. The IT industry has
to recover. already factored this in.
####$
Government and Government budget deficits Moderate. The strengthening
trade and trade imbalances will of the dollar may help U.S.
remain neutral in their impact software companies somewhat.
on IT. The dollar may
↔
strengthen somewhat. The
mood of Europe toward the
###$$
United States is a concern;
anger over the war in Iraq may
create an informal
protectionism.
Scandals The Enron, WorldCom, Tyco, Low. There will be no change.
and Parmalat scandals will
recede into memory, and ↔ ####$
business and consumer
confidence will begin to return.
©2004 IDC #32391 19
T ABLE 3
Key Forecast Assumptions for the Worldwide Security Software Market,
2004–2008
Accelerator/
Inhibitor/ Certainty of
Market Force IDC Assumption Impact Neutral Assumption
Exchange rates Improved profits in the United Moderate. This may accelerate
States, with the possibility of IT exports from exporting
interest rates going up, may countries into the United
↔
strengthen the U.S. dollar States.
somewhat. Top IT vendors'
###$$
growth will be attributable
mainly to the decline in the
dollar.
Expansion of the Increases will need to manage Low. There will be a balance of
eurozone business automation and spending, with jobs/production
↔
integration. moving to Eastern Europe
(shutting down of some existing
####$
systems), freeing up alternative
IT spending in Western Europe.
Compliance With regulations such as Moderate. Compliance
Sarbanes-Oxley, Basel II, and regulations may begin to have
HIPAA, increased compliance an effect on software spending
legislation within the United in 2005 and beyond.
States and Western Europe will Compliance will affect areas of
↑
increase transparency in many infrastructure software and
industries. services such as security and
####$
storage and applications areas
such as records management,
content management, and
business performance
management (to name a few).
Technology/
service
developments
Software Years of add-on and point-to- Moderate. The complexity
complexity point integration strategies crisis will maintain the need for
have resulted in an overly integration, but the demand for
complex infrastructure. high quality and productivity
Demand for simplicity and
agility will require a focus on
could deter skeptical buyers
from existing product offerings.
↔ ####$
business process as opposed Increasingly, this functionality
to technology itself. may be delivered as an IT or
business service.
20 #32391 ©2004 IDC
T ABLE 3
Key Forecast Assumptions for the Worldwide Security Software Market,
2004–2008
Accelerator/
Inhibitor/ Certainty of
Market Force IDC Assumption Impact Neutral Assumption
Linux Technical IT users will lead Low. This will have a
application deployment, with downward impact on price
↔
homegrown applications pressures.
moving first. Mainstream
####$
software is also moving toward
application serving on Linux.
Mobility Application and user-focused Low. This will have a low
mobile deployments are now impact on overall software
addressing business needs, growth.
which are being driven by line
of business. The need for more
↑ ####$
devices with useful applications
will continue.
Utility computing Multinational vendors will Low. This will have a low near-
continue to drive the concept of term impact on software
utility computing in various revenue. Software spending ↑ ##$$$
forms, but the concept is not may pick up toward the end of
well defined in the marketplace. the forecast period.
Killer apps New technology (e.g., Web Moderate. No killer apps or
services, wireless LANs, new technologies will come to
storage area networks, drive overall industry growth in
clustering, and high-growth the same way Windows and
↔
software areas) will help drive Office suites did in the 1980s or
price performance to attractive the Internet did in the late
####$
levels that support new IT 1990s. Web services will
spending growth. continue to be mostly a
software development
technique.
Labor supply
Productivity Job creation in the United Moderate. This will impact
management States and Europe will not be
prevalent.
increasing software revenue
growth.
↑ ###$$
Offshoring Skill supplies will be fulfilled Low. This will have little impact
with offshore software on overall software growth. The
↔
development. Developer jobs job market and pricing pressure
will not be returning to the are already major factors in
####$
United States or Western Western Europe.
Europe.
©2004 IDC #32391 21
T ABLE 3
Key Forecast Assumptions for the Worldwide Security Software Market,
2004–2008
Accelerator/
Inhibitor/ Certainty of
Market Force IDC Assumption Impact Neutral Assumption
Capitalization
Venture Venture funding will begin to Low. Money will continue to
pick up, but funding amounts open up. ↑ ####$
will be smaller.
Stocks There will be a modest upward Moderate. This will create
trend worldwide, but the U.S. decreased business confidence
↓
stock market may be in the United States.
overpriced and may go down,
##$$$
causing some small increases
in inflation in the United States.
Market
characteristics
Large enterprise There will be extreme price Moderate. This will have an
software renewals pressure on large enterprise
software renewals.
impact on changing software
revenue growth.
↓ ####$
Software licensing Attention to building predictable Moderate. Short term, there
revenue streams through will be less of an impact on
↑
nontraditional software overall software revenue.
licensing models will increase. Toward the back end of the
#####
forecast period, the impact on
software revenue will be higher.
