Professional Documents
Culture Documents
Autonomous PG CURRICULUM Web Curriculum ME CSE
Uploaded by
rishikarthick0 ratings0% found this document useful (0 votes)
83 views54 pageskoioo
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this Documentkoioo
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
83 views54 pagesAutonomous PG CURRICULUM Web Curriculum ME CSE
Uploaded by
rishikarthickkoioo
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 54
23
MEPCO SCHLENK ENGINEERING COLLEGE, SIVAKASI (AUTONOMOUS)
AFFILIATED TO ANNA UNIVERSITY, CHENNAI 600 025
REGULATIONS: MEPCO - R2013 (FULL TIME)
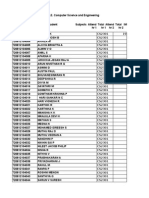
M.E. COMPUTER SCIENCE AND ENGINEERING
Department Vision Department Mission
To become the centre of
excellence in computer education
and research and to create the
platform for industrial
consultancy
o To produce globally competent and quality computer
professionals by educating computer concepts and
techniques.
o To facilitate the students to work with recent tools
and technologies.
o To mould the students by inculcating the spirit of
moral values contributing to the societal ethics.
Programme Educational Objectives (PEOs) M.E Computer Science and Engineering
After 3 to 5 years of completing the Programme on Master of Computer Science and Engineering, the
post graduates will become:
PEO
No.
PEO
1.
Competent Computer/Software Engineer rendering expertise to the industrial and societal
needs in an effective manner.
2. Sustained learner to bring out novel ideas by addressing the research issues
3. Trainer/Philosopher to guide others towards the development of technology
Programme Outcomes (POs) M.E Computer Science and Engineering
During the course of the programme on Master of Computer Science and Engineering the learners
will acquire the ability to:
PO
Number
PO
1.
Apply knowledge of mathematics, science and information science in computer
engineering in advance level
2.
Design a Comput er system with components and processes of desired needs within
realistic constraints such as economic, environmental, social, political, ethical, health
and safety
3.
Identify and modify the functions of the internal of computer components such as
operating systems and compilers
4.
Apply Software Engineering principles, techniques and tools in software development
5.
Create, collect, process, view, organize, store, mine and retrieve data in both local and
remote locations in a secure and effective manner
6.
Design and conduct experiments, as well as to analyze and interpret data to lay a
foundation for solving complex problems
24
PO
Number
PO
7.
Engage in life-long learning to acquire knowledge of contemporary issues to meet the
challenges in the career
8.
Apply the skills and techniques in computer engineering and inter-disciplinary domains for
providing solutions in a global, economic, environmental, and societal context
9.
Develop research skills and innovative ideas
10.
Model the real world problems to address and share the research issues
11.
Share their knowledge and express their ideas in any technical forum
12.
Present their ideas to prepare for a position to educate and guide others
CURRICULUM (I TO IV SEMESTER)
I SEMESTER
SL.
NO.
COURSE
CODE
COURSE TITLE L T P C
THEORY
1.
13MA174 Mathematics and Statistics for Computer
Science
3 1 0 4
2.
13MC101 Advanced Data Structures & Algorithms
(Common to ME CSE &MTech IT)
3 0 0 3
3.
13MC102 Design and Management of Computer
Networks
3 0 2 4
4.
13MC103 Software Architectures 3 0 0 3
5.
13MC104 Advanced Databases 3 0 0 3
6.
13MC105 Multicore Architectures 3 0 0 3
PRACTICAL
7. 13MC151 Advanced Data Structures Laboratory
(Common to ME CSE &MTech IT)
0 0 3 2
8. 13MC152 Advanced Databases Laboratory 0 0 3 2
CREDITS 18 1 8 24
II SEMESTER
SL.
NO.
COURSE
CODE
COURSE TITLE L T P C
THEORY
1.
13MC201 Advanced Operating Systems 3 0 0 3
2.
13MC202 Machine Learning Techniques 3 0 2 4
3.
13MI202 Cloud Computing Technologies
(Common to ME CSE &MTech IT)
3 0 0 3
4.
13MI204 Big Data Analytics
(Common to ME CSE &MTech IT)
3 0 0 3
5.
Elective I 3 0 0 3
6.
Elective II 3 0 0 3
25
PRACTICAL
7.
13MC251 Advanced Operating Systems Laboratory 0 0 3 2
8.
13MI252 Cloud Computing Laboratory
(Common to ME CSE &M.Tech. IT)
0 0 3 2
9.
13MC252 Technical Seminar* 0 0 2 1
CREDITS 18 0 10 24
* Internal Assessment Only
III SEMESTER
SL.
NO.
COURSE
CODE
COURSE TITLE L T P C
THEORY
1.
13MC301 Parallel Programming Paradigms 3 0 2 4
2.
Elective III 3 0 2 4
3.
Elective IV 3 0 2 4
PRACTICAL
4.
13MC351 Project Work (Phase I) 0 0 12 6
CREDITS 9 0 18 18
IV SEMESTER
SL.
NO.
COURSE
CODE
COURSE TITLE L T P C
PRACTICAL
1. 13MC451 Project Work ( Phase II) 0 0 24 12
CREDITS 0 0 24 12
Total No. of Credits : 78
ELECTIVES
SL.
NO.
COURSE
CODE
COURSE TITLE L T P C
1. 13MC401
Formal models of software systems 3 0 0 3
2. 13MC402
Performance Evaluation of Computer Systems 3 0 0 3
3. 13MC403
Model Checking and Program Verification 3 0 0 3
4. 13MC404
Sensing Techniques and Sensors 3 0 0 3
5. 13MI403
Internet of Things
(Common to ME CSE &MTech IT)
3 0 0 3
6. 13MI408
Video Analytics
(Common to ME CSE &MTech IT)
3 0 0 3
7. 13MC405
Reconfigurable Computing 3 0 0 3
8. 13MI409
Wireless Sensor Networks
(Common to ME CSE &MTech IT)
3 0 0 3
9. 13MC406
Language Technologies 3 0 0 3
10. 13MC407
Energy Aware Computing 3 0 0 3
26
(Common to ME CSE &MTech IT)
11. 13MC408
Information Storage Management 3 0 0 3
12. 13MC409
Software Process and Project Management 3 0 0 3
13.
13MC410 Image Processing and Analysis 3 0 2 4
14.
13MC411 Data Mining Techniques 3 0 2 4
15.
13MC412 Parallel Algorithms 3 0 2 4
16.
13MC413 Probabilistic Reasoning Systems 3 0 2 4
17.
13MC414 Data Analysis and Business Intelligence 3 0 2 4
18.
13MC415 Embedded Software Development 3 0 2 4
19.
13MC416 Mobile Application Development 3 0 2 4
20.
13MC417 Bio inspired Computing 3 0 2 4
21.
13MC418 Medical Image Processing 3 0 2 4
22.
13MC419 Enterprise Application Integration 3 0 2 4
23.
13MC420 Concurrency Models 3 0 2 4
REGULATIONS MEPCO R2013 (PART TIME)
CURRICULUM (I TO VI SEMESTER)
I SEMESTER
SL.
NO.
COURSE
CODE
COURSE TITLE L T P C
THEORY
1. 13MA174 Mathematics and Statistics for Computer
Science
3 1 0 4
2. 13MC101 Advanced Data Structures & Algorithms
(Common to ME CSE & MTech IT)
3 0 0
3. 13MC102 Design and Management of Computer
Networks
3 0 2 4
PRACTICAL
4. 13MC151 Advanced Data Structures Laboratory
(Common to ME CSE & MTech IT)
0 0 3 2
TOTAL 9 1 5 13
II SEMESTER
SL.
NO.
COURSE
CODE
COURSE TITLE L T P C
THEORY
1. 13MC201 Advanced Operating Systems 3 0 0 3
2. 13MC202 Machine Learning Techniques 3 0 2 4
3. Elective I 3 0 0 3
PRACTICAL
27
4. 13MC251 Advanced Operating Systems Laboratory 0 0 3 2
TOTAL 9 0 5 12
III SEMESTER
SL.
NO.
COURSE
CODE
COURSE TITLE L T P C
THEORY
1. 13MC103 Software Architectures 3 0 0 3
2. 13MC104 Advanced Databases 3 0 0 3
3. 13MC105 Multicore Architectures 3 0 0 3
PRACTICAL
4. 13MC152 Advanced Databases Laboratory 0 0 3 2
TOTAL 9 0 3 11
IV SEMESTER
SL.
NO.
COURSE
CODE
COURSE TITLE L T P C
THEORY
1.
13MI202 Cloud Computing Technologies
(Common to ME CSE & MTech IT)
3 0 0 3
2.
13MI204 Big Data Analytics
(Common to ME CSE & MTech IT)
3 0 0 3
3. Elective II 3 0 0 3
PRACTICAL
4.
13MI252 Cloud Computing Laboratory
(Common to ME CSE & MTech IT)
0 0 3 2
5. 13MC252 Technical Seminar * 0 0 2 1
TOTAL 9 0 5 12
* Internal Assessment Only
V SEMESTER
SL.
NO.
COURSE
CODE
COURSE TITLE L T P C
THEORY
1. 13MC301 Parallel Programming Paradigms 3 0 2 4
2. Elective III 3 0 2 4
3. Elective IV 3 0 2 4
PRACTICAL
4. 13MC351 Project Work (Phase I) 0 0 12 6
TOTAL 9 0 18 18
VI SEMESTER
SL.
NO.
COURSE
CODE
COURSE TITLE L T P C
PRACTICAL
1. 13MC451 Project Work ( Phase II) 0 0 24 12
TOTAL 0 0 24 12
28
Total No. of Credits : 78
ELECTIVES
SL.
NO.
COURSE
CODE
COURSE TITLE L T P C
1. 13MC401 Formal models of software systems 3 0 0 3
2. 13MC402 Performance Evaluation of Computer Systems 3 0 0 3
3. 13MC403 Model Checking and Program Verification 3 0 0 3
4. 13MC404 Sensing Techniques and Sensors 3 0 0 3
5.
13MI403 Internet of Things
(Common to ME CSE & MTech IT)
3 0 0 3
6.
13MI408 Video Analytics
(Common to ME CSE & MTech IT)
3 0 0 3
7. 13MC405 Reconfigurable Computing 3 0 0 3
8.
13MI409 Wireless Sensor Networks
(Common to ME CSE & MTech IT)
3 0 0 3
9. 13MC406 Language Technologies 3 0 0 3
10.
13MC407 Energy Aware Computing
(Common to ME CSE & MTech IT)
3 0 0 3
11. 13MC408 Information Storage Management 3 0 0 3
12. 13MC409 Software Process and Project Management 3 0 0 3
13. 13MC410 Image Processing and Analysis 3 0 2 4
14. 13MC411 Data Mining Techniques 3 0 2 4
15. 13MC412 Parallel Algorithms 3 0 2 4
16. 13MC413 Probabilistic Reasoning Systems 3 0 2 4
17. 13MC414 Data Analysis and Business Intelligence 3 0 2 4
18. 13MC415 Embedded Software Development 3 0 2 4
19. 13MC416 Mobile Application Development 3 0 2 4
20. 13MC417 Bio inspired Computing 3 0 2 4
21. 13MC418 Medical Image Processing 3 0 2 4
22. 13MC419 Enterprise Application Integration 3 0 2 4
23. 13MC420 Concurrency Models 3 0 2 4
I SEMESTER
13MA174:MATHEMATICS AND STATISTICS FOR COMPUTER
SCIENCE
L T P C
3 1 0 4
Course Objectives:
To understand propositional and predicate logics and their applications
To understand lambda calculus and functional programming
To understand graph structures and their applications
To provide information about Estimation theory, Correlation, Regression and Testing of
29
hypothesis
Course Outcomes:
Students are able
To gain the knowledge of proof techniques in logic
To apply lambda calculus
To explain logic programming and functional programming principles
To apply sequential structures, tree structures, and graph structures
To acquire the concept of Estimation theory
To do the testing of hypothesis which will be useful in solving Engineering problems
UNIT I LOGIC AND LOGIC PROGRAMMING 9+3
Propositional Logic Syntax Interpretations and models Deduction theorems Normal forms
Inference rules SAT solvers Predicate logic Syntax Proof theory Semantics of predicate
logic Undecidability of predicate logic inferences in first-order logic Logic programming
definite programs SLD resolution Normal programs SLDNF resolution Introduction to
prolog.
UNIT II LAMBDA CALCULUS AND FUNCTIONAL PROGRAMMING 9+3
Lambda notation for functions syntax Curried functions Parametric polymorphism Lambda
reduction Alpha reduction Beta reduction Beta abstraction Extensionality theorem Delta
reduction reduction strategies Normal forms Church-Rosser Theorems Pure lambda
calculus constants Arithmetic conditionals iteration recursion Introduction to Functional
programming.
UNIT III GRAPH STRUCTURES 9+3
Graph representations Regular graph structures Random graphs connectivity cycles
Graph coloring: chromatic number, chromatic partitioning, chromatic polynomial Cliques, Vertex
Covers, Independent sets Spanning Trees Fundamental circuits Spanning trees in a weighted
graph - Network flows.
UNIT IV ESTIMATION THEORY 9+3
Unbiased estimators Method of moments Maximum likelihood estimation Curve fitting by
principles of least squares Regression lines.
UNIT V TESTING OF HYPOTHESIS 9+3
Sampling distributions Type I and II errors Test based on normal, t, F and chi-square
distributions for testing of Mean, Variance and Proportions Tests for independence of Attributes
and Goodness of fit.
TOTAL: 60 PERIODS
REFERENCE BOOKS:
1. UweSchoning, Logic for Computer Scientists, Birkhauser, 2008.
2. M.Ben-Ari, Mathematical logic for computer science, Springer, second edition, 2003.
3. John Harrison, Handbook of Practical Logic and Automated Reasoning, Cambridge
University Press, 2009.
4. Greg Michaelson, An introduction to functional programming through lambda calculus,
Dover Publications, 2011.
30
5. Kenneth Slonneger, and Barry Kurtz, Formal syntax and semantics of programming
languages, Addison Wesley, 1995.
6. Kennth H. Rosen, Discrete Mathematics and its applications, Tata McGraw Hill, Seventh
Edition, 2011.
7. Gupta S.C. and Kapoor V.K., Fundamentals of Mathematical Statistics, Sultan & Sons,
2011.
8. NarsinghDeo, Graph Theory with Applications to Engineering and Computer Science,
Prentice-Hall of India, 1995.
13MC101: ADVANCED DATA STRUCTURES AND ALGORITHMS L T P C
(Common to ME CSE / M.Tech IT) 3 0 0 3
Course Objectives:
To recall elementary data structures and the significance of writing efficient algorithms
To study data structures for concurrency
To study advanced data structures such as search trees, hash tables, heaps and operations
on them
To expose various distributed data structures
To understand the principles of efficient algorithm design and learn various advanced
algorithms
Course Outcomes:
Implement and apply concurrent linked lists, stacks, and queues
Perform operations on search trees and hash tables
Perform operations on different types of heap
Implement and apply data structures for strings
Implement advanced concurrent structures
Explain design techniques for algorithms and advanced algorithm
UNIT I DATA STRUCTURES AND CONCURRENCY 9
Review of algorithm design and analysis review of elementary data structures data structures
and concurrency locking linked lists coarse-grained synchronization fine-grained
synchronization lazy synchronization non-blocking synchronization concurrent queues
bounded partial queues unbounded lock-free queues dual data structures concurrent stacks
elimination backoff stack
UNIT II SEARCH TREES, HASH TABLES AND STRINGS 9
Search Trees Weight Balanced trees Red Black trees Finger Trees and level linking Skip
lists joining and splitting balanced search trees Hash trees extendible hashing- Strings
tries and compressed tries dictionaries suffix trees suffix arrays.
