Professional Documents
Culture Documents
RMCT Assignment
Uploaded by
Lim Keng LiangCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
RMCT Assignment
Uploaded by
Lim Keng LiangCopyright:
Available Formats
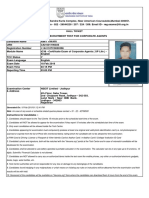
Research Methods for Computing and Technology
INDIVIDUAL ASSIGNMENT
Lecturer
: Dr. Imran Medi
Student Name
: Lim Keng Liang (TP028092)
Module Code
: CT098-3.5-2-RMCT
Module Title
: Research Methods for Computing and
Technology
Assignment Title
: NFC Login Application for Mobile Devices
Intake
: UC2F1404SE
CT098-3.5-2-RMCT
Page 1
Research Methods for Computing and Technology
Contents
1.0 Title...................................................................................................................... 3
2.0 Introduction.......................................................................................................... 3
3.0 Problem Statement............................................................................................... 3
4.0 Research Aims & Objectives.................................................................................6
4.1 Aims.................................................................................................................. 6
4.2 Objectives......................................................................................................... 6
5.0 Research Questions.............................................................................................. 7
5.1 Domain Research.............................................................................................. 7
5.2 Technical Research............................................................................................ 7
6.0 Research Design................................................................................................... 8
6.1 Primary Data Collection..................................................................................... 8
6.2 Secondary Data Collection................................................................................9
6.3 Timeline........................................................................................................... 10
7.0
Personal Reflection.......................................................................................... 11
8.0 References and Bibliography.............................................................................. 12
CT098-3.5-2-RMCT
Page 2
Research Methods for Computing and Technology
1.0 Title
NFC Login Application for Mobile Devices
2.0 Introduction
In this era of technology, it is safe to say that every household and office has a desktop or
personal computer, whether for work or entertainment purposes. A developing country is no
exception of having such devices, which includes cities that are growing tremendously every
year. A household computer has multiple functions, depending on the necessities of the user. A
computer is usually unique to either one or a limited set of owners, meaning only a few select
people can access his/her computer at a given time. Thus, a security system is usually
implemented in each personal computer to ensure safeguard of information and privacy is kept to
a maximum.
3.0 Problem Statement
There are many ways one can secure a personal computer; the most common ones include
manual keyboard input for password. The advanced methods include thumb print scanning,
facial recognition and near-field communication (NFC) using a piece of chip or card
implemented with one. Each ways has its pros and cons; as such a proposed solution is to create
a program that uses near-field communication to login onto a personal computer using a users
personal cellphone with NFC functions.
A study from Ponemon Institute shed some light on the subject on the current state of password
usage among 1900 people, spread across countries such as United States, United Kingdom and
Germany. It turns out that nearly 50% of the people conducting the survey failed to present their
CT098-3.5-2-RMCT
Page 3
Research Methods for Computing and Technology
passwords to execute an online transaction, resulting in authentication failure (Kerner, 2015).
Furthermore, a strong 46% of the respondents stressed that they do not trust websites that rely
only on passwords as a form of login authentication, as said by author Larry Ponemon. As per
quote from Larry Ponemon himself, We think thats a sign that users are using websites without
necessarily trusting them. As some websites require alphanumeric passwords; making them
more complex, it is also common that a user might forget his/her password because of
complexity. Ponemon also said that 69% of the respondents admitted that they have forgotten
their passwords as it was either too long or too complex to remember. Losing passwords can also
lead to one being frustrated and also said to be more annoying than misplacing keys, a mobile
phone battery depleting or getting junk email (Curtis,2014).
In the case of a forgotten password, usually computers or websites offer a password reset system,
but consumers were apparently too lazy or find the process inconvenient, as 54% said it took
too long to reset a password that they basically gave up, (Kerner,2015). If it were to be viewed
from a business perspective, a company might lose a lot of customers due to lack of patience and
customers opting to buy from somewhere else instead. Based on the abovementioned points, it is
safe to say that passwords are virtually the weak link in security as they only have that much to
offer but with too much downside. Lunabee, an innovator of mobile and desktop applications has
also announced results from an online survey, circulating among 100 end users and their insights
on mobile banking and mobile security. According to Olivier Berni, managing director of
Lunabee, about 58% of people who have undergone the survey admitted to forgetting their
passwords frequently and must use system resets on websites to gain access to their accounts.
