Professional Documents
Culture Documents
Materi Analisis Dan Design Algoritma
Uploaded by
jesyameliaOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Materi Analisis Dan Design Algoritma
Uploaded by
jesyameliaCopyright:
Available Formats
CSE 5311 Design and Analysis of Algorithms
Sample Questions
The quiz will have questions for approx. 70 minutes
1. Choose the MOST appropriate answer and circle the letter corresponding to
your answer.
(15 Minutes)
The penalty for each INCORRECT answer is 0.25 point.
i)
Input comprises a sorted list of n integers with many duplications such
that the number of distinct integers in the sequence is O (log n), the
time complexity to find an element in the list is given by,
A. O(n)
ii)
B. O(log n)
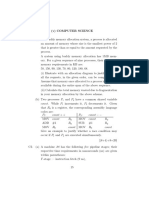
The residual capacity of the augmenting path for the network shown
below is
A. 1
B. 2
C. 3
1/1
D. 7
c
1/1
1/1
s
t
0/3
0/2
b
iii)
D. (1)
C. O(log log n)
0/2
Which of the following is not O (n2)
C. 105n + 26n
A. n + 10000n
B. n1.9999
iv)
The augmenting path in a flow network
A. determines the edge connectivity of a network
B. comprises edges which can admit positive flow
C. converts a tree network into a cyclic chain
D. is used only for cyclic chain networks
v)
We employ dynamic programming approach when
A. It gives optimal solution
B. The solution has optimal substructure
C. It is faster than Greedy technique
D. n3/n
D. The given problem can be reduced to the 3-SAT problem.
vi)
A problem is said to be NP-Complete
A. If it is as hard as any problem in NP
B. A non-polynomial time algorithm has been discovered
C. A polynomial time algorithm can exist but needs a parallel computer
D. There is Greedy solution to the problem
vii)
Which of the following problems is known to have a polynomial time
solution
A. Longest simple path problem for a given graph
B. The 3-colorability problem in graphs
C. The Eulerian cycle in a graph
D. The Hamiltonian Cycle in a graph
viii)
The distance matrix of a graph with vertices P,Q, R and S is given by
0
3
1
1
0 2 4
0 1
0
The shortest path from Q to S consists of edges
A. QR and RS
B. QS
C. PQ and RS
D. there is no path
ix)
Which of the following basic algorithms can be used to most efficiently
determine the presence of a cycle in a given graph
A. minimum cost spanning tree algorithm
B. Ford-Fulkersons algorithm
C. breadth-first search algorithm
D. depth-first search algorithm
x)
Working modulo q= 11, how many spurious hits does the Rabin-Karp
matcher encounter in the text T = 31415926 when looking for the
pattern P = 26
A. None B. One
C. Two
D. Three
2. State whether the following statements are TRUE or FALSE
(15 Minutes)
Penalty for each incorrect answer is 0.5 point
i)
If f(n) = O g(n) and g(n) = O (h(n)) then f(n) = (h(n))
ii)
A binary search tree on n integer keys in the range from 1 to n2
can be constructed in O(n) worst-case time.
iii)
Kruskals algorithm of finding a minimum spanning tree of a
weighted undirected graph is an example of a dynamic
programming algorithm.
iv)
The transitive closure of a directed graph G = (V, E) can be
computed in O(v2) time by the Floyd-Warshall algorithm, which
repeatedly squares the adjacency matrix of G.
v)
The (log n) th smallest number of n unsorted numbers can be
determined in O(n) worst-case time.
vi)
The worst-case running time randomized quicksort on an array of
length n is (n2).
vii)
In the bitonic merge-sorting network, there are n/2 stages with
log n switches per stage.
viii)
The recurrence for mergesort algorithm can be written as
T(n)=2T(n/2)+ (n)
ix)
The time complexity of the Heapify algorithm is O(n).
x)
The asymptotically tight upper bound for T(n) = T(n-2) + 1 is
O (log n).
3. Consider a set S of n 2 distinct numbers given in unsorted order and,
x and y are two distinct numbers in the set S. Write an O(n) time
algorithm to determine x, y S such that x-y w-z for all w,z S.
(15 Minutes)
4. Examine the procedure DOES_SOMETHING below and answer the
following questions.
(15 Minutes)
a. What is the function of the procedure DOES_SOMETHING?
b. What is the time complexity of the procedure?
c. If A[l .. r] = [24, 30, 09, 46, 15, 19, 29, 86,78], what is the output?
Procedure DOES_SOMETHING(A,l,r)
Input : Array A(l .. r)
1.
2.
3.
4.
5.
6.
7.