UNIT III HEAPS 9
Heaps - Array-Based Heaps - Heap-Ordered Trees and Half-Ordered Trees - Leftist Heaps Skew
Heaps - Binomial Heaps - Changing Keys in Heaps - Fibonacci Heaps - Double-Ended Heap
structures multidimensional heaps
UNIT IV ADVANCED CONCURRENT STRUCTURES 9
31
Concurrent hashing closed-address hash sets lock-free hash sets open-addressed hash sets
lock-based concurrent skip lists lock-free concurrent skip lists concurrent priority queues
bounded priority queue unbounded priority queue concurrent heap skip list based
unbounded priority queues.
UNIT V ADVANCED ALGORITHMS 9
Introduction to Approximation algorithms job scheduling on a single machine knapsack
problem minimizing weighted sum of completion time on a single machine MAX SAT and MAX
CUT. Introduction to Randomized algorithms min cut. Introduction to Parallel algorithms
parallel sorting algorithms.
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. M. Herlihy and N. Shavit, The Art of Multiprocessor Programming, Morgan Kaufmann,
2012.
2. Peter Brass, Advanced Data Structures, Cambridge University Press, 2008.
3. A. V. Aho, J. E. Hopcroft, and J. D. Ullman, The Design and Analysis of Computer
Algorithms, Addison-Wesley, 1975.
4. Gavpai, Data Structures and Algorithms Concepts, techniques and Applications, First
Edition, Tata McGraw-Hill, 2008.
5. Edited by S.K. Chang, Data Structures and Algorithms Series of Software Engineering
and Knowledge Engineering, Vol. 13, World Scientific Publishing, 2003.
6. Jon Kleinberg, "Algorithm Design", Addison-Wesley, 2013.
7. David P. Williamson, David B. Shmoys, The Design of Approximation Algorithms,
Cambridge University Press, 2011.
8. Rajeev Motwani and PrabhakarRaghavan, Randomized Algorithms, Cambridge University
Press, 1995.
9. Michael J. Quinn, Parallel Computing: Theory & Practice, Tata McGraw Hill Edition, 2003.
10. AnanthGrama, Anshul Gupta, et al., Introduction to Parallel Computing, Second Edition,
Pearson Education, 2003.
Web References:
1. http://www.geeksforgeeks.org/pattern-searching-set-8-suffix-tree-introduction/
2. http://iamwww.unibe.ch/~wenger/DA/SkipList/
3. http://www.cs.au.dk/~gerth/slides/soda98.pdf
4. http://www.cs.sunysb.edu/~algorith/files/suffix-trees.shtml
5. http://pages.cs.wisc.edu/~shuchi/courses/880-S07/scribe-notes/lecture20.pdf
13MC102: DESIGN AND MANAGEMENT OF COMPUTER NETWORKS L T P C
3 0 2 4
Course Objectives:
To collect the requirements associated with the network management
To study how to gather and analyse the requirements
To study the flow characteristics and its model
To understand how the network architecture can be built
32
To study the issues in the design of the network
Course Outcomes:
Gather the requirements related to the functioning of the netwok
Analyze the network requirements for further planning
Analyze the behaviour of the flow and model it
Draw the architecture of the network and identify the operations of each constituent in it
Design the network by integrating the functional components in it
Design the protocol associated with the functioning of each component
UNIT I INTRODUCTION TO NETWORK MANAGEMENT 9
Overview of Analysis, Architecture and Design Process - System Methodology, Service
methodology, Service Description - Service characteristics - Performance Characteristics - Network
supportability Requirements: User Requirements, Application Requirements, Device
Requirements, Network Requirements, Other Requirements, Requirement specification and map
UNIT II REQUIREMENTS ANALYSIS 9
Requirement Analysis Process Gathering and Listing Requirements- Developing service metrics
Characterizing behaviour Developing RMA requirements Developing delay Requirements -
Developing capacity Requirements - Developing supplemental performance Requirements
Requirements mapping Developing the requirements specification
UNIT III FLOW ANALYSIS 9
Individual and Composite Flows Critical Flows - Identifying and developing flows Data sources
and sinks Flow models Flow prioritization Flow specification algorithms Example
Applications of Flow Analysis
UNIT IV NETWORK ARCHITECTURE 9
Architecture and design Component Architectures Reference Architecture Architecture Models
System and Network Architecture Addressing and Routing Architecture Addressing and
Routing Fundamentals Addressing Mechanisms Addressing Strategies Routing Strategies
Network Management Architecture Network Management Mechanisms Performance Architecture
Performance Mechanisms Security and Privacy Architecture Planning security and privacy
Mechanisms
UNIT V NETWORK DESIGN 9
Design Concepts Design Process - Network Layout Design Traceability Design Metrics
Logical Network Design Topology Design Bridging, Switching and Routing Protocols- Physical
Network Design Selecting Technologies and Devices for Campus and Enterprise Networks
Optimizing Network Design
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. Network Analysis, Architecture, and Design By James D. McCabe, Morgan Kaufmann, Third
Edition, 2007.ISBN-13: 978-0123704801
2. Computer Networks: A Systems Approach by Larry L. Peterson, Bruce S. Davie -2007,
Elsevier Inc.
3. Top-down Network Design: [a Systems Analysis Approach to Enterprise Network Design]
By Priscilla Oppenheimer, Cisco Press , 3rd Edition, ISBN-13: 978-1-58720- 283-4 ISBN-
33
10: 1-58720-283-2
4. Integrated Management of Networked Systems: Concepts, Architectures, and Their
Operational Application (The Morgan Kaufmann Series in Networking), Heinz-
GerdHegering, Sebastian Abeck, and Bernhard Neumair, 1999.
5. Network Design and Management by Steven T.Karris, Orchard publications, Second
edition, Copyright 2009, ISBN 978-1-934404-15-7
6. Network Design, Management and Technical Perspective, Teresa C. Mann-Rubinson and
KornelTerplan, CRC Press, 1999
7. Ethernet Networks-Design, Implementation, Operation and Management by Gilbert Held,
John Wiley and sons, Fourth Edition
8. James Kurose and Keith Ross, Computer Networking: A Top-Down Approach Featuring the
Internet, 1999
Web References:
1. http://www.ietf.org/
2. http://www.inetdaemon.com
13MC103: SOFTWARE ARCHITECTURES L T P C
3 0 0 3
Course Objectives:
To Understand the architectural requirements
To Identify the architectural structures
To Develop the architectural documentation
To Generate the architectural alternatives
To Evaluate the architecture against the drivers
Course Outcomes:
Explain the key architectural drivers
Explain the influence of architecture on business and technical activities
Identify key architectural structures
Adopt good practices for documenting the architecture
Develop alternative architectures for a given problem
Explain how to use formal languages to specify architecture
Evaluate the architecture against the drivers
Describe the recent trends in software architecture
UNIT I ARCHITECTURAL DRIVERS 9
Introduction Standard Definitions of Software Architecture Architectural structures Influence
of software architecture on organization Architecture Business Cycle Functional requirements
Technical constraints Quality Attributes Quality Attribute Workshop (QAW) Documenting
Quality Attributes Six part scenarios
UNIT II ARCHITECTURAL VIEWS AND DOCUMENTATION 9
Introduction Standard Definitions for views Structures and views- Perspectives: Static,
dynamic and physical and the accompanying views Representing views-available notations
Good practices in documentation Documenting the Views using UML Merits and Demerits of
34
using visual languages Need for formal languages - Architectural Description Languages ACME
UNIT III ARCHITECTURAL STYLES 9
Introduction Data flow styles Call-return styles Shared Information styles Event styles
Case studies for each style
UNIT IV ARCHITECTURAL DESIGN 9
Approaches for architectural design System decomposition Attributes driven design
Architecting for specific quality attributes Performance, Availability Security Architectural
conformance
UNIT V ARCHITECTURE EVALUATION AND SOME SPECIAL TOPICS 9
Need for evaluation Scenario based evaluation against the drivers ATAM and its variations
Case studies in architectural evaluations SOA and Web services Cloud Computing Adaptive
structures
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. Len Bass, Paul Clements, and Rick Kazman, Software Architectures Principles and
Practices, 2n Edition, Addison-Wesley, 2003.
2. Anthony J Lattanze, Architecting Software Intensive System. A Practitioner's Guide,
Auerbach Publications, 2010.
3. Paul Clements, Felix Bachmann, Len Bass, David Garlan, James Ivers, Reed Little, Paulo
Merson, Robert Nord, and Judith Stafford, Documenting Software Architectures. Views
and Beyond, 2
nd
Edition, Addison-Wesley, 2010.
4. Paul Clements, Rick Kazman, and Mark Klein, Evaluating software architectures:
Methods and case studies., Addison-Wesley, 2001.
5. David Garlan and Mary Shaw, Software architecture: Perspectives on an emerging
discipline, Prentice Hall, 1996.
6. RajkumarBuyya, James Broberg, and AndrzejGoscinski, Cloud Computing. Principles
and Paradigms, John Wiley & Sons, 2011
7. Mark Hansen, SOA Using Java Web Services, Prentice Hall, 2007
8. David Garlan, Bradley Schmerl, and Shang-Wen Cheng, Software Architecture-Based
Self-Adaptation, 31-56. Mieso K Denko, Laurence Tianruo Yang, and Yan Zang (eds.),
Autonomic Computing and Networking. Springer Verlag, 2009.
WEB REFERENCES:
1. http://www.sei.cmu.edu/architecture/
2. http://msdn.microsoft.com/en-us/library/ee658093.aspx
3. http://kti.tugraz.at/staff/denis/courses/sa/index.html
4. http://www.codingthearchitecture.com/pages/book/software-architecture-document-
guidelines.html
13MC104: ADVANCED DATABASES L T P C
3 0 0 3
Course Objectives:
To learn the modeling and design of databases.
35
To acquire knowledge on parallel and distributed databases and its applications.
To study the usage and applications of Object Oriented database
To understand the principles of intelligent databases.
To understand the usage of advanced data models.
To learn emerging databases such as XML, Cloud and Big Data.
To acquire inquisitive attitude towards research topics in databases.
Course Outcomes:
Select the appropriate high performance database like parallel and distributed database
Model and represent the real world data using object oriented database
Design a semantic based database like active and deductive databases to meaningful
data access
Embed the rule set in the database to implement intelligent databases like multimedia
and spatial databases
Represent the data using XML database for better interoperability
Handle Big data and store in a transparent manner in the cloud
To solve the issues related to the data storage and retrieval
UNIT I PARALLEL AND DISTRIBUTED DATABASES 9
Database System Architectures: Centralized and Client-Server Architectures Server System
Architectures Parallel Systems- Distributed Systems Parallel Databases: I/O Parallelism
Inter and Intra Query Parallelism Inter and Intra operation Parallelism Design of Parallel
Systems- Distributed Database Concepts - Distributed Data Storage Distributed Transactions
Commit Protocols Concurrency Control Distributed Query Processing Case Studies
UNIT II OBJECT AND OBJECT RELATIONAL DATABASES 9
Concepts for Object Databases: Object Identity Object structure Type Constructors
Encapsulation of Operations Methods Persistence Type and Class Hierarchies Inheritance
Complex Objects Object Database Standards, Languages and Design: ODMG Model ODL
OQL Object Relational and Extended Relational Systems: Object Relational features in
SQL/Oracle Case Studies.
UNIT III INTELLIGENT DATABASES 9
Active Databases: Syntax and Semantics (Starburst, Oracle, DB2)- Taxonomy- Applications-
Design Principles for Active Rules- Temporal Databases: Overview of Temporal Databases-
TSQL2- Deductive Databases: Logic of Query Languages Datalog- Recursive Rules-Syntax and
Semantics of Datalog Languages- Implementation of Rules and Recursion- Recursive Queries in
SQL- Spatial Databases- Spatial Data Types- Spatial Relationships- Spatial Data Structures-
Spatial Access Methods- Spatial DB Implementation.
UNIT IV ADVANCED DATA MODELS 9
Mobile Databases: Location and Handoff Management - Effect of Mobility on Data Management -
Location Dependent Data Distribution - Mobile Transaction Models -Concurrency Control -
Transaction Commit Protocols- Multimedia Databases- Information Retrieval- Data Warehousing-
Data Mining- Text Mining.
UNIT V EMERGING TECHNOLOGIES 9
XML Databases: XML-Related Technologies-XML Schema- XML Query Languages- Storing XML in
36
Databases-XML and SQL- Native XML Databases- Web Databases- Geographic Information
Systems- Biological Data Management- Cloud Based Databases: Data Storage Systems on the
Cloud- Cloud Storage Architectures-Cloud Data Models-Introduction to Big Data-Storage-
Analysis
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. R. Elmasri, S.B. Navathe, Fundamentals of Database Systems, Fifth Edition, Pearson
Education/Addison Wesley, 2007.
2. Thomas Cannolly and Carolyn Begg, Database Systems, A Practical Approach to Design,
Implementation and Management, Third Edition, Pearson Education, 2007.
3. Henry F Korth, Abraham Silberschatz, S. Sudharshan, Database System Concepts,
Fifth Edition, McGraw Hill, 2006.
4. C.J.Date, A.Kannan and S.Swamynathan, An Introduction to Database Systems, Eighth
Edition, Pearson Education, 2006.
5. Raghu Ramakrishnan, Johannes Gehrke, Database Management Systems, McGraw
Hill, Third Edition 2004.
6. Carlo Zaniolo, Stefano Ceri, Christos Faloustsos, R.T.Snodgrass, V.S.Subrahmanian,
Advanced Database Systems, Morgan Kaufman, 1997.
7. N.TamerOzsu, Patrick Valduriez, Principles Of Distributed Database Systems,
Prentice Hall Internatl Inc., 1999.
8. Vijay Kumar, Mobile Database systems, Wiley-interScience, 2006.
13MC105: MULTICORE ARCHITECTURES L T P C
3 0 0 3
Course Objectives:
To understand the recent trends in the field of Computer Architecture and identify
performance related parameters
To appreciate the need for parallel processing
To expose the students to the problems related to multiprocessing
To understand the different types of multicore architectures
To expose the students to warehouse-scale and embedded architectures
Course Outcomes:
Identify the limitations of ILP and the need for multicore architectures
Discuss the issues related to multiprocessing and suggest solutions
Point out the salient features of different multicore architectures and how they exploit
parallelism
Critically analyze the different types of inter connection networks
Analyse the architecture of GPUs, warehouse-scale computers and embedded processors
UNIT I FUNDAMENTALS OF QUANTITATIVE DESIGN AND ANALYSIS 9
Classes of Computers Trends in Technology, Power, Energy and Cost Dependability
Measuring, Reporting and Summarizing Performance Quantitative Principles of Computer
37
Design Classes of Parallelism - ILP, DLP, TLP and RLP - Multithreading - SMT and CMP
Architectures Limitations of Single Core Processors - The Multicore era Case Studies of
Multicore Architectures.
UNIT II DLP IN VECTOR, SIMD AND GPU ARCHITECTURES 9
Vector Architecture - SIMD Instruction Set Extensions for Multimedia Graphics Processing
Units - Detecting and Enhancing Loop Level Parallelism - Case Studies.
UNIT III TLP AND MULTIPROCESSORS 9
Symmetric and Distributed Shared Memory Architectures Cache Coherence Issues -
Performance Issues Synchronization Issues Models of Memory Consistency - Interconnection
Networks Buses, Crossbar and Multi-stage Interconnection Networks.
