Professional Documents
Culture Documents
Psnmun 2016 - Disec
Uploaded by
CharuMathurOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Psnmun 2016 - Disec
Uploaded by
CharuMathurCopyright:
Available Formats
PATHWAYS SCHOOL NOIDA
Middle School Model UN Conference 2016
30th-31st August, 2016
Committee: GA-DISEC
Agenda: New Battlegrounds: The Future of Cyber Security and
Cyber Warfare
Introduction
Information and communication technologies (ICTs) are permeating and transforming every
aspect of our lives in the 21st century. Today, the number of global web users, stands at an
estimated 2.4 billion, just over one third of the world's total population. Over 60% of all
internet users are in developing countries, with 45% of all internet users below the age of 25.
It is estimated that by the year 2017, mobile broadband subscriptions will approach 70% of
the world's total population. By the year 2020, the number of networked devices (the
internet of things) will outnumber people by six to one, transforming current conceptions
of the internet.
As societies transform into information societies, we have witnessed widespread system
interconnection, and increased dependence of individuals, organisations and countries on
digital technologies and information infrastructures. While cyberspace has presented
significant opportunities, our accelerating dependence on ICTs also comes with increasing
security threats and risks. A 2011 Norton Study estimates that threats to cyberspace have
increased dramatically over the past year, afflicting 431 million adult victims globally or
14 adult victims every second, one million cybercrime victims every day. Today, cybercrime
is an over one-trillion dollar a year business in online fraud, identity theft and lost
intellectual property. It affects millions of individuals and countless businesses and
governments worldwide. The challenge lies in the fact that countries are not easily able to
close their borders to incoming cyber threats, nor can they contain those cyber threats
coming from within. Cyber security is thus a complex transnational issue that requires global
cooperation and solutions which are harmonised across borders in order to ensure a safe
internet for all.As the increasing proliferation of ICTs has far outpaced national and
international regulations governing them, international cooperation is required, at the
1
Conference website: psnmun.pathways.in
PATHWAYS SCHOOL NOIDA
Middle School Model UN Conference 2016
30th-31st August, 2016
Committee: GA-DISEC
Agenda: New Battlegrounds: The Future of Cyber Security and
Cyber Warfare
government level, as well as with industry, non-governmental and international
organisations. Individuals, organisations and countries must take steps to adopt measures
and procedures, and acquire tools to improve the way that technological and cyber-risks are
managed. An appropriate legal framework is necessary in order to address a range of issues
including: the problems of responsibility, consumer and child protection; the protection of
privacy and property rights, as well as the aterritorial nature of the Internet. Furthermore, it
is essential that any comprehensive approach towards cyber security takes into consideration
issues such as national security, state sovereignty, the cultural heritage of nations, as well as
the protection of critical infrastructure, systems, networks, goods and values, and the safety
of individuals.
What is Cyberspace?
Cyberspace is a domain characterized by the use of electronics and the electromagnet
spectrum to store, modify, and exchange data via networked systems and associated physical
infrastructures. In effect, cyberspace can be thought of as the interconnection of human
beings through computers and telecommunication, without regard to physical geography.
What is Cybersecurity?
Cybersecurity is defined by the International Telecommunication Union (ITU) as a
"collection of tools, policies, security concepts, security safeguards, guidelines, risk
management approaches, actions, training, best practices, assurance, and technologies that
can be used to protect the cyber environment, including organisations' and users' assets."
2
Conference website: psnmun.pathways.in
PATHWAYS SCHOOL NOIDA
Middle School Model UN Conference 2016
30th-31st August, 2016
Committee: GA-DISEC
Agenda: New Battlegrounds: The Future of Cyber Security and
Cyber Warfare
Cybersecurity includes topics related to cybercrime issues and to potential ICT or security
misuse, however, cyber security does not only entail fighting cybercrime.
Cybersecurity also concerns:
- Producing secure, transparent and third controlling products;
- The development of a reliable and safe behaviour in regard of the use of ICT;
- The development of a legal framework enforceable at national level and compatible at
international level.
What is Cyber Warfare?
Cyber Warfare can be defined as politically motivated hacking to conduct sabotage and
espionage. Government security expert Richard A. Clarke defined cyber warfare as actions
by a nation-state to penetrate another nations computers or networks for the purpose of
causing damage or disruption. The most common of these are espionage and national
security breaches, and sabotage. These methods are motivated by specific reasons.
What is Cyberterrorism?
While there is no single internationally agreed-upon definition for cyberterrorism, various
understandings of what comprises cyberterrorism have emerged in recent years.
Many people understand cyberterrorism according to the concept offered in the paper on the
issue from the Special Oversight Panel on Terrorism in 2000, which provides the following
explanation: Cyber Terrorism is the convergence of terrorism and cyberspace. It is
3
Conference website: psnmun.pathways.in
PATHWAYS SCHOOL NOIDA
Middle School Model UN Conference 2016
30th-31st August, 2016
Committee: GA-DISEC
Agenda: New Battlegrounds: The Future of Cyber Security and
Cyber Warfare
generally understood to mean unlawful attacks and threats of attack against computers,
networks, and the information stored therein when done to intimidate or coerce a
government or its people in furtherance of political or social objectives. In order for an
attack to qualify as cyberterrorism, it should result in violence against persons or property,
or at least cause enough harm to motivate fear.