8.
x A[l]; i l; j r;
while i < j do
while A[i] x and i r do i i +1;
while A[j] > x and j l do j j -1;
if i< j then
exchange A[i] A[j];
q j;
exchange A[l] A[q];
5. Show how to compute the length of an LCS (Longest Common Sequence)
using only min (m,n) entries in an array plus O(1) additional space. (15 Minutes)
6. A graph is bipartite if all its vertices can be partitioned into two disjoint subsets
X and Y so that every edge connects a vertex in X with a vertex in Y. Design an
algorithm to check whether a given graph is bipartite.
(15 Minutes)
7. What is an optimal Huffman code for the following set of frequencies, based on
the first 8 Fibonacci numbers?
a:1
b:1
c:2
d:3
e:5
f:8
g:13 h:21
Can you generalize your answer to find the optimal code when the frequencies
are the first n Fibonacci numbers?
(15 Minutes)
You might also like
- CSE 5311 Sample Quiz QuestionsDocument4 pagesCSE 5311 Sample Quiz QuestionsSandeep ChaurasiaNo ratings yet
- CA Question BankDocument13 pagesCA Question Bankaryanbamane2003No ratings yet
- Algorithms - Exam 2021-2022 Model AnswerDocument4 pagesAlgorithms - Exam 2021-2022 Model AnswerAhmed MabrokNo ratings yet
- AlgorithmDocument14 pagesAlgorithmSachin MichuNo ratings yet
- Capgemini Pseudo Code MCQsDocument10 pagesCapgemini Pseudo Code MCQsSristi KumariNo ratings yet
- Algorithms and Data Structures Sample 3Document9 pagesAlgorithms and Data Structures Sample 3Hebrew JohnsonNo ratings yet
- Advanced Algorithms MCQDocument14 pagesAdvanced Algorithms MCQmathuNo ratings yet
- Ahuja1990 FasterDocument11 pagesAhuja1990 FasterdnyNo ratings yet
- MCQ, Design and Analysis of AlgorithmDocument19 pagesMCQ, Design and Analysis of AlgorithmSK DUDE100% (1)
- Gate-Cs 2006Document31 pagesGate-Cs 2006tomundaNo ratings yet
- Gate-Cs 2005Document31 pagesGate-Cs 2005tomundaNo ratings yet
- ExamDocument9 pagesExamSyed Ahsan HabibNo ratings yet
- Question Bank: Unit I Subjective QuestionsDocument33 pagesQuestion Bank: Unit I Subjective QuestionsChandra Shekar Reddy TummuriNo ratings yet
- CS Gate 20101Document29 pagesCS Gate 20101roshni_lingalaNo ratings yet
- Final Exam 2017 - CO4403Document4 pagesFinal Exam 2017 - CO4403vs sNo ratings yet
- True or False: StackDocument15 pagesTrue or False: StackAmro AbosaifNo ratings yet
- MCS 031 NotesDocument5 pagesMCS 031 NotesAshikNo ratings yet
- Cs 503 - Design & Analysis of Algorithm: Multiple Choice QuestionsDocument3 pagesCs 503 - Design & Analysis of Algorithm: Multiple Choice QuestionsSheikh ShabirNo ratings yet
- Cs 503 - Design & Analysis of Algorithm: Multiple Choice QuestionsDocument3 pagesCs 503 - Design & Analysis of Algorithm: Multiple Choice QuestionsMyWBUT - Home for Engineers100% (3)
- Cs 503 - Design & Analysis of Algorithm: Multiple Choice QuestionsDocument3 pagesCs 503 - Design & Analysis of Algorithm: Multiple Choice QuestionsHusnain MahmoodNo ratings yet
- Design Amp Analysis of Algorithm Multiple Choice QuestionsDocument3 pagesDesign Amp Analysis of Algorithm Multiple Choice QuestionsemirNo ratings yet
- Design Amp Analysis of Algorithm Multiple Choice QuestionsDocument3 pagesDesign Amp Analysis of Algorithm Multiple Choice QuestionsemirNo ratings yet
- Design Amp Analysis of Algorithm Multiple Choice QuestionsDocument3 pagesDesign Amp Analysis of Algorithm Multiple Choice QuestionsemirNo ratings yet
- Design Amp Analysis of Algorithm Multiple Choice QuestionsDocument3 pagesDesign Amp Analysis of Algorithm Multiple Choice QuestionsemirNo ratings yet
- Cs 503 - Design & Analysis of Algorithm: Multiple Choice QuestionsDocument3 pagesCs 503 - Design & Analysis of Algorithm: Multiple Choice QuestionsAyoade Akintayo MichaelNo ratings yet
