Professional Documents
Culture Documents
A Survey On Protecting Privacy Using Biometric of Fingerprint Combination
Uploaded by
seventhsensegroup0 ratings0% found this document useful (0 votes)
20 views3 pagesWith the extensive applications of fingerprint
techniques in authentication systems, protecting the
privacy of the fingerprint becomes an important issue.
Traditional encryption is not sufficient for fingerprint
privacy protection because decryption is required before
the fingerprint matching, which exposes the fingerprint to
the attacker. Therefore, in recent years, significant efforts
have been put into developing specific protection
techniques for fingerprint. In this paper various methods
for recognizing fingerprint has been surveyed. These
methods has been compared against the proposed method
of SIFT Based Ridge enhanced fingerprint recognization
method. Thus each and every method in literature
provides satisfiable result and lacks the result in analysis
when compared with the proposed research.
Original Title
A Survey on Protecting Privacy Using Biometric of Fingerprint
Combination
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentWith the extensive applications of fingerprint
techniques in authentication systems, protecting the
privacy of the fingerprint becomes an important issue.
Traditional encryption is not sufficient for fingerprint
privacy protection because decryption is required before
the fingerprint matching, which exposes the fingerprint to
the attacker. Therefore, in recent years, significant efforts
have been put into developing specific protection
techniques for fingerprint. In this paper various methods
for recognizing fingerprint has been surveyed. These
methods has been compared against the proposed method
of SIFT Based Ridge enhanced fingerprint recognization
method. Thus each and every method in literature
provides satisfiable result and lacks the result in analysis
when compared with the proposed research.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
20 views3 pagesA Survey On Protecting Privacy Using Biometric of Fingerprint Combination
Uploaded by
seventhsensegroupWith the extensive applications of fingerprint
techniques in authentication systems, protecting the
privacy of the fingerprint becomes an important issue.
Traditional encryption is not sufficient for fingerprint
privacy protection because decryption is required before
the fingerprint matching, which exposes the fingerprint to
the attacker. Therefore, in recent years, significant efforts
have been put into developing specific protection
techniques for fingerprint. In this paper various methods
for recognizing fingerprint has been surveyed. These
methods has been compared against the proposed method
of SIFT Based Ridge enhanced fingerprint recognization
method. Thus each and every method in literature
provides satisfiable result and lacks the result in analysis
when compared with the proposed research.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 3
International Journal of Computer Trends and Technology (IJCTT) volume 10 number 1 Apr 2014
ISSN: 2231-2803 http://www.ijcttjournal.org Page58
A Survey on Protecting Privacy Using Biometric of Fingerprint
Combination
B.Janani M.Sc
1
, Dr.N.Radha M.Sc, M.phil, Phd
2
1
Research Scholar, Department of Computer Application, PSGR Krishnammal College for Women,
Coimbatore, India.
2
Assistant Professor, Department of Computer Application, PSGR Krishnammal College for Women,
Coimbatore, India.
Abstract With the extensive applications of fingerprint
techniques in authentication systems, protecting the
privacy of the fingerprint becomes an important issue.
Traditional encryption is not sufficient for fingerprint
privacy protection because decryption is required before
the fingerprint matching, which exposes the fingerprint to
the attacker. Therefore, in recent years, significant efforts
have been put into developing specific protection
techniques for fingerprint. In this paper various methods
for recognizing fingerprint has been surveyed. These
methods has been compared against the proposed method
of SIFT Based Ridge enhanced fingerprint recognization
method. Thus each and every method in literature
provides satisfiable result and lacks the result in analysis
when compared with the proposed research.
I. INTRODUCTION
Recently, fingerprint recognition is one of the leading
biometric technologies based on fingerprint distinctiveness,
persistence and ease of attainment. Even though there are
many real applications utilizing this technology, its problems
are still not completely solved, particularly in poor quality
fingerprint images and when low-cost acquisition devices with
a small area are assumed
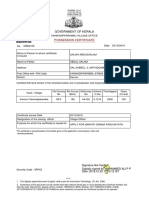
Fig.1 Fingerprint Recognition process
The basic process of fingerprint recognition process is
shown in the above figure 1. In fingerprint recognition
process, the significant step which involves on system
accuracy is matching between template and query fingerprint.
Various solutions are designed to enlarge this steps accuracy.
These matching algorithms may be classified into three types
such as minutiae-based, correlation-based and feature-based
approaches. Still, based on analysis, the score of these
algorithms is not high (particularly in case fingerprints are of
the same finger but they are rotated or the intersection is
moreover small). Consequently, its essential to design a
model for standardized fingerprint template so as to improve
matching score.