The Center for Strategic and International Studies (CSIS) on the other hand, defines cyber
terrorism as, The use of computer network tools to shut down critical national
infrastructures (e.g., energy, transportation, government operations) or to coerce or
intimidate a government or civilian population.
Some argue that definitional problems surrounding cyberterrorism are in part due to the
definitional challenges surrounding terrorism, but also due to the nature of terrorists' use of
the Internet, cyberspace and IT is less well delineated and defined. The basic approach to
cyberterrorism as the convergence of cyberspace and terrorism includes not only
cyberterrorist attacks, but also terrorist use of cyberspace for various activities. Beyond
propaganda, cyberspace allows groups to gather and share information across great distances
with instant ease, and spread particular knowledge in new and innovative ways. What
terrorist groups value from the Internet is much the same as everyone else reliable service,
easy terms and virtual anonymity.
Furthermore, it is argued that cyberterrorism has similar motives to those of real-world
terrorism. Social, economic and political issues are motivations for these attacks.
Cyberterrorism aims to shut down critical national infrastructures, including government
operations, energy and transportation, in order to intimidate or coerce the population.
4
Conference website: psnmun.pathways.in
PATHWAYS SCHOOL NOIDA
Middle School Model UN Conference 2016
30th-31st August, 2016
Committee: GA-DISEC
Agenda: New Battlegrounds: The Future of Cyber Security and
Cyber Warfare
Intimidation of civilian enterprises also results from cyberterrorism, which works to
communicate social, economic or political beliefs that threaten countries around the world.
International and Regional Framework
While cyber security, cyber warfare, and cyber terrorism are relatively newer security
threats, many regional agreements and initiatives between states already exist to strengthen
cooperation on cyber security and deter breaches. One of the key regional conventions is the
Budapest Convention on Cybercrime (2001) adopted by the Council of Europe. The
convention, which entered into force in 2004, commits States Parties to standardize national
legislation and regulatory measures regarding cyber crime and related issues, including
criminal prosecution and jurisdiction. To address the relative novelty of cyber crime, as well
as its transnational nature, the convention takes a dual-pronged approach: tailoring domestic
criminal law to prosecute instances of cyber crime, and also creating procedures to support
greater international cooperation in this area. The convention additionally encourages greater
interstate cooperation and information sharing regarding cyber crime and preventative
security measures. While nearly all of the Council of Europe members are States Parties,
several other non-European states have also ratified the convention.
There is also an African regional convention, the African Union Convention on Cyber
Security and Personal Data Protection (2014). Adopted in 2014, this convention promotes
regional cooperation and provides a legal framework for strengthening cyber security and
combatting cyber crime. The convention was drafted to provide a holistic framework to
address the cyber security needs particular to the African continent and to prevent African
states from becoming safe havens for cyber criminals. While more than one year after its
5
Conference website: psnmun.pathways.in
PATHWAYS SCHOOL NOIDA
Middle School Model UN Conference 2016
30th-31st August, 2016
Committee: GA-DISEC
Agenda: New Battlegrounds: The Future of Cyber Security and
Cyber Warfare
adoption it has not yet been ratified by any signatory, many states have used it as a guide to
enact domestic cyber crime legislation.
In addition to regional arrangements, several United Nations bodies have also responded to
the increasing threat of cyber warfare and cyber crime. In 1999, the GA adopted resolution
53/70 on information technology and communications in relation to international security,
the first resolution on this topic. In addition to drawing an explicit link between information
and communication technologies (ICTs) and security, the resolution calls on states to outline
definitions and central concerns, and requests the Secretary-General prepare a report on the
topic. Since the resolution was adopted, the Secretary-General has produced several reports
to the GA outlining Member States perspective on the issue to share information and build
consensus on a way forward. In 2003, the GA passed resolution 58/32, which created a
Group of Governmental Experts (GGE) to assist the Secretary-General in drafting a report
on cooperative measures to combat cyber threats and strengthen cyber security measures.
The GGE has been renewed for several terms and is key in providing recommendations and
guiding the work of the General Assembly and the UN Secretariat in addressing this issue.
In 2013, the GA adopted resolution 68/167 on the right to \ privacy in the digital age. The
resolution notes that while states and international organizations should take measures to
combat cyber warfare, cyber crime, and serious informational breaches, these should not be
allowed to violate human rights, particularly ones right to privacy. In 2014, the GA adopted
resolution 69/28, based on the GGEs most recent report on Developments in the field of
information and telecommunications in the context of international security. The resolution
calls on all Member States to consider pressing cyber security threats, and to discuss and
communicate strategies to combat these threats to encourage a collaborative and multilateral
approach.
