Professional Documents
Culture Documents
25 Most Frequently Used Linux IPTables Rules PDF
Uploaded by
renegade78Original Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
25 Most Frequently Used Linux IPTables Rules PDF
Uploaded by
renegade78Copyright:
Available Formats
171 Like Like
Home
Free eBook
Contact
About
Start Here
25 Most Frequently Used Linux IPTables Rules Examples
by Ramesh Natarajan on June 14, 2011
Tweet 128
At a first glance, IPTables rules might look cryptic.
In this article, Ive given 25 practical IPTables rules that you can copy/paste and use it for your needs.
These examples will act as a basic templates for you to tweak these rules to suite your specific requirement.
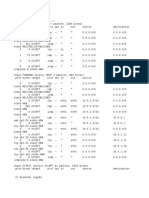
For easy reference, all these 25 iptables rules are in shell script format: iptables-rules
1. Delete Existing Rules
Before you start building new set of rules, you might want to clean-up all the default rules, and existing rules. Use the iptables flush command as shown below to do this.
iptables -F
(or)
iptables --flush
2. Set Default Chain Policies
The default chain policy is ACCEPT. Change this to DROP for all INPUT, FORWARD, and OUTPUT chains as shown below.
iptables -P INPUT DROP
iptables -P FORWARD DROP
iptables -P OUTPUT DROP
When you make both INPUT, and OUTPUT chains default policy as DROP, for every firewall rule requirement you have, you should define two rules. i.e one for incoming and one for
outgoing.
In all our examples below, we have two rules for each scenario, as weve set DROP as default policy for both INPUT and OUTPUT chain.
If you trust your internal users, you can omit the last line above. i.e Do not DROP all outgoing packets by default. In that case, for every firewall rule requirement you have, you just have
to define only one rule. i.e define rule only for incoming, as the outgoing is ACCEPT for all packets.
Note: If you dont know what a chain means, you should first familiarize yourself with the IPTables fundamentals.
3. Block a Specific ip-address
25 Most Frequently Used Linux IPTables Rules Examples http://www.thegeekstuff.com/2011/06/iptables-rules-examples/
1 of 10 10/15/2014 3:55 PM
Before we proceed further will other examples, if you want to block a specific ip-address, you should do that first as shown below. Change the x.x.x.x in the following example to the
specific ip-address that you like to block.
BLOCK_THIS_IP="x.x.x.x"
iptables -A INPUT -s "$BLOCK_THIS_IP" -j DROP
This is helpful when you find some strange activities from a specific ip-address in your log files, and you want to temporarily block that ip-address while you do further research.
You can also use one of the following variations, which blocks only TCP traffic on eth0 connection for this ip-address.
iptables -A INPUT -i eth0 -s "$BLOCK_THIS_IP" -j DROP
iptables -A INPUT -i eth0 -p tcp -s "$BLOCK_THIS_IP" -j DROP
4. Allow ALL Incoming SSH
The following rules allow ALL incoming ssh connections on eth0 interface.
iptables -A INPUT -i eth0 -p tcp --dport 22 -m state --state NEW,ESTABLISHED -j ACCEPT
iptables -A OUTPUT -o eth0 -p tcp --sport 22 -m state --state ESTABLISHED -j ACCEPT
Note: If you like to understand exactly what each and every one of the arguments means, you should read How to Add IPTables Firewall Rules
5. Allow Incoming SSH only from a Sepcific Network
The following rules allow incoming ssh connections only from 192.168.100.X network.
iptables -A INPUT -i eth0 -p tcp -s 192.168.100.0/24 --dport 22 -m state --state NEW,ESTABLISHED -j ACCEPT
iptables -A OUTPUT -o eth0 -p tcp --sport 22 -m state --state ESTABLISHED -j ACCEPT
In the above example, instead of /24, you can also use the full subnet mask. i.e 192.168.100.0/255.255.255.0.
6. Allow Incoming HTTP and HTTPS
The following rules allow all incoming web traffic. i.e HTTP traffic to port 80.
iptables -A INPUT -i eth0 -p tcp --dport 80 -m state --state NEW,ESTABLISHED -j ACCEPT
iptables -A OUTPUT -o eth0 -p tcp --sport 80 -m state --state ESTABLISHED -j ACCEPT
The following rules allow all incoming secure web traffic. i.e HTTPS traffic to port 443.
iptables -A INPUT -i eth0 -p tcp --dport 443 -m state --state NEW,ESTABLISHED -j ACCEPT
iptables -A OUTPUT -o eth0 -p tcp --sport 443 -m state --state ESTABLISHED -j ACCEPT
7. Combine Multiple Rules Together using MultiPorts
When you are allowing incoming connections from outside world to multiple ports, instead of writing individual rules for each and every port, you can combine them together using the
multiport extension as shown below.
The following example allows all incoming SSH, HTTP and HTTPS traffic.
iptables -A INPUT -i eth0 -p tcp -m multiport --dports 22,80,443 -m state --state NEW,ESTABLISHED -j ACCEPT
iptables -A OUTPUT -o eth0 -p tcp -m multiport --sports 22,80,443 -m state --state ESTABLISHED -j ACCEPT
8. Allow Outgoing SSH
The following rules allow outgoing ssh connection. i.e When you ssh from inside to an outside server.
iptables -A OUTPUT -o eth0 -p tcp --dport 22 -m state --state NEW,ESTABLISHED -j ACCEPT
iptables -A INPUT -i eth0 -p tcp --sport 22 -m state --state ESTABLISHED -j ACCEPT
Please note that this is slightly different than the incoming rule. i.e We allow both the NEW and ESTABLISHED state on the OUTPUT chain, and only ESTABLISHED state on the
INPUT chain. For the incoming rule, it is vice versa.