U.S. homeland There will be an increase in Low. Security spending is not
security government programs to significantly on software yet;
↔
improve homeland security and spending is currently on
protect against terrorism. physical security. Software
###$$
growth will be affected beyond
the five-year forecast period.
Services-oriented Services-oriented architectures Moderate. In the short term,
architectures will allow companies to speed existing systems will be
the development of rearchitected and new
modularized applications and integration technologies will be
respond faster to new business
pressure.
deployed, which will improve
business processes/
↑ ####$
automation. In the midterm,
applications will begin to be
replaced.
22 #32391 ©2004 IDC
T ABLE 3
Key Forecast Assumptions for the Worldwide Security Software Market,
2004–2008
Accelerator/
Inhibitor/ Certainty of
Market Force IDC Assumption Impact Neutral Assumption
Application There will be demand for clear High. This demand will require
verticalization and unique software vendor vendors to develop more
↔
product differentiation, faster sophisticated partnerships and
implementation, and more increase market applicability of
####$
relevant "out of box" solutions. offered solutions (particularly to
SMEs).
Market ecosystem
Services IT services will continue to grow Moderate. These trends are
as companies attempt to already factored in.
concentrate on what they do
best and rely on IT services to
handle complexity they cannot.
Companies clearly see the
advantages of using outside ↔ ####$
services and outsourcers. IT
services will grow faster than
the overall IT market as
budgets shift from internal
spending to external
companies.
Consumption
Buying sentiment IT buyers will begin to Moderate. These trends are
moderately spend again as the already factored in.
economy improves; CIOs will
begin to replace hardware and
operating systems, begin to
↑
spend on mobility, and regain
the attitude that IT spending is
####$
critical to the well-being of a
company (or household). IT
spending as a percentage of
revenue (or income) will
increase.
Saturation PC and Internet markets will Moderate. These trends are
continue to saturate, but already factored in.
↔
emerging geographies will
invest and new applications will
####$
drive users to multiplatform
usage.
Legend: #$$$$ very low, ##$$$ low, ###$$ moderate, ####$ high, ##### very high
Source: IDC, July 2004
©2004 IDC #32391 23
ESSENTIAL GUIDANCE
The 2003 onslaught of viruses and worms such as Blaster, Nachi, and SoBig not only
highlights the importance of keeping security solutions up to date, it also shines a
spotlight on the growing need for more proactive security products and services. The
rapid infection by these new worm and virus attacks means that slow responses will
cripple most customer environments because they will not be able to get ahead of the
initial infection and the far more serious reinfections. Malicious hackers are getting
much more sophisticated and faster at exploiting application vulnerabilities. Zero-day
attacks that take advantage of software vulnerabilities for which there are no available
fixes are starting to be viewed as a major threat to data security.
Intrusion detection and preventions products will continue to gain acceptance as a
way to eliminate Internet worms and maintain control over the internal working of
enterprise networks and applications. A new segment of ID&P products designed
specifically to protect and segment the internal network is beginning to emerge. IDC
is dubbing this the "FireDoor" market. FireDoor's will primarily use behavioral or
anomaly detection and policy rules to identify variations and unexpected events that
signal attacks, anomalous behavior, and misuse and abuse. They also can be very
good for worm detection, segmentation of virtual domains for protection of proprietary
or sensitive information, and verification of authentication credentials. The FireDoor
products will eventually include much more prevention as they are used to seal off
network segments from worms and other automated attacks recognized within a
company's network.
Firewall/VPN software products must be able to have smooth integration with
complementary security products, such as intrusion detection and content security. In
doing so, the software firewall/VPN can evolve into the unified threat management
space that is emerging in the appliances market. Vendors should also look closely at
partnering with managed service providers. These service providers will eventually
provide firewalls as an embedded service; to succeed, the software vendor must
capture some of this market. Software vendors must also offer options that can
compete with the faster-growing firewall/VPN security appliance market. Licensing
and partnerships will be required to remain strong in this market.
Government and industry regulations will continue to put unprecedented pressure on
corporations to secure access to information and applications not just with
employees, but also with customers, partners, and contractors. Moreover, budgetary
and staffing constraints will continue to drive organizations to look for better ways to
cost effectively manage their security infrastructure. Security solutions that can
simplify the complexity associated with managing multiple security solutions, while at
the same time increasing the effectiveness of protection will be key.