6
Conference website: psnmun.pathways.in
PATHWAYS SCHOOL NOIDA
Middle School Model UN Conference 2016
30th-31st August, 2016
Committee: GA-DISEC
Agenda: New Battlegrounds: The Future of Cyber Security and
Cyber Warfare
Role of the International System
Many UN bodies are engaged in issues around cyber security and cyber warfare. In addition
to the creation of the GGE and the adoption of multiple resolutions on the topic, the GA
First Committee has sought to increase dialogue and cooperation by requesting that Member
States submit their views on international law and opportunities for cooperation in
cyberspace, which many states have done. Many states within the GA have expressed the
need to discuss concrete measures for cyber security improvements, particularly information
sharing and confidencebuilding measures (CBMs). The latest GGE report also provides a set
of recommendations to the General Assembly, including greater investment in researching
ICT threats and increasing multilateral dialogue and cooperation in addressing these threats.
In the recently adopted resolution 69/28 on Developments in the field of information
technology and telecommunications in the context of international security, the GA
recognized the importance of greater cooperation on this topic but did not provide for any
concrete action to achieve it. The GA added this topic to the provisional agenda of the
Assemblys 70th session, and the issues were discussed in the October 2015 meetings in the
First Committee. Some Member States stated their belief for the need of a comprehensive,
overarching approach to cybersecurity that accounted for state specific security
deficiencies, while others maintained that existing international law was best for cyberstability and information security with the addition of specific cyber-related provisions; the
different perspectives on cyber security highlight the fragmentation amongst Member States
on achieving unified solutions.
The International Telecommunication Union (ITU), the UN agency focused on information
and communication technology, is heavily involved within this topic. The ITU writes reports
7
Conference website: psnmun.pathways.in
PATHWAYS SCHOOL NOIDA
Middle School Model UN Conference 2016
30th-31st August, 2016
Committee: GA-DISEC
Agenda: New Battlegrounds: The Future of Cyber Security and
Cyber Warfare
and recommendations on increasing technological and telecommunications access, as well as
identifying emerging threats and challenges. In 2007, the ITU launched the Global
Cybersecurity Agenda (GCA), a collaborative platform to encourage cooperation and
information sharing on cyber-security centered on the following five pillars: legal measures,
technical and procedural measures, organizational structures, capacity building, and
international cooperation. The GCA is guided by the High-Level Experts Group (HLEG), a
group of cyber-security experts, which provides information and recommendations on
strengthening cyber security to Member States and relevant stakeholders working on this
issue.
The ITU also hosts the World Summit on Information Societies (WSIS), an
intergovernmental forum established in 2001.139 While the fundamental goal of WSIS is to
universalize access to ICTs, it also notes that to build a global information society, there
must be a global culture of cybersecurity to protect users and encourage broader use and
applications. In 2005, WSIS agreed to a set of outcome goals contained within the Tunis
Agenda for the Information Society. The goals include expanding access to information
technologies, encouraging international and regional cooperation, including capacitybuilding and information-sharing, and building confidence and enhancing security measures
in the use of ICTs. In December 2015, the GA will hold the WSIS+10 Review to evaluate
the implementation and achievement of these goals on a national and international level.
In addition to the ITU, the United Nations Office for Disarmament Affairs (UNODA) and
the United Nations Institute for Disarmament Research (UNIDIR) have made important
contributions towards understanding current security threats and identifying gaps in national
and international security and legislation. UNIDIR has written numerous reports on the
relationship between information technology and international peace and security,
8
Conference website: psnmun.pathways.in
PATHWAYS SCHOOL NOIDA
Middle School Model UN Conference 2016
30th-31st August, 2016
Committee: GA-DISEC
Agenda: New Battlegrounds: The Future of Cyber Security and
Cyber Warfare
particularly in the way these systems may be used to control weapons systems. Additionally
UNIDIR has produced important research on the legality of certain cyber security
mechanisms and how international law might address these particular forms of attacks and
terrorism. UNODA and UNIDIR also provide recommendations for best practices that guide
the General Assembly and the Secretary-General.
Individual Member States have also made important contributions in strengthening cyber
security mechanisms. Many states, including the United Kingdom and the United States,
have dedicated domestic offices and initiatives for cyber security. Internationally, many
developed states are investing in technical support and capacity building projects aimed at
strengthening developing states ability to respond to cyber threats. States have also signed
regional and bilateral partnerships, such as the one between the United States and Canada, to
increase cooperation, but these are generally with close regional partners and have not
expanded to include a wider international context.150 Additionally multilateral programs are
playing a larger role in international cooperation, such as the Commonwealth Cybercrime
Initiative (CCI), which was created at a multilateral forum of Commonwealth states in 2011.
The CCI aims to increase cooperation and information-sharing between Commonwealth
states, as well as various international and regional organizations, to reduce cyber crime and
strengthen accountability and enforcement mechanisms.
Cyber security and cybercrime also have important implications for civil society, and many
international organizations are taking steps which include private sector businesses and civil
society organizations as key stakeholders in their programs and discussions.153 Some civil
society organizations, such as the Global Information Society Watch (GISWatch), monitor
and interact with states to ensure equal access to ICTs; GISWatch also publishes reports on
states progress in reaching the WSIS goals.154 Human rights organizations, including
9
Conference website: psnmun.pathways.in
PATHWAYS SCHOOL NOIDA
Middle School Model UN Conference 2016
30th-31st August, 2016
Committee: GA-DISEC
Agenda: New Battlegrounds: The Future of Cyber Security and
Cyber Warfare
Human Rights Watch and Amnesty International, have also become engaged in this issue,
raising discussions about the overlap between cyber security measures and human rights,
such as ensuring the right to privacy and freedom of expression.
