Professional Documents
Culture Documents
2017 Global State of Information Security Survey
Uploaded by
IDG_WorldCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
2017 Global State of Information Security Survey
Uploaded by
IDG_WorldCopyright:
Available Formats
2017 Global State of
Information Security Survey
2017 Global State of Information Security Survey conducted by PwC, CSO and CIO. Confidential.
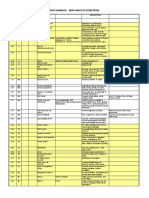
This year, organizations are prioritizing spending on broad
strategies to strengthen their digital ecosystems.
Security priorities in 2016 emphasize internal collaboration, new security
safeguards for evolving business models and the Internet of Things.
51%
44%
46%
46%
46%
Information
security
spending
priorities for
2016
Biometrics &
advanced
authentication
Digital enterprise
architecture
Security for the
Internet of Things
New security needs
Improved
related to evolving collaboration among
business models
business,
digital & IT
59%
Say digitization
has increased
information
security spending
Q. What types of security safeguards does your organization plan to invest in over the next 12 months? AND What impact has digitization of the
business ecosystem had on your organizations security spending?
2017 Global State of Information Security Survey conducted by PwC, CSO and CIO. Confidential.
As the Internet of Things takes off, organizations are moving to
update their cybersecurity and privacy safeguards.
Key initiatives address data governance, device and system interconnectivity,
and employee training. Consumer privacy is also a priority.
32%
34%
35%
35%
37%
46%
Policies,
technologies
and people
skills being
implemented
for the Internet
of Things
Uniform
Policies &
Employee training Assess device &
cybersecurity
technologies to
on IoT security
system
standards &
safeguard against
practices
interconnectivity &
policies for IoT consumer privacy
vulnerability
devices &
violations
across the
systems
business
ecosystem
New data
collection,
retention &
destruction
policies
Are investing in
a security strategy
for the Internet
of Things
Q. What policies, technologies and people skills does your organization plan to implement over the next 12 months to address the cybersecurity
and privacy risks associated with the Internet of Things (IoT)? AND What types of security safeguards does your organization plan to invest in
over the next 12 months?
2017 Global State of Information Security Survey conducted by PwC, CSO and CIO. Confidential.
Big Data Analytics
Use analytics?
40%
25%
Benefits
57%
16%
Currently in place Not in place but a
priority for 2017
52%
47%
45%
43%
38%
Currently
outsourced
11%
12%
No plans to adopt
Don't know
37%
28%
17%
Improved
Improved
Better visibility
Improved
understanding of understanding of into anomalous understanding of
external security internal security network activity user behaviour
threats
threats
Improved ability Provides advance Has prevented
We have
Improved forensic
to quickly identify warning of cyber security incidents detected more
investigations
and respond to
incidents
security incidents
security incidents
2%
2%
Do not know
Other
Q. What are the most significant benefits of a Big Data-driven security capability? AND Does your organization employ Big Data analytics to model for and
identify information security incidents?
2017 Global State of Information Security Survey conducted by PwC, CSO and CIO. Confidential.
Respondents are embracing managed security services to
extend and enhance their cybersecurity capabilities.
Organizations say they rely on managed security services for highly technical initiatives
such as authentication, data loss prevention and identity management.
48%
55%
60%
61%
64%
62%
Types of
managed
security
services used
Threat
intelligence
Real-time
monitoring &
anlytics
Identity & access
management
Data loss
prevention
Authentication
Use managed
security services
for cybersecurity
& privacy
Q. Does your organization use managed security services in its cybersecurity and privacy programs? AND Which of the following managed
security services does your organization use?