Exploring the possibility of generating a template in the
direction of conventional fingerprint approach represents a
joint identity through a mixing process. In particular, the
digital identity has been created by mixing the fingerprints of
two individuals to generate a single fingerprint in turn defines
the joint identity. Figure 2 refers to the flow of ridge patterns
of the fingerprint in the tip of the finger. Irregularities in local
regions of the fingertip have been exhibited, referred as
minutiae points. The distribution of these minutiae points,
with the associated ridge structure, is considered to be
different for each fingerprint.
Fig 2. A design of mixing fingerprints of two different
individuals to generate a mixed fingerprint representing
their joint identity
To provide better verification and authentication various
methods of fingerprint recognition can be surveyed in the
following literature.
International Journal of Computer Trends and Technology (IJCTT) volume 10 number 1 Apr 2014
ISSN: 2231-2803 http://www.ijcttjournal.org Page59
II. FINGRPRINT AUTHENTICATION
A. BIO HASHING APPROACH
In [1] Teoh et al, presented a bio hashing approach by
estimating the inner products among a pseudorandom number
that is probably said to be key and users fingerprint features.
These two factors of Bio Hashing has major functional
advantages over singular biometrics or token usage, namely
clear separation of the genuine and the imposter populations
and zero EER(Equal error rate) level, thus moderate the
suffering from increased amount of FRR while eliminate the
FAR(False acceptance ratio). The method of generating a
token of pseudo-randomvectors happening only once for an
individual, it can be assumed secure in the case that there is no
mode to recover the fingerprint data by attaining on the token
(one-way transformation). Accordingly, a sole compact code
per person should be attained, which is highly advantageous in
a secure environment and outperforms the standard
verification scheme, assumed as a weak-security systemfor it
needs to admit an external database of user data. Additionally,
Bio Hashing technique also dealt with the invasion of privacy
problem, such as biometric fabrication.
B. NON INVERTIBLE TRANSFORM APPROACH
In [2] Ratha et al presented an approach to produce
cancellable fingerprint templates by applying noninvertible
transforms on the minutiae. The noninvertible transform is
conducted by a key; it normally leads to a reduction in
matching accuracy. Fundamentally, a user can be given as
numerous biometric identifiers as needed by producing a new
transformation key. Original identifiers can be ignored and
replaced when compromised. The performance of some
algorithms such as surface folding transformations and
Cartesian, polar of the minutiae positions has been compared.
It is established through numerous experiments that we can
attain revocability and stop cross-matching of biometric
databases. It is also shown that the changes are noninvertible
by indicating that it is computationally as hard to recover the
original biometric identifier from a changed version as
through randomguessing.
C. FUZZY-FAULT APPROACH
In [3] Nandakumar et al. presented fuzzy fault on the
minutiae in turns susceptible to the key-inversion attack. The
fuzzy vault construct is a biometric cryptosystem that provides
secure system for both the secret key and the biometric
template through connecting them within a cryptographic
structure. A fully automatic implementation of the fuzzy vault
scheme is presented based on fingerprint minutiae. As the
fuzzy vault holds only a transformed report of the template,
aligning such a query fingerprint with the template is a
challenging job. High curvature points derived from the
fingerprint orientation field has been extracted and used them
as supporting data to align the query minutiae and template.
The supporting data itself do not disclose any information
about the minutiae template, however contain enough
information to align the template and query fingerprints
perfectly. In addition, a minutiae matcher has been applied
during decoding to justify nonlinear distortion and this show
the ways to significant improvement in the genuine accept
rate.
D. VISUAL CRYPTOGRAPHIC SCHEME
In [4] Othman presented visual cryptography for guarding
the privacy of biometrics. The fingerprint image is partitioned
by utilizing a visual cryptography scheme to create two noise-
like images (referred as sheets) which is stored in two distinct
databases. While authentication, the two sheets are stacked to
create a temporary fingerprint image for matching. The
benefit of this system is that in which the identity of the
biometrics is never exposed to the attacker in a single
database. Still, it needs two distinct databases to work jointly,
which is not useful in same applications.
E. MULTI BIOMETRIC TEMPLATE
In [5] Yanikoglu et al.presented two distinct fingerprints
into a single identity either in the image level or in the feature
level. In this the idea of combining two different fingerprints
into a new identity is first projected, where the novel identity
is created by combining the minutiae positions extracted from
the two different fingerprints. The positions of original
minutiae of each fingerprint can be defended in the new
identity. Yet, it is easy for the attacker to identify such a new
identity since it holds more minutiae positions than that of an
original fingerprint.