Timeline
1941 - Because of its usefulness in World War II to decode Japanese transmissions, the
SIGINT cooperation is finalized and establishes its importance in the world.
1942 - The Central Bureau of the Allied Intelligence Bureau for the Pacific is instated in
Melbourne, maintained by a US Chief and an Australian Deputy Chief.
1947- The first general purpose electronic computer is introduced.
1982 - Soviet gas pipeline explodes due to logic bomb, in one of the earliest instances of
cyber exploitation.
1988 - Mainly in the US, the Morris worm is spread to computers, which slows the machines
down to unusable conditions. It is one of the first worms to affect the emerging global cyber
infrastructure.
1998 - During the Kosovo war, the US hacks into Serbian air force programs.
2001 The Nimda computer virus attacks financial systems, causing major economic
damage.
10
Conference website: psnmun.pathways.in
PATHWAYS SCHOOL NOIDA
Middle School Model UN Conference 2016
30th-31st August, 2016
Committee: GA-DISEC
Agenda: New Battlegrounds: The Future of Cyber Security and
Cyber Warfare
2006 - NASAs plans for US space launch vehicles are hacked by unknown overseas
intruders. NASA is forced to block all attachments in emails before the launch.
April 2007 - After a disagreement with Russia, Estonia is hacked by foreign intruders.
Online government services and banking are halted. However, the Estonian government
responds immediately and resolves the issue in just a few days.
June 2007 - Unknown infiltrators hack into The US Secretary of Defenses email account in
order to access and utilize the Pentagons network.
October 2007 - After spyware was discovered in the networks of designated departments,
The Peoples Republic of Chinas Ministry of Security states that overseas hackers, with
about 42% of them from Taipei and another 25% of them from the United States, have been
stealing key information from the Chinese network.
2008 - Cyber-attacks take on major roles in the Russia-Georgia conflict.
2009 - Israels internet infrastructure is hacked during the Gaza Strip military offensive.
With a focus mainly on government databases, the attack is carried out to approximately
5,000,000 computers.
2010 - The Iranian Cyber Army disrupts the service of Twitter as well as Baidu, the wellknown Chinese search engine, by redirecting pages to display a political message from Iran.
11
Conference website: psnmun.pathways.in
PATHWAYS SCHOOL NOIDA
Middle School Model UN Conference 2016
30th-31st August, 2016
Committee: GA-DISEC
Agenda: New Battlegrounds: The Future of Cyber Security and
Cyber Warfare
2010 - Stuxnet, a malware piece designed to disrupt Siemens industrial control databases, is
found in Iran and Indonesia. Speculations postulate that Stuxnet is a cyber weapon made by
governments aiming to disrupt the Iranian nuclear program.
January 2011 - A major cyber attack forces Canadian major economic agencies, the Finance
Department and Treasury Board, to unplug from the Internet.
July 2011 - The US Deputy Secretary of Defense states that a major defense contractor was
hacked and 24,000 files were taken from the Department of Defense.
2012 - Kaspersky, a Russian cyber security firm, discovers a global cyber attack mechanism
called the Red October that has been used since 2007 to steal critical government embassy
and nuclear infrastructure information through vulnerabilities in Microsoft programs. The
attack is primarily focused in Eastern Europe, Central Asia, and the former USSR.
June 2013 - The first meeting for cyber defense is held. NATO Defense Ministers stated that
cyberdefense should be immediately operational to protect the networks of NATO member
nations.
October 2013 - The NATO Computer Incident Response Capability (NCIRC) project is
completed to help NATO combat the increasing number of cyber-attacks in its member
states.
2014 - NATO adopts a new policy, which states that cyber defense is part of the Alliances
key collective defense and ensures that international law is applicable in cyberspace.
12
Conference website: psnmun.pathways.in
PATHWAYS SCHOOL NOIDA
Middle School Model UN Conference 2016
30th-31st August, 2016
Committee: GA-DISEC
Agenda: New Battlegrounds: The Future of Cyber Security and
Cyber Warfare
2015 - A Russian hacking division, The Dukes, is discovered after allegedly attacking
governments and organizations in foreign nations for seven years.
Historical Context
In a world where the population is becoming ever more reliant on computers for day-to-day
life, digital attacks have the potential to be devastating. The currently underdeveloped
system of rules and regulations in cyberspace and the relatively low cost building a cyberweapon can mean that small groups, and even individuals, could use computer technology to
wage war against entire continents. To illustrate the historical context of cybersecurity, we
consider multiple case studies of cyberwarfare in the past.
The Logic Bomb (1980s)
In June of 1982, during the Cold War, a large blast in Siberia was detected. A Soviet gas
pipeline had exploded, but this was no normal explosion. It turns out that the cause was a
malfunction in the computer-based system that ran the pipeline. According to Thomas Reed,
a former Secretary of the U.S. Air Force, the CIA had corrupted the software so that the
pipeline exploded in a ball of flame that was the most monumental non-nuclear explosion
and fire ever seen from space. This was one of the first uses of a logic bomb.