Only a mere 10% of people said they never forget their passwords, and a staggering number of
52% of people said that they write their passwords down so that they dont lose track of it
(Marketwire, 2015). It has become very clear that passwords are no longer a secure way of
accessing sensitive material online or offline, as per mentioned that they are in many ways
susceptible to many forms of breaching or loss of data.
Keyloggers are a prime example as to why manual input passwords are no longer secure in this
tech-savvy generation. A keylogger is a piece of malicious software that can be installed onto any
personal computer without the users knowledge when they visit a website, read spam email or
installing a program. It is a spyware or malware that records keystrokes a user makes on a
CT098-3.5-2-RMCT
Page 4
Research Methods for Computing and Technology
keyboard (Waller, 2014) Once the keylogger is deployed, it simply lies in wait by collecting
information and transmitting them back to the origin, in this case the hacker. Keyloggers are
easily obtained as they are also legitimate keyloggers used in offices and big companies to keep
track of their workers as to what they are doing at their desk. With that, data can be easily stolen
without consent (Grebennikov,2007) Imagine this happening to a larger scale, where government
secrets can be hacked and leaked onto the internet, marketing strategies of rival companies can
be exploited and most importantly, classified and/or personal information; whether used for
blackmailing or for fun it is unlawful and irresponsible of the hacker.
Hence, a safer and more secure way to access personal information is introduced, known as nearfield communication or NFC in short. A short ranged radio technology that can be triggered by
two NFC-compatible devices; it is more secure and safe because of its transmission range of
around 4 centimeters, hence inherently more secure for transactions (Oracle.com, 2015). It has
little to no set up time, easy to use, fast, and efficient. It allows flow of information between
devices as long as they are within the set distance mentioned above. It is often used in keycards
and other cards with an embedded microchip, such as credit cards. NFC is also available on most
mobile phones, namely the ones that run on an Android operating system, where it can be used to
transfer data from phone to phone with a simple tap on the screen. As such, a system is proposed
to combine both the secure ways of using NFC as a login system and replacing it with the
traditional manual keystrokes on a computer. In this system, a NFC supported mobile phone
doubles as an access card to a personal computer, making it secure and hassle-free, with the users
not needing to memorize passwords and saves time. It is easy to use, as a user is not required to
carry multiple keycards for different functions as it can all be embedded into the mobile phone.
Now this may sound risky at first, but if the phone is password protected or requires a biometric
scan to access (thumbprint scanning is on the new iPhone 6, sooner or later every other
smartphone is assumed to catch up to this technology). Even a simple pattern recognition which
is available in most phones is enough to deter any thief from accessing your credentials on your
phone. Moreover, a GPS enabled smartphone can be recovered and tracked down easily, whereas
lost passwords cannot be traced back if a user loses total access to an account. It also saves space
in your wallet if one is to juggle credit cards and access cards, which can be quite a handful for
the working class (Nearfieldcommunication.org, 2015). NFC is also versatile and can double up
CT098-3.5-2-RMCT
Page 5
Research Methods for Computing and Technology
as many other functions are available and open to NFC, such as paying bills, boarding subways
and many more (Nearfieldcommunicationnfc.net, 2015).
4.0 Research Aims & Objectives
4.1 Aims
The aim of this application is to implement a safe login system with the NFC feature, creating a
secure login mechanism that not only promotes information security but also is simple and user
friendly in order to help reshape computer security.
4.2 Objectives
- To implement a hassle free login system, where users only require an Android Device to access
their personal computer.
- To provide optimal security and safeguard data from unauthorized users
- To be fast and efficient in a professional working environment
CT098-3.5-2-RMCT
Page 6
Research Methods for Computing and Technology
5.0 Research Questions
5.1 Domain Research
1.
2.
3.
4.
5.
6.
7.
Who are the target users for this application?