In [6] Arun Ross presented the method in which an input
fingerprint image is mixed with another fingerprint that is
froma different finger, so as to produce a new mixed image
that produces difficult to understand the identity of the
original fingerprint. Mixing fingerprints produces a new unit
that looks like a reasonable fingerprint and, therefore, (a) it
can be practiced by traditional fingerprint algorithms and (b)
an intruder may not be able to decide if a given print is mixed
or not. In order to mix two fingerprints, each fingerprint is
partitioned into two components, viz., the spiral and
continuous components. Subsequent to the pre-aligning the
two components of each fingerprint, the continuous
component of one fingerprint is united with the spiral
component of the other fingerprint image so as to generate a
mixed fingerprint.
In [7] Eren Camlikaya et al. presented a multimodal
biometric verification system by mixing fingerprint and voice
modalities. The framework combines the two modalities at the
template level, using multibiometric templates. The
combination of fingerprint and voice data productively
diminishes privacy concerns through hiding the minutiae
points from the fingerprint, between the artificial points
produced by the features which are attained fromthe spoken
utterance of the speaker.
International Journal of Computer Trends and Technology (IJCTT) volume 10 number 1 Apr 2014
ISSN: 2231-2803 http://www.ijcttjournal.org Page60
.
III. CONCLUSION
In the present work, various methods of fingerprint
recognition have been surveyed. The methods based on Bio
hashing approach, Non invertible transform approach
provides better accuracy however it is vulnerable to intrusion
and linkage attacks when both the key and the transformed
template are stolen. Then Fuzzy-fault approach provides better
recognition since it vulnerable to the key-inversion attack.
Next the scheme of visual cryptography is used for the
purpose of authentication and confidentiality however it
requires two separate databases to work together, which is not
practical in same applications. Finally, Multibiometric
template scheme has been used for providing robust integrity
among fingerprint templates and difficult for the attacker to
distinguish a mixed fingerprint fromthe original fingerprints.
However the ridge enhancement is not addressed in these
approaches when the user fingerprint is considered in a least
frequency model. Thus the proposed scheme outperforms
these model and authentication has been done through the
ridge enhancement based on SIFT based approach
.
REFERENCES
[1]. B. J . A. Teoh, C. L. D. Ngo, and A. Goh, Biohashing: Two factor
authentication featuring fingerprint data and tokenised random
number, Pattern Recognit., vol. 37, no. 11, pp. 22452255, 2004.
[2]. N. K. Ratha, S. Chikkerur, J. H. Connell, and R. M. Bolle,
Generating cancellable fingerprint templates, IEEE Trans.
Pattern Anal. Mach. Intell., vol. 29, no. 4, pp. 56172, Apr. 2007.
[3]. K. Nandakumar, A. K. J ain, and S. Pankanti, Fingerprint-based
fuzzy vault: Implementation and performance, IEEE Trans. Inf.
Forensics Security, vol. 2, no. 4, pp. 74457, Dec. 2007.
[4]. Ross and A. Othman, Visual cryptography for biometric
privacy, IEEE Trans. Inf. Forensics Security, vol. 6, no. 1, pp.
7081,Mar. 2011
[5]. Yanikoglu and A. Kholmatov, Combining multiple biometrics to
protect privacy, in Proc. ICPR- BCTP Workshop, Cambridge,
U.K., Aug. 2004.
[6]. Ross and A. Othman, Mixing fingerprints for template security
and privacy, in Proc. 19th Eur. Signal Proc. Conf. (EUSIPCO),
Barcelona, Spain, Aug. 29Sep. 2, 2011.