UNIT IV RLP AND DLP IN WAREHOUSE-SCALE ARCHITECTURES
9
Programming Models and Workloads for Warehouse-Scale Computers Architectures for
Warehouse-Scale Computing Physical Infrastructure and Costs Cloud Computing Case
Studies.
UNIT V ARCHITECTURES FOR EMBEDDED SYSTEMS 9
Features and Requirements of Embedded Systems Signal Processing and Embedded
Applications The Digital Signal Processor Embedded Multiprocessors - Case Studies.
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. John L. Hennessey and David A. Patterson, Computer Architecture A Quantitative
Approach, Morgan Kaufmann / Elsevier, 5
th
edition, 2012.
2. Kai Hwang, Advanced Computer Architecture, Tata McGraw-Hill Education, 2003
3. Richard Y. Kain, Advanced Computer Architecture a Systems Design Approach,
Prentice Hall, 2011.
4. David E. Culler, Jaswinder Pal Singh, Parallel Computing Architecture : A Hardware/
Software Approach , Morgan Kaufmann / Elsevier, 1997.
Web References:
1. http://www.cs.cmu.edu/~fp/courses/15213-s07/lectures/27-multicore.pdf
2. http://rolfed.com/nehalem/nehalemPaper.pdf
3. http://accel.cs.vt.edu/files/lecture2.pdf
4. http://web.njit.edu/~rlopes/12.1.0%20-%20Cellproc-PS3.pdf
5. http://cs.nyu.edu/~lerner/spring10/projects/multicore-niagara.pdf
13MC151: ADVANCED DATA STRUCTURES LABORATORY L T P C
(Common to ME CSE / M.Tech IT) 0 0 3 2
Course Objectives:
To learn implementation of data structures for concurrency
To learn implementation of advanced data structures such as search trees, hash tables,
heaps and operations on them
38
To learn to implement advanced concurrent data structures
To learn to apply principles of efficient algorithm design and learn various advanced
algorithms
Course Outcomes:
Implement and apply concurrent linked lists, stacks, and queues
Perform operations on search trees and hash tables
Perform operations on different types of heaps
Implement and apply data structures for strings
Implement advanced concurrent structures
Apply design techniques for algorithms and advanced algorithms
SYLLABUS FOR THE LAB:
Each student has to work individually on assigned lab exercises. Lab sessions could be
scheduled as one contiguous three-hour session per week. The students have to complete a
minimum of 12 exercises. It is recommended that all implementations are carried out in Java.
If C or C++ has to be used, then the threads library will be required for concurrency.
Implementation and applications of classic linear data structures, namely, linked lists,
queues, and stacks.
Implementation of various locking and synchronization mechanisms for concurrent linked
lists, concurrent queues, and concurrent stacks.
Implementation of weight balanced search trees and skip lists.
Implantation of suffix trees and pattern matching
Implementation of various heap structures.
Implementation of concurrent hashing, concurrent skip lists, and concurrent priority
queues.
Implementation of approximation and randomized algorithms.
Implementation of parallel sorting algorithms.
Developing an application involving concurrency and data structures.
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. M. Herlihy and N. Shavit, The Art of Multiprocessor Programming, Morgan Kaufmann,
2012.
2. Peter Brass, Advanced Data Structures, Cambridge University Press, 2008.
3. A. V. Aho, J. E. Hopcroft, and J. D. Ullman, The Design and Analysis of Computer
Algorithms, Addison-Wesley, 1975.
4. Gavpai, Data Structures and Algorithms Concepts, techniques and Applications, First
Edition, Tata McGraw-Hill, 2008.
5. Edited by S.K. Chang, Data Structures and Algorithms Series of Software Engineering
and Knowledge Engineering, Vol. 13, World Scientific Publishing, 2003.
6. Jon Kleinberg, "Algorithm Design", Addison-Wesley, 2013.
7. David P. Williamson, David B. Shmoys, The Design of Approximation Algorithms,
Cambridge University Press, 2011.
8. Rajeev Motwani and PrabhakarRaghavan, Randomized Algorithms, Cambridge
39
University Press, 1995.
9. Michael J. Quinn, Parallel Computing: Theory & Practice, Tata McGraw Hill Edition,
2003.
10. AnanthGrama, Anshul Gupta, et al., Introduction to Parallel Computing, Second Edition,
Pearson Education, 2003.
WEB REFERENCES:
1. http://www.w3schools.in/c-programming-language
2. http://www.geeksforgeeks.org/pattern-searching-set-8-suffix-tree-introduction/
3. http://iamwww.unibe.ch/~wenger/DA/SkipList/
4. http://www.cs.au.dk/~gerth/slides/soda98.pdf
5. http://www.cs.sunysb.edu/~algorith/files/suffix-trees.shtml
6. http://pages.cs.wisc.edu/~shuchi/courses/880-S07/scribe-notes/lecture20.pdf
List of Sample Exercises
1. AfileconsistsofalistofCDtitles withinformationsuchascategory(in alphanumericform
maximumof 25 characters)andtitle(inalphanumericformmaximum of 25 characters
characters).Duplicatesentriesare allowed. Example Categories are: Education,
Entertainment, Examinations, Soft skill, Games etc.
Designasystemtogetnewentries toadd, search for an entry, delete
theexistingentriesandviewthetitles. Thesystemdoesnotknowthe numberof
titlesinadvance. The system may keep the information either in order or unordered.
Compare the efficiency of the above two approaches.
2. An electronics goods dealer has 50 different types of item and for each item he has a
maximum of 5 branded company products for sale. Read and store the monthly sales
(day wise) of the shop in a multi list and produce the following reports.
List the day wise total sales amount of all goods
List the weekly sale details of refrigerator.
List the monthly sale details of all LG brand electronic good
Make the list as empty at the end of seventh day of the week after taking
appropriate back up.
3. Construct concurrent bi-stack in a single array and perform the following operation
for string manipulation such as:
i) Search for a character and Replace it by a new one if available
ii) Reverse a String
iii) Test for palindrome
iv) Count the occurrences of the given character
4. A deque is a data structure consisting of a list of items, on which the following
operations are possible:
Push(X,D): Insert item X on the front end of the deque D.
Pop(D): Remove the front item from the deque D and return it
Inject(X,D): Insert an item X on the rear end of the deque D.
Eject(D): Remove the rear item from the deque D and return it.
40
Implement the above concurrent double ended queue.
5. Suppose that an advertising company maintain a database and needs to generate
mailing labels for certain constituencies. A typical request might require sending out a
mailing to people who are between the ages of 34 and 49and whose annual income is
between $100000 and $200000.This problem is known as a two dimensional range
query. To solve such range queries a two dimensional search tree namely 2-D tree can
be used which has the simple property that branching on odd levels is done with
respect to the first key and branching on even levels is done with respect to the
second key. Implement a 2-D tree with company database consist of the following
fields such mail-ID, Age, Gender, Annual Income and Occupation.
6. Using weight balanced search tree construct a Telephone directory with the
Information such as: Phone Number, Name and address then perform the following
a)Search for a phone number and print the customer name and address
b) Remove a Phone number from the directory
c) Change the address of the customer whose phone number is given.
d) Print the content of the directory
7. Construct a Red-Black tree with the database containing Book detail such access
Number, Title, Author name, Department and price. Perform the following operations
i) Search for a book based on Book title
ii) Add a new book entry into the database
iii)Remove the lost book entry from the database
Note: Arrange the list of records based an book title to improve the performance of the
frequent search operations.
8. The details of employees (Emp.Id, Name, Department and Total Years of experience) of
a company are to be maintained. The list indicates both alphabetical ordering of names,
ascending order of Emp.Id Number and alphabetical ordering of department names.
Perform the following by using Skip List structure:
Insert a new employee detail in the appropriate position
Remove an employee detail where Emp.Id is given
Find an employee detail whose ID is given.
Find employee information whose name in a particular department is
given.
List all employee detail in order of their name.
9. Construct a Suffix Tree data structure to construct a Telephone directory Telephone
directory with the Information such as: Phone Number, Name and address then
perform the following operation
a. Insert a new customer information into the directory
b. Disable a connection and Delete that phone number from the
directory
c. Print all customer addresses that starts with name AN*.
d. Print all customer addresses and phone numbers whose name starts
41
with alphabets A-E.
10. Construct double ended priority queue using Min-Max heaps and perform the following
a) Find 3
rd
minimum
b) Delete an item(with random priority)
c) Delete maximum element
d) Heap sort in descending order
e) Modify the priority of an item
11. Online dictionary implementation using Hashing
Implement a dictionary which contains the meaning of different words. Both the word
and the meaning can be in the same language. Your program should read a word and
should give the meaning. If the word is a new one (not available in the dictionary) then
include the word into its correct position with its meaning.
Implement the same problem using concurrent Hashing technique.
12. Implementation of Approximation algorithm : Solve the 0-1 Knapsack problem
Given a knapsack with maximum weight capacity C and a set S consisting of n items,
each item i with weight w
i
and profit p
i
(all w
i
, p
i
and W are integer values). The
problem is to pack the knapsackto achieve maximum total profit of packed items with
items total weight less than or equal to C.
13. Implementation of randomized algorithm: Find the solution for the Project selection
problem.
In the project selection problem, there are n projects and m equipments. Each project
pi yields revenue r(pi)and each equipment qi costs c(qi)to purchase. Each project
requires a number of equipments and each equipment can be shared by several
projects. The problem is to determine which projects and equipments should be
selected and purchased respectively, so that the profit is maximized.
14. Implement the following parallel sorting and compare the performance those
algorithms.
i) parallel Quick sort
ii) Parallel merge sort
iii) Batchers Bitonic sort
Note:
Batchers Bitonicsort is a parallel sorting algorithm whose main operation is a technique
for merging two bitonic sequences. A bitonic sequence is the concatenation of an
ascending and a descending sequence. For example 2, 4, 6, 8, 23, 8, 5, 3, 0 is a
bitonic sequences.
13MC152: ADVANCED DATABASES LABORATORY L T P C
0 0 3 2
Course Objectives:
To work with various databases
To work with Weka tool
Course Outcomes:
42
Create various databases
Design Classification and Clustering algorithms
SYLLABUS FOR THE LAB:
Create a relational database using B+ tree structure. Implement the operations insert,
modify, delete and search operations with query parser.
Implement query optimizer by accessing the meta data.
Create a distributed database and run various queries. Use stored procedures.
Queries using Object Oriented Database.
Parallel Database Access from a Programming Language
- Access database from a programming language such as Java and Python.
Active Databases
-Create an Active Database including Triggers and assertions.
Deductive Database
-Create a knowledge database with facts and extract data using rules.
XML
-Create an XML Schema for the Company Database.
Weka
-Work with Weka tool classification and clustering algorithms.
Building Web Applications
- Build Web applications using Java servlet API.
TOTAL: 45 PERIODS
WEB REFERENCES:
1. http://www.db-book.com
2. http://infolab.stanford.edu/~ullman/dscb.html
3. http://www.cs.wisc.edu/~dbbook
List of Sample Exercises
1 B+ Tree
Scenario: Consider a relation consisting of the following fields.
Student(sid,sname,login,age,gpa)
Answer the following queries:
1. Get all records with search key greater than 38.
2. Insert a record with search key 109 into the tree
3. Delete the record with search key 81 from the tree.
4. Modify the record with search key 60 in the tree.
2 Query Optimizer
Consider the following relational Schema and SQL Query:
Suppliers(sid: integer, sname: char(20), city: char(20)
Supply(sid: integer, pid: integer)
Parts(pid:integer, pname: char(20), price:real)
SELECT S.sname, P.pname
FROM Suppliers S, Parts P, Supply Y
43
WHERE S.sid = Y.sid AND Y.pid =P.pid AND
S.city = Madison AND P.price<= 1000
1. What information about these relations does the query optimizer need to select
a good query execution plan for the given query?
2. How many different join orders, assuming that cross-products are disallowed,
does a System R style Query optimizer consider when deciding how to
process the given query ?
3. Create the indexes needed in processing this query?
4. Experiment how does adding DISTINCT to the SELECT clause affect the plans
produced
5. Experiment how does adding ORDER BY sname to the query affect the plans
produced
6. Experiment how does adding GROUP BY to the query affect the plans produced
3 Distributed Database
Scenario: Consider a distributed database for a bookstore with 4 sites called S1, S2,
S3 and S4.
Consider the following relations:
Books ( ISBN, primaryAuthor, topic, totalStock, price )
BookStore ( storeNo, city, state, zip, inventoryValue )
Stock ( storeNo, ISBN, Qty )
totalStock is the total number of books in stock and inventoryValue is the total
inventory value for the store in dollars.
Consider that Books are fragmented by price amounts into:
F1: Books: price up to $20
F2: Books: price from $20.01 to $50
F3: Books: price from $50.01 to $100
F4: Books: price $100.01 and above
Similarly, BookStores are divided by ZIP codes into:
S1: Bookstore: Zip up to 25000
S2: Bookstore: Zip 25001 to 50000
S3: Bookstore: Zip 50001 to 75000
S4: Bookstore: Zip 75001 to 99999
Task 1: Write SQL query for the following
1. Insert and Display details in each table.
2. Find the total number of books in stock where price is between $15 and $55.
3. Update the bookprice of bookNo=1234 from $45 to $55 at site S3.
4. Find total number of book at site S2.
Task 2: Implement deadlock detection algorithm for distributed database using
wait-for graph and test with the following information.
Consider five transactions T1, T2, T3, T4 and T5 with
44
T1 initiated at site S1 and spawning an agent at site S2
T2 initiated at site S3 and spawning an agent at site S1
T3 initiated at site S1 and spawning an agent at site S3
T4 initiated at site S2 and spawning an agent at site S3
T5 initiated at site S3
The locking information for these transactions is shown in the following table
Transactions Data items locked
by transactions
Data items transaction is
waiting for
Site involved in
operations
T1 X1 X8 S1
T1 X6 X2 S2
T2 X4 X1 S1
T2 X5 S3
T3 X2 X7 S1
T3 X3 S3
T4 X7 S2
T4 X8 X5 S3
T5 X3 X7 S3
Produce local wait for graph for each of the sites and construct global wait for graph
and check for dead lock.
4 Object Oriented Database
1. Scenario: Universitywants to track persons associated with them. A person
can be an Employee or Student. Employees are Faculty, Technicians and
project Associates. Students are Full time students, Part time students and
Teaching Assistants.
TASK1: Design an Enhanced Entity Relationship (EER) Model for university database.
Write and execute OQL for the following
Insert details in each object.
Display the Employee details.
Display Student Details.
Modify person details.
Delete person details.
45
TASK2: Extend the design by incorporating the following information.
Students are registering for courses which are handled by instructor researchers
(graduate students). Faculty are advisors to graduate students. Instructor researchers
class is a category with superclass of faculty and graduate students. Faculty are having
sponsored research projects with a grant supporting instruction researchers. Grants are
sanctioned by different agencies. Faculty belongs to different departments. Department
is chaired by a faculty. Insert and Display details in each class.
5 Parallel Database
1. Consider the application for University Counselling for Engineering Colleges.
The college, department and vacancy details are maintained in 3 sites.
Students are allocated colleges in these 3 sites simultaneously. Implement this
application using parallel database.
2. Scenario: There are 5 processors working in a parallel environment and
producing output. The output record contains college details and students mark
information. Implement parallel join and parallel sort algorithms to get the
marks from different colleges of the university and publish 10 ranks for each
discipline. Use java and Python.
6 Active database
1. Create triggers and assertions for Bank database handling deposits and loan
and Admission database handling seat allocation and vacancy position.