9. Allow Outgoing SSH only to a Specific Network
The following rules allow outgoing ssh connection only to a specific network. i.e You an ssh only to 192.168.100.0/24 network from the inside.
iptables -A OUTPUT -o eth0 -p tcp -d 192.168.100.0/24 --dport 22 -m state --state NEW,ESTABLISHED -j ACCEPT
iptables -A INPUT -i eth0 -p tcp --sport 22 -m state --state ESTABLISHED -j ACCEPT
10. Allow Outgoing HTTPS
The following rules allow outgoing secure web traffic. This is helpful when you want to allow internet traffic for your users. On servers, these rules are also helpful when you want to use
wget to download some files from outside.
iptables -A OUTPUT -o eth0 -p tcp --dport 443 -m state --state NEW,ESTABLISHED -j ACCEPT
iptables -A INPUT -i eth0 -p tcp --sport 443 -m state --state ESTABLISHED -j ACCEPT
Note: For outgoing HTTP web traffic, add two additional rules like the above, and change 443 to 80.
11. Load Balance Incoming Web Traffic
You can also load balance your incoming web traffic using iptables firewall rules.
This uses the iptables nth extension. The following example load balances the HTTPS traffic to three different ip-address. For every 3th packet, it is load balanced to the appropriate
server (using the counter 0).
iptables -A PREROUTING -i eth0 -p tcp --dport 443 -m state --state NEW -m nth --counter 0 --every 3 --packet 0 -j DNAT --to-destination 192.168.1.101:443
iptables -A PREROUTING -i eth0 -p tcp --dport 443 -m state --state NEW -m nth --counter 0 --every 3 --packet 1 -j DNAT --to-destination 192.168.1.102:443
25 Most Frequently Used Linux IPTables Rules Examples http://www.thegeekstuff.com/2011/06/iptables-rules-examples/
2 of 10 10/15/2014 3:55 PM
iptables -A PREROUTING -i eth0 -p tcp --dport 443 -m state --state NEW -m nth --counter 0 --every 3 --packet 2 -j DNAT --to-destination 192.168.1.103:443
12. Allow Ping from Outside to Inside
The following rules allow outside users to be able to ping your servers.
iptables -A INPUT -p icmp --icmp-type echo-request -j ACCEPT
iptables -A OUTPUT -p icmp --icmp-type echo-reply -j ACCEPT
13. Allow Ping from Inside to Outside
The following rules allow you to ping from inside to any of the outside servers.
iptables -A OUTPUT -p icmp --icmp-type echo-request -j ACCEPT
iptables -A INPUT -p icmp --icmp-type echo-reply -j ACCEPT
14. Allow Loopback Access
You should allow full loopback access on your servers. i.e access using 127.0.0.1
iptables -A INPUT -i lo -j ACCEPT
iptables -A OUTPUT -o lo -j ACCEPT
15. Allow Internal Network to External network.
On the firewall server where one ethernet card is connected to the external, and another ethernet card connected to the internal servers, use the following rules to allow internal network
talk to external network.
In this example, eth1 is connected to external network (internet), and eth0 is connected to internal network (For example: 192.168.1.x).
iptables -A FORWARD -i eth0 -o eth1 -j ACCEPT
16. Allow outbound DNS
The following rules allow outgoing DNS connections.
iptables -A OUTPUT -p udp -o eth0 --dport 53 -j ACCEPT
iptables -A INPUT -p udp -i eth0 --sport 53 -j ACCEPT
17. Allow NIS Connections
If you are running NIS to manage your user accounts, you should allow the NIS connections. Even when the SSH connection is allowed, if you dont allow the NIS related ypbind
connections, users will not be able to login.
The NIS ports are dynamic. i.e When the ypbind starts it allocates the ports.
First do a rpcinfo -p as shown below and get the port numbers. In this example, it was using port 853 and 850.
rpcinfo -p | grep ypbind
Now allow incoming connection to the port 111, and the ports that were used by ypbind.
iptables -A INPUT -p tcp --dport 111 -j ACCEPT
iptables -A INPUT -p udp --dport 111 -j ACCEPT
iptables -A INPUT -p tcp --dport 853 -j ACCEPT
iptables -A INPUT -p udp --dport 853 -j ACCEPT
iptables -A INPUT -p tcp --dport 850 -j ACCEPT
iptables -A INPUT -p udp --dport 850 -j ACCEPT
The above will not work when you restart the ypbind, as it will have different port numbers that time.
There are two solutions to this: 1) Use static ip-address for your NIS, or 2) Use some clever shell scripting techniques to automatically grab the dynamic port number from the rpcinfo
-p command output, and use those in the above iptables rules.
18. Allow Rsync From a Specific Network
The following rules allows rsync only from a specific network.
iptables -A INPUT -i eth0 -p tcp -s 192.168.101.0/24 --dport 873 -m state --state NEW,ESTABLISHED -j ACCEPT
iptables -A OUTPUT -o eth0 -p tcp --sport 873 -m state --state ESTABLISHED -j ACCEPT
19. Allow MySQL connection only from a specific network
If you are running MySQL, typically you dont want to allow direct connection from outside. In most cases, you might have web server running on the same server where the MySQL
database runs.
However DBA and developers might need to login directly to the MySQL from their laptop and desktop using MySQL client. In those case, you might want to allow your internal
network to talk to the MySQL directly as shown below.
iptables -A INPUT -i eth0 -p tcp -s 192.168.100.0/24 --dport 3306 -m state --state NEW,ESTABLISHED -j ACCEPT
iptables -A OUTPUT -o eth0 -p tcp --sport 3306 -m state --state ESTABLISHED -j ACCEPT
20. Allow Sendmail or Postfix Traffic
The following rules allow mail traffic. It may be sendmail or postfix.
iptables -A INPUT -i eth0 -p tcp --dport 25 -m state --state NEW,ESTABLISHED -j ACCEPT
iptables -A OUTPUT -o eth0 -p tcp --sport 25 -m state --state ESTABLISHED -j ACCEPT
25 Most Frequently Used Linux IPTables Rules Examples http://www.thegeekstuff.com/2011/06/iptables-rules-examples/
3 of 10 10/15/2014 3:55 PM
Tweet 128
171 Like Like
21. Allow IMAP and IMAPS
The following rules allow IMAP/IMAP2 traffic.