- Design Amp Analysis of Algorithm Multiple Choice QuestionsDocument3 pagesDesign Amp Analysis of Algorithm Multiple Choice QuestionsemirNo ratings yet
- Design Analysis AlgorithmDocument36 pagesDesign Analysis AlgorithmAnil Kumar100% (2)
- Robert Bosch Placement Pattern 2 - Freshers ChoiceDocument14 pagesRobert Bosch Placement Pattern 2 - Freshers ChoicefresherschoiceNo ratings yet
- JNTUK M Tech R13 1 1 I Sem March 2014 Computer Aided Manufacturing CAD CAMDocument6 pagesJNTUK M Tech R13 1 1 I Sem March 2014 Computer Aided Manufacturing CAD CAMRameshNo ratings yet
- CoCubes Practice SheetDocument8 pagesCoCubes Practice SheetBabita Kumari100% (2)
- EndsemDocument3 pagesEndsemfirebase appsNo ratings yet
- 5/24/2014 02:05:00 PM Varuna V: BEL Old Question Paper With AnswersDocument15 pages5/24/2014 02:05:00 PM Varuna V: BEL Old Question Paper With AnswersUddipto SenNo ratings yet
- Types of Algorithms Solutions: 1. Which of The Following Algorithms Is NOT A Divide & Conquer Algorithm by Nature?Document8 pagesTypes of Algorithms Solutions: 1. Which of The Following Algorithms Is NOT A Divide & Conquer Algorithm by Nature?ergrehgeNo ratings yet
- 01 DS Quiz SetDocument109 pages01 DS Quiz Setvinay harshaNo ratings yet
- Daa 2022-23Document3 pagesDaa 2022-23Siddhartha SikderNo ratings yet
- q6 DSA - Q10Document6 pagesq6 DSA - Q10Sumanth_YedotiNo ratings yet
- Aac MCQDocument3 pagesAac MCQaryang720No ratings yet
- Future SoftDocument5 pagesFuture Softashokno1985No ratings yet
- BCADocument76 pagesBCAArvinder SinghNo ratings yet
- CSE 565 Midterm Exam 1 Algorithm Design AnalysisDocument14 pagesCSE 565 Midterm Exam 1 Algorithm Design Analysish_liang93No ratings yet
- DAABitsDocument4 pagesDAABitsEesha MusicNo ratings yet
- Computer Science and Engineering - Full Paper - 2010Document17 pagesComputer Science and Engineering - Full Paper - 2010गोपाल शर्माNo ratings yet
- Gate-Cs 2008Document31 pagesGate-Cs 2008tomundaNo ratings yet
- GATE 2013 Question Paper With Answer Key For CSEDocument26 pagesGATE 2013 Question Paper With Answer Key For CSEPremKumarKalikiri0% (1)
- Fundamental of MATLAB: Part: I Introduction To MATLABDocument3 pagesFundamental of MATLAB: Part: I Introduction To MATLABRavi ShekarNo ratings yet
- Robert Bosch Placement Paper 1 - Freshers ChociDocument11 pagesRobert Bosch Placement Paper 1 - Freshers ChocifresherschoiceNo ratings yet
- Daa QBDocument13 pagesDaa QBbabaNo ratings yet
- AllDocument57 pagesAllKhondoker Razzakul HaqueNo ratings yet
- COMPUTER SCIENCE DOCUMENTDocument4 pagesCOMPUTER SCIENCE DOCUMENT20UCS128Debajeet DasNo ratings yet
- Iii Sem - Design Analysis Algorithm PDFDocument36 pagesIii Sem - Design Analysis Algorithm PDFAnil KumarNo ratings yet
- Digital Signal Processing 12Document2 pagesDigital Signal Processing 12Anil RaiNo ratings yet
- Important QuestionsDocument3 pagesImportant QuestionsAshenafi AberaNo ratings yet
- QP UpdatedDocument2 pagesQP Updatedsambhav raghuwanshiNo ratings yet
- Old Quesition Papers (III Sem) Dec-13Document52 pagesOld Quesition Papers (III Sem) Dec-139966197483No ratings yet
- NERIST Digital Signal Processing ExamDocument2 pagesNERIST Digital Signal Processing ExamAkho John RichaNo ratings yet
- TPC Q2Document8 pagesTPC Q2Tanusha handeNo ratings yet
- COL106 Problems PDFDocument10 pagesCOL106 Problems PDFgNo ratings yet
- Questions On Unit 1Document5 pagesQuestions On Unit 1Harish NayakNo ratings yet
- Mathematical and Computational Modeling: With Applications in Natural and Social Sciences, Engineering, and the ArtsFrom EverandMathematical and Computational Modeling: With Applications in Natural and Social Sciences, Engineering, and the ArtsRoderick MelnikNo ratings yet