Is it user friendly?
Is it easy to implement?
Are there any benefits of using this application?
How often do users require login information?
Is NFC widely agreed upon as a better alternative?
Is NFC a safer alternative?
5.2 Technical Research
1.
2.
3.
4.
5.
6.
7.
What are the special features of this application?
How is the application helping a users security status?
What are the components needed to build a NFC tag?
How is the application going to transfer information across the hardware?
Is data sent from the application retrievable?
Is there any setup required before using this application?
What type of methodology is to be implemented when developing this application?
CT098-3.5-2-RMCT
Page 7
Research Methods for Computing and Technology
6.0 Research Design
In the research design phase, it is mainly categorized into two main steps, which are primary data
collection and secondary data collection. Primary data collection is the initial data collection,
where the researcher gets to collect data first handedly from the source/subject under question.
Secondary data collection is taken from primary data collection, mainly used for analyzing
primary data.
6.1 Primary Data Collection
a) Interview Method
Interviews are a common research tool often used in one on one data collection method, where
an interviewer (researcher) asks a set of questions directed towards the interviewee (subject). An
interview may vary depending on the type of questions asked, duration of the interview, number
of subjects and amount of data generated and collected. Using this technique, a researcher is able
to gather information on what is on an interviewees mind when it comes to the topic of question
(in this case, NFC Secure Login System). The researcher is able to gather ideas and suggestions
to which can help build and improve the application. In this case, interviews will be gathered
from students at Asia Pacific University and also lecturers teaching Software Engineering. Basic
knowledge for what is to be done is required, thus the need to interview seasoned and
professional lecturers is crucial to make this project a success.
b) Questionnaires
Questionnaires consist of a set of questions which can be given to a group of select respondents
in order to collect specific information. The questions should be concise and easily understood
CT098-3.5-2-RMCT
Page 8
Research Methods for Computing and Technology
by the respondents. Using this technique, a researcher is able to gather information on what
people think of the software and what are the ways to improve it (NFC Secure Login System).
Any feedback and suggestions can be viewed and maybe implemented if it has solid reasoning
and may prove useful for the sustainability of the system. Questionnaires can be given out to
random students or staff members in Asia Pacific University or even individuals outside the
university.
6.2 Secondary Data Collection
a) Case study
Using the case study method, researchers can gather data from related or existing case studies.
This includes journals, conference studies or books in general. This method is useful because it
gives technical knowledge on the research. Hence, the research can be prepared better and any
problems that might occur can be foresighted and dealt with in the early stages of development.
6.3 Timeline
CT098-3.5-2-RMCT
Page 9
Research Methods for Computing and Technology
7.1
Personal Reflection
CT098-3.5-2-RMCT
Page 10
Research Methods for Computing and Technology
Upon completion of the proposal, there are a few limitations that come to mind
of the researcher. The first limitation being that the researcher has no
background knowledge on how NFC works. There will be a lot of research to do if
the researcher is to proceed with the current topic.
Secondly, the topic of choice is more to mobile computing instead of software
engineering. Even though it requires a computer to operate the program, the
mobile programming part is much more crucial in the development of the
system. The researcher should take into careful consideration the accuracy of
the topic.
Finally, the researcher has to have very good knowledge on the topics of mobile
programming language as well as computer programming languages. In the
mobile programming language factor, he/she will face some difficulties as it is
not his scope of study. Thus, plenty of self-study and research is required if the
researcher is to progress with this topic.
CT098-3.5-2-RMCT
Page 11
Research Methods for Computing and Technology
8.0 References and Bibliography
References
Carter, J. and Faulker, C. (2014). What is NFC and why is it in your phone?. [online] TechRadar.
Available at: http://www.techradar.com/news/phone-and-communications/what-is-nfc-andwhy-is-it-in-your-phone-948410 [Accessed 11 Dec. 2014].
Grebennikov, N. (2007). Keyloggers: How they work and how to detect them (Part 1). [online]
Securelist - English - Global - securelist.com. Available at:
https://securelist.com/analysis/36138/keyloggers-how-they-work-and-how-to-detect-thempart-1/ [Accessed 11 Dec. 2014].