iptables -A INPUT -i eth0 -p tcp --dport 143 -m state --state NEW,ESTABLISHED -j ACCEPT
iptables -A OUTPUT -o eth0 -p tcp --sport 143 -m state --state ESTABLISHED -j ACCEPT
The following rules allow IMAPS traffic.
iptables -A INPUT -i eth0 -p tcp --dport 993 -m state --state NEW,ESTABLISHED -j ACCEPT
iptables -A OUTPUT -o eth0 -p tcp --sport 993 -m state --state ESTABLISHED -j ACCEPT
22. Allow POP3 and POP3S
The following rules allow POP3 access.
iptables -A INPUT -i eth0 -p tcp --dport 110 -m state --state NEW,ESTABLISHED -j ACCEPT
iptables -A OUTPUT -o eth0 -p tcp --sport 110 -m state --state ESTABLISHED -j ACCEPT
The following rules allow POP3S access.
iptables -A INPUT -i eth0 -p tcp --dport 995 -m state --state NEW,ESTABLISHED -j ACCEPT
iptables -A OUTPUT -o eth0 -p tcp --sport 995 -m state --state ESTABLISHED -j ACCEPT
23. Prevent DoS Attack
The following iptables rule will help you prevent the Denial of Service (DoS) attack on your webserver.
iptables -A INPUT -p tcp --dport 80 -m limit --limit 25/minute --limit-burst 100 -j ACCEPT
In the above example:
-m limit: This uses the limit iptables extension
limit 25/minute: This limits only maximum of 25 connection per minute. Change this value based on your specific requirement
limit-burst 100: This value indicates that the limit/minute will be enforced only after the total number of connection have reached the limit-burst level.
24. Port Forwarding
The following example routes all traffic that comes to the port 442 to 22. This means that the incoming ssh connection can come from both port 22 and 422.
iptables -t nat -A PREROUTING -p tcp -d 192.168.102.37 --dport 422 -j DNAT --to 192.168.102.37:22
If you do the above, you also need to explicitly allow incoming connection on the port 422.
iptables -A INPUT -i eth0 -p tcp --dport 422 -m state --state NEW,ESTABLISHED -j ACCEPT
iptables -A OUTPUT -o eth0 -p tcp --sport 422 -m state --state ESTABLISHED -j ACCEPT
25. Log Dropped Packets
You might also want to log all the dropped packets. These rules should be at the bottom.
First, create a new chain called LOGGING.
iptables -N LOGGING
Next, make sure all the remaining incoming connections jump to the LOGGING chain as shown below.
iptables -A INPUT -j LOGGING
Next, log these packets by specifying a custom log-prefix.
iptables -A LOGGING -m limit --limit 2/min -j LOG --log-prefix "IPTables Packet Dropped: " --log-level 7
Finally, drop these packets.
iptables -A LOGGING -j DROP
All of the above 25 iptables rules are in shell script format: iptables-rules
Previous articles in the iptables series:
Linux Firewall Tutorial: IPTables Tables, Chains, Rules Fundamentals
IPTables Flush: Delete / Remove All Rules On RedHat and CentOS Linux
Linux IPTables: How to Add Firewall Rules (With Allow SSH Example)
Linux IPTables: Incoming and Outgoing Rule Examples (SSH and HTTP)
> Add your comment
Linux provides several powerful administrative tools and utilities which will help you to manage your systems effectively. If you dont know what these
tools are and how to use them, you could be spending lot of time trying to perform even the basic administrative tasks. The focus of this course is to help you understand system
25 Most Frequently Used Linux IPTables Rules Examples http://www.thegeekstuff.com/2011/06/iptables-rules-examples/
4 of 10 10/15/2014 3:55 PM
administration tools, which will help you to become an effective Linux system administrator.
Get the Linux Sysadmin Course Now!
If you enjoyed this article, you might also like..
50 Linux Sysadmin Tutorials 1.
50 Most Frequently Used Linux Commands (With Examples) 2.
Top 25 Best Linux Performance Monitoring and Debugging Tools 3.
Mommy, I found it! 15 Practical Linux Find Command Examples 4.
Linux 101 Hacks 2nd Edition eBook 5.
Awk Introduction 7 Awk Print Examples
Advanced Sed Substitution Examples
8 Essential Vim Editor Navigation Fundamentals
25 Most Frequently Used Linux IPTables Rules Examples
Turbocharge PuTTY with 12 Powerful Add-Ons
Tags: IPTables Block IP, IPTables Block IP Address, IPTables Block Port, IPTables DNAT, IPTables HowTo, IPTables Log, IPTables NAT, IPTables Tutorial, IPTables Ubuntu
{ 37 comments read them below or add one }
1 kgas June 14, 2011 at 3:42 am
Good one and expecting all your iptables related writings in a single pdf file. Thanks
2 diptanu June 14, 2011 at 3:57 am
Hi,Thanks alot for the above info.However would like to know that if the blocking or allowing through iptables is possible for specific MAC address over internet, as because if my
eth0 is using a local ip 10.10.10.10 which is natted via public ip eg 100.100.100.100 and connected to internet via ISP, then someone from internet with specific MAC id (allowed
in iptables) should be able to ssh to my public ip (100.100.100.100) and the rest should be dropped.
Is that possible over the internet
3 Manoj June 14, 2011 at 4:25 am
Keep Writing Gr8 Work!!!
4 Gareth Williams June 14, 2011 at 11:16 am
Diptanu you cannot filter packets based on mac addresses. Even if that was possible that host is not on your subnet therefore you do not communicate to it or it to you using MAC
address. When communicating to that host all traffic is routed via your default gateway.
