Professional Documents
Culture Documents
Goal and Problem Statements 2.1 Goal
Uploaded by
kirrukachikOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Goal and Problem Statements 2.1 Goal
Uploaded by
kirrukachikCopyright:
Available Formats
1.
GOAL AND PROBLEM STATEMENTS
2.1 GOAL STATEMENT
The extreme goal of this work is How to effectively select the best security scheme
for stored data under different environments? Due to large number of potential
solutions available, it is not easy for a prospective customer to identify the best
suitable approach for his/her multimedia requirements. This paper gives an
overview of the prominent characteristics of several systems to provide a
foundation for selecting the most appropriate solution.
2.2 PROBLEM STATEMENT
For protecting Multimedia Data in Storage, Many potential schemes are developed
for ensuring information confidentiality, integrity, and availability without
substantially degrading performance. In order to choose the best security scheme,
users must have proper knowledge about of the primary security features available
in the storage security community and then be able to quantifiably compare the
systems. So, How to classify various storage schemes and to compare their
performance? In attacking this problem, we are confronted with the following
challenges that should be addressed.
• How to properly weigh the costs and benefits associated with these security
measures?
• How to compare the methods based on confidentiality, integrity, availability
and performance?
• What are the major differences between all the methods?
• What are the Specific applications of storage devices in the multimedia
environment?
1. BACK GROUND AND RELATED WORK
This section briefly explains about common set of criteria for evaluating a storage
security system i.e. confidentiality, integrity, availability, and performance.
Confidentiality
Ensuring confidentiality means that no one has access to data unless
specifically authorized. The first step in authorizing access to information is to
properly identify users via authentication. The storage system must define the
means for a user to be properly identified prior to gaining access, and then having
appropriately identified a user, the system must allow access to only specified data
associated with that user. The system must encrypt data and, therefore, requires
either users or servers to apply cryptographic keys. Determining how the keys are
managed has had a significant impact on the overall design. And also once the
system determines to revoke a particular user’s access, the user’s keys must no
longer work within the system, or at a minimum not allow access to future versions
of the files.
You might also like
- CISA Exam-Testing Concept-Knowledge of Logical Access ControlFrom EverandCISA Exam-Testing Concept-Knowledge of Logical Access ControlRating: 2.5 out of 5 stars2.5/5 (3)
- Security and Usability p4 Daniel DuncanDocument9 pagesSecurity and Usability p4 Daniel DuncanDrake JuneNo ratings yet
- Security Challenges of DS?: 2.what Do You Mean by Scalability of A System?Document10 pagesSecurity Challenges of DS?: 2.what Do You Mean by Scalability of A System?SirishaNo ratings yet
- Distributed Systems Security ManagementDocument44 pagesDistributed Systems Security ManagementwirdinaNo ratings yet
- Data Sharing in Cloud Storage Using Key Aggregate: 2.1 Existing SystemDocument44 pagesData Sharing in Cloud Storage Using Key Aggregate: 2.1 Existing SystemUday SolNo ratings yet
- Potential Covert Channel in Distributed DatabaseDocument9 pagesPotential Covert Channel in Distributed DatabaseseventhsensegroupNo ratings yet
- Safeguarding Data Privacy by Placing Multi-Level Access RestrictionsDocument3 pagesSafeguarding Data Privacy by Placing Multi-Level Access Restrictionsrahul sharmaNo ratings yet
