Professional Documents
Culture Documents
Resource Allocation and Receiver Localization For Underlay CRs Using Interference Tweets
Uploaded by
Editor IJRITCCOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Resource Allocation and Receiver Localization For Underlay CRs Using Interference Tweets
Uploaded by
Editor IJRITCCCopyright:
Available Formats
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 3 Issue: 2
ISSN: 2321 - 8169
803 - 807
_______________________________________________________________________________________________
Resource Allocation and Receiver Localization for Underlay CRs Using
Interference Tweets
Sayali S. Mane.
M.E. Student, Dept. of ENTC Engineering,
D.Y.Patil College of Engg. & Technology, Dist. Kolhapur,
Maharashtra, India
E-mail: sayali_maness@yahoo.com
Prof. Dr. S. V. Sankpal
Professor, Dept. of ENTC Engineering,
D.Y.Patil College of Engg. & Technology, Dist. Kolhapur,
Maharashtra, India
E-mail: sankpal16@yahoo.com
Abstract- Cognitive radio network provides re-utilization of unused portions of the licensed spectrum. Such that primary users do not affect
harmful interference from the transmission of secondary users. Therefore, to analyze the effect of interference across primar y user and their
minimization have become an important criterion in cognitive network. This paper attempts to provide localization technique based on Bayesian
approach gives exact location of primary user. The conventional localization technique provides information related to coverage region of
primary user so we cannot estimate accurate location. Secondary users opportunistically share a fixed spectrum resource with different
probability of interference constraints. The proposed algorithm shows increased network utility with optimize performance of secondary
network.
Keywords- Cognitive radio network; cross layer optimization; receiver localization; interference tweet.
__________________________________________________*****_________________________________________________
I. INTRODUCTION
With the emergence of new wireless applications and
devices, there is excessive demand for radio spectrum. Due to
the scarcity of radio spectrum and the under-utilization of
assigned spectrum, Federal Communications Commission
(FCC) has started to review their spectrum allocation policies
for selection of best available spectrum band. Cognitive radio
systems are radios with the ability to exploit their environment
to increase spectral efficiency and capacity. As spectral
resources are more limited the FCC has recommended that
greater spectral efficiency could be realized by deploying
wireless devices that can coexist with primary users, generating
minimal interference.
The main purpose of localization of primary user (PU)
receiver is to optimize performance of secondary network by
reducing the interference across primary user. Bayesian
approach is based on 1-bit interference tweet. So after resource
allocation if PU is interfered, one can find out its location and
limit the interference to those locations.
The rest of paper is organized as follows. Section II
presents the methodology which involves block diagram of the
system. In section III, CSI model is presented which is to
account for CSI imperfections. A simplified resource allocation
problem is formulated in section IV. Section V shows all
numerical results. Conclusions and future work in section VI
wrap-up this paper.
II.
METHODOLOGY
The proposed system involves following steps as shown in
Fig.1. After resource allocation communication will takes place
in between secondary users. There is receiver map as a tool to
locate a primary user receiver. The location is tracked using
recursive Bayesian approach, which is based interference
tweet. Receiver map as a tool for unveiling areas where PU
receivers are located, with the objective of limiting the
interference inflicted to those locations.
Resource allocation
Interference tweet
Receiver localization
Opportunistic spectrum
access
Fig.1. System Model
III. MODELING
A. State information of primary and secondary channel
Consider a multi-hop secondary user (SU) network with M
{U}M
m =1 deployed in area AR2.Based on the
no. of nodes.
output of the spectrum sensing stage such as maximum
tolerable power, probability of interference across primary user,
average link gain, coverage region etc. SUs implement adaptive
RA, [1] while protecting the PU system from excessive
interference.