[7]. E. Camlikaya, A. Kholmatov, and B. Yanikoglu, Multi-biometric
templates using fingerprint and voice, Proc. SPIE, vol. 69440I,
pp. 69440I-169440I-9, 2008
You might also like
- Deep BiometricsFrom EverandDeep BiometricsRichard JiangNo ratings yet
- Fingerprint Matching Approach Based On Bifurcation MinutiaeDocument8 pagesFingerprint Matching Approach Based On Bifurcation MinutiaeJournalofICTNo ratings yet
- Enhance Security Using Cancellable Biometric Key GenerationDocument11 pagesEnhance Security Using Cancellable Biometric Key GenerationlambanaveenNo ratings yet
- Literature Review: 2.1 by A.K. Jain, S. Pankanti, and S. Prabhakar in 2000 Ref.Document3 pagesLiterature Review: 2.1 by A.K. Jain, S. Pankanti, and S. Prabhakar in 2000 Ref.Anonymous l5X3VhTNo ratings yet
- Comparative Analysis of Minutiae Based Fingerprint Matching AlgorithmsDocument13 pagesComparative Analysis of Minutiae Based Fingerprint Matching AlgorithmsAnonymous Gl4IRRjzNNo ratings yet
- 2006 MMUA FingerprNormQ AlonsoDocument8 pages2006 MMUA FingerprNormQ Alonsolmtp80No ratings yet
- Development of open-CV Framework For Minutiae Extraction and Matching of FingerprintsDocument5 pagesDevelopment of open-CV Framework For Minutiae Extraction and Matching of FingerprintsSunitha ManamNo ratings yet
- 1.1 Biometrics Authentication TechniquesDocument55 pages1.1 Biometrics Authentication Techniquesusharani manickamNo ratings yet
- Fingerprint Recognition SystemDocument26 pagesFingerprint Recognition SystemAshley JaswalNo ratings yet
- Writer-Independent Offline Signature Verification Using Deep LearningDocument7 pagesWriter-Independent Offline Signature Verification Using Deep LearningIJRASETPublicationsNo ratings yet
- Implementation of Minutiae Based Fingerprint Identification System Using Crossing Number ConceptDocument6 pagesImplementation of Minutiae Based Fingerprint Identification System Using Crossing Number ConceptseventhsensegroupNo ratings yet
- FF PDFDocument4 pagesFF PDFShweta MullurNo ratings yet
- Black BookDocument21 pagesBlack Bookदेवेश सिंह राजपूतNo ratings yet
- Eng-A Novel Multimodal Biometric Scheme-P. Aruna KumariDocument12 pagesEng-A Novel Multimodal Biometric Scheme-P. Aruna KumariImpact JournalsNo ratings yet
- PDF/JCSSP 2012 431 435Document5 pagesPDF/JCSSP 2012 431 435jit_72No ratings yet
- An Embedded Real-Time Biometric Recognition System For Defense SystemDocument5 pagesAn Embedded Real-Time Biometric Recognition System For Defense SystemInternational Organization of Scientific Research (IOSR)No ratings yet
- RSA Key Generation Using Combination of Fingerprints: Sharda Singh, Dr. J. A. LaxminarayanaDocument6 pagesRSA Key Generation Using Combination of Fingerprints: Sharda Singh, Dr. J. A. LaxminarayanahmmohanNo ratings yet
- IJAERS-SEPT-2014-021-A Hybrid Algorithm For Fingerprint Recognition SystemDocument6 pagesIJAERS-SEPT-2014-021-A Hybrid Algorithm For Fingerprint Recognition SystemIJAERS JOURNALNo ratings yet
- Vu Watermarking MultimodalDocument9 pagesVu Watermarking MultimodallabbasmohammedamineNo ratings yet
- Authentication Using Finger Knuckle Print Techniques: (Volume2, Issue4) Available Online atDocument7 pagesAuthentication Using Finger Knuckle Print Techniques: (Volume2, Issue4) Available Online atakki11111No ratings yet
- Data Level Fusion For Multi Biometric System Using Face and FingerDocument5 pagesData Level Fusion For Multi Biometric System Using Face and FingerIjarcsee JournalNo ratings yet
- h200010j Katuruza G W MTECH SE Biometric Fingerprint AuthentificationDocument25 pagesh200010j Katuruza G W MTECH SE Biometric Fingerprint AuthentificationWalter G KaturuzaNo ratings yet
- Enhanced Thinning Based Finger Print RecognitioDocument14 pagesEnhanced Thinning Based Finger Print RecognitioJames Moreno100% (1)
- Finger Print Recognition PaperDocument4 pagesFinger Print Recognition PaperNakib Aman TurzoNo ratings yet
- Elbeqqal 2018Document9 pagesElbeqqal 2018Dickson Scott Rosales CanoNo ratings yet
- 1 s2.0 S0031320323006337 MainDocument11 pages1 s2.0 S0031320323006337 MainDidedla;,No ratings yet
- Fast Multimodal Biometric Approach Using Dynamic Fingerprint Authentication and Enhanced Iris FeaturesDocument45 pagesFast Multimodal Biometric Approach Using Dynamic Fingerprint Authentication and Enhanced Iris FeaturesShruti SharmaNo ratings yet