TASK: Design the above relational database schema and implement the following
triggers and assertions.
a. When a deposit is made by a customer, create a trigger for updating
customers account and bank account
b. When a loan is issued to the customer, create a trigger for updating
customers loan account and bank account.
c. Create assertion for bank database so that the total loan amount does
not exceed the total balance in the bank.
d. When an admission is made, create a trigger for updating the seat
allocation details and vacancy position.
7 Deductive database
Construct a knowledge database for kinship domain (family relations) with facts.
Extract the following relations using rules.
Parent, Sibling, Brother, Sister, Child, Daughter, Son, Spouse, Wife, husband,
Grandparent, Grandchild, Cousin, Aunt and Uncle.
46
8 Weka tool
1. Work with Weka tool classification and clustering algorithms using the given
training data and test with the unknown sample
RID Age Income Student
Credit_
rating
Class: buys_
computer
1 youth high no fair no
2 youth high no excellent no
3 middle_aged high no fair yes
4 senior medium no fair yes
5 senior low yes fair yes
6 senior low yes excellent no
7 middle_aged low yes excellent yes
8 youth medium no fair no
9 youth low yes fair yes
10 senior medium yes fair yes
11 Youth medium yes excellent yes
12 middle_aged medium no excellent yes
13 middle_aged high yes fair yes
14 senior medium no excellent no
9
Web Application
Implement web application using java servlet API for the supplier database.
10 XML
1. Design XML Schema for the given company database
Department (deptName, deptNo, deptManagerSSN, deptManagerStartDate,
deptLocation )
Employee (empName, empSSN, empSex, empSalary, empBirthDate,
empDeptNo, empSupervisorSSN, empAddress, empWorksOn)
Project ( projName, projNo, projLocation, projDeptNo, projWorker )
47
TASK1: Implement the following queries using XQuery and XPath
1. Retrieve the department name, manager name, and manager salary for every
department
2. Retrieve the employee name, supervisor name and employee salary for each
employee who works in the Research Department.
3. Retrieve the project name, controlling department name, number of employees
and total hours worked per week on the project for each project.
4. Retrieve the project name, controlling department name, number of employees
and total hours worked per week on the project for each project with more
than one employee working on it
TASK2: Implement a storage structure for storing XML database and test with the
above schema.
SEMESTER II
13MC201: ADVANCED OPERATING SYSTEMS L T P C
Course Objectives:
To review the functional components of operating system and the types of advanced
operating systems.
To understand how to order events in a distributed system using logical clocks.
To study the various algorithms for distributed mutual exclusion and distributed deadlock
detection.
To learn about the design and working of distributed file system, distributed shared
memory and distributed scheduling.
To study the different types of faults and the recovery methods for distributed systems.
To know the components and management aspects of Real time and Mobile operating
systems
Course Outcomes:
Analyse the various synchronization, scheduling and memory management issues
Able to order events in a distributed system using lamports clock and vector clock.
Analyse the performance of various mutual exclusion algorithms.
Compare the working of various distributed deadlock detection algorithms
Find solutions to the various design issues in various distributed file systems.
Explore the concept of distributed shared memory.
Identify the components in distributed scheduling
Evaluate various error recovery algorithms
Identify the features of real time and mobile operating systems
Explore the design and implementation of Android operating system.
48
UNIT I FUNDAMENTALS OF OPERATING SYSTEMS 9
Overview Synchronization Mechanisms Processes and Threads - Process Scheduling
Deadlocks: Detection, Prevention and Recovery Models of Resources Memory Management
Techniques.
UNIT II DISTRIBUTED OPERATING SYSTEMS 9
Introduction Issues Communication Primitives Inherent Limitations -Lamports Logical Clock;
Vector Clock; Causal Ordering; Global State; Cuts; Termination Detection. Distributed Mutual
Exclusion Non-Token Based Algorithms Lamports Algorithm -Token-Based Algorithms
Suzuki-Kasamis Broadcast Algorithm Distributed Deadlock Detection Issues Centralized
Deadlock-Detection Algorithms -Distributed Deadlock-Detection Algorithms.Agreement Protocols
Classification -Solutions Applications.
UNIT III DISTRIBUTED RESOURCE MANAGEMENT 9
Distributed File systems Architecture Mechanisms Design Issues Distributed Shared
Memory Architecture Algorithm Protocols -Design Issues. Distributed Scheduling Issues
Components Algorithms.
UNIT IV FAILURE RECOVERY AND FAULT TOLERANCE 9
Basic Concepts-Classification of Failures Basic Approaches to Recovery; Recovery in Concurrent
System; Synchronous and Asynchronous Checkpointing and Recovery; Check pointing in
Distributed Database Systems; Fault Tolerance; Issues -Two-phase and Non-blocking Commit
Protocols; Voting Protocols; Dynamic Voting Protocols;
UNIT V REAL TIME AND MOBILE OPERATING SYSTEMS 9
Basic Model of Real Time Systems - Characteristics- Applications of Real Time Systems Real
Time Task Scheduling - Handling Resource Sharing - Mobile Operating Systems Micro Kernel
Design - Client Server Resource Access Processes and Threads - Memory Management - File
system.
Case Study: iOS and Android: Architecture and SDK Framework - Media Layer - Services Layer -
Core OS Layer - File System.
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. MukeshSinghal and Niranjan G. Shivaratri, Advanced Concepts in Operating Systems
Distributed, Database, and Multiprocessor Operating Systems, Tata McGraw-Hill, 2001.
2. Abraham Silberschatz; Peter Baer Galvin; Greg Gagne, Operating System Concepts,
Seventh Edition, John Wiley & Sons, 2004.
3. Rajib Mall, Real-Time Systems: Theory and Practice, Pearson Education India, 2006.
4. Neil Smyth, iPhone iOS 4 Development Essentials Xcode, Fourth Edition, Payload
media, 2011.
5. Daniel P Bovet and Marco Cesati, Understanding the Linux kernel, 3rd edition, OReilly,
2005.
6. Andrew S. Tanenbaum, Modern Operating Systems, Second Edition, AddisonWesley,
2001.
49
Web References:
1. http://deneb.cs.kent.edu/~mikhail/classes/aos.f02/
2. http://www.coda.cs.cmu.edu/ljpaper/lj.html
3. http://www.coda.cs.cmu.edu/
4. http://www.windowsnetworking.com/articles_tutorials/Windows2003-Distributed-File-
System.html
5. http://www.developers.net/intelisnshowcase/view/758
6. http://csi-india.org/resource-scheduling-real-time-database-systems-operating-system-
perspective
7. http://www.xcubelabs.com/evolution-of-mobile-operating-systems.php
13MC202: MACHINE LEARNING TECHNIQUES L T P C
3 0 2 4
Course Objectives:
To explain the concepts of machine learning
To implement linear and non-linear learning models
To implement distance-based clustering techniques
To build tree and rule based models
To apply reinforcement learning techniques
Course Outcomes:
To explain theory underlying machine learning
To construct algorithms to learn linear and non-linear models
To implement data clustering algorithms
To construct algorithms to learn tree and rule-based models
To apply reinforcement learning techniques
UNIT I FOUNDATIONS OF LEARNING 9
Components of learning learning models geometric models probabilistic models logic
models grouping and grading learning versus design types of learning supervised
unsupervised reinforcement theory of learning feasibility of learning error and noise
training versus testing theory of generalization generalization bound approximation-
generalization tradeoff bias and variance learning curve
UNIT II LINEAR MODELS 9
Linear classification univariate linear regression multivariate linear regression regularized
regression Logistic regression perceptrons multilayer neural networks learning neural
networks structures support vector machines soft margin SVM going beyond linearity
generalization and overfitting regularization validation
UNIT III DISTANCE-BASED MODELS 9
Nearest neighbor models K-means clustering around medoids silhouttes hierarchical
clustering k-d trees locality sensitive hashing non-parametric regression ensemble learning
bagging and random forests boosting meta learning
50
UNIT IV TREE AND RULE MODELS 9
Decision trees learning decision trees ranking and probability estimation trees regression
trees clustering trees learning ordered rule lists learning unordered rule lists descriptive
rule learning association rule mining first-order rule learning
UNIT V REINFORCEMENT LEARNING 9
Passive reinforcement learning direct utility estimation adaptive dynamic programming
temporal-difference learning active reinforcement learning exploration learning an action-
utility function Generalization in reinforcement learning policy search applications in game
playing applications in robot control
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. Y. S. Abu-Mostafa, M. Magdon-Ismail, and H.-T. Lin, Learning from Data, AMLBook
Publishers, 2012.
2. P. Flach, Machine Learning: The art and science of algorithms that make sense of data,
Cambridge University Press, 2012.
3. K. P. Murphy, Machine Learning: A probabilistic perspective, MIT Press, 2012.
4. C. M. Bishop, Pattern Recognition and Machine Learning, Springer, 2007.
5. D. Barber, Bayesian Reasoning and Machine Learning, Cambridge University Press, 2012.
6. M. Mohri, A. Rostamizadeh, and A. Talwalkar, Foundations of Machine Learning, MIT
Press, 2012.
7. T. M. Mitchell, Machine Learning, McGraw Hill, 1997.
8. S. Russel and P. Norvig, Artificial Intelligence: A Modern Approach, Third Edition,
Prentice Hall, 2009.
13MI202: CLOUD COMPUTING TECHNOLOGIES L T P C
(Common to M.E CSE / M.Tech IT) 3 0 0 3
Course Objectives:
To understand the concept of cloud and utility computing.
To understand the various issues in cloud computing.
To familiarize themselves with the types of virtualization.
To familiarize themselves with the lead players in cloud.
To appreciate the emergence of cloud as the next generation computing paradigm.
To be able to set up a private cloud.
Course Outcomes:
Recognize the strengths and limitations of cloud computing
Discuss on various virtual machine products
Identify the architecture, infrastructure and delivery models of cloud computing Applications.
Suggest solutions for the core issues of cloud computing such as security, privacy and
interoperability
Decide the appropriate technologies, algorithms and approaches for the related issues
51
UNIT I OVERVIEW OF VIRTUALIZATION 8
Basics of Virtualization - Virtualization Types Desktop Virtualization Network Virtualization
Server and Machine Virtualization Storage Virtualization System-level of Operating
Virtualization Application Virtualization- Virtualization Advantages - Virtual Machine Basics
Taxonomy of Virtual Machines - Process Virtual Machines - System Virtual Machines Hypervisor
Interpretation and Binary translation.
UNIT II VIRTUALIZATION STRUCTURES 8
Implementation Levels of Virtualization - Virtualization Structures - Tools and Mechanisms -
Virtualization of CPU, Memory, I/O Devices - Virtual Clusters and Resource Management
Virtualization for Data-Center Automation.
UNIT III CLOUD INFRASTRUCTURE 9
Scalable Computing over the Internet Technologies for Network based Systems - System Models
for Distributed and Cloud Computing Service Oriented Architecture NIST Cloud Computing
Reference Architecture. Cloud Computing and Services Model Public, Private and Hybrid Clouds
Cloud Eco System - IaaS -PaaS SaaS. Architectural Design of Compute and Storage Clouds
Layered Cloud Architecture Development Design Challenges - Inter Cloud Resource Management
Resource Provisioning and Platform Deployment Global Exchange of Cloud Resources.
Case Study : Amazon Web Service reference , GoGrid, Rackspace.
UNIT IV PROGRAMMING MODEL 10
Parallel and Distributed Programming Paradigms MapReduce , Twister and Iterative MapReduce
Hadoop Library from Apache Mapping Applications - Programming Support - Google App
Engine, Amazon AWS - Cloud Software Environments -Eucalyptus, Open Nebula, OpenStack.
CloudSim Architecture - Cloudlets VM creation Broker VM allocation Hosts Data
Center.
UNITV SECURITY IN THE CLOUD AND RESOURCE MANAGEMENT AND RESOURCE MANAGEMENT 10
Cloud Computing Risk Issues Cloud Computing Security Challenges Cloud Computing Security
Architecture Trusted cloud Computing Identity Management and Access Control Autonomic
Security. Dynamic Resource Allocation Using Virtual Machines for Cloud Computing Environment
- Optimization of Resource Provisioning Cost in Cloud Computing
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. Kai Hwang, Geoffrey C Fox, Jack G Dongarra, Distributed and Cloud Computing, From
Parallel Processing to the Internet of Things, Morgan Kaufmann Publishers, 2012.
2. Ronald L. Krutz, Russell Dean Vines, Cloud Security A comprehensive Guide to Secure
Cloud Computing, Wiley India, 2010.
3. John W.Rittinghouse and James F.Ransome, Cloud Computing: Implementation,
Management, and Security, CRC Press, 2010.
4. George Reese, Cloud Application Architectures: Building Applications and Infrastructure
in the Cloud O'Reilly
5. SivadonChaisiri, Bu-Sung Lee, and DusitNiyato, Optimization Of Resource Provisioning
Cost In Cloud Computing, IEEE TRANSACTIONS ON SERVICES COMPUTING, VOL. 5,
52
NO. 2, APRIL-JUNE 2012.
6. Zhen Xiao, Weijia Song, And Qi Chen, Dynamic Resource Allocation Using Virtual
Machines For Cloud Computing Environment, IEEE TRANSACTIONS ON PARALLEL AND
DISTRIBUTED SYSTEMS, VOL. 24, NO. 6, JUNE 2013.
7. RajkumarBuyya, Christian Vecchiola, S.TamaraiSelvi, Mastering Cloud Computing,
TMGH,2013.
8. James E. Smith, Ravi Nair, Virtual Machines: Versatile Platforms for Systems and
Processes, Elsevier/Morgan Kaufmann, 2005.
9. William von Hagen, Professional Xen Virtualization, Wrox Publications, January, 2008.
10. DimitriosZissis, DimitriosLekkas, Addressing Cloud Computing Security Issues, Future
Generation Computer Systems 28 (2012) 583592,ELSEVIER
11. Rodrigo N.Calheiros, Rajiv Ranjan, Anton Beloglazov, Csar A. F. De Rose, and
RajkumarBuyya, CloudSim: A Toolkit for Modeling and Simulation of Cloud Computing
Environments and Evaluation of Resource Provisioning Algorithms , Cloud Computing
and Distributed Systems (CLOUDS) Laboratory.
http://www.buyya.com/papers/CloudSim2010.pdf
13MI204:BIG DATA ANALYTICS L T P C
(Common to M.E CSE / M.Tech IT) 3 0 0 3
Course Objectives:
To Explore the fundamental concepts of big data and analytics
To apply various techniques for mining data stream.
To analyze the big data using intelligent techniques.
To apply search methods and Visualization.
To design applications using Map Reduce Concepts.
Course Outcomes:
Work with big data platform and its analysis techniques.
Design efficient algorithms for mining the data from large volumes.
Model a framework for Human Activity Recognition.
Analyze the big data for useful business applications.
Implement search methods and Visualization
UNIT I INTRODUCTION TO BIG DATA 9
Introduction to Big Data Platform Challenges of Conventional Systems - Intelligent data analysis
Nature of Data - Analytic Processes and Tools - Analysis Vs Reporting - Modern Data Analytic
Tools - Statistical Concepts: Sampling Distributions - Re-Sampling - Statistical Inference -
Prediction Error.