5 Marcin Rybak June 14, 2011 at 2:26 pm
First ruleset should go deep deep , if somebody has default policy to drop first rule:
iptables -F, will cut him out. You have been warned
6 Kishore June 14, 2011 at 2:59 pm
Very Useful
7 Vonskippy June 14, 2011 at 3:03 pm
A default rule should always be block ALL outbound traffic on TCP25 except to your own email server.
8 vierupro June 16, 2011 at 3:07 am
Good collection of iptables rules!
Just wanted to mention that -m limit does match packets not connections, so in your example you will match 25 packets per minute, which I think is not what you want to.
The solution to limit the number of connections is to use connlimit match.
an example:
iptables -A INPUT -p tcp syn dport 80 -m connlimit connlimit-above 15 connlimit-mask 32 -j REJECT reject-with tcp-reset
that will reject connections above 15 from one source IP a very good rule to defend a web server.
Also it will be great to add to your list of rules an example with hashlimit match, which has more options when you want to protect from a DDoS attack.
With limit match you can limit the global rate of packets per time interval, but with hashlimit, you can limit them per IP, per combination IP + port, etc.
So an example for a web server will be something like that:
iptables -A INPUT -p tcp dport 80 -m hashlimit hashlimit 45/sec hashlimit-burst 60 hashlimit-mode srcip
hashlimit-name DDOS hashlimit-htable-size 32768 hashlimit-htable-max 32768 hashlimit-htable-gcinterval 1000
hashlimit-htable-expire 100000 -j ACCEPT
Hope this will help someone.
Anyway, thanks for a good article!
9 Paul M June 30, 2011 at 7:59 am
25 Most Frequently Used Linux IPTables Rules Examples http://www.thegeekstuff.com/2011/06/iptables-rules-examples/
5 of 10 10/15/2014 3:55 PM
it makes sense to have a generic rule permitting established/related for input and forwarded, allow all outbound traffic from the firewall itself, and then control traffic in the
forwarded or input chain, otherwise it gets too complex too quickly.
and dont forget to add rules for the lo interface.
10 jalal hajigholamali October 21, 2011 at 11:04 am
very good thanks
11 Sharad December 12, 2011 at 6:11 am
Really helped me a lot
Just 1 question, after implementing some of the policies, My server is unable to resolve any domain name.
12 Rod_Moncada January 16, 2012 at 4:48 pm
Hey Sharad,
Actually need to open port 53 for INPUT. Something like this will work:
# dnsserver=ipaddress
# iptables -A INPUT -p udp sport 53 dport 1024:65535 -d $dnsserver -j ACCEPT
That worked for me, please some advice if theres a better or safer way
13 Stuart January 28, 2012 at 2:17 pm
Excellent. Thanks.
14 de2x February 24, 2012 at 11:13 pm
Can i allow host/domain google on iptables? can you tell me, please help..
15 tarani March 28, 2012 at 7:36 am
EXELLENT
16 Curtis Ruck May 8, 2012 at 2:52 pm
How can you forward traffic (like 443) to a hidden server (i.e. in a DMZ) from one NIC to another? Ive tried setting up your rule #24, but the packets are getting logged and
dropped from the FORWARD chain.
17 Max May 27, 2012 at 2:13 pm
VERY USEFULL ARTICE.
@vierupro, I have router with busybox and have defined many rules to set network limits. plz write down a rule which is capable to limit download speed to 20 kb /s for a specif IP.
18 sriram r July 9, 2012 at 5:51 pm
Is there a rule so I can make my outbound https sessions sticky using iptables? I am trying to achieve this on a dual WAN dd-wrt router (Linksys E2000)
19 Kennedy August 25, 2012 at 8:26 am
Error applying iptables rules. Exit code: 11.
iptables v1.4.10
iptables: No chain/target/ match by that name.
Can any one tell what this error is and how to over come.
I have a android phone and i am tring to install a firewall in my rooted device and i am stuck with this error.
20 Renato September 13, 2012 at 9:44 pm
How do I compare two linux firewall, in terms of network security?
21 Saed September 28, 2012 at 10:01 pm
that right Paul M
iptables flush
iptables policy INPUT DROP
iptables policy OUTPUT DROP
iptables policy FORWARD DROP
iptables append INPUT -i lo -j ACCEPT
iptables append OUTPUT -o lo -j ACCEPT
iptables append INPUT -m state state \
ESTABLISHED,RELATED -j ACCEPT
iptables append OUTPUT -m state state \
NEW,ESTABLISHED,RELATED -j ACCEPT
22 aleee January 30, 2013 at 2:09 am
thanks..
23 dp February 23, 2013 at 7:24 am
Hai Friends,
25 Most Frequently Used Linux IPTables Rules Examples http://www.thegeekstuff.com/2011/06/iptables-rules-examples/
6 of 10 10/15/2014 3:55 PM
Please let me know how to restrict the server access by using the iptables with mac addressses.
I want to give permission only to 2 mac addresses and restict the remaining mac addresses to connect with the server.
Thanks
dp
24 Amit Shrivastava April 9, 2013 at 2:51 am
Good collectionThx
25 Sumanta April 25, 2013 at 1:42 am
Hi,
Thanks for this great article! I have one query regarding the deletion of a rule.
I am creating a static nat rule in iptables using the command
iptables -t nat -I POSTROUTING 1 -j SNAT -p ip -s 1.1.1.10/32 to-source 2.2.2.30-2.2.2.30 -o eth2
After executing the above command i am able to observe the source translation happening and also it is listed in the iptables nat list.
After I remove the rule by executing the below command
iptables -t nat -D POSTROUTING -j SNAT -p ip -s 1.1.1.10/32 to-source 2.2.2.30-2.2.2.30 -o eth2
The entry in the iptables nat is deleted, but i am still able to observe the source translation happening from 1.1.1.10 to 2.2.2.30.
Please suggest what i need to do to delete the entry completely from the nat table or did i missed something.
Thanks in advance!
Regards,
Sumanta.
26 Daniel June 10, 2013 at 12:25 am
I would offer that you may want to consider changing the order you discuss the commands.