When resources are shared in a hierarchical setup, the
available channel state information (CSI) over different SU
network is different. Here, we assume the state of the SU-to-SU
803
IJRITCC | February 2015, Available @ http://www.ijritcc.org
_______________________________________________________________________________________
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 3 Issue: 2
ISSN: 2321 - 8169
803 - 807
_______________________________________________________________________________________________
channels is already known. The instantaneous gain of link
Um Un is denoted as
g m,n
At the medium access layer, let wm , n be the binary
Suppose now that PU transmitters communicate with Q
PU receivers located at {x
(q)
There are some notations are used for further calculation:
A}
Q
q1 .
instantaneous channel gain between
With
U m transmits to its
hm, x(q) is the neighbouring node U , otherwise zero. Assume that one
n
U m and position x (q) .Here
we can obtained average link gain
scheduling variable such that, wm , n =1 for
secondary link is scheduled per time slot, it as follows
based on locations
(m,n)
{x (q) A}Qq1 ,but the instantaneous value of the primary link
cannot perfectly determined due to random fast fading effects.
Where,
wm,n (g,s) 1
{(m, n) : n Nm , m 1,....M}
represents the
assumed that only { hm , x (q) } i.e. the joint distribution of
set of SU-to-SU link [6].
At physical layer, instantaneous rate and transmit
power variables are coupled, and this rate power coupling is
processes is known to the SU network, which is denoted as
modelled. Let average transmit-power of U m is,
Therefore, SU
h ({h m , x }) [2].
(q)
may cause interference to PU q . Next, it is
Let I be the maximum instantaneous
interference power tolerable by the PUs, the secondary network
can determine the interference probabilities at each
location x
(q)
. For instance, if
U m is scheduled to access the
channel with a transmit-power
p , the probability of causing
interference to PU receiver q is Pr {ph m , x(q)
I}.
locations {x (q) A}Qq1
are
Sometime
uncertain. For this, let
p m Eg ,s [ wm,n (g,s) pm,n (g,s)]
..
(1)
nNm
Where Eg , s [.] denotes expectation with respect to random
variable g , s .Powers transmitted by the SUs have to obey two
pm,n
different constraints. First, the instantaneous power
generally
max
cannot exceed a pre-defined limit pm . Second, the average
z X (q) is a binary variable having value 1 power
p m pm max .The
satisfies
binary
variable
if PU receiver q is located at x A . Let G {x g } are grid
i (q) ({p m ,n} , s ) represents interference inflicted to the PU
points representing potential locations for the PU receivers.
system as,
Instead of { z X (q) }, the idea is to use the probabilities
x(q) Pr {z X 1} , x G , to identify areas where a
(q)
PU
i (q) ({pm,n} , s)
xG
wm ,n (g,s)pm ,n (g,s)h
(m,n)
I }
m ,x (q)
z x(q)
.................
receiver q is more likely to reside, and limit the interference
accordingly.
The PU system is protected by setting I = 70 dB and
max
0.05. Let, sets s {h } { x(q) } and g {g m,n } are
Statistical primary state information (PSI) and available
secondary CSI, respectively.
IV. RESOURCE ALLOCATION BASED ON
INTERFERENCE CONSTRAINTS
Where
{x} the
indicator function (
otherwise zero). If i
(q)
{x}
destination is denoted by d (k) . Packet arrivals at U m , for each
flow k , are modelled by a stationary stochastic process with
mean am 0 .
if x is true,
({p m ,n} , s ) 1 then one or more PU
receivers are interfered. Finding the condition for stochastic
resource allocation, let us consider i[t] be the interference
across PU, as [7]
t
i[t] 1/ t i ({p m ,n [ ]},s[ ])
1
Application-level data packets are generated at the SUs, and
routed throughout the network to the intended destination(s).
Packet streams are referred to k .The each flow for the
) =1
(2)
............... (3)
And running average of interference is, i[t] 1/ t
i[ ]
Reported in graph of Fig.3.So as t
A. Optimal adaptive resource allocation
804
IJRITCC | February 2015, Available @ http://www.ijritcc.org
_______________________________________________________________________________________
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 3 Issue: 2
ISSN: 2321 - 8169
803 - 807
_______________________________________________________________________________________________
Some values for have been designed for optimal solution of
resource allocation. Whenever primary user receiver is
interfered, they generate information related to their location.