A logic bomb is malicious software that, when activated causes widespread damage of
computer systems. In the early days of cyberwarfare, logic bombs were rarely used (the
pipeline explosion is the only example). However, throughout the Cold War, Soviet and
American spies used information technology to extract information and compromise enemy
13
Conference website: psnmun.pathways.in
PATHWAYS SCHOOL NOIDA
Middle School Model UN Conference 2016
30th-31st August, 2016
Committee: GA-DISEC
Agenda: New Battlegrounds: The Future of Cyber Security and
Cyber Warfare
plans. While cyber-attacks during the 1980s were basic by todays standards they set the
stage for increasingly dangerous and frequent attacks in the next decade.
Increased Use (1990s)
Due to the increased connectivity of computers and an increasingly sophisticated hacker
community, the 1990s saw more and more instances of cyber-attacks. Governments such as
China began to recognize the possibility of cyber warfare and started up preliminary military
programs. The ease with which cyber-attacks could be launched is evidenced in the United
States 1997 military exercise Eligible Receiver, in which team of hackers from the
National Security Agency were asked to hack into the Pentagons systems. Though some
details are still classified it is known that the group was able to infiltrate the power grid and
911 systems of 9 major US cities. Cyber weapons were also used for the first time as an
adjunct to standard warfare during this period. In an interview with PBS, John Arquilla
mentioned that during the Kosovo war, the United States used technology to distort images
used by Serbian air defense systems. In the late 90s, the dangerous nature of cyber-attacks
was recognized by many governments and media sources and cyber-warfare became a
realistic concern.
Commonplace Cyber Attacks (2000s)
As more and more people began using the internet for business and social purposes, cyber
attacks expanded from the realm of secret nation to nation conflict to attacks on business and
personal computers. Worms, viruses and Trojan horses began popping up all over the
internet. The Nimda worm, released in 2001, spread quickly, causing devastating economic
14
Conference website: psnmun.pathways.in
PATHWAYS SCHOOL NOIDA
Middle School Model UN Conference 2016
30th-31st August, 2016
Committee: GA-DISEC
Agenda: New Battlegrounds: The Future of Cyber Security and
Cyber Warfare
damage and becoming the internets most widespread cyber attack. That same year, in the
summer of 2001, the US detected a suspicious pattern of intrusions into the infrastructure of
various American cities. These probes came from the Middle East and were extracting
information on the cities utilities and emergency systems. After 9/11 Al Qaeda computers
were seized and it appears that the probes may have been related to terrorist activity. In the
early 2000s more and more countries began cyber warfare military programs and as
technology advanced, so did the ease with which cyber-attacks could be performed. Even
smaller countries such as Israel began using cyber weapons to disrupt their enemys systems.
The first instance of widespread cyber attack on a nation occurred in April 2007. After the
Estonian government decided to move a Soviet war memorial away from its capital city of
Tallinn, the government, bank and media servers of Estonia were hit with a massive cyber
attack. Known as Web War I, groups of hackers (suspected to be working for Russia) used
computers around the globe to launch a denial of service attacks to bring down the internet
in Estonia. Denial of service attacks flood a website with fake requests and cause an
information overload. The attack on Estonia was more of a cyber-riot than a war but
effectively cut Estonia off from the internet and showed the potential for a more serious
attack in the future. Merely a year later, there was once again a major cyber attack in the
Caucasus region. In August 2008, Russia physically invaded Georgia. The physical attack
was accompanied by a sophisticated cyber attack that denied Georgians access to news cash
and transportation tickets. The Georgian government found it difficult to communicate with
its citizens and the outside world and Georgian websites were defaced with Russian
propaganda. Russia denied any state sponsored cyber attack on Georgia and claimed it was
the work of radical Russian nationalists around the world. While Russia has been active in
cyber activity, it is by no means the only country to be accused of cyber-warfare. In 2009,
two major attacks were launched from computer servers based in China; Ghost Net and
15
Conference website: psnmun.pathways.in
PATHWAYS SCHOOL NOIDA
Middle School Model UN Conference 2016
30th-31st August, 2016
Committee: GA-DISEC
Agenda: New Battlegrounds: The Future of Cyber Security and
Cyber Warfare
Operation Aurora. Ghost Net was a large-scale cyber espionage project that tapped into the
computers of many governments, corporations and Tibetan rebels. Later in 2009, Operation
Aurora was an attack on foreign corporations, the most notable being Google. Intellectual
property was stolen from the companies and Google responded by removing censors on its
website in China. During the last ten years cyber-attacks have continued to evolve. Though
they have yet to cause massive physical damage or loss of human life, attacks have been
widespread. Governments, corporations, citizens, in both NATO nations and the world at
large are all at risk.
Current Situation & Analysis of Cyber-Attack Trends:
To understand the realm of cybersecurity, it is critical that the mechanisms of cyber-attacks
are considered. There are three main areas of concern when it comes to cyber-warfare:
information warfare (cyber espionage), nation to nation attacks, and independent, radical
attacks (cyber terrorism).
Limited Cyber Attacks
Many so called cyber-attacks have not actually been all that potent. These attacks, known as
limited cyber-attacks, slow down websites, block internet access and spread propaganda.