Howley, D. (2014). What Is NFC, and Why Does It Matter for the iPhone 6?. [online]
Yahoo.com. Available at: https://www.yahoo.com/tech/what-is-nfc-and-why-does-it-matterfor-the-iphone-6-96456683964.html [Accessed 11 Dec. 2014].
Waller, G. (2014). Keyloggers: The Most Dangerous Security Risk in Your Enterprise -Enterprise Systems. [online] Esj.com. Available at:
http://esj.com/articles/2012/11/12/keylogger-security-risk.aspx [Accessed 11 Dec. 2014].
Esecurityplanet.com, (2015). Passwords Are Weak Link in Security - eSecurity Planet. [online]
Available at: http://www.esecurityplanet.com/network-security/passwords-are-weak-link-insecurity.html [Accessed 31 Jan. 2015].
Internetnews.com, (2015). How Often Do You Forget Your Password? - InternetNews.. [online]
Available at: http://www.internetnews.com/security/how-often-do-you-forget-yourpassword.html [Accessed 31 Jan. 2015].
Marketwire, (2015). Lunabee Survey Finds that 17 Percent of Internet Users Often Forget Their
Online Passwords, Creating Mandatory Password Reset. [online] Available at:
http://www.marketwired.com/press-release/lunabee-survey-finds-that-17-percent-internetusers-often-forget-their-online-passwords-1850682.htm [Accessed 31 Jan. 2015].
Nearfieldcommunication.org, (2015). Benefits of NFC for Individuals
NearFieldCommunication.org. [online] Available at:
CT098-3.5-2-RMCT
Page 12
Research Methods for Computing and Technology
http://www.nearfieldcommunication.org/benefits.html [Accessed 31 Jan. 2015].
Nearfieldcommunicationnfc.net, (2015). Benefits of Near Field Communication NEARFIELDCOMMUNICATIONNFC.NET. [online] Available at:
http://www.nearfieldcommunicationnfc.net/benefits.html [Accessed 31 Jan. 2015].
Rapidnfc.com, (2015). What is NFC ?. [online] Available at: http://rapidnfc.com/what_is_nfc
[Accessed 31 Jan. 2015].
Rapidnfc.com, (2015). What is NFC ?. [online] Available at: http://rapidnfc.com/what_is_nfc
[Accessed 31 Jan. 2015].
CT098-3.5-2-RMCT
Page 13
You might also like
- RMCT 2016Document15 pagesRMCT 2016Ah YongNo ratings yet
- Research Methods For Computing and Technology (RMCT) - AssigmentDocument17 pagesResearch Methods For Computing and Technology (RMCT) - AssigmentRaoufNo ratings yet
- CRI AssignmentDocument38 pagesCRI AssignmentroshanNo ratings yet
- SDM AssignmentDocument36 pagesSDM AssignmentVidur Sharma100% (2)
- RMCT DocumentationDocument16 pagesRMCT DocumentationVincentMingShenLeeNo ratings yet
- CT050!3!2 WAPP AssignmentDocument33 pagesCT050!3!2 WAPP AssignmentNiraj ThapaNo ratings yet
- RMCT AssignmentDocument12 pagesRMCT AssignmentPyo Wai Lian HK0% (2)
- Integrated Smart Phone Apps for Shopping Mall ParkingDocument18 pagesIntegrated Smart Phone Apps for Shopping Mall ParkingYeong DeeNo ratings yet
- Integrated Smartphone Apps to Solve Shopping Mall Parking IssuesDocument18 pagesIntegrated Smartphone Apps to Solve Shopping Mall Parking IssuesLeongFonNo ratings yet
- CRI AssignmentDocument19 pagesCRI AssignmentLim Keng LiangNo ratings yet
- CRIDocument43 pagesCRIFaisal Ali0% (1)
- Ct050-3-2-Wapp (NP000149, NP000150, NP000151)Document36 pagesCt050-3-2-Wapp (NP000149, NP000150, NP000151)Rupak ThapaNo ratings yet
- DCI GroupDocument23 pagesDCI GroupRupak ThapaNo ratings yet
- Apu RMCTDocument10 pagesApu RMCTAiman Bin IdrisNo ratings yet