Some of primary users are more frequently interfered than
others. [9]
Assuming the optimal multipliers {
p m (*m ) arg max
Where
Jm ( pm )
pm
pm
of node
J m ( p m ) *m p m
k*
m }
are,
450 m and cooperate in routing packets to the sink node U12 .
located at x
a ( ) arg max ak ,min a ak ,max V (a) a
m
k
m
k*
m
}, scheduling variable {
and instantaneous transmit power
rmk,*n [t ] {kk
pm* ,n [t ]
wm* , n [t ]
are given as,
*
*
m ,n [ t ] wm ,n [ t ]Cm ,n ( g [ t ], pm ,n [ t ])}
wm* ,n [t ] {( m,n )argmax
= (x = 250, y = 280), static, and it is served by
4
Vmk (amk ) denote non decreasing, utility function with
ak
exogenous rate m .
rmk,*n [t ]
(1)
the PU source during the entire simulation interval t [1,10 ] .
Where
The optimal rates {
V. SIMULATION RESULTS
cyan triangle) communicates with 2 PU receivers (cyan
rhombus) using a power of 3 dB. The first PU receiver is
k*
m
(q)
Pr{i ( q ) [t ] o H t
U m when its average transmit power One data flow is considered, and traffic is generated at
SUs Ns {1, 2,3, 4,7,8} . A PU transmitter (marked with a
The optimal exogenous rates {
k*
m
(q)
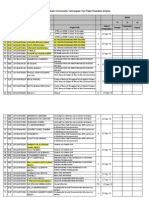
The simulation studies involve the deterministic small
network scenario as shown in the Fig.2. The proposed
technique is implemented with MATLAB. There are 12 SU
transceivers (marked with red circles) are placed over 450 *
U m is,
be a non decreasing function representing
the cost incurred by
is
max
0 p m p m
(q)
BX [t t ]
mk* , m* , * } are available.
*
The optimal average transmit power
(q)
Pr{i ( q ) [t ] o zX( q ) [t ] 1, H t }BX [t t 1]
The second PU is located at x
(2)
= (130, 240) and it is served
3
by the PU source only during the interval [1, 6*10 ] . The PU
system is protected by setting I = 70 dB and i
max
0.05 [8].
Here Rayleigh-distributed small-scale fading is also simulated
[3]. The SU system can estimate the PU source location, and of
its coverage region by sensing phase ([1][3]). Now, the PU
coverage region is then plotted by using equidistant grid points
(marked with black squares in Fig.2).
*
*
( i , j )m ,n ( g [ t ], pm ,n [ t ], d )}
Simulation Scenario
450
pm* ,n [t ] [arg max p m ( g[t ], p, d * )]0
pmmax
PU tx
PU rx
Grid
400
350
(q)
X
B [[t 1]
xGX
(q)
X
(xq, x) [t ]B [[t 1 t 1]
300
[meter]
Algorithm 1: Resource allocation & receiver localization
1. Perform following step [9]
250
8
200
9
2
150
5
1
100
10
12
11
7
50
2. Acquire SU-to-SU channels
3. Obtain optimal exogenous rate, optimal rate, optimal
average transmit power.
*
4. Obtain wm , n [t ] , optimal instantaneous transmit power at
instant t.
5. Update multipliers m , m .
k*
6. Receive interference tweet
7. Update third multiplier
message
8. Perform last step
*,
using the observed tweet
50
100
150
200
250
[meter]
300
350
400
450
Fig.2 Simulated Scenario
Fig.3. shows interference notification across each primary
receiver. Whenever PU is getting interfered due to secondary
user, they broadcast interference announcement message, also
called as tweet. Initially both receivers are interfered. So by
optimizing network parameter such transmit power, rate of data
transmission etc. secondary users can limit interference across
primary users.