MOST things in linux require a service x restart in order to put the change into effect.
Not, apparently, iptables.
Telling a VPS to drop ALL traffic while youre SSHd into it is never a good idea.
27 Br H August 5, 2013 at 6:36 am
Hi,
Thanks for this wonderful list.
Just with the emails the only configuration that worked was with the following three rules:
iptables -A OUTPUT -o eth0 -p tcp sport 25 -m state state NEW,ESTABLISHED -j ACCEPT
iptables -A OUTPUT -o eth0 -p tcp dport 25 -m state state NEW,ESTABLISHED -j ACCEPT
iptables -A INPUT -i eth0 -p tcp sport 25 -m state state ESTABLISHED -j ACCEPT
Many thanks again
28 iabc August 27, 2013 at 9:10 am
Here is iptables for passive ftp if anyone is interested.
& Thanks for Ramesh for your wonderful blogs.
iptables -A INPUT -p tcp -m tcp dport 21 -m state state NEW,ESTABLISHED -j ACCEPT
iptables -A OUTPUT -p tcp -m tcp sport 21 -m state state ESTABLISHED -j ACCEPT
iptables -A INPUT -p tcp -m tcp sport 1024:65535 dport 1024:65535 -m state state NEW,RELATED,ESTABLISHED -j ACCEPT
iptables -A OUTPUT -p tcp -m tcp sport 1024:65535 dport 1024:65535 -m state state NEW,RELATED,ESTABLISHED -j ACCEPT
29 iTommix September 2, 2013 at 7:25 am
Hi,
nice tutorial. I have a following question:
I build a captive portal (hotspot) using iptables. from the beginning i block every port and routing to an splash page on the own apache server:
iptables -t mangle -A PREROUTING -i wlan0 -p tcp -m tcp dport 1:65535 -j internet
iptables -t nat -A PREROUTING -i wlan0 -p tcp -m mark mark 99 -m tcp dport 1:65535 -j DNAT to-destination 10.0.0.254
But i need an exception on a specific domain to load some css and javascript files into this splash page. How can i do this?
Regards an thanks for reply in advance.
30 tarvi October 16, 2013 at 12:29 am
What is eth0 ?
31 zug October 16, 2013 at 10:32 pm
25 Most Frequently Used Linux IPTables Rules Examples http://www.thegeekstuff.com/2011/06/iptables-rules-examples/
7 of 10 10/15/2014 3:55 PM
Very helpful and a good introduction. Thanks.
32 saththiyan November 3, 2013 at 10:18 pm
hey ,
I have two AWS instances , Ngx and another one call WP, WP running a as hosting server and Ngx is proxy. I need to configure WP to accept only HTTP request from Ngx. How
do i do this?
33 saththiyan November 3, 2013 at 10:23 pm
Hi,
I need to configure firewall ( iptable) to accept HTTP request from a server, How do i configure this?
i have two instances on AWS, instance one need to accept HTTP request from Instance two only.
How do i configure ? Do i need to configure incoming and outgoing http request ?
34 Anon February 10, 2014 at 6:13 am
It worked for me, Gj!
35 Anitha February 13, 2014 at 12:54 am
We have to block the unused IPs through IPTABLE, for example one of our branch network has configured through this range 192.168.3.0/24 and many unused IPs are present in
this series. For some reason we have to block the unused IP address.How could we have to block those IPs (Unused IPs like 192.168.3.5, 192.168.3.10 to 192.168.3.20,
192.168.3.24, 192.168.3.27, etc.,)
36 Mitchelle June 5, 2014 at 5:04 am
Hello,
I am not able to access to imap and smtp ports 465 and 993 to access gmail using outlook express or ms outlook. Though i have accepted both ports in iptables. Still cant access.
Is there anything else our gateway that is ubuntu 14.04, proxy is on. two interface card one connecting to router and one to internal interface.
Any ideas?
37 Holger June 24, 2014 at 4:15 pm
Example 24: you dont have to open port 422, the prerouting is done before filter!
Leave a Comment
Name
E-mail
Website
Notify me of followup comments via e-mail
Previous post: Top 7 Free SFTP or SCP Clients for Windows (Transfer Files to Linux)
Next post: Happy 3rd Birthday to The Geek Stuff
RSS | Email | Twitter | Facebook | Google+
Search
COURSE
25 Most Frequently Used Linux IPTables Rules Examples http://www.thegeekstuff.com/2011/06/iptables-rules-examples/
8 of 10 10/15/2014 3:55 PM
Linux Sysadmin CentOS 6 Course - Master the Tools, Configure it Right, and be Lazy
EBOOKS
Linux 101 Hacks 2nd Edition eBook - Practical Examples to Build a Strong Foundation in Linux
Bash 101 Hacks eBook - Take Control of Your Bash Command Line and Shell Scripting
Sed and Awk 101 Hacks eBook - Enhance Your UNIX / Linux Life with Sed and Awk
Vim 101 Hacks eBook - Practical Examples for Becoming Fast and Productive in Vim Editor
Nagios Core 3 eBook - Monitor Everything, Be Proactive, and Sleep Well
The Geek Stuff
8,057 people like The Geek Stuff.