- Chapter 7Document10 pagesChapter 7minichelagumas143No ratings yet
- CPPPMUSABDocument75 pagesCPPPMUSABMusabNo ratings yet
- Network Security Chapter 1Document34 pagesNetwork Security Chapter 1NasRul Nasrullah0% (1)
- Final Report ChaptersDocument56 pagesFinal Report ChaptersJai Deep PonnamNo ratings yet
- Operating Systems Security ConsiderationsDocument7 pagesOperating Systems Security ConsiderationsSachin MehrolNo ratings yet
- CCSDocument111 pagesCCSSoe YazarNo ratings yet
- Ijret - Enhanced Security Framework To Ensure Data Security in Cloud Using Security Blanket AlgorithmDocument5 pagesIjret - Enhanced Security Framework To Ensure Data Security in Cloud Using Security Blanket AlgorithmInternational Journal of Research in Engineering and TechnologyNo ratings yet
- Information Assurance and Security (IAS)Document27 pagesInformation Assurance and Security (IAS)mohed ahmedNo ratings yet
- Info Assurance and Security2Document8 pagesInfo Assurance and Security2Navier ClementineNo ratings yet
- A Cryptographically Enforced Access Control With ADocument13 pagesA Cryptographically Enforced Access Control With AHyma PaladugulaNo ratings yet
- Report 4Document24 pagesReport 4mahalaxmi2012No ratings yet
- Database Security and Integrity Group 3Document52 pagesDatabase Security and Integrity Group 3Jm McCallNo ratings yet
- Unit 5Document33 pagesUnit 5chalie tarekegnNo ratings yet
- ENSURING ACCOUNTABILITY IN THE CLOUDDocument10 pagesENSURING ACCOUNTABILITY IN THE CLOUDShekhar ImvuNo ratings yet
- CIPT Onl Mod5Transcript PDFDocument9 pagesCIPT Onl Mod5Transcript PDFChrist SierraNo ratings yet
- ISYS6508 Database System: Week 10 Security and AdministrationDocument54 pagesISYS6508 Database System: Week 10 Security and AdministrationCaesar MontanaNo ratings yet
- Database SecurityDocument26 pagesDatabase SecurityFelipe OliverosNo ratings yet
- S2 Module 2: System ImplementationDocument10 pagesS2 Module 2: System Implementationer_sushilkumargNo ratings yet
- System AnalysisDocument2 pagesSystem Analysisholylike88No ratings yet
- Final Report 3Document44 pagesFinal Report 3Barath Kumar DhanushNo ratings yet
- SYAD Prefinal Exams FINALDocument5 pagesSYAD Prefinal Exams FINALBien Joshua Martinez PamintuanNo ratings yet
- Security Management in Distributed SystemsDocument55 pagesSecurity Management in Distributed Systemsdaily careNo ratings yet
- DDBSDocument19 pagesDDBSBudhaditya MukherjeeNo ratings yet
- Computer Base Information ControlDocument39 pagesComputer Base Information ControlAura MaghfiraNo ratings yet
- Week6 ClassActivity ArchiPerspectiveDocument2 pagesWeek6 ClassActivity ArchiPerspectiveمحمد احمدNo ratings yet
- Lab #4 - Assessment Worksheet Craft A Layered Security Management Policy - Separation of Duties ABC Credit Union Policy Name+ Policy StatementDocument4 pagesLab #4 - Assessment Worksheet Craft A Layered Security Management Policy - Separation of Duties ABC Credit Union Policy Name+ Policy StatementVo Minh Khanh (K14 HCM)No ratings yet
- CPDS Cortez Activity 4Document5 pagesCPDS Cortez Activity 4Emelex CortezNo ratings yet
- Cloud Computing: Security ChallengesDocument31 pagesCloud Computing: Security ChallengesChristos GeorgiadisNo ratings yet
- Day 3 Session 1: Secure Software RequirementsDocument32 pagesDay 3 Session 1: Secure Software RequirementsmrzNo ratings yet
- Unit - 4 - CCDocument66 pagesUnit - 4 - CCg.lakshmirohana13No ratings yet
- Architecture Des Not Esp 2Document13 pagesArchitecture Des Not Esp 2Nourisher MugeroNo ratings yet
- Unit 7 Data Security and Management: StructureDocument15 pagesUnit 7 Data Security and Management: StructurevidvaNo ratings yet
- Isel532 - Chapter OneDocument34 pagesIsel532 - Chapter OneZcel TablizoNo ratings yet
- Security Engineering PhasesDocument20 pagesSecurity Engineering PhasescajaroNo ratings yet
- Unit 3 Network Security and Traffic MGMT 4Document7 pagesUnit 3 Network Security and Traffic MGMT 4earl bagainNo ratings yet