805
IJRITCC | February 2015, Available @ http://www.ijritcc.org
_______________________________________________________________________________________
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 3 Issue: 2
ISSN: 2321 - 8169
803 - 807
_______________________________________________________________________________________________
Per-PU interfeence tweet
Per-PU interfeence tweet
400
350
350
350
300
300
300
250
250
250
200
[meter]
400
[meter]
[meter]
Per-PU interfeence tweet
400
200
200
150
150
150
100
100
100
50
50
50
50
100
150
200
[meter]
250
300
350
400
(a) Interference tweet at instant= 100
50
100
150
200
[meter]
250
300
350
400
(b) interference tweet at instant= 1000
50
100
150
200
[meter]
250
300
350
400
(c) interference tweet at instant= 10000
Fig.3. Per-PU interference tweet across each primary receiver
System wide interference notifiaction
System wide interference notifiaction
400
350
350
350
300
300
300
250
250
250
200
[meter]
400
[meter]
[meter]
System wide interference notifiaction
400
200
200
150
150
150
100
100
100
50
50
50
50
100
150
200
[meter]
250
300
350
400
(a) Interference tweet at instant= 100
50
100
150
200
[meter]
250
300
350
400
(b) Interference tweet at instant = 1000
50
100
150
200
[meter]
250
300
350
400
(c) Interference tweet at instant= 10000
Fig.4. System wide interference notification across each primary receiver
Avg interference
Avg exogenous rates
0.1
2
c1:with system-wide tweets
c2:with per-PU tweets
s1-perfect-PSI
0.09
1.6
0.07
1.4
0.06
1.2
a[t] [bps/Hz]
i[t]
0.08
0.05
0.04
1
0.8
0.03
0.6
0.02
0.4
0.01
0.2
1000
2000
3000
4000
5000
t
6000
7000
8000
9000
10000
Fig.5.Average interference rate
with per-PU tweets
perfect-PSI
with system-wide tweets
1.8
1000
2000
3000
4000
5000
t
6000
7000
8000
9000
10000
Fig.6. Average exogenous rate
806
IJRITCC | February 2015, Available @ http://www.ijritcc.org
_______________________________________________________________________________________
International Journal on Recent and Innovation Trends in Computing and Communication
Volume: 3 Issue: 2
ISSN: 2321 - 8169
803 - 807
_______________________________________________________________________________________________
There are number of reasons behind occurrence of
interference across PU. It may due to secondary user
transmission or due to system parameters. Fig.4. shows
Interference at different instant due to system parameters. Both
receivers are initially interfered.
At last our system reduced it to very negligible amount.
Fig.5. gives average amount of interference tweet across each
PU, system wide tweets and perfect PSI. Average exogenous
rates for above three results are shown in Fig.6.
VI. CONCLUSION
Resource allocation and localization of PU for cognitive
network were designed. A Bayesian approach was developed to
estimate the unknown location of the PU receiver. The inputs
to the Bayesian estimator were the power transmitted by the
secondary system and a binary interference notification
broadcasted by primary user system. Proposed System
increases network utility as well as improves the performance
of secondary network.
REFERENCES
[1] E. DallAnese, J. A. Bazerque, and G. B. Giannakis, Group
sparse Lasso for cognitive network sensing robust to model
uncertainties and outliers Elsevier Phy. Commun, vol. 5,
no. 2, pp. 161172, Jun. 2012.
[2] A. Goldsmith, Wireless communications. Cambridge Univ.
Press, 2005.
[3] B. Mark and A. Nasif, Estimation of maximum
interference-free power level for opportunistic spectrum
access IEEE Trans. Wireless Commun., vol. 8, no. 5, pp.
25052513, May 2009.
[4] A. G. Marques, L. M. Lopez-Ramos, G. B. Giannakis, J.
Ramos, and A. Caamano, Resource allocation for
interweave and underlay cognitive radios under probabilityof-interference constraints IEEE Trans. Veh. Technol., vol.
61, no. 6, pp. 2789 2807, Jul. 2012.