Like Like
POPULAR POSTS
12 Amazing and Essential Linux Books To Enrich Your Brain and Library
50 UNIX / Linux Sysadmin Tutorials
50 Most Frequently Used UNIX / Linux Commands (With Examples)
How To Be Productive and Get Things Done Using GTD
30 Things To Do When you are Bored and have a Computer
Linux Directory Structure (File System Structure) Explained with Examples
Linux Crontab: 15 Awesome Cron Job Examples
Get a Grip on the Grep! 15 Practical Grep Command Examples
Unix LS Command: 15 Practical Examples
15 Examples To Master Linux Command Line History
Top 10 Open Source Bug Tracking System
Vi and Vim Macro Tutorial: How To Record and Play
Mommy, I found it! -- 15 Practical Linux Find Command Examples
15 Awesome Gmail Tips and Tricks
15 Awesome Google Search Tips and Tricks
RAID 0, RAID 1, RAID 5, RAID 10 Explained with Diagrams
Can You Top This? 15 Practical Linux Top Command Examples
Top 5 Best System Monitoring Tools
Top 5 Best Linux OS Distributions
How To Monitor Remote Linux Host using Nagios 3.0
Awk Introduction Tutorial 7 Awk Print Examples
How to Backup Linux? 15 rsync Command Examples
The Ultimate Wget Download Guide With 15 Awesome Examples
Top 5 Best Linux Text Editors
Packet Analyzer: 15 TCPDUMP Command Examples
The Ultimate Bash Array Tutorial with 15 Examples
3 Steps to Perform SSH Login Without Password Using ssh-keygen & ssh-copy-id
Unix Sed Tutorial: Advanced Sed Substitution Examples
UNIX / Linux: 10 Netstat Command Examples
The Ultimate Guide for Creating Strong Passwords
6 Steps to Secure Your Home Wireless Network
Turbocharge PuTTY with 12 Powerful Add-Ons
CATEGORIES
Linux Tutorials
Vim Editor
Sed Scripting
Awk Scripting
Bash Shell Scripting
Nagios Monitoring
OpenSSH
IPTables Firewall
Apache Web Server
MySQL Database
Perl Programming
Google Tutorials
Ubuntu Tutorials
PostgreSQL DB
Hello World Examples
C Programming
C++ Programming
DELL Server Tutorials
Oracle Database
VMware Tutorials
25 Most Frequently Used Linux IPTables Rules Examples http://www.thegeekstuff.com/2011/06/iptables-rules-examples/
9 of 10 10/15/2014 3:55 PM
About The Geek Stuff
My name is Ramesh Natarajan. I will be posting instruction guides, how-to, troubleshooting tips and tricks on Linux, database, hardware, security and web. My
focus is to write articles that will either teach you or help you resolve a problem. Read more about Ramesh Natarajan and the blog.
Support Us
Support this blog by purchasing one of my ebooks.
Bash 101 Hacks eBook
Sed and Awk 101 Hacks eBook
Vim 101 Hacks eBook
Nagios Core 3 eBook
Contact Us
Email Me : Use this Contact Form to get in touch me with your comments, questions or suggestions about this site. You can also simply drop me a line to say hello!.
Follow us on Google+
Follow us on Twitter
Become a fan on Facebook
Copyright 20082014 Ramesh Natarajan. All rights reserved | Terms of Service
25 Most Frequently Used Linux IPTables Rules Examples http://www.thegeekstuff.com/2011/06/iptables-rules-examples/
10 of 10 10/15/2014 3:55 PM
You might also like
- 25 Most Frequently Used Linux IPTables Rules ExamplesDocument8 pages25 Most Frequently Used Linux IPTables Rules ExamplesictnewNo ratings yet
- 25 Most Frequently Used Linux IPTables Rules ExamplesDocument15 pages25 Most Frequently Used Linux IPTables Rules ExamplesSwak StekieNo ratings yet
- Iptables - F (Or) Iptables - Flush: 1. Delete Existing RulesDocument5 pagesIptables - F (Or) Iptables - Flush: 1. Delete Existing RulesZumaro QoirulNo ratings yet
- Iptables Essentials: Common Firewall Rules and Commands: How To Use This GuideDocument12 pagesIptables Essentials: Common Firewall Rules and Commands: How To Use This GuideLuis Eduardo Becerra RuízNo ratings yet
- 10 Iptables Rules To Help Secure Your Linux Box - TechRepublic PDFDocument3 pages10 Iptables Rules To Help Secure Your Linux Box - TechRepublic PDFozanalikayaNo ratings yet
- Working With IptablesDocument10 pagesWorking With IptablesMordor ChaliceNo ratings yet
- Centos / Redhat Iptables Firewall Configuration TutorialDocument7 pagesCentos / Redhat Iptables Firewall Configuration TutorialsaidpmkNo ratings yet
- DL 10 IptablesDocument4 pagesDL 10 Iptablesdiptimehra1247No ratings yet
- Iptables 1Document13 pagesIptables 1srinivasNo ratings yet
- Linux 20 Iptables Examples For New SysAdminsDocument7 pagesLinux 20 Iptables Examples For New SysAdminsalls_allsNo ratings yet
- Contoh Konfigurasi Firewall Pada VoipDocument2 pagesContoh Konfigurasi Firewall Pada VoipBudi Kurniawan100% (1)
- Lab Assignment 11 Firewalls Using IPTABLESDocument12 pagesLab Assignment 11 Firewalls Using IPTABLESRahul ShahNo ratings yet
- Iptables Tutorial For BeginnersDocument4 pagesIptables Tutorial For BeginnerssaidpmkNo ratings yet
- Asterisknow - Iptables Firewall ConfigurationDocument3 pagesAsterisknow - Iptables Firewall ConfigurationJuan PerezNo ratings yet
- Linux Forward PortDocument3 pagesLinux Forward PortIoas IodfNo ratings yet
- How To Set Up A VPN Server On UbuntuDocument4 pagesHow To Set Up A VPN Server On UbuntuMD ABUL KHAYERNo ratings yet