- CRI-Assignment 2 SimpleDocument19 pagesCRI-Assignment 2 SimpleMohammed HakimNo ratings yet
- Object Oriented Development With Java Documentation JJDocument51 pagesObject Oriented Development With Java Documentation JJJing Jie Leim0% (1)
- Dci AnjanaDocument27 pagesDci AnjanaRupak ThapaNo ratings yet
- NP000194-NP000200-NP000203 - (Ct026-3-2-Hci)Document62 pagesNP000194-NP000200-NP000203 - (Ct026-3-2-Hci)Rupak ThapaNo ratings yet
- NP000194 - NP000200 - NP000203 - (Ct050-3-2-Wapp)Document45 pagesNP000194 - NP000200 - NP000203 - (Ct050-3-2-Wapp)Rupak ThapaNo ratings yet
- CRI Assignment UCF1505 IT SEDocument2 pagesCRI Assignment UCF1505 IT SEElaine LaLa0% (1)
- Creativity and Innovation BM006-3-2-CRI Individual AssignmentDocument24 pagesCreativity and Innovation BM006-3-2-CRI Individual AssignmentDinikaNo ratings yet
- RMCT AssignmentDocument10 pagesRMCT AssignmentDynamite For sure100% (1)
- SDM AssignmentDocument24 pagesSDM AssignmentJoshua Jebaraj JosephNo ratings yet
- Final Cri AssignmentDocument38 pagesFinal Cri AssignmentZaed Derehem100% (1)
- CRI AssignmentDocument23 pagesCRI AssignmentIrufan Ibrahim67% (3)
- Cri AssignmentDocument23 pagesCri AssignmentNyx JawadNo ratings yet
- Research Methods For Computing and Technology: Individual Assignment CT098-3-2-RMCTDocument21 pagesResearch Methods For Computing and Technology: Individual Assignment CT098-3-2-RMCTRupak ThapaNo ratings yet
- SDM AssignmentDocument4 pagesSDM AssignmentElaine LaLaNo ratings yet
- Individual Assignment: Name Tp-Number Melikov Savlatjon Sobirovich TP058455Document9 pagesIndividual Assignment: Name Tp-Number Melikov Savlatjon Sobirovich TP058455savlatNo ratings yet
- Research Methodology in Computing and Technology (RMCT) Assignment: Project ProposalDocument10 pagesResearch Methodology in Computing and Technology (RMCT) Assignment: Project Proposalgrek0% (1)
- CRI Documentation APUDocument21 pagesCRI Documentation APURaabiahMukadamNo ratings yet
- CRI AssignmentDocument31 pagesCRI AssignmentHam Dan PrinceNo ratings yet
- Manage After-School Care RequirementsDocument61 pagesManage After-School Care RequirementsThendral SriNo ratings yet
- Computing and Concurrent System Design (Java Threads)Document56 pagesComputing and Concurrent System Design (Java Threads)Isuri_PabasaraNo ratings yet
- OODJ AssignmentDocument6 pagesOODJ AssignmentSagaaboyz Mg R0% (1)
- CRI G6 AssignmentDocument103 pagesCRI G6 AssignmentDynamite For sureNo ratings yet
- DSTR AssignmentDocument5 pagesDSTR AssignmentmamadNo ratings yet
- APU Staffordshire Final Year Project (FYP) Plagiarism NoticeDocument78 pagesAPU Staffordshire Final Year Project (FYP) Plagiarism NoticePouya Vedadiyan0% (1)
- Research Methodology in Computing & Technology: - Using Artificial Intelligence To Detect Security ThreatsDocument8 pagesResearch Methodology in Computing & Technology: - Using Artificial Intelligence To Detect Security ThreatsVïvïan Xuan100% (1)
- Research Methodology in Computing and Technology (RMCT) Assignment: Project PaperDocument11 pagesResearch Methodology in Computing and Technology (RMCT) Assignment: Project PaperSyed Ghazi Abbas RizviNo ratings yet
- SDM Final AssignmentDocument47 pagesSDM Final AssignmentAbdullah Ali100% (4)