2017 Global State of Information Security Survey conducted by PwC, CSO and CIO. Confidential.
Continue the Conversation
For more information, please contact: Sue Yanovitch, VP, Marketing at
IDG Enterprise syanovitch@idgenterprise.com
To get results from CSO research when it happens,
or any other news, follow us on Twitter: @idgenterprise
ADDITIONAL WAYS TO STAY ON TOP OF INFORMATION FROM IDG ENTERPRISE:
Sign up to receive our monthly marketing
newsletter at www.idgenterprise.com/newsletter
Visit us on LinkedIn:
www.linkedin.com/company/idg-enterprise
77
You might also like
- IDG Enterprise's 2014 Role & Influence of The Technology Decision-MakerDocument10 pagesIDG Enterprise's 2014 Role & Influence of The Technology Decision-MakerIDG_WorldNo ratings yet
- CIO/CSO Partnership SurveyDocument8 pagesCIO/CSO Partnership SurveyIDG_WorldNo ratings yet
- IDG 2017 Security Priorities StudyDocument8 pagesIDG 2017 Security Priorities StudyIDG_WorldNo ratings yet
- 2018 CIO Tech Poll: Economic OutlookDocument8 pages2018 CIO Tech Poll: Economic OutlookIDG_World100% (1)
- Today's Cloud Focus & MotivatorsDocument1 pageToday's Cloud Focus & MotivatorsIDG_World100% (2)
- Set-2 - InterviewquestionspdfDocument7 pagesSet-2 - InterviewquestionspdfGoliBharggavNo ratings yet
- IDG Enterprise Cloud Computing Research (2014)Document10 pagesIDG Enterprise Cloud Computing Research (2014)IDG_World100% (1)
- MBA820 Course Slides 1-21Document21 pagesMBA820 Course Slides 1-21Charlene PienaarNo ratings yet
- 2016 Customer Engagement ResearchDocument14 pages2016 Customer Engagement ResearchIDG_World100% (1)
- Eppm 16 1 Tested ConfigsDocument25 pagesEppm 16 1 Tested ConfigsNguyễn Viết HoànNo ratings yet
- 2018 IDG Security Priorities SurveyDocument9 pages2018 IDG Security Priorities SurveyIDG_WorldNo ratings yet
- Tech Priorities 2017 SampleDocument7 pagesTech Priorities 2017 SampleIDG_WorldNo ratings yet
- Weee/E-Waste Business Model: Ministry of EnvironmentDocument26 pagesWeee/E-Waste Business Model: Ministry of EnvironmentDhiraj KumarNo ratings yet
- ITSM My Messages WidgetDocument10 pagesITSM My Messages WidgetDaniel Urma100% (1)
- Symbioun Tech Corp PresentationDocument16 pagesSymbioun Tech Corp PresentationSymbiounTechNo ratings yet
- Logical Framework InformationDocument2 pagesLogical Framework InformationeradityaNo ratings yet
- Control Objectives (PO1 - PO2 - PO4)Document22 pagesControl Objectives (PO1 - PO2 - PO4)Rizkie Denny PratamaNo ratings yet
- IBM's CIO Study: Telecom Industry Executive SummaryDocument16 pagesIBM's CIO Study: Telecom Industry Executive SummaryIBMTelecomNo ratings yet
- A Guide To Understanding How Organizations Are Evolving To A Digital-First Business ModelDocument1 pageA Guide To Understanding How Organizations Are Evolving To A Digital-First Business ModelIDG_WorldNo ratings yet
- Business Process Mapping and ModelingDocument34 pagesBusiness Process Mapping and ModelingVitalii LiakhNo ratings yet
- The Future Growth of A Career As A Business Analyst Its Role and ResponsibilitiesDocument23 pagesThe Future Growth of A Career As A Business Analyst Its Role and ResponsibilitieslearningrowNo ratings yet
- Plan Scope ManagementDocument1 pagePlan Scope ManagementPrakashNo ratings yet
- Tech Influencer: Technology Buying Trends Related To The NetworkDocument1 pageTech Influencer: Technology Buying Trends Related To The NetworkIDG_WorldNo ratings yet