- Analytical Modeling of Wireless Communication SystemsFrom EverandAnalytical Modeling of Wireless Communication SystemsNo ratings yet
- Probability & Statistics For Scientist and Engineers: Dr. M. M. BhattiDocument25 pagesProbability & Statistics For Scientist and Engineers: Dr. M. M. BhattiMLW BDNo ratings yet
- Laplace Table PDFDocument2 pagesLaplace Table PDFBhanu100% (1)
- Practical's Core: Course Outcome Experiment CL LinkedDocument5 pagesPractical's Core: Course Outcome Experiment CL Linkedmanasa nagarajNo ratings yet
- Lecture 5: Intro to Graphs - Models for NetworksDocument7 pagesLecture 5: Intro to Graphs - Models for NetworkssevroussnapeNo ratings yet
- Trigonometry FormulaDocument6 pagesTrigonometry FormulaHarish kumar100% (1)
- Pigeonhole PrincipleDocument0 pagesPigeonhole PrincipleMarco CollantesNo ratings yet
- Some New Kinds of Connected Domination in Fuzzy GraphsDocument11 pagesSome New Kinds of Connected Domination in Fuzzy GraphsIOSRjournal100% (1)
- Algorithms Notes For ProfessionalsDocument252 pagesAlgorithms Notes For ProfessionalsJin100% (1)
- Planar Graphs and Nonplanar Graphs DefinedDocument29 pagesPlanar Graphs and Nonplanar Graphs DefineddangreglongNo ratings yet
- Euler Paths and Euler Circuits 1Document2 pagesEuler Paths and Euler Circuits 1Fahim Ahmed 19No ratings yet
- Compilation of Random Problems From Various OlympiadsDocument4 pagesCompilation of Random Problems From Various OlympiadsaayamNo ratings yet
- Question Bank 1to11Document19 pagesQuestion Bank 1to11rinkalNo ratings yet
- Chap 11Document12 pagesChap 11Mohamed El-Mutasim El-FeelNo ratings yet
- Integral Calculus FormulaDocument5 pagesIntegral Calculus FormulaJom Agullana100% (1)
- Striver's CP List for Coding RoundsDocument7 pagesStriver's CP List for Coding RoundsVinay Prajapat100% (1)
- Assignment 3: Joseph Sharp Luevano (Sharplue) Tingyu Liang (Liangt19)Document4 pagesAssignment 3: Joseph Sharp Luevano (Sharplue) Tingyu Liang (Liangt19)王乔峪No ratings yet
- YyyyyyyyyDocument47 pagesYyyyyyyyyabi sathwikNo ratings yet
- 5.06 Transformations of Functions - AnswerkeyDocument10 pages5.06 Transformations of Functions - AnswerkeyKimiNo ratings yet
- MCS-033 Solved Assignment 2015-16Document7 pagesMCS-033 Solved Assignment 2015-16Sonakshi DasNo ratings yet
- Shortest Path ProblemDocument10 pagesShortest Path ProblemNaveen AngadiNo ratings yet
- Magnus, W. - Oberhettinger, F. - Formulas & Theorems For The Functions of Mathematical Physics. CheDocument178 pagesMagnus, W. - Oberhettinger, F. - Formulas & Theorems For The Functions of Mathematical Physics. CheMiku Fourier AlvaradoNo ratings yet
- สรุป MidtermDocument15 pagesสรุป Midtermwonning maoNo ratings yet
- CS2040 NoteDocument2 pagesCS2040 NoteChoonKit -No ratings yet
- Admath Properties 1Document6 pagesAdmath Properties 1Missy ForlajeNo ratings yet
- Logarithmic TableDocument168 pagesLogarithmic TablechristopherjudepintoNo ratings yet
- Articulation PointsDocument17 pagesArticulation PointsbinnyjNo ratings yet
- Krishna Raj P.M., Ankith Mohan, Srinivasa K.G. - Practical Social Network Analysis With Python-Springer (2018)Document355 pagesKrishna Raj P.M., Ankith Mohan, Srinivasa K.G. - Practical Social Network Analysis With Python-Springer (2018)matirva456No ratings yet
- GraphDocument84 pagesGraphRiyaz ShresthaNo ratings yet
- AC06 SA DjvuDocument51 pagesAC06 SA DjvuNizid GaleowNo ratings yet
- Calculus and Applications Formula SheetDocument3 pagesCalculus and Applications Formula SheetNathan JacksonNo ratings yet