- CRI Assignment Apiit UctiDocument41 pagesCRI Assignment Apiit UctiMan Zai100% (5)
- APU Fyp Final LatestDocument119 pagesAPU Fyp Final LatestJaga Ravi100% (2)
- Hciau IndividualDocument13 pagesHciau IndividualParveen NarayananNo ratings yet
- DDAC AssignmentDocument26 pagesDDAC AssignmentHoo Johnny33% (3)
- MWT AssignmentDocument15 pagesMWT AssignmentJoshua RyanNo ratings yet
- Individual Assignment Object-Oriented Development with JavaDocument16 pagesIndividual Assignment Object-Oriented Development with JavaLim Keng Liang100% (1)
- MWT AssignmentDocument3 pagesMWT AssignmentRaabiahMukadamNo ratings yet
- ADVBS Group Assignment DocumentationDocument58 pagesADVBS Group Assignment DocumentationAlexander Ho67% (3)
- BCD Assignment UC3F2007CS-Part2Document43 pagesBCD Assignment UC3F2007CS-Part2Sasvinaa KandasamyNo ratings yet
- Designing a Cloud-Based Carnival Cruises Booking ApplicationDocument43 pagesDesigning a Cloud-Based Carnival Cruises Booking ApplicationMunawwar MohamedNo ratings yet
- #Shuaib RMCT AssignmentDocument9 pages#Shuaib RMCT Assignments_dark155No ratings yet
- Ijet V4i3p48 PDFDocument8 pagesIjet V4i3p48 PDFInternational Journal of Engineering and TechniquesNo ratings yet
- OTP Based 2F AuthenticationDocument16 pagesOTP Based 2F AuthenticationCao ThủNo ratings yet
- A Study On Comparison of Algorithm For One Time Password SystemDocument6 pagesA Study On Comparison of Algorithm For One Time Password SystemInternational Organization of Scientific Research (IOSR)No ratings yet
- Bio-Touchpass Efficient Password Mechanism To Overcome Spyware AttacksDocument9 pagesBio-Touchpass Efficient Password Mechanism To Overcome Spyware AttacksIJRASETPublicationsNo ratings yet
- Multi Factor Authentication Whitepaper Arx - Intellect DesignDocument12 pagesMulti Factor Authentication Whitepaper Arx - Intellect DesignIntellect DesignNo ratings yet
- Sniffeer Technology For Mobiles: Poonam SinglaDocument9 pagesSniffeer Technology For Mobiles: Poonam SinglaSantosh kumar reddy KudumulaNo ratings yet
- Privacy-Preserving Applications On Smartphones: Yan Huang Peter Chapman University of Virginia David EvansDocument6 pagesPrivacy-Preserving Applications On Smartphones: Yan Huang Peter Chapman University of Virginia David EvansZekria Noori AfghanNo ratings yet
- PSF Sample APIITDocument11 pagesPSF Sample APIITLim Keng LiangNo ratings yet
- PSF Sample APIITDocument11 pagesPSF Sample APIITLim Keng LiangNo ratings yet
- Procurement Management APIITDocument15 pagesProcurement Management APIITLim Keng LiangNo ratings yet
- PSF Sample APIITDocument11 pagesPSF Sample APIITLim Keng LiangNo ratings yet
- CRI AssignmentDocument19 pagesCRI AssignmentLim Keng LiangNo ratings yet
- Individual Assignment Object-Oriented Development with JavaDocument16 pagesIndividual Assignment Object-Oriented Development with JavaLim Keng Liang100% (1)
- ICP DocumentationDocument39 pagesICP DocumentationLim Keng LiangNo ratings yet
- Portable Programmer: FeaturesDocument1 pagePortable Programmer: FeaturesC VelNo ratings yet
- CEH Module 06: EnumerationDocument17 pagesCEH Module 06: EnumerationAhmad MahmoudNo ratings yet
- The Untold Story of Silk Road, Part 1Document42 pagesThe Untold Story of Silk Road, Part 1HeartwalkerNo ratings yet