UNIT II DATA ANALYSIS 9
Regression Modeling - Multivariate Analysis Bayesian Methods Bayesian Paradigm - Bayesian
Modeling - Inference and Bayesian Networks - Support Vector and Kernel Methods - Analysis of
53
Time Series: Linear Systems Analysis - Nonlinear Dynamics - Rule Induction - Fuzzy Logic:
Extracting Fuzzy Models from Data - Fuzzy Decision Trees
UNIT III SEARCH METHODS AND VISUALIZATION 9
Search by simulated Annealing Stochastic, Adaptive search by Evaluation Evalution Strategies
Genetic Algorithm Genetic Programming Visualization Classification of Visual Data Analysis
Techniques Data Types Visualization Techniques Interaction techniques Specific Visual data
analysis Techniques.
UNIT IV MINING DATA STREAMS 9
Introduction To Streams Concepts Stream Data Model and Architecture - Stream Computing -
Sampling Data in a Stream Filtering Streams Counting Distinct Elements in a Stream
Estimating Moments Counting Oneness in a Window Decaying Window - Real time Analytics
Platform(RTAP) Applications - Case Studies - Real Time Sentiment Analysis, Stock Market
Predictions.
UNIT V FRAMEWORKS 9
MapReduce Hadoop, Hive, MapR Sharding NoSQL Databases - S3 - Hadoop Distributed File
Systems Case Study- Preventing Private Information Inference Attacks on Social Networks-Grand
Challenge: Applying Regulatory Science and Big Data to Improve Medical Device Innovation
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. Michael Berthold, David J. Hand, Intelligent Data Analysis, Springer, 2007.
2. AnandRajaraman and Jeffrey David Ullman, Mining of Massive Datasets, Cambridge
University Press, 2012.
3. Bill Franks, Taming the Big Data Tidal Wave: Finding Opportunities in Huge Data Streams
with Advanced Analytics, John Wiley & sons, 2012.
4. Glenn J. Myatt, Making Sense of Data, John Wiley & Sons, 2007
5. Pete Warden, Big Data Glossary, OReilly, 2011.
6. Jiawei Han, MichelineKamber Data Mining Concepts and Techniques, Second Edition,
Elsevier, Reprinted 2008.
7. Raymond Heatherly , Murat Kantarcioglu and BhavaniThuraisingham Preventing Private
Information Inference Attacks on Social Networks IEEE Transaction on Knowledge and
Data Engineering,Vol 25, No.8 ,August 2013.
8. Arthur G. Erdman, Daniel F. Keefe, Senior Member, IEEE, and Randall SchiestGrand
Challenge: Applying Regulatory Science andBig Data to Improve Medical Device
InnovationIEEE TRANSACTIONS ON BIOMEDICAL ENGINEERING, VOL. 60, NO. 3, MARCH
2013
54
13MC251: ADVANCED OPERATING SYSTEMS LABORATORY L T P C
0 0 3 2
Course Objectives:
To achieve synchronisation among processes and threads. (Multiprocessor operating
system)
To write a program order events and messages in a distributed system using vector clocks.
(Distributed operating system)
To write a distributed application using RMI. (Distributed operating system)
To study and develop Android based mobile applications. (Mobile OS)
To study and develop real time applications like alarm clock (Real Time OS)
Course Outcomes:
Achieve Synchronisation among multiple processes.
Provide synchronisation using monitors in a multithreaded application.
Develop RMI applications.
Order events using Lamports logical clock and vector clock.
Order messages in a distributed system using vector clock.
Compare various distributed scheduling algorithms.
Explore a real time OS and develop real time applications.
Investigate Android OS and develop an Android based mobile application.
List of Sample Exercises
Exercise 1
Semaphores - Multiprocessor operating systems
6
Assume there are three processes: Pa, Pb, and Pc. Only Pa can output the letter A, Pb B,
and Pc C.Utilizing only semaphores (and no other variables) the processes are synchronized so
that the output satisfies the following conditions:
a) A B must be output before any C's can be output.
b) B's and C's must alternate in the output string, that is, after the first B is
output, another B cannot be output until a C is output. Similarly, once a C is output,
another C cannot be output until a B is output.
c) The total number of B's and C's which have been output at any given point in
the output string cannot exceed the number of A's which have been output up to that
point.
Examples
AACB -- invalid, violates a)
ABACAC -- invalid, violates b)
AABCABC -- invalid, violates c)
AABCAAABC -- valid
AAAABCBC -- valid
AB valid
55
Exercise 2 Multithreading - Multiprocessor operating systems 3
The Cigarette Smokers Problem
Consider a simulation with three smoker threads and one agent thread. Each smoker
continuously makes a cigarette and smokes it. But to make a cigarette, a smoker needs three
ingredients: tobacco, paper, and matches. One of the smoker threads has only paper, another has
only tobacco and the third has only matches. The agent thread has an infinite supply of all three
materials. The three smoker threads are initially blocked. The agent places two randomly chosen
(different) ingredients on the table and unblocks the one smoker who has the remaining
ingredient. The agent then blocks. The unblocked smoker removes the two ingredients from the
table, makes a cigarette, and smokes it for a random amount of time, unblocking the agent on
completion of smoking the cigarette. The agent then puts out another random two of the three
ingredients, and the cycle repeats.
Write a multi-class multithreaded Java program that uses a monitor to synchronize the
agent thread and the three smoker threads. Do not mechanically translate semaphore code into
monitor code! The agent thread executes in an agent object created from an agent class. Each
smoker thread executes in a smoker object. All smoker objects are created from one smoker class
whose constructor is used to specify the ingredient possessed by the smoker object. A driver class
with a main method constructs the objects and starts the threads. Use a single monitor object
instantiated from a class Control for synchronization. Each of the four threads invokes a
synchronized monitor method for its synchronization. No semaphores are allowed. No
synchronized blocks are allowed, only synchronized methods. No busy waiting is allowed. No calls
to nap inside a synchronized method are allowed (do not nap while holding the monitor object's
lock, that is, while inside a synchronized method or while inside a method called by a synchronized
method).
Exercise 3 Multiple sleeping barbers - Multiprocessor operating systems 3
Write a multi-class multithreaded Java program that simulates multiple sleeping barbers, all in one
barbershop that has a finite number of chairs in the waiting room. Each customer is instantiated
from a single Customer class; each barber is instantiated from a single Barber class.
Exercise 4 Lamports Mutual Exclusion - Distributed operating systems 3
Implement the Lamports distributed mutual exclusion algorithm.
Requesting the critical section:
When a site Si wants to enter the CS, it broadcasts a REQUEST(tsi , i )message to all other sites
and places the request on request queuei . ((tsi ,i )denotes the timestamp of the request.)
When a site Sj receives the REQUEST(tsi , i ) message from site Si ,places siteSi s request on
request queuej and it returns a timestamped REPLY messageto Si .
Executing the critical section:
Site Si enters the CS when the following twoconditions hold:
L1: Si has received a message with timestamp larger than (tsi ,i ) fromall other sites.
L2: Si s request is at the top of request queuei .
Releasing the critical section:
Site Si , upon exiting the CS, removes its request from the top of its request queue and broadcasts
a timestamped RELEASE message to all other sites.
56
When a site Sj receives a RELEASE message from site Si , it removes Si s request from its request
queue.
When a site removes a request from its request queue, its own request may come
at the top of the queue, enabling it to enter the CS.
Exercise 5 Event Ordering - Distributed operating systems 3
Consider a distributed system that consists of two processes which communicate with each other.
Let P be a state predicate on the local state of one process and Q be a state predicate on the local
state of the other process. Order all the events that happen in the processes using lamports clock
and vector clock.
Exercise 6 Causal Message Ordering -Distributed operating systems 6
The purpose of causal ordering of messages is to insure that the same causal relationship for the
"message send" events correspond with "message receive" events. (i.e. All the messages are
processed in order that they were created.)
Birman-Schiper-Stephenson Protocol
There are three basic principles to this algorithm:
1. All messages are time stamped by the sending process.
[Note: Each element of the vector corresponds to the number of messages sent (including
this one) to other processes.]
2. A message cannot be delivered until:
o All the messages before this one have been delivered locally.
o All the other messages that have been sent out from the original processshas been
accounted as delivered at the receiving process.
3. When a message is delivered, the clock is updated.
This protocol requires that the processes communicate through broadcast messages since
this would ensure that only one message could be received at any one time (thus concurrently
timestamped messages can be ordered).
Exercise 7 Scheduling -Distributed operating systems
6
Simulate the sender initiated, receiver initiated and symmetric initiated load sharing algorithms.
Assume n nodes and generate values for parameters like queue length and threshold. Run the
simulation, compare the results and print the statistics.
Exercise 8 Real time operating systems
3
A real-time program implementing an alarm clock shall be developed.
[Alarm clock, using C and Simple_OS]
The program shall fulfill the following requirements:
Clock with alarm functionality shall be implemented, It shall be possible to set the time, It
shall be possible to set the alarm time, the alarm shall be enabled when the alarm time is set, the
alarm shall be activated when the alarm is enabled, and when the current time is equal to the
alarm time, an activated alarm must be acknowledged. Acknowledgement of an alarm shall lead to
the alarm being disabled, the alarm is enabled again when a new alarm time is set, and an alarm
which is not acknowledged shall be repeated every 10 seconds. The program shall communicate
57
with a graphical user interface, where the current time shall be displayed, and where the alarm
time shall be displayed when the alarm is enabled. It shall be possible to terminate the program,
using a command which is sent from the graphical user interface.
Exercise 9 Case Study Embedded and Real time operating systems 3
Study and experiment any embedded and real-time operating system such as eCos
Exercise 10 Case Study - Mobile Operating System 6
Study the Android open source operating system for mobile devices and develop an simple
application
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. MukeshSinghal and Niranjan G. Shivaratri, Advanced Concepts in Operating Systems
Distributed, Database, and Multiprocessor Operating Systems, Tata McGraw-Hill, 2001.
2. Abraham Silberschatz; Peter Baer Galvin; Greg Gagne, Operating System Concepts,
Seventh Edition, John Wiley & Sons, 2004.
3. Rajib Mall, Real-Time Systems: Theory and Practice, Pearson Education India, 2006.
4. Neil Smyth, iPhone iOS 4 Development Essentials Xcode, Fourth Edition, Payload
media, 2011.
5. Daniel P Bovet and Marco Cesati, Understanding the Linux kernel, 3rd edition, OReilly,
2005.
6. Andrew S. Tanenbaum, Modern Operating Systems, Second Edition, AddisonWesley,
2001.
7. Harvey Deitel and Paul J. Deitel, Java How to Program,Ninth Edition,
PearsonEducation,2011
Web References:
1. http://ecos.sourceware.org
2. http://source.android.com/
3. http://docs.oracle.com/javase/tutorial/rmi/
13MI252:CLOUD COMPUTING LABORATORY L T P C
(Common to M.E CSE / M.Tech IT) 0 0 3 2
Course Objectives:
To learn how to use Cloud Services.
To implement Virtualization
To implement Task Scheduling algorithms.
To implement Energy-conscious model.
To build Private Cloud.
Course Outcomes:
Analyze the use of Cloud Applications
Apply resource allocation, scheduling algorithms.
Implement Energy-conscious model.
Create virtual machines from available physical resources.
58
Setup a private cloud.
Familiarize with Open Source Cloud computing Software.
SYLLABUS FOR THE LAB:
1. Study and Usage of Google Apps.
2. Implement Virtual OS using virtual box.
3. Simulate VM allocation algorithm using cloudSim
4. Simulate Task Scheduling algorithm using CloudSim
5. Simulate Energy-conscious model using CloudSim
6. Setup a Private Cloud Using Open Stack or Eucalyptus.
7. Install and configure Open Stack Object Storage - Swift in Ubuntu.
8. Implement Open Stack Nova-Compute
9. Implement Open Stack Image services Glance.
10. Implement Map Reduce concept for an application.
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. James E. Smith, Ravi Nair, Virtual Machines: Versatile Platforms for Systems and
Processes, Elsevier/Morgan Kaufmann, 2005.
2. George Reese, Cloud Application Architectures: Building Applications and Infrastructure
in the Cloud O'Reilly.
WEB REFERENCES:
1. http://cloudblab.wordpress.com/
2. http://searchservervirtualization.techtarget.com/
List of Sample Exercises
1
1.
Create a Collaborative learning environment for a particular learning topic using Google
Apps. Google Drive, Google Docs and Google Slides must be used for hosting e-books,
important articles and presentations respectively. The instructor must use the Google
Sheets to convey the timetable for different events and for analyzing the scores for
individual assignment submission.
2.
Modeling and simulation Cloud computing environments, including Data Centers, Hosts
and Cloudlets and perform VM provisioning using CloudSim: Design a host with two CPU
cores, which receives request for hosting two VMs, such that each one requires two cores
and plans to host four tasks units. More specifically, tasks t1, t2, t3 and t4 to be hosted
in VM1, while t5, t6, t7, and t8 to be hosted in VM2.
Implement space-shared allocation policy and time-shared allocation policy. Compare the
results
3
3.
Model a Cloud computing environment having Data center that had 100 hosts. The hosts
are to be modeled to have a CPU core (1000 MIPS), 2 GB of RAM and 1 TB of storage.
Consider the workload model for this evaluation included provisioning requests for 400
VMs, with each request demanding 1 CPU core (250 MIPS), 256 MB of RAM and 1 GB of
storage. Each VM hosts a web-hosting application service, whose CPU utilization
distribution was generated according to the uniform distribution. Each instance of a web-
59
hosting service required 150,000 MIPS or about 10 minutes to complete execution
assuming 100% utilization.
Simulate Energy-conscious model for power consumption and power management
techniques such as Dynamic Voltage and Frequency Scaling (DVFS).
Initially, VMs are to be allocated according to requested parameters (4 VMs on each
host). The Cloud computing architecture that is to be considered for studying energy-
conscious resource management techniques/policies included a data center,
CloudCoordinator, and Sensor component. The CloudCoordinator and Sensor perform
their usual roles. Via the attached Sensors (which are connected with every host),
CloudCoordinator must periodically monitor the performance status of active VMs such as
load conditions, and processing share. This real time information is to be passed to VMM,
which can use it for performing appropriate resizing of VMs and application of DVFS and
soft scaling. CloudCoordinator continuously has to adapt allocation of VMs by issuing VM
migration commands and changing power states of nodes according to its policy and
current utilization of resources.
1
4.
Model and simulate the environment consisting of a data center with 10,000 hosts where
each host was modeled to have a single CPU core (1200MIPS), 4GB of RAM memory and
2TB of storage. Consider the provisioning policy for VMs as space-shared, which allows
one VM to be active in a host at a given instance of time. Make a request from the end-
user (through the DatacenterBroker) for creation and instantiation of 50 VMs that had
following constraints: 1024MB of physical memory, 1 CPU core and 1GB of storage. The
application granularity was modeled to be composed of 300 task units, with each task
unit requiring 1,440,000 million instructions (20 minutes in the simulated hosts) to be
executed on a host. Minimal data transfer (300 KB) overhead can be considered for the
task units (to and from the data center). After the creation of VMs, task units were
submitted in small groups of 50 (one for each VM) at inter-arrival delay of 10 minutes.
5. Implement Map Reduce concept for:
a. Strassens Matrix Multiplication for a huge matrix.
Computing the average number of citation index a researcher has according to age
among some 1 billion journal articles.
3
6.
1
Consider a network of entities and relationships between them. It is required to calculate
a state of each entity on the basis of properties of the other entities in its neighborhood.
This state can represent a distance to other nodes, indication that there is a neighbor
with the certain properties, characteristic of neighborhood density and so on. A network
is stored as a set of nodes and each node contains a list of adjacent node IDs. Mapper
emits messages for each node using ID of the adjacent node as a key. Reducer must
recompute state and rewrite node with the new state. Implement this scenario.
Setup a Private Cloud Using OpenStack or Eucalyptus. Develop a simple application and
make it available to the intended user.