[5] A. Ribeiro, Ergodic stochastic optimization algorithms for
wireless communication and networking IEEE Trans. Sig.
Proc., vol. 58, no. 12, pp. 63696386, Dec. 2010.
[6] Srivastava, Pankaj and Rudravarapu, Mohan "Certain
Transformation
Formulae
for
the
Generalized
Hypergeometric Series of Multi Variables", Journal of
Applied Sciences Research, 2011.
[7] Szytula, A., B. Penc, and E. Ressouche. "Magnetic
structures of DyNiSn and TbRhSn", Journal of Alloys and
Compounds, 1996.
[8] Antonio G. Marques, Emiliano DallAnese, and Georgios B.
Giannakis, Cross Layer Optimization and Receiver
Localization for Cognitive Networks Using Interference
Tweets, IEEE Journal on Selected Areas in
Communications, vol. 32, no. 3, pp. 641-653, march 2014.
[9] Antonio G. Marques, Emiliano DallAnese, and Georgios B.
Giannakis, Cross Layer Optimization and Receiver
Localization for Cognitive Networks Using Interference
Tweets, IEEE Journal on Selected Areas in
Communications, vol. 32, no. 3, pp. 641-653, march 2014.
807
IJRITCC | February 2015, Available @ http://www.ijritcc.org
_______________________________________________________________________________________
You might also like
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (119)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (265)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (587)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (890)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Game TheoryDocument85 pagesGame TheoryMuthuKumar RajendranNo ratings yet
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- Image Restoration Techniques Using Fusion To Remove Motion BlurDocument5 pagesImage Restoration Techniques Using Fusion To Remove Motion Blurrahul sharmaNo ratings yet
- Cognitive Dynamic Systems - Simon HaykinDocument320 pagesCognitive Dynamic Systems - Simon Haykinatom tuxNo ratings yet
- Statement of PurposeDocument2 pagesStatement of PurposeMohsin AliNo ratings yet
- A Review of Wearable Antenna For Body Area Network ApplicationDocument4 pagesA Review of Wearable Antenna For Body Area Network ApplicationEditor IJRITCCNo ratings yet
- Channel Estimation Techniques Over MIMO-OFDM SystemDocument4 pagesChannel Estimation Techniques Over MIMO-OFDM SystemEditor IJRITCCNo ratings yet
- A Review of 2D &3D Image Steganography TechniquesDocument5 pagesA Review of 2D &3D Image Steganography TechniquesEditor IJRITCCNo ratings yet
- Regression Based Comparative Study For Continuous BP Measurement Using Pulse Transit TimeDocument7 pagesRegression Based Comparative Study For Continuous BP Measurement Using Pulse Transit TimeEditor IJRITCCNo ratings yet
- Performance Analysis of Image Restoration Techniques at Different NoisesDocument4 pagesPerformance Analysis of Image Restoration Techniques at Different NoisesEditor IJRITCCNo ratings yet
- A Review of Wearable Antenna For Body Area Network ApplicationDocument4 pagesA Review of Wearable Antenna For Body Area Network ApplicationEditor IJRITCCNo ratings yet
- Importance of Similarity Measures in Effective Web Information RetrievalDocument5 pagesImportance of Similarity Measures in Effective Web Information RetrievalEditor IJRITCCNo ratings yet
- Comparative Analysis of Hybrid Algorithms in Information HidingDocument5 pagesComparative Analysis of Hybrid Algorithms in Information HidingEditor IJRITCCNo ratings yet