24 #32391 ©2004 IDC
LE ARN MORE
Related Research
! Worldwide Antispam 2004–2008 Forecast Update and 2003 Vendor Shares
(forthcoming)
! Worldwide Identity and Access Management 2004–2008 Forecast and 2003
Competitive Vendor Shares: The Death of Security 3A, Part I (IDC #31997,
November 2004)
! Worldwide Security and Vulnerability Management 2004–2008 Forecast and
2003 Vendor Shares: The Death of Security 3A, Part II (IDC #32008, November
2004)
! Worldwide Vulnerability Assessment and Management 2004–2008 Forecast and
2003 Vendor Shares: Assessing Risk and Compliance (IDC #32026, October
2004)
! Worldwide Intrusion Detection and Prevention 2004–2008 Forecast and 2003
Vendor Shares: Introducing the FireDoor (IDC #32004, October 2004)
! Worldwide Threat Management Security Appliances 2004–2008 Forecast and
2003 Vendor Shares: The Rise of the Unified Threat Management Security
Appliance (IDC #31840, September 2004)
! Worldwide Firewall Software 2004–2008 Forecast and 2003 Vendor Shares:
Desktop Firewalls on the Move (IDC #31839, September 2004)
! Worldwide Antivirus 2004–2008 Forecast and 2003 Vendor Shares (IDC #31737,
August 2004)
! Worldwide Secure Content Management 2004–2008 Forecast Update and 2003
Vendor Shares: A Holistic View of Antivirus, Web Filtering, and Messaging
Security (IDC #31598, August 2004)
! IDC's Software Taxonomy, 2004 (IDC #30838, February 2004)
©2004 IDC #32391 25
Copyright Notice
This IDC research document was published as part of an IDC continuous intelligence
service, providing written research, analyst interactions, telebriefings, and
conferences. Visit www.idc.com to learn more about IDC subscription and consulting
services. To view a list of IDC offices worldwide, visit www.idc.com/offices. Please
contact the IDC Hotline at 800.343.4952, ext. 7988 (or +1.508.988.7988) or
sales@idc.com for information on applying the price of this document toward the
purchase of an IDC service or for information on additional copies or Web rights.
Copyright 2004 IDC. Reproduction is forbidden unless authorized. All rights reserved.
Published Under Services: Security Products; 3As Security; Secure Content
Management; Intrusion Detection and Vulnerability Assessment; Firewalls and
Security Appliances; Mobile Security Software
26 #32391 ©2004 IDC
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- Saks SKSDocument1 pageSaks SKSapi-3702531100% (1)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- Indian Insider Buyings June 19, 2008-DhananDocument2 pagesIndian Insider Buyings June 19, 2008-Dhananapi-3702531No ratings yet
- Dillard DDSDocument1 pageDillard DDSapi-3702531100% (2)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- SMG PLC - ProfileDocument4 pagesSMG PLC - Profileapi-3702531No ratings yet
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- Walmart WMTDocument1 pageWalmart WMTapi-3702531100% (2)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- BSE Special Situations 19th June 2008Document5 pagesBSE Special Situations 19th June 2008api-3702531No ratings yet
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- Half Yearly Report 2007-08Document44 pagesHalf Yearly Report 2007-08api-3702531No ratings yet
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (588)
- GilletteDocument14 pagesGilletteapi-3702531No ratings yet
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- Avon Product AVPDocument1 pageAvon Product AVPapi-3702531100% (1)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- Dabur IndiaDocument43 pagesDabur Indiaapi-3702531No ratings yet
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Fem CareDocument16 pagesFem Careapi-3702531No ratings yet
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Colgate AR March 2006Document76 pagesColgate AR March 2006api-3702531No ratings yet
- Dabur India - 2Document51 pagesDabur India - 2api-3702531No ratings yet
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- DUBARINDIAAR200708Document164 pagesDUBARINDIAAR200708Santosh KumarNo ratings yet
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Annual Report 2007 2008Document84 pagesAnnual Report 2007 2008api-3702531No ratings yet
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- March 2008 Consolidated ResultsDocument1 pageMarch 2008 Consolidated Resultsapi-3702531No ratings yet
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- Dabur IndiaDocument43 pagesDabur Indiaapi-3702531No ratings yet
- AR March 2007Document147 pagesAR March 2007api-3702531No ratings yet
- AR March 2003 - Only ConsolidatedDocument17 pagesAR March 2003 - Only Consolidatedapi-3702531No ratings yet