7. Install and configure OpenStack Object Storage - Swift in Ubuntu. Consider a huge
storage requirements and store it in the cloud in a transparent manner.
60
3
8.
Install and configure OpenStack Nova-Compute. Enable a connected user to get a virtual
machine of a selected performance such as CPU, Memory.
1
9.
Install and configure Stack Image services to query for information on available disk
images, and use the Image Service's client library for streaming virtual disk images.
ELECTIVE COURSES - ELECTIVE I & II
13MC401: FORMAL MODELS OF SOFTWARE SYSTEMS L T P C
3 0 0 3
Course Objectives:
To understand the basic elements of Z
To understand relations, functions, and logical structures in Z
To understand Z schemas and schema calculus
To learn selected Z case studies
To understand Z schema refinement
Course Outcomes:
Apply the basic elements of Z
Develop relational, functional, and logical Z structures
Develop Z schema as models of software systems
Perform verifications and conduct proofs using Z models
Refine Z models towards implementing software systems
UNIT I FOUNDATIONS OF Z 9
Understanding formal methods motivation for formal methods informal requirements to formal
specifications validating formal specifications Overview of Z specification basic elements of Z
sets and types declarations variables expressions operators predicates and equations
UNIT II STRUCTURES IN Z 9
Tuples and records relations, tables, databases pairs and binary relations functions
sequences propositional logic in Z predicate logic in Z Z and boolean types set
comprehension lambda calculus in Z simple formal specifications modeling systems and
change
UNIT III Z- SCHEMAS AND SCHEMA CALCULUS 9
Z schemas schema calculus schema conjunction and disjunction other schema calculus
operators schema types and bindings generic definitions free types formal reasoning
checking specifications precondition calculation machine-checked proofs
UNIT IV Z CASE STUDIES 9
Case Study: Text processing system Case Study: Eight Queens Case Study: Graphical User
Interface Case Study: Safety critical protection system Case Study: Concurrency and real
time systems
UNIT V Z REFINEMENT 9
Refinement of Z specification generalizing refinements refinement strategies program
derivation and verification refinement calculus data structures state schemas functions
and relations operation schemas schema expressions refinement case study
TOTAL: 45 PERIODS
61
REFERENCE BOOKS:
1. Jonathan Jacky, The way of Z: Practical programming with formal methods, Cambridge
University Press, 1996.
2. Antoni Diller, Z: An introduction to formal methods, Second Edition, Wiley, 1994.
3. Jim Woodcock and Jim Davies, Using Z Specification, Refinement, and Proof, Prentice
Hall, 1996.
4. J. M. Spivey, The Z notation: A reference manual, Second Edition, Prentice Hall, 1992.
5. M. Ben-Ari, Mathematical logic for computer science, Second Edition, Springer, 2003.
6. M. Huth and M. Ryan, Logic in Computer Science Modeling and Reasoning about
systems, Second Edition, Cambridge University Press, 2004.
Web References:
1. http://www.cs.ox.ac.uk/people/michael.wooldridge/teaching/soft-eng/lect12.pdf
2. http://www.rbjones.com/rbjpub/cs/csfm04.htm
3. http://spivey.oriel.ox.ac.uk/mike/zrm/zrm.pdf
4. http://www.jetcafe.org/~jim/lambda.html
5. http://www.utdallas.edu/~gupta/courses/apl/lambda.pdf
13MC402: PERFORMANCE EVALUATION OF COMPUTER SYSTEMS L T P C
3 0 0 3
Course Objectives:
To explore the mathematical foundations needed for performance evaluation of computer
systems
To exemplify the metrics used for performance evaluation
To elucidate the analytical modeling of computer systems
To enable the students to develop new queueing analysis for both simple and complex
systems
To illustrate the use of smart scheduling and introduce the students to analytical
techniques for evaluating scheduling policies
Course Outcomes:
Identify the need for performance evaluation and the metrics used for it
Discuss open and closed queueing networks
Define Littles law and other operational laws
Apply the operational laws to open and closed systems
Use discrete-time and continuous-time Markov chains to model real world systems
Develop analytical techniques for evaluating scheduling policies
UNIT I OVERVIEW OF PERFORMANCE EVALUATION 9
Need for Performance Evaluation in Computer Systems Overview of Performance Evaluation
Methods Introduction to Queueing Probability Review Generating Random Variables for
Simulation Sample Paths, Convergence and Averages Littles Law and other Operational Laws
Modification for Closed Systems.
62
UNIT II MARKOV CHAINS AND SIMPLE QUEUES 9
Discrete-Time Markov Chains Ergodicity Theory Real World Examples Google, Aloha
Transition to Continuous-Time Markov Chain M/M/1 and PASTA.
UNIT III MULTI-SERVER AND MULTI-QUEUE SYSTEMS 9
Server Farms: M/M/k and M/M/k/k Capacity Provisioning for Server Farms Time Reversibility
and Burkes Theorem Networks of Queues and Jackson Product Form Classed and Closed
Networks of Queues.
UNIT IV REAL-WORLD WORKLOADS 9
Case Study of Real-world Workloads Phase-Type Distributions and Matrix-Analytic Methods
Networks with Time-Sharing Servers M/G/1 Queue and the Inspection Paradox Task
Assignment Policies for Server Farms
UNIT V SMART SCHEDULING IN THE M/G/1 9
Performance Metrics Scheduling Non-Preemptive and Preemptive Non-Size-Based Policies -
Scheduling Non-Preemptive and Preemptive Size-Based Policies Scheduling - SRPT and
Fairness.
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. MorHarchol - Balter, Performance Modeling and Design of Computer Systems Queueing
Theory in Action, Cambridge University Press, 2013.
2. Raj Jain, The Art of Computer Systems Performance Analysis: Techniques for Experimental
Design, Measurement, Simulation and Modeling, Wiley-Interscience, 1991.
3. LievenEeckhout, Computer Architecture Performance Evaluation Methods, Morgan and
Claypool Publishers, 2010.
4. Paul J. Fortier and Howard E. Michel, Computer Systems Performance Evaluation and
Prediction, Elsevier, 2003.
5. David J. Lilja, Measuring Computer Performance: A Practitioners Guide, Cambridge
University Press, 2000.
6. Krishna Kant, Introduction to Computer System Performance Evaluation, McGraw-Hill,
1992.
7. K. S. Trivedi, Probability and Statistics with Reliability, Queueing and Computer Science
Applications, John Wiley and Sons, 2001.
WEB REFERENCES:
1. http://freevideolectures.com/Course/3066/Performance-Evaluation-of-Computer-Systems
2. http://homepages.inf.ed.ac.uk/jeh/Simjava/queueing/
3. http://www.supositorio.com/rcalc/rcalclite.htm
4. http://practicalperformanceanalyst.com/site/content/performance-modeling-101
13MC403: MODEL CHECKING AND PROGRAM VERIFICATION L T P C
3 0 0 3
Course Objectives:
To understand automata for model checking
To understand LTL, CTL, and CTL*
63
To understand timed automata, TCTL, and PCTL
To understand verification of deterministic and recursive programs
To understand verification of object-oriented programs
To understand verification of parallel, distributed, and non-deterministic programs
Course Outcomes:
Perform model checking using LTL
Perform model checking using CTL
Perform model checking using CTL*
Perform model checking using TCTL and PCTL
Verify deterministic and recursive programs
Verify object-oriented programs
Verify parallel, distributed, and non-deterministic programs
UNIT I AUTOMATA AND TEMPORAL LOGICS 9
Automata on finite words model checking regular properties automata on infinite words
Buchi automata Linear Temporal Logic (LTL) automata based LTL model checking
Computational Tree Logic (CTL) CTL model checking CTL* model checking
UNIT II TIMED AND PROBABILISTIC TREE LOGICS 9
Timed automata timed computational tree logic (TCTL) TCTL model checking probabilistic
systems probabilistic computational tree logic (PCTL) PCTL model checking PCTL* - Markov
decision processes.
UNIT III VERIFYING DETERMINISTIC AND RECURSIVE PROGRAMS 9
Introduction to program verification verification of while programs partial and total
correctness verification of recursive programs case study: binary search verifying
recursive programs with parameters
UNIT IV VERIFYING OBJECT-ORIENTED AND PARALLEL PROGRAMS 9
Partial and total correctness of object-oriented programs case study: Insertion in linked lists
verification of disjoint parallel programs verifying programs with shared variables case
study: parallel zero search verification of synchronization case study: the mutual exclusion
problem
UNIT V VERIFYING NON-DETERMINISTIC AND DISTRIBUTED PROGRAMS 9
Introduction to non-deterministic programs partial and total correctness of non-deterministic
programs case study: The Welfare Crook Problem syntax and semantics of distributed
programs verification of distributed programs case study: A Transmission Problem
introduction to fairness
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. C. Baier, J.-P. Katoen, and K. G. Larsen, Principles of Model Checking, MIT Press, 2008.
2. E. M. Clarke, O. Grumberg, and D. A. Peled, Model Checking, MIT Press, 1999.
3. M. Ben-Ari, Principles of the SPIN Model Checker, Springer, 2008.
4. K. R. Apt, F. S. de Boer, E.-R. Olderog, and A. Pnueli, Verification of Sequential and
Concurrent Programs, Third Edition, Springer, 2010.
5. M. Huth and M. Ryan, Logic in Computer Science --- Modeling and Reasoning about
64
Systems, Second Edition, Cambridge University Press, 2004.
6. B. Berard et al., Systems and Software Verification: Model-checking techniques and
tools, Springer, 2010.
7. J. B. Almeida, M. J. Frade, J. S. Pinto, and S. M. de Sousa, Rigorous Software
Development: An Introduction to Program Verification, Springer, 2011.
Web References:
1. http://resist.isti.cnr.it/free_slides/testing/bowen/w3_l1_ctl.pdf
2. http://www.cs.toronto.edu/~chechik/courses07/csc2108/Lectures/temporalLogics.2up.p
df
3. http://home.in.tum.de/~hoelzl/documents/hoelzl2012verifyingpctl.pdf
4. http://www-i2.informatik.rwth-
aachen.de/i2/fileadmin/user_upload/documents/MVPS11/lec13_handout_2_.pdf
5. http://developer.download.nvidia.com/assets/cuda/files/ZeroSumGPU-ISC11.pdf
13MC404: SENSING TECHNIQUES AND SENSORS L T P C
3 0 0 3
Course Objectives:
To gain knowledge on the sensor characteristics and the fundamental principles of
sensing
To learn the characteristics of sensor interface electronics
To get acquainted with motion-related sensors
To learn how to use light and radiation detectors
To find out the importance of selected temperature sensors
To locate the characteristics of selected chemical sensors
Course Outcomes:
Extrapolate the basics of sensors
Explain the physics of sensors
Predict the optical components of sensors
Capable of applying sensor interface electronics
Develop appropriate motion-related sensors
Capable of designing light and radiation detectors
Choose and use appropriate temperature andremote sensors
UNIT I PRINCIPLES OF SENSING 9
Data Acquisition sensor characteristics electric charges, fields, potentials capacitance
magnetism inductance resistance Specific resistivity - Temperature sensitivity- Strain
Sensitivity -piezoelectric effect pyroelectric Effect Hall effect thermoelectric effects sound
waves Temperature scales-Thermal Expansion- heat transfer light dynamic models of sensors
UNIT II OPTICAL COMPONENTS AND INTERFACE ELECTRONICS 9
Radiometry Photometry mirrors lenses fibre optics concentrators Interface circuits
Serial Interface - Parallel Interface- amplifiers light-to-voltage excitation circuits ADC
Digitization Capacitance-to-voltage bridge circuits data transmission noise in sensors and
circuits calibration low power sensors.
65
UNIT III MOTION RELATED SENSORS 9
Occupancy and motion detectors: ultrasonic microwave capacitive detectors tribo electric
optoelectronic motion sensors optical presence sensor Pressure Gradient sensors-Velocity and
acceleration sensors: Accelerometer characteristics capacitative accelerometers piezoelectric
accelerometers piezoresistive accelerometers thermal accelerometers Gyroscopes
piezoelectric cables gravitational sensors
UNIT IV LIGHT AND RADIATION DETECTORS 9
Light Detectors: Photo diodes photo transistor photo resistor cooled detectors CCD and
CMOS image sensors thermal detectors optical design gas flame detectors- Radiation
Detectors: scintillating detectors ionization detectors cloud and bubble chambers
UNIT V TEMPERATURE AND CHEMICAL SENSORS 9
Temperature Sensors: coupling with objects temperature reference points thermo resistive
sensors thermo electric contact sensors semiconductor sensors acoustic sensors
piezoelectric sensors - Chemical sensors: characteristics classes of chemical sensors
biochemical sensors multi-sensor arrays electronic noses and tongues Electro chemical
sensors - Remote sensors
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. Jacob Fraden, Handbook of Modern Sensors: Physics, Designs, and Applications, Fourth
Edition, Springer, 2010.
2. D.Patranabis,Sensors and Transducers, PHI Learning Pvt. Ltd, Second Edition, 2003.
3. John Vetelino, AravindReghu, Introduction to sensors, CRC Press, 2011
WEB REFERENCES:
1. http://www.remm.nlm.gov/civilian.htm
2. http://hlt.media.mit.edu/cmi_readings/sensorsPapers/modernSensors3.pdf
3. http://www.newhavendisplay.com/app_notes/parallel-serial.pdf
4. http://www.intlsensor.com/pdf/electrochemical.pdf
13MI403:INTERNET OF THINGS L T P C
(Common to M.E CSE / M.Tech IT) 3 0 0 3
Course Objectives:
To learn the basic issues, policy and challenges in the Internet
To understand the components and the protocols in Internet
To build a small low cost embedded system with the internet
To understand the various modes of communications with internet
To learn to manage the resources in the Internet
To deploy the resources into business
To understand the cloud and internet environment.
Course Outcomes:
Identify the components of IOT
Design a portable IOT using appropriate boards
Program the sensors and controller as part of IOT
66
Develop schemes for the applications of IOT in real time scenarios
Establish the communication to the cloud through wifi/ Bluetooth
Manage the internet resources
Model the Internet of things to business
UNIT I INTRODUCTION 9
Definition phases Foundations Policy Challenges and Issues - identification - security
privacy. Components in internet of things: Control Units Sensors Communication modules
Power Sources Communication Technologies RFID Bluetooth Zigbee Wifi Rflinks
Mobile Internet Wired Communication
UNIT II PROGRAMMING THE MICROCONTROLLER FOR IOT 9
Basics of Sensors and actuators examples and working principles of sensors and actuators
Cloud computing and IOT Arduino/Equivalent Microcontroller platform Setting up the board -
Programming for IOT Reading from Sensors
Communication: Connecting microcontroller with mobile devices communication through
bluetooth and USB connection with the internet using wifi / ethernet
UNIT III RESOURCE MANAGEMENT IN THE INTERNET OF THINGS 9
Clustering - Software Agents - Data Synchronization - Clustering Principles in an Internet of Things
Architecture - The Role of Context - Design Guidelines -Software Agents for Object - Data
Synchronization- Types of Network Architectures - Fundamental Concepts of Agility and
Autonomy-Enabling Autonomy and Agility by the Internet of Things-Technical Requirements for
Satisfying the New Demands in Production - The Evolution from the RFID-based EPC Network to an
Agent based Internet of Things- Agents for the Behaviour of Objects
UNIT IV BUSINESS MODELS FOR THE INTERNET OF THINGS 9
The Meaning of DiY in the Network Society- Sensor-actuator Technologies and Middleware as a
Basis for a DiY Service Creation Framework - Device Integration - Middleware Technologies
Needed for a DiY Internet of Things Semantic Interoperability as a Requirement for DiY Creation -
Ontology- Value Creation in the Internet of Things-Application of Ontology Engineering in the
Internet of Things-Semantic Web-Ontology - The Internet of Things in Context of EURIDICE -
Business Impact
UNIT V FROM THE INTERNET OF THINGS TO THE WEB OF THINGS: 9
Resource-oriented Architecture and Best Practices- Designing RESTful Smart Things - Web-
enabling Constrained Devices - The Future Web of Things - Set up cloud environment send data
from microcontroller to cloud Case study CAM:cloud Assisted Privacy Other recent projects.