- Linux Operating IptablesDocument5 pagesLinux Operating IptablesVenu GopalNo ratings yet
- Firewall LinuxDocument6 pagesFirewall LinuxDeepu MeackelNo ratings yet
- Linux Ip TablesDocument20 pagesLinux Ip Tablesd14n4dNo ratings yet
- WCG FAQs 78Document10 pagesWCG FAQs 78list_courseNo ratings yet
- Configuration of NAT With Iptablesep Configuration of NAT With IptablesDocument8 pagesConfiguration of NAT With Iptablesep Configuration of NAT With IptablesSreedhar SidNo ratings yet
- Linux Firewall Tutorial: Iptables Tables, Chains, Rules FundamentalsDocument12 pagesLinux Firewall Tutorial: Iptables Tables, Chains, Rules FundamentalsSigmahardik HardikNo ratings yet
- #1: Displaying The Status of Your Firewall: Type The Following Command As RootDocument19 pages#1: Displaying The Status of Your Firewall: Type The Following Command As Rootarjun bNo ratings yet
- Iptables and Nat ConfigurationDocument30 pagesIptables and Nat ConfigurationRavi Prakash ReddyNo ratings yet
- Ip TablesDocument6 pagesIp TablesPedroNo ratings yet
- Linux Operating SystemDocument9 pagesLinux Operating SystemASAP ChannelNo ratings yet
- Iptables 2Document34 pagesIptables 2Claudemir De Almeida RosaNo ratings yet
- Boot Process: Run Level DescriptionDocument7 pagesBoot Process: Run Level Descriptiongaurav775588No ratings yet
- Ip TablesDocument14 pagesIp TablesSri WasteNo ratings yet
- PasosDocument4 pagesPasosVíctor PintoNo ratings yet
- Setting Up HTB On CentOS 6 PDFDocument4 pagesSetting Up HTB On CentOS 6 PDFLeandro Henrique AgostinhoNo ratings yet
- Netfilter TutorialDocument31 pagesNetfilter TutorialarieffirdausNo ratings yet
- Iptables Firewall: From WikiDocument9 pagesIptables Firewall: From Wikidisse_detiNo ratings yet
- ClearOS Incoming FirewallDocument7 pagesClearOS Incoming FirewallztehackNo ratings yet
- Nftables Firewall Setup LinuxDocument10 pagesNftables Firewall Setup Linuxlinuxer69No ratings yet
- Linux Firewall - IPTABLESDocument8 pagesLinux Firewall - IPTABLESVenugopal100% (1)
- + Iptables: Packet Filtering && FirewallDocument31 pages+ Iptables: Packet Filtering && Firewall-aaa-No ratings yet
- 1xHOWTO Open VPNDocument26 pages1xHOWTO Open VPNFlorencio CoquillaNo ratings yet
- Ril - Lab6dobre Marcela Fils FrancezaDocument7 pagesRil - Lab6dobre Marcela Fils FrancezaMarcela DobreNo ratings yet
- ITC314 TP5 IptablesDocument4 pagesITC314 TP5 Iptablesamine.besrour5214No ratings yet
- Firewalld Basic: Disabling Iptables ServiceDocument5 pagesFirewalld Basic: Disabling Iptables ServiceGOLDEN FISHNo ratings yet
- Rhel Notes For Rh253Document27 pagesRhel Notes For Rh253jayaraj5382100% (1)
- Linux Firewall With IptablesDocument39 pagesLinux Firewall With IptablesnarsingthakurNo ratings yet
- Contoh Iptables RulesDocument15 pagesContoh Iptables RulesLintangNo ratings yet
- Linux Iptables Firewall Configuration: Prince - KenshiDocument8 pagesLinux Iptables Firewall Configuration: Prince - KenshiMohith VarmaNo ratings yet
- Cyberciti - Biz-Linux Iptables Setup Firewall For A Web ServerDocument7 pagesCyberciti - Biz-Linux Iptables Setup Firewall For A Web Serverlist_courseNo ratings yet
- Adding Iptables Rules On SmoothWallDocument4 pagesAdding Iptables Rules On SmoothWallviviribNo ratings yet
- Highly Available ELKDocument22 pagesHighly Available ELKHalim Maulana LNo ratings yet
- Iptables: Configuring/Modifying IptablesDocument4 pagesIptables: Configuring/Modifying IptablesSovello HildebrandNo ratings yet
- Flytrap Exploit Enhancements 12 2007 Dev NotesDocument18 pagesFlytrap Exploit Enhancements 12 2007 Dev Notes0xbitNo ratings yet
- How Do I Block An IP Address On My Linux ServerDocument1 pageHow Do I Block An IP Address On My Linux ServerhuberttulanNo ratings yet
- Fortigate Firewall HA A-P - A-A Mode ConfigurationDocument28 pagesFortigate Firewall HA A-P - A-A Mode ConfigurationLolNo ratings yet
- Quick CommandsDocument9 pagesQuick CommandsMark WoffardNo ratings yet
- Block Ports in Windows FirewallDocument11 pagesBlock Ports in Windows Firewallsuper quotes newNo ratings yet
- Secure Your Kloxo Installation With Your Firewall/IPTABLESDocument4 pagesSecure Your Kloxo Installation With Your Firewall/IPTABLESMatt JanecekNo ratings yet
- 03 Linux Firewall 1Document21 pages03 Linux Firewall 1TuggNo ratings yet
- Linux Firewalls (Ubuntu Iptables)Document21 pagesLinux Firewalls (Ubuntu Iptables)vetti KuttyNo ratings yet
- CISCO PACKET TRACER LABS: Best practice of configuring or troubleshooting NetworkFrom EverandCISCO PACKET TRACER LABS: Best practice of configuring or troubleshooting NetworkNo ratings yet
- 10 Frequently Asked SQL Query Interview Questions - Java67Document26 pages10 Frequently Asked SQL Query Interview Questions - Java67renegade78No ratings yet
- SQL - A Practical Introduction PDFDocument179 pagesSQL - A Practical Introduction PDFmthithetNo ratings yet
- Starting and Stopping Apache ServerDocument4 pagesStarting and Stopping Apache Serverrenegade78No ratings yet