- AR March 2004 - Only ConsolidatedDocument17 pagesAR March 2004 - Only Consolidatedapi-3702531No ratings yet
- ColgateDocument32 pagesColgateapi-3702531No ratings yet
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- ColgateDocument32 pagesColgateapi-3702531No ratings yet
- Colgate AR March 2007Document88 pagesColgate AR March 2007api-3702531No ratings yet
- AR March 2005Document116 pagesAR March 2005api-3702531No ratings yet
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- AR March 2006Document36 pagesAR March 2006api-3702531No ratings yet
- Colgate AR March 2004Document72 pagesColgate AR March 2004api-3702531No ratings yet
- Colgate AR March 2005Document72 pagesColgate AR March 2005ashusingh0141No ratings yet
- 4q07 08Document1 page4q07 08api-3702531No ratings yet
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (120)
- Colgate AR March 2003Document72 pagesColgate AR March 2003api-3702531No ratings yet
- Colgate AR March 2002Document88 pagesColgate AR March 2002api-3702531No ratings yet
- Grandstream Networks, Inc.: HA100 High Availability Kit For UCM6510Document11 pagesGrandstream Networks, Inc.: HA100 High Availability Kit For UCM6510MOhamedNo ratings yet
- RAN Engineer PDFDocument4 pagesRAN Engineer PDFRadu Tudor ParaschivNo ratings yet
- Cmos 0 To 44 MHZ Single Chip 8-Bit Microntroller: DescriptionDocument20 pagesCmos 0 To 44 MHZ Single Chip 8-Bit Microntroller: DescriptionJoel Hauk HaukNo ratings yet
- MSBI Training Plans: Plan A Plan B Plan CDocument14 pagesMSBI Training Plans: Plan A Plan B Plan CVeerendra ReddyNo ratings yet
- Maya Lab 1Document1 pageMaya Lab 1MonoNo ratings yet
- Project 1 Creating A Dynamic Web Page: Header - PHP Footer - PHPDocument4 pagesProject 1 Creating A Dynamic Web Page: Header - PHP Footer - PHPIvan PangitNo ratings yet
- SBWP Customization (Tip For Inbox Customization)Document8 pagesSBWP Customization (Tip For Inbox Customization)koisakNo ratings yet
- Pillars of EcommerceDocument8 pagesPillars of EcommerceShaik YusafNo ratings yet
- Course Outline Software ArchitectureDocument3 pagesCourse Outline Software ArchitectureahmedNo ratings yet
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- Parallel Computers Networking PDFDocument48 pagesParallel Computers Networking PDFHemprasad BadgujarNo ratings yet
- Artificial Intelligence and PrivacyDocument14 pagesArtificial Intelligence and PrivacyVivekKumarNo ratings yet
- The Coca Cola Company PLC Official Yearly Prize Award Winners NotificationDocument7 pagesThe Coca Cola Company PLC Official Yearly Prize Award Winners NotificationHckron Farm1100% (1)
- (Object Oriented Programming) : CCS0023LDocument8 pages(Object Oriented Programming) : CCS0023LKross FordNo ratings yet
- Course Guide-CMSC311Document5 pagesCourse Guide-CMSC311Mark BernardinoNo ratings yet
- Datasheet Allplan Engineering PDFDocument2 pagesDatasheet Allplan Engineering PDFRafael PopaNo ratings yet
- Chapter 5 TableDocument106 pagesChapter 5 TableFOO POH YEENo ratings yet
- Health IT Security Risk Assessment ToolDocument57 pagesHealth IT Security Risk Assessment ToolTUP BOXNo ratings yet
- Google AdsDocument15 pagesGoogle AdsRituNo ratings yet
- Ds Oop Lab ManualDocument63 pagesDs Oop Lab ManualramaNo ratings yet
- Computer Technician Training CourseDocument8 pagesComputer Technician Training CourseApnhs ApequeñoNo ratings yet
- 07 Laboratory Exercise 1Document5 pages07 Laboratory Exercise 1kwalwalgud21No ratings yet
- Ai Engine Development For Versal: Olivier Tremois, PHD SW Technical Marketing Ai Engine ToolsDocument30 pagesAi Engine Development For Versal: Olivier Tremois, PHD SW Technical Marketing Ai Engine ToolsAliNo ratings yet
- ICT Lecture 08 Computer SoftwareDocument32 pagesICT Lecture 08 Computer SoftwareNasir Faraz KalmatiNo ratings yet
- Apple IIgs Demo SamplerDocument6 pagesApple IIgs Demo SamplerduesenNo ratings yet
- Ccnpv7.1 Switch Lab3-1 Vlan-trunk-Vtp StudentDocument20 pagesCcnpv7.1 Switch Lab3-1 Vlan-trunk-Vtp StudentItamar Zimmerman0% (1)
- Introduction To Embedded Systems: Melaku MDocument150 pagesIntroduction To Embedded Systems: Melaku MTalemaNo ratings yet
- Teracom Training Institute Ilt CatalogDocument16 pagesTeracom Training Institute Ilt CatalognebubuNo ratings yet
- Log View User GuideDocument53 pagesLog View User GuideSerhiiNo ratings yet
- PM Debug InfoDocument256 pagesPM Debug InfoGreg Edimilson GregNo ratings yet
- 02 - CCM - Functionality KeyCapabilities - EN - V1 2docxDocument31 pages02 - CCM - Functionality KeyCapabilities - EN - V1 2docxAnoop Kumar67% (3)