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. CharalamposDoukas , Building Internet of Things with the Arduino, Create space, April
2002
2. Dieter Uckelmann et.al, Architecting the Internet of Things, Springer, 2011
3. Luigi Atzor et.al, The Internet of Things: A survey, , Journal on Networks, Elsevier
Publications, October, 2010
67
4. Huang Lin ; Dept. of Electr. &Comput. Eng., Univ. of Florida, Gainesville, FL, USA ; Jun
Shao ; Chi Zhang ; Yuguang Fang,CAM: Cloud-Assisted Privacy Preserving Mobile Health
Monitoring IEEE Transactions on Information Forensics and Security, 2013
5. Pengwei Hu; Fangxia Hu An optimized strategy for cloud computing architecture,3rd IEEE
Transactions onComputer Science and Information Technology (ICCSIT), 2010
Web References :
1. http://postscapes.com/
2. http://www.theinternetofthings.eu/what-is-the-internet-of-things
13MI408: VIDEO ANALYTICS
(Common to M.E CSE / M.Tech IT)
L T P C
3 0 0 3
Course Objectives:
To acquire the knowledge of extracting information from surveillance videos.
To learn Event Modelling for different applications.
To understand the models used for recognition of objects in videos.
To learn analysis techniques employed for videos.
To know the concepts behind video analytics in business intelligence.
Course Outcomes:
Work with surveillance videos for analytics.
Design optimization algorithms for better analysis and recognition of objects in a scene.
Model a framework for Human Activity Recognition.
Analyze video scenes.
Estimate age of Human and Classify the sex.
Analyze Crowded videos and count crowd.
UNIT I VIDEO ANALYTICS 9
Introduction- Video Basics - Fundamentals for Video Surveillance- Scene Artifacts- Object
Detection and Tracking: Adaptive Background Modelling and Subtraction- Pedestrian Detection and
Tracking-Vehicle Detection and Tracking- Articulated Human Motion Tracking in Low-Dimensional
Latent Spaces.
UNIT II BEHAVIOURAL ANALYSIS & ACTIVITY RECOGNITION
9
Event Modelling- Behavioural Analysis- Human Activity Recognition-Complex Activity Recognition-
Activity modelling using 3D shape, Video summarization, shape based activity models- Suspicious
Activity Detection.
UNIT III HUMAN FACE RECOGNITION & GAIT ANALYSIS 9
Introduction: Overview of Recognition algorithms Human Recognition using Face: Face
Recognition from still images, Face Recognition from video, Evaluation of Face Recognition
Technologies- Human Recognition using gait: HMM Framework for Gait Recognition, View Invariant
Gait Recognition, Role of Shape and Dynamics in Gait Recognition - Factorial HMM and Parallel
HMM for Gait Recognition- Face Recognition Performance: Role of Demographic Information.
68
UNIT IV VIDEO ANALYTICS FOR BUSINESS INTELLIGENCE - I 9
Video Analytics for Business Intelligence - Object Detection and Tracking -Auto-calibration of Non-
overlapping Multi-camera CCTV Systems -Fast Approximate Nearest Neighbor Methods for
Example-Based Video Search -Human Age Estimation and gender Classification -People Counter:
Counting of Mostly Static People in Indoor Conditions -Scene Invariant Crowd Counting and Crowd
Occupancy Analysis.
UNIT V VIDEO ANALYTICS FOR BUSINESS INTELLIGENCE - II 9
Identifying Customer Behaviour and Dwell Time Using Soft Biometrics -Automatic Activity Profile
Generation from Detected Functional Regions for Video Scene Analysis - Analyzing Groups: A
Social Signaling Perspective - Design and Validation of a System for People Queue Statistics
Estimation.
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. Michael Berthold, David J.Hand, Intelligent Data Analysis, Springer, 2007.
2. AnandRajaraman and Jeffrey David Ullman, Mining of Massive Datasets, Cambridge
University Press, 2012.
3. Yunqian Ma, Gang Qian, Intelligent Video Surveillance: Systems and Technology, CRC
Press (Taylor and Francis Group), 2009.
4. Rama Chellappa, AmitK.Roy-Chowdhury, Kevin Zhou.S, Recognition of Humans and their
Activities using Video, Morgan&Claypool Publishers, 2005.
5. YiHuang,DongXu and Tat-Jen Cham, Face and Human Gait Recognition Using Image-to-
Class Distance IEEE Transactions On Circuits And Systems For Video Technology, Vol. 20,
No. 3, March 2010.
6. Changhong Chen, Jimin Liang, Heng Zhao, Haihong Hu, and JieTian, Factorial HMM and
Parallel HMM for Gait Recognition, IEEE Transactions On Systems, Man, And Cybernetics
Part C: Applications And Reviews, Vol. 39, No. 1, January 2009.
7. Changhong Chen, Jimin Liang, Haihong Hu, Licheng Jiao, Xin Yang, Factorial Hidden
Markov Models for Gait Recognition, Advances in BiometricsLecture Notes in Computer
Science Volume 4642, 2007, pp 124-133.
8. Brendan F. Klare, Mark J. Burge, Joshua C. Klontz, Richard W. VorderBruegge, and Anil K.
Jain, Face Recognition Performance: Role of Demographic Information IEEE Transactions
On Information Forensics And Security, Vol. 7, No. 6, December 2012.
9. Caifeng Shan, FatihPorikli, Tao Xiang, Shaogang Gong, Video Analytics for Business
Intelligence, Studies in Computational Intelligence, Springer, 2012.
13MC405: RECONFIGURABLE COMPUTING L T P C
3 0 0 3
Course Objectives:
To understand the need for reconfigurable computing
To expose the students to various device architectures
To examine the various reconfigurable computing systems
To understand the different types of compute models for programming reconfigurable
69
architectures
To expose the students to HDL programming and familiarize with the development
environment
To expose the students to the various placement and routing protocols
To develop applications with FPGAs
Course Outcomes:
Identify the need for reconfigurable architectures
Discuss the architecture of FPGAs
Point out the salient features of different reconfigurable architectures
Build basic modules using any HDL
Develop applications using any HDL and appropriate tools
Design and build an SoPC for a particular application
UNIT I DEVICE ARCHITECTURE 9
General Purpose Computing Vs Reconfigurable Computing Simple Programmable Logic Devices
Complex Programmable Logic Devices FPGAs Device Architecture - Case Studies.
UNIT II RECONFIGURABLE COMPUTING ARCHITECTURES AND SYSTEMS AND SYSTEMS 9
Reconfigurable Processing Fabric Architectures RPF Integration into Traditional Computing
Systems Reconfigurable Computing Systems Case Studies Reconfiguration Management.
UNIT III PROGRAMMING RECONFIGURABLE SYSTEMS 9
Compute Models - Programming FPGA Applications in HDL Compiling C for Spatial Computing
Operating System Support for Reconfigurable Computing
UNIT IV MAPPING DESIGNS TO RECONFIGURABLE PLATFORMS 9
The Design Flow - Technology Mapping FPGA Placement and Routing Configuration
BitstreamGeneration Case Studies with Appropriate Tools.
UNIT V APPLICATION DEVELOPMENT WITH FPGAS 9
Case Studies of FPGA Applications System on a Programmable Chip (SoPC) Designs.
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. Maya B. Gokhale and Paul S. Graham, Reconfigurable Computing: Accelerating
Computation with Field-Programmable Gate Arrays, Springer, 2005.
2. Scott Hauck and Andre Dehon (Eds.), Reconfigurable Computing The Theory and
Practice of FPGA-Based Computation, Elsevier / Morgan Kaufmann, 2008.
3. Christophe Bobda, Introduction to Reconfigurable Computing Architectures,
Algorithms and Applications, Springer, 2010
WEB REFERENCES:
1. http://scale.engin.brown.edu/classes/EN2911XF07/index.html
2. http://www.cs.uni-paderborn.de/?id=24991
3. http://www.cs.washington.edu/education/courses/csep567/04sp/tools/t2.html
4. http://nanocad.ee.ucla.edu/pub/Main/SnippetTutorial/Santiago_FPGA_CAD.html
5. http://www.cs.washington.edu/education/courses/cse467/11wi/lectures.pdf
70
13MI409:WIRELESS SENSOR NETWORKS
(Common to M.E CSE / M.Tech IT)
L T P C
3 0 0 3
Course Objectives:
To understand the basics of Sensor Networks
To learn various fundamental and emerging protocols of all layers
To study about the issues pertaining to major obstacles in establishment and efficient
management of sensor networks
To understand the nature and applications of sensor networks
To understand various security practices and protocols of Sensor Networks
Course Outcomes:
Analyze various protocols and its issues
Implement various routing protocols for Sensor networks
Use various security techniques in WSN
Create a Sensor network environment for different type of applications.
UNIT I SENSOR NETWORKS FUNDAMENTALS AND ARCHITECTURE 9
Introduction and Overview of WSNs, Application of WSNs, Challenges for Wireless Sensor
Networks, Enabling Technologies For Wireless SensorNetworks. Node Architecture- Sensing
Subsystem, Processing Subsystem, Communication Interfaces - Prototypes.
UNIT II NETWORKING SENSORS 9
Fundamentals of (Wireless) MAC Protocols, Low duty cycle protocols and wakeup concepts ,
Contention based Protocols Naming and Addressing- Fundamentals, Address and Name Management
in WSN, Assignment of MAC Addresses-Content based and geographic addressing
UNIT III SENSOR NETWORK MANAGEMENT AND PROGRAMMING 9
Sensor Management - Topology Control Protocols and Sensing Mode Selection Protocols - Time
Synchronization-Sender/sender synchronization, Sender/receiver synchronization - Localization and
Positioning Operating Systems and Sensor Network Programming Sensor Network Simulators - A
Lightweight and Energy-Efficient Architecture for WSNs.
UNIT IV SENSOR NETWORK DATABASES, PLATFORMS AND TOOLS 9
Sensor Database Challenges, Querying- Aggregation. Sensor Node Hardware Berkeley Motes,
Programming Challenges, Node-level software platforms, Node-level Simulators, State-centric
programming.
71
UNIT V SENSOR NETWORK SECURITY 9
Security in Sensor Networks Challenges of Security in WSNs-Security Attacks in sensor networks-
Detecting and Localizing Identity-Based Attacks in WSN, Protocols and Mechanisms for security-
Symmetric and Public keyCryptograpy, Key Management-Low-Energy Symmetric Key Distribution in
Wireless Sensor Networks, Defenses against attacks, Secure Protocols,TinySec, SPINS ,Localized
Encryption and Authentication Protocol,IEEE 802.15.4 and Zigbee security
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. KazemSohraby, Daniel Minoli,TaiebZnati Wireless Sensor Networks: Technology, Protocols, and
Applications John Wiley & Sons, Inc .2007
2. Holger Karl, Andreas willig, Protocols and Architectures for Wireless Sensor Networks, John
Wiley & Sons, Inc .2005.
3. Erdalayrc , ChunmingRong, Security in Wireless Ad Hoc and Sensor Networks, John Wiley
and Sons, 2009
4. WaltenegusDargie, Christian Poellabauer, Fundamentals of Wireless Sensor Networks Theory
and Practice, John Wiley and Sons, 2010
5. Miguel A. Lopez-Gomez, Member, IEEE, and Juan C. Tejero-Calado, Nonmember A Lightweight
and Energy-Efficient Architecture for Wireless Sensor Networks IEEE Transactions on Consumer
Electronics, Vol. 55, No. 3, AUGUST 2009
6. Yingying Chen, Member, IEEE, Jie Yang, Student Member, IEEE, Wade Trappe, Member, IEEE,
and Richard P. Martin, Member, IEEE Detecting and Localizing Identity-Based Attacks in
Wireless and Sensor Networks , IEEE transactions on vehicular technology, Vol. 59, No. 5,June
2010
7. KealanMcCusker, Member, IEEE, and Noel E. OConnor, Member, IEEE ,Low-Energy Symmetric
Key Distribution in Wireless Sensor Networks ,IEEE Transactions On Dependable and Secure
Computing, Vol. 8, No. 3, May/June 2011
13MC406: LANGUAGE TECHNOLOGIES L T P C
3 0 0 3
Course Objectives:
To understand the mathematical foundations needed for language processing
To understand the representation and processing of Morphology and Part-of Speech
Taggers
To understand different aspects of natural language syntax and the various methods used
for processing syntax
To understand different methods of disambiguating word senses
To know about various applications of natural language processing
To learn the indexing and searching processes of a typical information retrieval system and
to study NLP based retrieval systems
To gain knowledge about typical text categorization and clustering techniques
72
Course Outcomes:
Identify the different linguistic components of given sentences
Design a morphological analyser for a language of your choice using finite state automata
concepts
Implement a parser by providing suitable grammar and words
Discuss algorithms for word sense disambiguation
Build a tagger to semantically tag words using WordNet
Design an application that uses different aspects of language processing
UNIT I INTRODUCTION 9
Natural Language Processing Mathematical Foundations Elementary Probability Theory
Essential information Theory - Linguistics Essentials - Parts of Speech and Morphology Phrase
Structure Semantics Corpus Based Work
UNIT II WORDS 9
Collocations Statistical Inference n-gram Models Word Sense Disambiguation Lexical
Acquisition.
UNIT III GRAMMAR 9
Markov Models Part-of-Speech Tagging Probabilistic Context Free Grammars - Parsing.
UNIT IV INFORMATION RETRIEVAL 9
Information Retrieval Architecture Indexing - Storage Compression Techniques Retrieval
Approaches Evaluation - Search Engines - Commercial Search Engine Features Comparison -
Performance Measures Document Processing - NLP based Information Retrieval Information
Extraction.
UNIT V TEXT MINING 9
Categorization Extraction Based Categorization Clustering - Hierarchical Clustering - Document
Classification and Routing - Finding and Organizing Answers from Text Search Text
Categorization and Efficient Summarization using Lexical Chains Machine Translation - Transfer
Metaphor - Interlingual and Statistical Approaches.
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. Christopher D.Manning and HinrichSchutze, Foundations of Statistical Natural Language
Processing , MIT Press, 1999.
2. Daniel Jurafsky and James H. Martin, Speech and Language Processing , Pearson, 2008.
3. Ron Cole, J.Mariani, et.al Survey of the State of the Art in Human Language Technology,
Cambridge University Press, 1997.
4. Michael W. Berry, Survey of Text Mining: Clustering, Classification and Retrieval,
Springer Verlag, 2003.
13MC407:ENERGY AWARE COMPUTING L T P C
(Common to M.E CSE / M.Tech IT) 3 0 0 3
Course Objectives:
To know the fundamental principles energy efficient devices
To study the concepts of Energy efficient storage
73
To introduce energy efficient algorithms
To enable the students to know energy efficient techniques involved to support real-time
systems.
To study Energy aware applications
Course Outcomes:
Design Power efficient architecture Hardware and Software.
Analyze power and performance trade off between various energy aware storage devices.
Implement various energy aware algorithms.
Restructure the software and Hardware for Energy aware applications.