- Jetty Server: Windows XP/VistaDocument3 pagesJetty Server: Windows XP/Vistarenegade78No ratings yet
- Fortigate - DHCP Lease Clear IP - KB at HeratorDocument1 pageFortigate - DHCP Lease Clear IP - KB at Heratorrenegade78No ratings yet
- How To Configure ESXi To Shutdown Using An APC ..Document10 pagesHow To Configure ESXi To Shutdown Using An APC ..renegade78No ratings yet
- WAP3205 1 Ed2Document208 pagesWAP3205 1 Ed2renegade78No ratings yet
- Network Discovery - Turn On or Off in Windows 7Document4 pagesNetwork Discovery - Turn On or Off in Windows 7renegade78No ratings yet
- How To Create and Delete VLAN On Cisco Catalyst SwitchDocument9 pagesHow To Create and Delete VLAN On Cisco Catalyst Switchrenegade78No ratings yet
- How To Configure DNS Server in LinuxDocument7 pagesHow To Configure DNS Server in Linuxrenegade78No ratings yet
- How To Use Print Server FeatureDocument39 pagesHow To Use Print Server Featurerenegade78No ratings yet
- Overview of SAP Author Is at IonsDocument6 pagesOverview of SAP Author Is at Ionsrenegade78No ratings yet
- MB Manual Ga-P41t-Usb3l eDocument88 pagesMB Manual Ga-P41t-Usb3l erenegade78No ratings yet
- Steps To Install SAP Note: S AP Basis Components, Application Modules, Certification, ABAP/4 Programming BooksDocument2 pagesSteps To Install SAP Note: S AP Basis Components, Application Modules, Certification, ABAP/4 Programming Booksrenegade78No ratings yet
- Aki Moilanen Tips and TricksDocument34 pagesAki Moilanen Tips and Trickssen2natNo ratings yet
- Technical Drafting Ncii: Sunny B. Ojeda, RMPDocument27 pagesTechnical Drafting Ncii: Sunny B. Ojeda, RMPDel James LambongogNo ratings yet
- Riya Saini: ObjectivesDocument7 pagesRiya Saini: ObjectivesRiya SainiNo ratings yet
- Poster Workshop of The Complex Systems Design & Management Conference CSD&M 2014Document292 pagesPoster Workshop of The Complex Systems Design & Management Conference CSD&M 2014Sứa BiểnNo ratings yet
- Frampton, Toward S A Critical Regionalism, 1983Document8 pagesFrampton, Toward S A Critical Regionalism, 1983Georgi StanishevNo ratings yet
- VS7000 UserManual v02.11 EdDDocument276 pagesVS7000 UserManual v02.11 EdDAlejandro GomezNo ratings yet
- Structural Risk Assessment & Method Statement: Planning ApplicationDocument19 pagesStructural Risk Assessment & Method Statement: Planning ApplicationNaresh DharmaNo ratings yet
- Jahanpanah ClubDocument4 pagesJahanpanah ClubAanchal MishraNo ratings yet
- Agra City Is World Famous For Its Seventh WonderDocument2 pagesAgra City Is World Famous For Its Seventh WonderSonam GuptaNo ratings yet
- Interim Geotech Report For Umer Hospital Sanda Raj Garh LahoreDocument9 pagesInterim Geotech Report For Umer Hospital Sanda Raj Garh Lahoremazhar955No ratings yet
- Construction of Heydar Aliyev Center by Zaha Hadid (Part 1) Adelto AdeltoDocument13 pagesConstruction of Heydar Aliyev Center by Zaha Hadid (Part 1) Adelto AdeltoRAJ AGRAWAL33% (3)
- HUAWEI CloudEngine 6800 Switch Datasheet PDFDocument12 pagesHUAWEI CloudEngine 6800 Switch Datasheet PDFMendizabal Eduardo EmilioNo ratings yet
- SlabDocument8 pagesSlabchristianNo ratings yet
- Amp CEAG Ex-Safety 20ADocument3 pagesAmp CEAG Ex-Safety 20Arocket-vtNo ratings yet
- Shortening Estimate of Post Tensioned Floors TN458Document16 pagesShortening Estimate of Post Tensioned Floors TN458Anonymous x9STa9No ratings yet
- Stonehell Dungeon - II - Into The Heart of Hell PDFDocument170 pagesStonehell Dungeon - II - Into The Heart of Hell PDFrcsample67% (3)
- Ï ® 6 Uxk 1429 Êçð Hšóõk 2009Document12 pagesÏ ® 6 Uxk 1429 Êçð Hšóõk 2009rosgazNo ratings yet
- Rapid Problem Resolution (RPR) ExplainedDocument12 pagesRapid Problem Resolution (RPR) Explainedaks1995No ratings yet
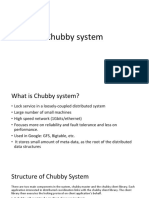
- Chubby System and Google APIDocument13 pagesChubby System and Google APIVivek JadhavNo ratings yet
- IndexDocument212 pagesIndexbecketsbestNo ratings yet
- Phoenix Contact 2832771Document4 pagesPhoenix Contact 2832771e9uerraNo ratings yet
- Gate DetailsDocument149 pagesGate DetailsMadhav BaralNo ratings yet
- Coastal Construction ManualDocument279 pagesCoastal Construction ManualRomina Roxana Rivera LemonaoNo ratings yet
- Residential House Building TemplateDocument91 pagesResidential House Building Templateanuj3936No ratings yet
- What'S New in Ibm Integration Bus & Websphere Message BrokerDocument43 pagesWhat'S New in Ibm Integration Bus & Websphere Message BrokerAli100% (1)
- Assembly Language Fundamentals: Javeria AminDocument42 pagesAssembly Language Fundamentals: Javeria AminAtiqa SafdarNo ratings yet
- Posco E&c - Manual of Seismic Steel Connections v1.1Document524 pagesPosco E&c - Manual of Seismic Steel Connections v1.1David Santiago100% (3)
- Pattern Samples PDFDocument3 pagesPattern Samples PDFm0211No ratings yet
- Die Casting Design PDFDocument38 pagesDie Casting Design PDFPrabagarane Ramachandran100% (2)
- CustomObject-Utilization Best Practices - FinalDocument13 pagesCustomObject-Utilization Best Practices - FinalBogdan VasileNo ratings yet