Nationalists from countries such as Russia and China have been known to hamper
opponents websites and partake in web-graffiti. The denial of service attacks on Estonia
is a recent example of this kind of attack. Though these attacks are an inconvenience they
are not particularly dangerous. Nevertheless, there should be some rules that prevent the
16
Conference website: psnmun.pathways.in
PATHWAYS SCHOOL NOIDA
Middle School Model UN Conference 2016
30th-31st August, 2016
Committee: GA-DISEC
Agenda: New Battlegrounds: The Future of Cyber Security and
Cyber Warfare
many limited attacks that occur worldwide, they disrupt a nations affairs and are carried
out with malicious intent.
Cyber Espionage
Cyber espionage is the infiltration of secure systems in order to steal information. It is the
first step in the cyber warfare process. Traditional spies risk arrest by trying to smuggle
information out of hostile countries, in cyberspace there are none of these risks. Cyber spies,
if given enough time and resources will almost always be able to penetrate a targeted
system. Adding to the problem is the fact that cyber spies can steal vast amounts of
information, more than traditional spies ever dreamt of stealing. A spy might once have
been able to take a few books worth of materialnow they can take the whole library, a
senior American official said. Recently, China has come under fire for wholesale espionage.
Governments and corporation are worried that the loss of information could damage their
economic advantages, or, in the case of governments, affect their military capability. Jim
Lewis, of the Centre for Strategic and International Studies says Cyber espionage is the
biggest intelligence disaster since the loss of nuclear secrets. Stolen information can be
used for nefarious purposes. In order to ensure the safety of people around the world, Cyberespionage needs to be brought under control.
Unrestricted Cyber Attacks
These types of cyber-attacks are extremely dangerous. Unrestricted cyber-attacks target both
the military and civilians and cause physical or economic damage and/or loss of life. Experts
fear that cyber-attacks could go after power grids or vital city infrastructure. A loss of power
17
Conference website: psnmun.pathways.in
PATHWAYS SCHOOL NOIDA
Middle School Model UN Conference 2016
30th-31st August, 2016
Committee: GA-DISEC
Agenda: New Battlegrounds: The Future of Cyber Security and
Cyber Warfare
in a major country such as the U.S would have severe economic implications31. Other
potential targets include satellites, traffic grids and factories/chemical plants. A logic bomb
planted in a factory of plant has the potential to be devastating. Though there have been no
unrestricted cyber-attacks in recent years, governments are responding to the growing threat
with military power. America has set up a Cyber Command to defend its network and to
retaliate if attacked by a rival nation or group. Unrestricted attacks are frightening due to
their unpredictability. A terrorist group such as Al Qaeda, giving the right funding and
technology could attack infrastructure relatively easily at any given moment. If the threat of
unrestricted cyber-attacks is not dealt with promptly, there will be dire
consequences.
Conclusion
The increasing use of ICTs to carry out criminal activities, threats, and attacks make it a
critical issue in the maintenance of international peace and security. While some regions and
many states have adopted treaties on cyber crime and cyber security, reducing the threat of
cyber warfare requires a unified global response. The technological innovation broadening
access to global financial activity presents a catalyst for many forms of cyber warfare, and
the anonymity of online networks thwarts many efforts to reduce financing and prosecute
those responsible. The infiltration and disruption of military intelligence and weapons
systems poses risks to innocent lives and at worst, risks a global catastrophe. Many states
secrecy and competitiveness regarding military security has prevented fruitful discussions on
information-sharing and best practices for security measures. Finally, attributing
accountability and prosecuting individuals and/or groups responsible for acts of cyber
warfare remains difficult as state approaches vary significantly. The nature of cyber
18
Conference website: psnmun.pathways.in
PATHWAYS SCHOOL NOIDA
Middle School Model UN Conference 2016
30th-31st August, 2016
Committee: GA-DISEC
Agenda: New Battlegrounds: The Future of Cyber Security and
Cyber Warfare
networks and information technology increases global interconnectedness, but this
interconnectedness can also proliferate security threats between states and international
actors. In order to address these challenges to cyber security, a cooperative, multilateral
approach is needed.
Further Research
In preparing for this topic, delegates should consider how the General Assembly can address
these challenges and build towards a more unified approach on cyber security. Specifically,
delegates should consider: What legal frameworks would be helpful in drafting legislation
on this topic? Delegates may also want to consider alternatives to legislation, such as
capacity-building, CBMs, and the implementation of existing and new legislation. How can
key challenges, including lack of coordination, multiple points of enforcement, and
challenges of jurisdiction be overcome? Which UN organs and agencies would be wellsuited to assist in strengthening cyber-security measures?