- Diagnosis and Prognosis of Breast Cancer Using Multi Classification AlgorithmDocument5 pagesDiagnosis and Prognosis of Breast Cancer Using Multi Classification AlgorithmEditor IJRITCCNo ratings yet
- IJRITCC Call For Papers (October 2016 Issue) Citation in Google Scholar Impact Factor 5.837 DOI (CrossRef USA) For Each Paper, IC Value 5.075Document3 pagesIJRITCC Call For Papers (October 2016 Issue) Citation in Google Scholar Impact Factor 5.837 DOI (CrossRef USA) For Each Paper, IC Value 5.075Editor IJRITCCNo ratings yet
- A Review of 2D &3D Image Steganography TechniquesDocument5 pagesA Review of 2D &3D Image Steganography TechniquesEditor IJRITCCNo ratings yet
- Channel Estimation Techniques Over MIMO-OFDM SystemDocument4 pagesChannel Estimation Techniques Over MIMO-OFDM SystemEditor IJRITCCNo ratings yet
- Modeling Heterogeneous Vehicle Routing Problem With Strict Time ScheduleDocument4 pagesModeling Heterogeneous Vehicle Routing Problem With Strict Time ScheduleEditor IJRITCCNo ratings yet
- A Study of Focused Web Crawling TechniquesDocument4 pagesA Study of Focused Web Crawling TechniquesEditor IJRITCCNo ratings yet
- Network Approach Based Hindi Numeral RecognitionDocument4 pagesNetwork Approach Based Hindi Numeral RecognitionEditor IJRITCCNo ratings yet
- Efficient Techniques For Image CompressionDocument4 pagesEfficient Techniques For Image CompressionEditor IJRITCCNo ratings yet
- 41 1530347319 - 30-06-2018 PDFDocument9 pages41 1530347319 - 30-06-2018 PDFrahul sharmaNo ratings yet
- Fuzzy Logic A Soft Computing Approach For E-Learning: A Qualitative ReviewDocument4 pagesFuzzy Logic A Soft Computing Approach For E-Learning: A Qualitative ReviewEditor IJRITCCNo ratings yet
- Itimer: Count On Your TimeDocument4 pagesItimer: Count On Your Timerahul sharmaNo ratings yet
- Predictive Analysis For Diabetes Using Tableau: Dhanamma Jagli Siddhanth KotianDocument3 pagesPredictive Analysis For Diabetes Using Tableau: Dhanamma Jagli Siddhanth Kotianrahul sharmaNo ratings yet
- Prediction of Crop Yield Using LS-SVMDocument3 pagesPrediction of Crop Yield Using LS-SVMEditor IJRITCCNo ratings yet
- Safeguarding Data Privacy by Placing Multi-Level Access RestrictionsDocument3 pagesSafeguarding Data Privacy by Placing Multi-Level Access Restrictionsrahul sharmaNo ratings yet
- A Clustering and Associativity Analysis Based Probabilistic Method For Web Page PredictionDocument5 pagesA Clustering and Associativity Analysis Based Probabilistic Method For Web Page Predictionrahul sharmaNo ratings yet
- 45 1530697786 - 04-07-2018 PDFDocument5 pages45 1530697786 - 04-07-2018 PDFrahul sharmaNo ratings yet
- Hybrid Algorithm For Enhanced Watermark Security With Robust DetectionDocument5 pagesHybrid Algorithm For Enhanced Watermark Security With Robust Detectionrahul sharmaNo ratings yet
- 44 1530697679 - 04-07-2018 PDFDocument3 pages44 1530697679 - 04-07-2018 PDFrahul sharmaNo ratings yet
- Vehicular Ad-Hoc Network, Its Security and Issues: A ReviewDocument4 pagesVehicular Ad-Hoc Network, Its Security and Issues: A Reviewrahul sharmaNo ratings yet
- A Content Based Region Separation and Analysis Approach For Sar Image ClassificationDocument7 pagesA Content Based Region Separation and Analysis Approach For Sar Image Classificationrahul sharmaNo ratings yet
- Space Complexity Analysis of Rsa and Ecc Based Security Algorithms in Cloud DataDocument12 pagesSpace Complexity Analysis of Rsa and Ecc Based Security Algorithms in Cloud Datarahul sharmaNo ratings yet