- 7 Questions Every CEO Needs To Ask Their CIO: 1. What Security Issues Do We Have in The Company?Document4 pages7 Questions Every CEO Needs To Ask Their CIO: 1. What Security Issues Do We Have in The Company?arunkumarmgNo ratings yet
- The ABCs of ERP - EnterpriseDocument7 pagesThe ABCs of ERP - EnterpriseADIL KAKAKHELNo ratings yet
- Swot Analysis 3.5: WorksheetDocument62 pagesSwot Analysis 3.5: WorksheetAndroEstreNo ratings yet
- Project Process AgreementDocument11 pagesProject Process Agreementrgrao85No ratings yet
- Risk AssessmentDocument2 pagesRisk AssessmentNia NovitaNo ratings yet
- ITCoree BooksDocument99 pagesITCoree BooksJawad AnwarNo ratings yet
- Audit Universe and Risk Assessment ToolDocument10 pagesAudit Universe and Risk Assessment ToolAsis KoiralaNo ratings yet
- 01 - Risk Register - TemplateDocument19 pages01 - Risk Register - TemplateUsama AbuelattaNo ratings yet
- An Adaptive Priority Approach For Effective Problem Resolution in ITSMDocument12 pagesAn Adaptive Priority Approach For Effective Problem Resolution in ITSMProdapt Solutions100% (1)
- Comparing GCIO Development in US, Thailand, Japan and Recommendations for the PhilippinesDocument75 pagesComparing GCIO Development in US, Thailand, Japan and Recommendations for the PhilippinesJingle AllamNo ratings yet
- Detailed Plans and BudgetDocument8 pagesDetailed Plans and BudgetMaricel R IlaganNo ratings yet
- It Governance Guide v1.2Document15 pagesIt Governance Guide v1.2Nicolas Mejia100% (1)
- DRAFT Agilient Mapping Toolset 30517 v3.0Document541 pagesDRAFT Agilient Mapping Toolset 30517 v3.0holamundo123No ratings yet
- CIO Tech Priorities 2016Document6 pagesCIO Tech Priorities 2016IDG_WorldNo ratings yet
- Project Name: (Insert Your Company Name and Logo Here)Document11 pagesProject Name: (Insert Your Company Name and Logo Here)amitsingh5No ratings yet
- 5S-Manufacturing-Assessment v3.1Document2 pages5S-Manufacturing-Assessment v3.1MIKEHENDRICKNo ratings yet
- 2020 Salary Survey Report PDFDocument42 pages2020 Salary Survey Report PDFMatthew Burke100% (1)
- NDA Maturity Assessment WorksheetDocument31 pagesNDA Maturity Assessment Worksheetholamundo123No ratings yet
- Ransomware Self-Assessment Tool: OCTOBER 2020Document14 pagesRansomware Self-Assessment Tool: OCTOBER 2020AhmedAlHefnyNo ratings yet
- RFP-GRC Vs ERM-FINALDocument3 pagesRFP-GRC Vs ERM-FINALjaholmeNo ratings yet
- IDG 2016 Cloud Computing SurveyDocument9 pagesIDG 2016 Cloud Computing SurveyIDG_World100% (7)
- IT Strategy (Information Technology Strategy) : CIO Wiki Navigation ToolsDocument15 pagesIT Strategy (Information Technology Strategy) : CIO Wiki Navigation ToolsCarlos SamNo ratings yet
- IT ExecSum Sept 2021Document56 pagesIT ExecSum Sept 2021DxNo ratings yet
- Attrition Dashboard - May 31stDocument12 pagesAttrition Dashboard - May 31st32587412369No ratings yet
- Event Budget - SeminarDocument6 pagesEvent Budget - SeminarKashif ehsanNo ratings yet
- 11.management Awareness DiagnosticDocument2 pages11.management Awareness DiagnosticnoormutiaNo ratings yet
- Case Study - Global Construction CompanyDocument2 pagesCase Study - Global Construction Companymsfayas0% (1)
- The Forrester Wave™ Workforce Optimization Platforms, Q4 2021Document15 pagesThe Forrester Wave™ Workforce Optimization Platforms, Q4 2021Ashish NagarNo ratings yet
- Agile Project Plan Template Excel - awp3fO7DZjfxukIDocument25 pagesAgile Project Plan Template Excel - awp3fO7DZjfxukIAlex Orlando Castillo CentenoNo ratings yet
- IDC Worldwide DevSecOps Software Tools Forecast, 2021-2025Document13 pagesIDC Worldwide DevSecOps Software Tools Forecast, 2021-2025Yoav Ben EzraNo ratings yet