Sources:
1. (http://www.huffingtonpost.com/lia-petridis/between-doom-and-hesitantoptimism_b_3424313.html)
2. (http://www.itu.int/ITU-D/cyb/publications/2009/cgdc-2009-e.pdf)
3. (http://www.huffingtonpost.com/lia-petridis/between-doom-and-hesitantoptimism_b_3424313.html)
4. UNODC, Comprehensive Study on Cybercrime, 2013, p. xi.
5. Council of Europe, Convention on Cybercrime, 2001.
19
Conference website: psnmun.pathways.in
PATHWAYS SCHOOL NOIDA
Middle School Model UN Conference 2016
30th-31st August, 2016
Committee: GA-DISEC
Agenda: New Battlegrounds: The Future of Cyber Security and
Cyber Warfare
6. AU, African Union Convention on Cyber Security and Personal Data Protection, 2014.
7. Fidler, The African Union Cybersecurity Convention: A Missed Human Rights
Opportunity, Council on Foreign Relations, 2015.
8. UN
General
Assembly,
Developments
in
the
field
of
information
and
telecommunications in the context of international security (A/RES/58/32), 2003.
9. UN General Assembly, The Right to Privacy in the Digital Age (A/68/167), 2013.
10. War in the Fifth Domain The Economist July 3rd 2010
11. Tech Sabotage during the Cold War
http://web.archive.org/web/20071228164807rn_1/www.fcw.com/print/10_12/news/8270
9-1.html
12. http://www.pbs.org/wgbh/pages/frontline/shows/cyberwar/warnings/
13. http://www.pbs.org/wgbh/pages/frontline/shows/cyberwar/interviews/arquilla.html
14. Nimda Worm Information http://www.f-secure.com/v-descs/nimda.shtml
15. http://www.pbs.org/wgbh/pages/frontline/shows/cyberwar/warnings/
16. http://www.military.com/features/0,15240,210486,00.html
17. http://www.law.duke.edu/journals/dltr/articles/2010dltr003.html#41
18. http://www.nytimes.com/2009/04/28/us/28cyber.html?pagewanted=3&_r=1&ref=techno
logy
19. http://www.nato.int/docu/review/2001/0104-04.htm
20. UN
Report
on
Cybersecurity
http://www.cfr.org/publication/9161/un_report.html
September 15th, 2010.
20
Conference website: psnmun.pathways.in
You might also like
- High Court of Judicature For Rajasthan Jodhpur: (Downloaded On 09/12/2022 at 10:25:00 AM)Document1 pageHigh Court of Judicature For Rajasthan Jodhpur: (Downloaded On 09/12/2022 at 10:25:00 AM)CharuMathurNo ratings yet
- Delhi High Court Ruling on SCC Online Legal DatabaseDocument23 pagesDelhi High Court Ruling on SCC Online Legal DatabaseCharuMathurNo ratings yet
- High Court Judgment on RAS Exam ScribeDocument4 pagesHigh Court Judgment on RAS Exam ScribeCharuMathurNo ratings yet
- High Court of Judicature For Rajasthan Bench at Jaipur: Ashwani/-47Document1 pageHigh Court of Judicature For Rajasthan Bench at Jaipur: Ashwani/-47CharuMathurNo ratings yet
- The Industrial Disputes ActDocument71 pagesThe Industrial Disputes ActsharmarohitmsNo ratings yet
- High Court of Judicature For Rajasthan Bench at Jaipur: Upendra Pratap Singh /64Document1 pageHigh Court of Judicature For Rajasthan Bench at Jaipur: Upendra Pratap Singh /64CharuMathurNo ratings yet
- Sequence of Matters For MondayDocument2 pagesSequence of Matters For MondayCharuMathurNo ratings yet
- 1988Document4 pages1988CharuMathurNo ratings yet
- Display PDFDocument1 pageDisplay PDFCharuMathurNo ratings yet
- P-1282 Evaluation ReportDocument3 pagesP-1282 Evaluation ReportCharuMathurNo ratings yet
- 2+Combined+Annexures ResizedDocument190 pages2+Combined+Annexures ResizedCharuMathurNo ratings yet
- (Fresh (For Admission) - Civil Cases) : Supplementary ListDocument2 pages(Fresh (For Admission) - Civil Cases) : Supplementary ListCharuMathurNo ratings yet
- Prevention of Sexual Harassment at WorkplaceDocument35 pagesPrevention of Sexual Harassment at WorkplaceCharuMathur100% (1)
- 143748Document1 page143748CharuMathurNo ratings yet
- UNSC Background GuideDocument44 pagesUNSC Background GuideCharuMathurNo ratings yet
- South China Sea RulingDocument501 pagesSouth China Sea RulingAnonymous zBCMh8j100% (1)
- WWW - Livelaw.In: Signature Not VerifiedDocument138 pagesWWW - Livelaw.In: Signature Not VerifiedCharuMathurNo ratings yet
- Syria UK Non-Humanitarian Support - Public DocumentDocument2 pagesSyria UK Non-Humanitarian Support - Public DocumentCharuMathurNo ratings yet
- CBP 7213Document184 pagesCBP 7213CharuMathurNo ratings yet
- Unit 1.2 Settlement RevisionDocument15 pagesUnit 1.2 Settlement RevisionifeNo ratings yet
- Service LawDocument30 pagesService LawCharuMathurNo ratings yet
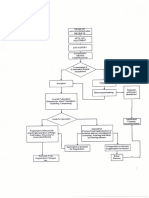