- Cross-Layer Design in Cognitive RadioDocument6 pagesCross-Layer Design in Cognitive RadioAbhishek Pandey0% (1)
- Energy Efficiency Improvement Through Cognitive Network CooperationDocument7 pagesEnergy Efficiency Improvement Through Cognitive Network Cooperationhamza malikNo ratings yet
- Software Defined Cognitive Radio Using Labview-Ieee FormatDocument6 pagesSoftware Defined Cognitive Radio Using Labview-Ieee FormatRijul ChoudhryNo ratings yet
- ProposalDocument26 pagesProposalVianey VerNo ratings yet
- 5G Course at IITKDocument4 pages5G Course at IITKtejash naikNo ratings yet
- Review Paper Cognitive Radio: Making Software Radios More PersonalDocument2 pagesReview Paper Cognitive Radio: Making Software Radios More PersonalaryagorilNo ratings yet
- Third Year Project PresentationDocument19 pagesThird Year Project PresentationNdagire OliverNo ratings yet
- BMMS 09 CognitiveRadioNetworks Part1Document56 pagesBMMS 09 CognitiveRadioNetworks Part1fsNo ratings yet
- A Review On Green Cellular NetworkDocument8 pagesA Review On Green Cellular NetworkEditor IJTSRDNo ratings yet
- White Spaces PDFDocument8 pagesWhite Spaces PDFSatya SahaNo ratings yet
- Research Article On Cognitive RadioDocument6 pagesResearch Article On Cognitive RadioDino kongkhamNo ratings yet
- Mohammad Abu Shattal Sep2020 PDFDocument8 pagesMohammad Abu Shattal Sep2020 PDFengmas5No ratings yet
- Resource Optimization-Based Network Selection Model For Heterogeneous Wireless NetworksDocument10 pagesResource Optimization-Based Network Selection Model For Heterogeneous Wireless NetworksIAES IJAINo ratings yet
- 2014 - Thesis - Analysis and Design of New Electronically Reconfigurable Periodic Leaky-Wave AntennasDocument242 pages2014 - Thesis - Analysis and Design of New Electronically Reconfigurable Periodic Leaky-Wave Antennasab4azizNo ratings yet
- Simulation and Analysis of Cognitive Radio System Using MatlabDocument16 pagesSimulation and Analysis of Cognitive Radio System Using MatlabOral RobertzNo ratings yet
- CR Unit 1 &11 (Part A &B)Document12 pagesCR Unit 1 &11 (Part A &B)durai muruganNo ratings yet
- Ec8071 Cognitive Radio: Diploma, Anna Univ UG & PG CoursesDocument2 pagesEc8071 Cognitive Radio: Diploma, Anna Univ UG & PG CoursesBALAKRISHNANNo ratings yet
- Aplicacion NanDocument22 pagesAplicacion NanjavierNo ratings yet
- Professional Elective - IDocument10 pagesProfessional Elective - IsridharchandrasekarNo ratings yet
- Book Chapter 6Document26 pagesBook Chapter 6Jihen BennaceurNo ratings yet
- 5G Networks: The Next Gen Evolution: Sandeepika Sharma Brahmjit SinghDocument6 pages5G Networks: The Next Gen Evolution: Sandeepika Sharma Brahmjit SinghFirmansyah KobongsatuNo ratings yet
- Cognitive Radio Networks: An Intelligent Wireless SystemDocument19 pagesCognitive Radio Networks: An Intelligent Wireless SystemSwadhin Kumar MishraNo ratings yet
- Spectrum OFDMFDocument1 pageSpectrum OFDMFvcazacuNo ratings yet
- IJACSA Volume3No10Document209 pagesIJACSA Volume3No10Editor IJACSANo ratings yet
- XMAX TechnologyDocument22 pagesXMAX TechnologyVijay Krishna0% (1)
- Cognitive Radio System Analysis Using MATLABDocument4 pagesCognitive Radio System Analysis Using MATLABKennedy RonohNo ratings yet
- ECE EEE F418 Term Project Presentation ScheduleDocument7 pagesECE EEE F418 Term Project Presentation SchedulesaimanobhiramNo ratings yet