- Info Assurance Security 2 Prelim FinalsDocument15 pagesInfo Assurance Security 2 Prelim FinalsLeary John TambagahanNo ratings yet
- Project Documentation-3Document46 pagesProject Documentation-3Gayathiri PNo ratings yet
- Mir-011 Unit-7Document34 pagesMir-011 Unit-7vidvaNo ratings yet
- 1.1 Methods of DefenseDocument4 pages1.1 Methods of DefenseRAJ TAPASENo ratings yet
- Computer Security Concepts (Inglés) (Artículo) Autor Zainab Abdullah JasimDocument7 pagesComputer Security Concepts (Inglés) (Artículo) Autor Zainab Abdullah JasimJavier David Afanador GüizaNo ratings yet
- Security and Usability Analysis ProcessDocument8 pagesSecurity and Usability Analysis ProcessMarceloDutraNo ratings yet
- Bai9-Vol45-2 - Nhom 5Document19 pagesBai9-Vol45-2 - Nhom 5Tran Lenh AnhNo ratings yet
- Cloud Data Protection Guidance - V1 DraftDocument21 pagesCloud Data Protection Guidance - V1 DraftCloudSANYNo ratings yet
- Security: A Need For Cloud Computing: - H.Kunaa L Khilnani (B.TECH IT) - S.Dhyan Eshwaran (B.E ECE)Document15 pagesSecurity: A Need For Cloud Computing: - H.Kunaa L Khilnani (B.TECH IT) - S.Dhyan Eshwaran (B.E ECE)Mukuntha VasNo ratings yet
- Web Application Security Standard PDFDocument5 pagesWeb Application Security Standard PDFyshprasdNo ratings yet
- 18BCS42C U5Document22 pages18BCS42C U5kskscks1610No ratings yet
- System Requirement SpecificationDocument38 pagesSystem Requirement SpecificationBala SudhakarNo ratings yet
- 3DS Information Security Overview ExternalDocument15 pages3DS Information Security Overview ExternalRaut AbhimanNo ratings yet
- Activity TemplateDocument3 pagesActivity Templatemunoz.136577090096No ratings yet
- Decentralized Access Control Based Crime Analysis-Survey: A A A A A B CDocument3 pagesDecentralized Access Control Based Crime Analysis-Survey: A A A A A B CeditorinchiefijcsNo ratings yet
- Telephone Billing SystemDocument43 pagesTelephone Billing Systemsouravroyonline79% (29)
- 03 SecurityDocument18 pages03 SecurityBody SallamNo ratings yet
- Design Class DiagramsDocument3 pagesDesign Class DiagramskirrukachikNo ratings yet
- SiRiUS - Securing Remote Untrusted StorageDocument2 pagesSiRiUS - Securing Remote Untrusted StoragekirrukachikNo ratings yet
- Goal and Problem Statements 2.1 GoalDocument2 pagesGoal and Problem Statements 2.1 GoalkirrukachikNo ratings yet
- Goal and Problem Statements 2.1 GoalDocument2 pagesGoal and Problem Statements 2.1 GoalkirrukachikNo ratings yet
- Integrity Refers To Maintaining Data Consistency inDocument2 pagesIntegrity Refers To Maintaining Data Consistency inkirrukachikNo ratings yet
- Protecting Multimedia Data in Storage: A SurveyDocument8 pagesProtecting Multimedia Data in Storage: A SurveykirrukachikNo ratings yet
- Goal and Problem Statements 2.1 GoalDocument2 pagesGoal and Problem Statements 2.1 GoalkirrukachikNo ratings yet
- Protecting Multimedia Data in Storage A SurveyDocument2 pagesProtecting Multimedia Data in Storage A SurveykirrukachikNo ratings yet
- 2005 Spies Tan Ton SurveyDocument12 pages2005 Spies Tan Ton SurveykirrukachikNo ratings yet
- Submit Submit: Error HandlerDocument1 pageSubmit Submit: Error HandlerkirrukachikNo ratings yet
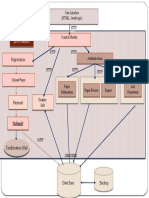
- Architecture For The Conference Management PortalDocument24 pagesArchitecture For The Conference Management PortalkirrukachikNo ratings yet
- Submit Submit: Error HandlerDocument1 pageSubmit Submit: Error HandlerkirrukachikNo ratings yet
- Software Architecture For Conference Management PortalDocument22 pagesSoftware Architecture For Conference Management PortalkirrukachikNo ratings yet
- RFC 791: Internet Protocol Specification Defines IP Addressing and FragmentationDocument52 pagesRFC 791: Internet Protocol Specification Defines IP Addressing and FragmentationMaskur IrwansyahNo ratings yet