Explore the Energy aware applications
UNIT I INTRODUCTION 9
Energy efficient network on chip architecture for multi core system-Energy efficient MIPS CPU core
with fine grained run time power gating Low power design of Emerging memory technologies.
UNIT II ENERGY EFFICIENT STORAGE 9
Disk Energy Management-Power efficient strategies for storage system-Dynamic thermal
management for high performance storage systems-Energy saving technique for Disk storage
systems
UNIT III ENERGY EFFICIENT ALGORITHMS 9
Scheduling of Parallel Tasks Task level Dynamic voltage scaling Speed Scaling Processor
optimization- Memetic Algorithms Online job scheduling Algorithms
UNIT IV REAL TIME SYSTEMS 9
Multi processor system Real Time tasks- Energy Minimization Energy aware scheduling-
Dynamic Reconfiguration- Adaptive power management-Energy Harvesting Embedded system
UNIT V ENERGY AWARE APPLICATIONS 9
On chip network Video codec Design Surveillance camera- Low power mobile storage.
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. Ishfaq Ah mad, Sanjay Ranka, Handbook of Energy Aware and Green Computing,
Chapman and Hall/CRC, 2012
2. Chong-Min Kyung, Sungiooyoo, Energy Aware system design Algorithms and
Architecture, Springer, 2011.
3. Bob steigerwald ,Chris:Luero, Energy Aware computing, Intel Press,2012.
4. RameshKarri, David Goodman Eds, System Level Power Optimization for Wireless
Multimedia Communication Power AwareComputing , Kluwer AcademicPublishers, 2002
WEB REFERENCES:
1. http://www.inf.ed.ac.uk/teaching/courses/eac/
13MC408 : INFORMATION STORAGE MANAGEMENT L T P C
3 0 0 3
Course Objectives:
To elucidate the challenges in data storage and management
To exemplify the architecture of storage systems
To illustrate the different networked storage options
74
To identify the failure in storage infrastructure and solutions to mitigate
To illustrate about the storage virtualization.
Course Outcomes:
Efficiently handle challenges in data storage and management
Explore the various storage systems
Apply storage options for different application environments
Ensure information availability and business continuity
Expertise in storage virtualization technologies
UNIT I INTRODUCTION TO STORAGE TECHNOLOGY 9
Review data creation and the amount of data being created and understand the value of data to a
business- challenges in data storage and data management- Solutions available for data storage-
Core elements of a data center infrastructure- role of each element in supporting business
activities
UNIT II STORAGE SYSTEMS ARCHITECTURE 9
Hardware and software components of the host environment- Key protocols and concepts used by
each component-Physical and logical components of a connectivity environment-Major physical
components of a disk drive and their function- logical constructs of a physical disk- access
characteristics and performance Implications- Concept of RAID and its components- Different RAID
levels and their suitability for different application environments: RAID 0, RAID 1, RAID 3, RAID 4,
RAID 5, RAID 0+1, RAID 1+0, RAID 6- Compare and contrast integrated and modular storage
systems- High-level architecture and working of an intelligent storage system
UNIT III INTRODUCTION TO NETWORKED STORAGE 9
Evolution of networked storage, Architecture, components, and topologies of FC-SAN, NAS, and
IP-SAN- Benefits of the different networked storage options- understand the need for long-term
archiving solutions and describe how CAS full fill the need- understand the appropriateness of the
different networked storage options for different application environments
UNIT IV INFORMATION AVAILABILITY, MONITORING & MANAGING
DATACENTER
9
List reasons for planned/unplanned outages and the impact of downtime- Impact of downtime -
Differentiate between business continuity (BC) and disaster recovery (DR) -RTO and RPO- Identify
single points of failure in a storage infrastructure and list solutions to mitigate these failures-
Architecture of backup/recovery and the different backup/ recovery topologies- replication
technologies and their role in ensuring information availability and business continuity- Remote
replication technologies and their role in providing disaster recovery and business continuity
capabilities. Identify key areas to monitor in a data center- Industry standards for data center
monitoring and management- Key metrics to monitor for different components in a storage
infrastructure- Key management tasks in a data center
UNIT V SECURING STORAGE AND STORAGE VIRTUALIZATION 9
Information security- Critical security attributes for information systems- Storage security
domains- List and analyzes the common threats in each domain- Virtualization technologies-
block-level and file-level virtualization technologies and processes
TOTAL: 45 PERIODS
75
REFERENCE BOOKS:
1. EMC Corporation, Information Storage and Management, Wiley, India.
2. Robert Spalding, Storage Networks: The Complete Reference, Tata McGraw Hill ,
Osborne, 2003.
3. Marc Farley, Building Storage Networks, Tata McGraw Hill ,Osborne, 2001.
4. Additional resource material on www.emc.com/resource-library/resource-library.esp
WEB REFERENCES:
1. http://www.itracs.com/what-is-data-center-infrastructure-management/
http://www.webopedia.com/TERM/R/RAID.html
2. http://www.nas-san.com/differ.html
3. http://omnitraining.net/storage-networking-101/319-storage-virtualization-explained
4. http://www.computerweekly.com/feature/A-guide-to-storage-virtualization
13MC409: SOFTWARE PROCESS AND PROJECT MANAGEMENT L T P C
3 0 0 3
Course Objectives:
To Explain the software process framework
To Discuss managed and optimized software process
To Introduce team software process and define team roles
To Define project management process group
To discuss the project management life cycle and strategies
To Examine the ways of managing multiple team project
Course Outcomes:
Elaborate the software process framework
Able to manage and optimize the software process
Comprehend team software process and team roles
Establish the project management process group
Identify the project management life cycle for problems and establish the strategies
To manage the multiple team project
UNIT I DEFINED AND MANAGED PROCESS 9
Software Maturity Framework Software Standards Inspections Software Engineering Process
Group - Data Gathering and Analysis Managing Software Quality
UNIT II OPTIMIZING PROCESS & TEAM SOFTWARE PROCESS 9
Defect Prevention Automating the Software Process Managing Software Contracts - Team
Software Process Team Roles - Team Leader Role Development Manager Role Planning
Manager Role Quality / Process Manager Role Support Manager Role
UNIT III PROJECT MANAGEMENT PROCESS GROUPS 9
Introduction to project andProject Management Process Groups - Project Scope Project Planning
Project Launching Monitoring and Controlling of a Project Closing a Project
UNIT IV PROJECT MANAGEMENT LIFE CYCLES AND STRATEGIES 9
Project Management Landscape Traditional Project Management Critical Chain Project
Management Agile Project Management Extreme Project Management
76
UNIT V PROJECT MANAGEMENT INFRASTRUCTURE 9
Defining Process and Practice Maturity Measuring Project Management Process Applying CPIM
TO Business Process Managing Multiple Team Projects
TOTAL: 45 PERIODS
REFERENCE BOOKS:
1. Watts S. Humphrey, Managing the Software Process, Pearson Education, 2006
2. Watts S. Humphrey, Introduction to the Team Software Process, Pearson Education,
2006
3. Robert K.Wysocki, Effective Project Management: Traditional, Agile, Extreme, 6
th
Edition, Wiley, 2011
4. Roger S.Pressman, Software Engineering, 7
th
Edition, 2010
You might also like
- SEPM LAB Questions1Document18 pagesSEPM LAB Questions1rishikarthickNo ratings yet
- Ug Degree CertificateDocument1 pageUg Degree CertificaterishikarthickNo ratings yet
- Jayabal Palanisamy Male R.Palaniamy P.Rajammal Abinaya Karunanithi Female K.karunanithi K.kalaiyarasiDocument7 pagesJayabal Palanisamy Male R.Palaniamy P.Rajammal Abinaya Karunanithi Female K.karunanithi K.kalaiyarasirishikarthickNo ratings yet
- Reading Screening Paper 1 - 2016-17Document10 pagesReading Screening Paper 1 - 2016-17rishikarthick100% (1)
- Reading Screening Paper 1 - 2016-17Document10 pagesReading Screening Paper 1 - 2016-17rishikarthick100% (1)
- Rathinam Technical Campus (Institute of Technology) Eachanari, Coimbatore - 641021Document2 pagesRathinam Technical Campus (Institute of Technology) Eachanari, Coimbatore - 641021rishikarthickNo ratings yet
- Reading Screening Paper 3 - 2016-17Document10 pagesReading Screening Paper 3 - 2016-17rishikarthick54% (48)
- Part ADocument11 pagesPart ArishikarthickNo ratings yet
- Home Student Detail Faculty Detail Examina뛕 Reports Admin U뛕 Entry Status Help LogoutDocument9 pagesHome Student Detail Faculty Detail Examina뛕 Reports Admin U뛕 Entry Status Help LogoutrishikarthickNo ratings yet
- Ex. No. 1b T T: Insert Table in Insert TabDocument2 pagesEx. No. 1b T T: Insert Table in Insert TabrishikarthickNo ratings yet
- Btech Syll Cse r2013-14Document245 pagesBtech Syll Cse r2013-14rishikarthickNo ratings yet
- CP7111Document2 pagesCP7111Pandiaraj ANo ratings yet
- Research and Design IDocument16 pagesResearch and Design ISoumyadeep MaityNo ratings yet
- Index PageDocument41 pagesIndex PagerishikarthickNo ratings yet
- CS6551Document103 pagesCS6551rishikarthick0% (1)
- Unit - II Understanding Internet BasicsDocument24 pagesUnit - II Understanding Internet BasicsrishikarthickNo ratings yet
- CP7102-Advanced Datastructure and Algorithm Question BankDocument4 pagesCP7102-Advanced Datastructure and Algorithm Question BankMohit UppalNo ratings yet
- Ads Unit-2Document74 pagesAds Unit-2Velumani BalakrishnanNo ratings yet
- CD LabDocument14 pagesCD LabrishikarthickNo ratings yet
- Iterative and Recursive Algorithms GuideDocument60 pagesIterative and Recursive Algorithms GuideVelumani BalakrishnanNo ratings yet
- Programs For LAB I YearDocument3 pagesPrograms For LAB I YearrishikarthickNo ratings yet
- V-VI Semester Batch (2012-2016)Document12 pagesV-VI Semester Batch (2012-2016)rishikarthickNo ratings yet
- Lecture 21Document24 pagesLecture 21rishikarthickNo ratings yet
- CS6301 U5Document16 pagesCS6301 U5rishikarthickNo ratings yet
- Cs 6503 Toc Question BankDocument27 pagesCs 6503 Toc Question BankrishikarthickNo ratings yet
- C SyntaxDocument14 pagesC SyntaxrishikarthickNo ratings yet
- Lecture 22Document36 pagesLecture 22rishikarthickNo ratings yet
- Bab IiDocument601 pagesBab IiHendra JurbonNo ratings yet
- IoT Workshop for EngineersDocument1 pageIoT Workshop for EngineersrishikarthickNo ratings yet
- A Cluster-Chain Based Routing Protocol For Balancing Energy Consumption in Wireless Sensor NetworksDocument16 pagesA Cluster-Chain Based Routing Protocol For Balancing Energy Consumption in Wireless Sensor NetworksrishikarthickNo ratings yet
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (890)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (587)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (265)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (119)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- ALU 7450 ESS - DataSheetDocument10 pagesALU 7450 ESS - DataSheetفيصل باديNo ratings yet
- Preventing Users From Accessing Jira Applications During Backups - Atlassian DocumentationDocument2 pagesPreventing Users From Accessing Jira Applications During Backups - Atlassian DocumentationShyamsundar VenkataramanNo ratings yet
- Set B - Tle ExamDocument13 pagesSet B - Tle ExamMark Anthony LibecoNo ratings yet
- Sample Explore Coding Through Scratch WorksheetsDocument10 pagesSample Explore Coding Through Scratch WorksheetsArmaMaretaNo ratings yet
- Operation ManualDocument47 pagesOperation ManualnavnetNo ratings yet
- Data Communication and Networking Basic MCQ Set - Behrouz A ForouzanDocument12 pagesData Communication and Networking Basic MCQ Set - Behrouz A ForouzanAnil SumanNo ratings yet
- Team Together 2 - MID YEAR EXAM WorksheetDocument10 pagesTeam Together 2 - MID YEAR EXAM WorksheetJennifer Elizabeth Macías MacíasNo ratings yet
- 7 Methods to Get a Free VPS Under 40 CharactersDocument9 pages7 Methods to Get a Free VPS Under 40 Charactersbaomuahe399100% (1)
- In This Assignment, You Will Create A Story Map Based or The Remote System - The Mobile App' - Google SearchDocument2 pagesIn This Assignment, You Will Create A Story Map Based or The Remote System - The Mobile App' - Google SearchA.G. AshishNo ratings yet
- D-10 LIS ManualDocument21 pagesD-10 LIS ManualAla'a HimourNo ratings yet
- Support Procedure For DN - Webhosting and Email Service - FInalDocument8 pagesSupport Procedure For DN - Webhosting and Email Service - FInalberiNo ratings yet
- Telecom Billing - Usage Capturing - TutorialspointDocument3 pagesTelecom Billing - Usage Capturing - TutorialspointChristopher AiyapiNo ratings yet
- Semantic Web Technologies in AEC IndustryDocument21 pagesSemantic Web Technologies in AEC IndustrykarinedepaulabsantosNo ratings yet
- Redhat - Planning-Identity-ManagementDocument64 pagesRedhat - Planning-Identity-ManagementGuntur KsNo ratings yet
- Spicejet - Test PlanDocument13 pagesSpicejet - Test PlanNarendra GowdaNo ratings yet
- Jacksonville: Ashley FabiaDocument11 pagesJacksonville: Ashley FabiaAshley FabiaNo ratings yet
- Importance of Telecom OSS and BSSDocument24 pagesImportance of Telecom OSS and BSSDolly Roliyan50% (2)
- SAP - Simplification List 1709 - Upgarde Guide - 20180201Document20 pagesSAP - Simplification List 1709 - Upgarde Guide - 20180201VickyNo ratings yet
- SOL5379 - Overview of HTTP Compression and Chunked ContentDocument2 pagesSOL5379 - Overview of HTTP Compression and Chunked ContentMahmoudAbdElGhaniNo ratings yet
- Plan View: PreliminaryDocument1 pagePlan View: PreliminaryArun KumarNo ratings yet
- DeploymentGuide PulseConnectSecure-SAMLauthDocument28 pagesDeploymentGuide PulseConnectSecure-SAMLauthNetsys BilisimNo ratings yet
- How To Start A Record Label - Marketing ChecklistDocument2 pagesHow To Start A Record Label - Marketing Checklistgibran jalu jos100% (1)
- NetAcad - ENSA - Check Your Understanding (Questions)Document22 pagesNetAcad - ENSA - Check Your Understanding (Questions)tester testerNo ratings yet
- NSTP 6101 National Service Training Program MANUSCRIPTDocument91 pagesNSTP 6101 National Service Training Program MANUSCRIPTMary Ann TaguinodNo ratings yet
- Dijoux Distance Learning Faq Parent SheetDocument2 pagesDijoux Distance Learning Faq Parent Sheetapi-520757309No ratings yet
- READMEDocument2 pagesREADMEiNo ratings yet
- SWIFT Customer Security Controls PolicyDocument38 pagesSWIFT Customer Security Controls PolicyHTM100% (3)
- Annotated BibliographyDocument4 pagesAnnotated Bibliographyapi-242174106No ratings yet
- Search Google: Back Links & PR Outcomes SEO SEMDocument2 pagesSearch Google: Back Links & PR Outcomes SEO SEMIvicaGranićNo ratings yet
- Id Scribd ComDocument2 pagesId Scribd ComIcha DeviNo ratings yet