- TMR FlowChart 09june2016Document1 pageTMR FlowChart 09june2016CharuMathurNo ratings yet
- Consumer ProtectionDocument25 pagesConsumer ProtectionCharuMathurNo ratings yet
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (894)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (587)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (265)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (119)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- Us Army Helicopter MaintenanceDocument296 pagesUs Army Helicopter MaintenanceDave Gagliostro100% (5)
- Afghanistan: A Guide to Diverse Culture and HistoryDocument5 pagesAfghanistan: A Guide to Diverse Culture and HistoryNosce Te IpsumNo ratings yet
- Weapons An International Encyclopedia From 5000 BC To 2000 AD The Diagram Group Text PDFDocument340 pagesWeapons An International Encyclopedia From 5000 BC To 2000 AD The Diagram Group Text PDFMauricio Mesa Jaramillo100% (5)
- 23 3 ET V1 S1 Range EquationDocument35 pages23 3 ET V1 S1 Range EquationRajuNo ratings yet
- Map - UNTSODocument1 pageMap - UNTSOcartographica100% (3)
- Classification LevelsDocument20 pagesClassification LevelsSenen SeanNo ratings yet
- A Literature Review of Common Techniques For Hiding Data, and The Methods That Are Used To Find ThemDocument15 pagesA Literature Review of Common Techniques For Hiding Data, and The Methods That Are Used To Find ThemNitin GuliaNo ratings yet
- Bishop Cotton Boys' School: Bangalore: Final Examination: March 2014 Subject: General KnowledgeDocument6 pagesBishop Cotton Boys' School: Bangalore: Final Examination: March 2014 Subject: General KnowledgeSandhya SriramanNo ratings yet
- Philippine Civil-Military RelationsDocument28 pagesPhilippine Civil-Military RelationsJade ManteNo ratings yet
- Nagaland & Naga RegimentDocument4 pagesNagaland & Naga RegimentJose SebastianNo ratings yet
- A/T "Cyber Attacks in The Past"Document3 pagesA/T "Cyber Attacks in The Past"linuspauling101No ratings yet
- Cv. Gustaf Adolf Manuhua - PumpmanDocument2 pagesCv. Gustaf Adolf Manuhua - PumpmanJevrieko SatriaNo ratings yet
- Transformable Multiple Use of Assault Bridge With 48 Meter SpanDocument7 pagesTransformable Multiple Use of Assault Bridge With 48 Meter SpanTun Hlaing WinNo ratings yet
- Secret Codes-Ken BeattyDocument64 pagesSecret Codes-Ken BeattyElena ManeaNo ratings yet
- Bharat Swabhiman FormDocument2 pagesBharat Swabhiman FormKingsuk NandiNo ratings yet
- Deliso - The Coming Balkan Caliphate The Threat of Radical Islam To Europe and The WestDocument241 pagesDeliso - The Coming Balkan Caliphate The Threat of Radical Islam To Europe and The Westpeterakiss100% (4)
- Adventure Shorts Volume 1 (5e)Document20 pagesAdventure Shorts Volume 1 (5e)admiralpumpkin100% (5)
- MATH 2Z03 Midterm 1 Supplement Solutions F21 FINALDocument69 pagesMATH 2Z03 Midterm 1 Supplement Solutions F21 FINALYousef HassaninNo ratings yet
- Ch11 AlignmentDocument12 pagesCh11 AlignmentNuttaphon SathonNo ratings yet
- Turas Math DhutDocument52 pagesTuras Math DhutAnonymous WUSxJ3rNo ratings yet
- JoA SIEGE Scenario Book ENG v3Document24 pagesJoA SIEGE Scenario Book ENG v3Wolf WingsNo ratings yet
- MKII Hordes Primal PDFDocument249 pagesMKII Hordes Primal PDFleotardnimoy100% (2)
- The U.S. M1911 and M1911A1 Pistols & Commercial M1911 Type Pistols - A Shop ManualDocument208 pagesThe U.S. M1911 and M1911A1 Pistols & Commercial M1911 Type Pistols - A Shop Manualblowmeasshole191189% (36)
- Fifth Grade Revolution Lesson 10 PT 2 Patriot Loyalist or Neutral-You Decide ActivityDocument4 pagesFifth Grade Revolution Lesson 10 PT 2 Patriot Loyalist or Neutral-You Decide Activityapi-249283966No ratings yet
- Acp Iace BriefingDocument33 pagesAcp Iace BriefingKatrina Mae SanchezNo ratings yet
- Wacker Neuson Wheel Dumper Dw90 Operator Service Manual Spare Parts CatalogDocument22 pagesWacker Neuson Wheel Dumper Dw90 Operator Service Manual Spare Parts Catalogmelvinsimpson190382tes100% (107)
- UTS LA, Yuliani, E1D018126, 6TP-2Document5 pagesUTS LA, Yuliani, E1D018126, 6TP-2Yuli KebgeqNo ratings yet
- Napoleon EmpireDocument2 pagesNapoleon EmpireRosemary714No ratings yet
- 3.parliamentary Committee System in Bangladesh23-35Document14 pages3.parliamentary Committee System in Bangladesh23-35iisteNo ratings yet
- Command Protocols Escalation INC FAQ 2.3Document121 pagesCommand Protocols Escalation INC FAQ 2.3ElanusNo ratings yet