- Abdc Journal ListDocument23 pagesAbdc Journal ListKiran DhankharNo ratings yet
- Incident Management Group Test 2016 - The Results - The ITSM ReviewDocument23 pagesIncident Management Group Test 2016 - The Results - The ITSM ReviewrobogormanNo ratings yet
- Profile PresentationDocument29 pagesProfile PresentationBhasaar65No ratings yet
- Ai For BusinessDocument4 pagesAi For BusinessjayaNo ratings yet
- ADRAP DatasheetDocument2 pagesADRAP DatasheetServerGeeksNo ratings yet
- Advanced Analytics for Government The Ultimate Step-By-Step GuideFrom EverandAdvanced Analytics for Government The Ultimate Step-By-Step GuideNo ratings yet
- 2017 U.S. State of Cybercrime SurveyDocument8 pages2017 U.S. State of Cybercrime SurveyIDG_WorldNo ratings yet
- 2018 IDG Security Priorities InfographicDocument1 page2018 IDG Security Priorities InfographicIDG_WorldNo ratings yet
- 2018 State of The Network InfographicDocument1 page2018 State of The Network InfographicIDG_WorldNo ratings yet
- 2018 U.S. State of Cybercrime SurveyDocument9 pages2018 U.S. State of Cybercrime SurveyIDG_WorldNo ratings yet
- IDG 2018 Cloud Computing ResearchDocument8 pagesIDG 2018 Cloud Computing ResearchIDG_World100% (4)
- 2018 IDG Cloud Computing InfographicDocument1 page2018 IDG Cloud Computing InfographicIDG_WorldNo ratings yet
- A Guide To Understanding How Organizations Are Evolving To A Digital-First Business ModelDocument1 pageA Guide To Understanding How Organizations Are Evolving To A Digital-First Business ModelIDG_WorldNo ratings yet
- 2018 CIO Tech Poll: Economic Outlook InfographicDocument1 page2018 CIO Tech Poll: Economic Outlook InfographicIDG_WorldNo ratings yet
- CIOs Are Driving Digital Transformation InfographicDocument1 pageCIOs Are Driving Digital Transformation InfographicIDG_WorldNo ratings yet
- 2018 Global State of Information Security SurveyDocument9 pages2018 Global State of Information Security SurveyIDG_WorldNo ratings yet
- 2018 IDG Security Priorities SurveyDocument9 pages2018 IDG Security Priorities SurveyIDG_WorldNo ratings yet
- CIO Tech Poll: Tech Priorities 2018Document7 pagesCIO Tech Poll: Tech Priorities 2018IDG_WorldNo ratings yet
- State of The Network 2018Document10 pagesState of The Network 2018IDG_WorldNo ratings yet
- 2018 IDG Digital Business SurveyDocument9 pages2018 IDG Digital Business SurveyIDG_World100% (3)
- State of The CIO 2018Document9 pagesState of The CIO 2018IDG_WorldNo ratings yet
- State of The CIO 2017Document9 pagesState of The CIO 2017IDG_World100% (1)
- 2017 IDG Customer Engagement ExcerptDocument8 pages2017 IDG Customer Engagement ExcerptIDG_WorldNo ratings yet
- 2017 CIO Tech Poll: Economic OutlookDocument6 pages2017 CIO Tech Poll: Economic OutlookIDG_WorldNo ratings yet
- Digital Disruption & The NetworkDocument1 pageDigital Disruption & The NetworkIDG_WorldNo ratings yet
- CSO 2016 SIEM Vendor Scorecard ResearchDocument7 pagesCSO 2016 SIEM Vendor Scorecard ResearchIDG_WorldNo ratings yet
- Demand GenerationDocument9 pagesDemand GenerationIDG_World100% (1)
- State of The Network 2017Document8 pagesState of The Network 2017IDG_WorldNo ratings yet
- 2017 Customer Engagment Sample SlidesDocument8 pages2017 Customer Engagment Sample SlidesIDG_WorldNo ratings yet
- CW Forecast 2017 SampleDocument8 pagesCW Forecast 2017 SampleIDG_World100% (1)
- Tech Priorities 2017 SampleDocument7 pagesTech Priorities 2017 SampleIDG_WorldNo ratings yet