- Exam Hall Ticket for Corporate Agents TestDocument1 pageExam Hall Ticket for Corporate Agents Testamit tiwariNo ratings yet
- STK Whitepaper enDocument12 pagesSTK Whitepaper encassius badueNo ratings yet
- Setup Mi WiFi Repeater with Other RoutersDocument76 pagesSetup Mi WiFi Repeater with Other RoutersCerebro CortexNo ratings yet
- 10982B LABsDocument106 pages10982B LABsUncarachaNo ratings yet
- Consider An Automated Teller MachineDocument5 pagesConsider An Automated Teller Machinekenneth delos santosNo ratings yet
- 3 E-Banking Security Issues - Is There A Solution in Biometrics - The Journal of Internet Banking and CommerceDocument10 pages3 E-Banking Security Issues - Is There A Solution in Biometrics - The Journal of Internet Banking and CommercesyazanaNo ratings yet
- Carbon Copy Cloner DocumentationDocument31 pagesCarbon Copy Cloner Documentationdmbtrpnbilly41No ratings yet
- Slashnext Targeted Phishing Defense DatasheetDocument2 pagesSlashnext Targeted Phishing Defense DatasheetNasirNo ratings yet
- Jonathan R Madi Koe HLP 14 Juni 17Document3 pagesJonathan R Madi Koe HLP 14 Juni 17agustinNo ratings yet
- Request For New PAN Card or / and Changes or Correction in PAN DataDocument2 pagesRequest For New PAN Card or / and Changes or Correction in PAN Datasv netNo ratings yet
- CNS Slide Set 1Document63 pagesCNS Slide Set 1Simple GuptaNo ratings yet
- TOEFL RonakDocument2 pagesTOEFL RonakBongo BashiNo ratings yet
- Prinsip Kerja PSVDocument4 pagesPrinsip Kerja PSVkaltumanikNo ratings yet
- Threat Protection - Windows 10Document3,502 pagesThreat Protection - Windows 10tetkaCNo ratings yet
- Vivares vs. STC, G.R. No. 202666, September 29, 2014Document11 pagesVivares vs. STC, G.R. No. 202666, September 29, 2014Lou Ann AncaoNo ratings yet
- TeamViewer API DocumentationDocument49 pagesTeamViewer API DocumentationTy TorresNo ratings yet
- Configure Juniper SRX Implicit DenyDocument3 pagesConfigure Juniper SRX Implicit DenyNguyen Hoang AnhNo ratings yet
- Online Examination SystemDocument18 pagesOnline Examination SystemAtul Kumar Singh100% (1)
- Av Delphi LibDocument29 pagesAv Delphi Lib2912882No ratings yet
- Syllabus: AIT 673 - Cyber Incident Handling/Response: Term: Spring 2018Document12 pagesSyllabus: AIT 673 - Cyber Incident Handling/Response: Term: Spring 2018ggcvbcNo ratings yet
- 17 03 2021Document3 pages17 03 2021OjjkkoNo ratings yet
- AuditScripts Critical Security Control Executive Assessment Tool V6.1aDocument4 pagesAuditScripts Critical Security Control Executive Assessment Tool V6.1aBruno RaimundoNo ratings yet
- Trading in a Global Environment: ISPS Code ImplementationDocument10 pagesTrading in a Global Environment: ISPS Code ImplementationIkoy Setyawan Keren100% (1)
- Attachment 1-PULL Data Dictionary V1.0.0 of The New FirmwareDocument17 pagesAttachment 1-PULL Data Dictionary V1.0.0 of The New FirmwareCreestianNo ratings yet
- Emerging Trendsof ICTin Teachingand LearningDocument14 pagesEmerging Trendsof ICTin Teachingand LearningJesse JollyNo ratings yet
- LOSA Ramp OperationsDocument70 pagesLOSA Ramp OperationskhagendrakryadavNo ratings yet
- Introduction To Introduction To SIM Cards SIM Cards PDFDocument64 pagesIntroduction To Introduction To SIM Cards SIM Cards PDFAndrew WaiNo ratings yet