- The Connection Between Security and Data & AnalyticsDocument1 pageThe Connection Between Security and Data & AnalyticsIDG_World100% (1)
- TibagDocument48 pagesTibagAngelika CalingasanNo ratings yet
- Krs One Pick It Up Fill in The Blank ActivityDocument1 pageKrs One Pick It Up Fill in The Blank ActivityAmadeus ReyNo ratings yet
- Mahindra Supply ChainDocument14 pagesMahindra Supply ChainDarshak ParikhNo ratings yet
- Kabataan Party-List v. COMELEC, G.R. No. 221318, 16 December 2015Document28 pagesKabataan Party-List v. COMELEC, G.R. No. 221318, 16 December 2015JM EnguitoNo ratings yet
- HR Cycle & Org Overview-1 PDFDocument8 pagesHR Cycle & Org Overview-1 PDFangga zalindraNo ratings yet
- Modern Recruitment Sources: Employee Referrals, Campus Recruitment & E-RecruitmentDocument10 pagesModern Recruitment Sources: Employee Referrals, Campus Recruitment & E-Recruitmentvikas dhere100% (1)
- 03 Sumulong Vs COMELECDocument2 pages03 Sumulong Vs COMELECJanno Sangalang100% (1)
- APICS 2012 CSCP List of Primary References and Additional AidsDocument17 pagesAPICS 2012 CSCP List of Primary References and Additional Aidsshivam_dubey4004No ratings yet
- SAP Plant Maintenance Course OutlineDocument9 pagesSAP Plant Maintenance Course Outlinenh0% (1)
- Soal Ab1 (Tm-1) Cost ConceptDocument5 pagesSoal Ab1 (Tm-1) Cost ConceptAntonius Sugi SuhartonoNo ratings yet
- Course Outline ProcurmentDocument5 pagesCourse Outline ProcurmentFahadJavedHusseiniNo ratings yet
- Supply Chain ManagementDocument6 pagesSupply Chain ManagementPhuong LeNo ratings yet
- Becoming Top Ten: An Analysis of Michigan's ESSA PlanDocument10 pagesBecoming Top Ten: An Analysis of Michigan's ESSA PlanThe Education Trust Midwest0% (1)
- Maam AssDocument3 pagesMaam AsslapNo ratings yet
- Grade IX Sun Ch.3 Electoral PoliticsDocument44 pagesGrade IX Sun Ch.3 Electoral PoliticsSharad MusaleNo ratings yet
- What is MBO? Management by Objectives ExplainedDocument3 pagesWhat is MBO? Management by Objectives ExplainedGokul BalajiNo ratings yet
- CIO Certificate RequirementsDocument1 pageCIO Certificate RequirementsHasna Hassan AnnacotNo ratings yet
- Onondaga County Police Reform PlanDocument59 pagesOnondaga County Police Reform PlanTim KnaussNo ratings yet
- Lamitan City, BasilanDocument3 pagesLamitan City, BasilanSunStar Philippine NewsNo ratings yet
- ACCTNG3Document3 pagesACCTNG3Almira ReyesNo ratings yet
- Raci Model in ITIL Service ManagementDocument1 pageRaci Model in ITIL Service ManagementPaul SudebNo ratings yet
- ISO 10002 Project PlanDocument1 pageISO 10002 Project Planchaouch.najehNo ratings yet
- The Democracy: Meaning and DefinitionDocument4 pagesThe Democracy: Meaning and DefinitionRumi RoyNo ratings yet
- Project Management Maturity ModelDocument223 pagesProject Management Maturity ModelNguyễn Hoàng Bảo100% (6)
- Creating A Culture of Empowerment and Accountability at SMDPDocument5 pagesCreating A Culture of Empowerment and Accountability at SMDPThomas Stuart100% (1)
- The Lean CRMDocument8 pagesThe Lean CRMSidak KatyalNo ratings yet
- Siasi, SuluDocument2 pagesSiasi, SuluSunStar Philippine NewsNo ratings yet
- The Power of Legality, Legitimacy and The (Im) Possibility of Interdisciplinary ResearchDocument31 pagesThe Power of Legality, Legitimacy and The (Im) Possibility of Interdisciplinary ResearchErnesto Gastón De MarsilioNo ratings yet
- Civics 8Document4 pagesCivics 8api-338367732No ratings yet
- Talalora, Samar (Western Samar)Document2 pagesTalalora, Samar (Western Samar)SunStar Philippine NewsNo ratings yet