- Multimodal Biometric Identification System Based On Iris & FingerprintDocument8 pagesMultimodal Biometric Identification System Based On Iris & FingerprintInternational Organization of Scientific Research (IOSR)No ratings yet
- Handwritten Signature Verification Using Instance Based LearningDocument4 pagesHandwritten Signature Verification Using Instance Based Learningsurendiran123No ratings yet
- On Fingerprint Template Synthesis: Wei-Yun Yau, Kar-Ann Toh, Xudong Jiang, Tai-Pang Chen and Juwei LuDocument6 pagesOn Fingerprint Template Synthesis: Wei-Yun Yau, Kar-Ann Toh, Xudong Jiang, Tai-Pang Chen and Juwei LuLucas AssisNo ratings yet
- Providing Multi-Authentication Using Multi-Biometric Cryptosystem For Enhancing SecurityDocument3 pagesProviding Multi-Authentication Using Multi-Biometric Cryptosystem For Enhancing SecurityInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- A Simple Text-Based Shoulder Surfing ResistantDocument9 pagesA Simple Text-Based Shoulder Surfing Resistantpriyanka badgujarNo ratings yet
- Biometric Fingerprint Authentication by Minutiae Extraction Using USB Token SystemDocument5 pagesBiometric Fingerprint Authentication by Minutiae Extraction Using USB Token SystemhmmohanNo ratings yet
- New Intuition On Ear Authentication With Gabor Filter Using Fuzzy VaultDocument7 pagesNew Intuition On Ear Authentication With Gabor Filter Using Fuzzy Vaultkavi priyaNo ratings yet
- Comparison of Signature Forgery Detection ArchitecturesDocument13 pagesComparison of Signature Forgery Detection ArchitecturesIJRASETPublicationsNo ratings yet
- Ip 55 672 677 PDFDocument6 pagesIp 55 672 677 PDFlambanaveenNo ratings yet
- Neural Network in Matching Fingerprint (Abstract)Document7 pagesNeural Network in Matching Fingerprint (Abstract)Aayush GargNo ratings yet
- User Interface Design of The Interactive Fingerprint Recognition (INFIR) SystemDocument7 pagesUser Interface Design of The Interactive Fingerprint Recognition (INFIR) System060920720No ratings yet
- Fingerprint Recognition Strategies Based On A Fuzzy CommitmentDocument4 pagesFingerprint Recognition Strategies Based On A Fuzzy CommitmentYashaswini PraveenNo ratings yet
- An Embedded Real-Time Finger-Vein Recognition SystemDocument6 pagesAn Embedded Real-Time Finger-Vein Recognition SystemArun GopinathNo ratings yet
- Cancellable BiometricsDocument6 pagesCancellable BiometricsSai SidharthNo ratings yet
- FingerprintDocument79 pagesFingerprintjagadeesh jagadeNo ratings yet
- Biometric Authentication Using Fingerprint Recognition: Rajiv Gandhi Institute of TechnologyDocument7 pagesBiometric Authentication Using Fingerprint Recognition: Rajiv Gandhi Institute of TechnologySarvesh DesaiNo ratings yet
- Mean-Discrete Algorithm For Individuality RepresentationDocument10 pagesMean-Discrete Algorithm For Individuality RepresentationBayan OmarNo ratings yet
- Estimation of Human Age Using Ear Recognition by KNN&SVM: A. Kavipriya A. MuthukumarDocument7 pagesEstimation of Human Age Using Ear Recognition by KNN&SVM: A. Kavipriya A. Muthukumarkavi priyaNo ratings yet
- Report On Fingerprint Recognition SystemDocument9 pagesReport On Fingerprint Recognition Systemaryan singhalNo ratings yet
- Behavioral Biometrics: MembersDocument4 pagesBehavioral Biometrics: MembersGondala SatvarshNo ratings yet
- A Certificate of Identification Growth Through Multimodal Biometric SystemDocument5 pagesA Certificate of Identification Growth Through Multimodal Biometric SystemInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- International Journal of Engineering Research and Development (IJERD)Document12 pagesInternational Journal of Engineering Research and Development (IJERD)IJERDNo ratings yet
- Detection and Rectification PDFDocument14 pagesDetection and Rectification PDFBala_9990No ratings yet
- Fingerprint Image Enhancement: Iterative Fast Fourier Transform Algorithm and Performance EvaluationDocument10 pagesFingerprint Image Enhancement: Iterative Fast Fourier Transform Algorithm and Performance EvaluationProdi Tmj-pnlNo ratings yet
- Entropy Based Local Binary Pattern ELBP Feature Extracti 2019 Alexandria EDocument12 pagesEntropy Based Local Binary Pattern ELBP Feature Extracti 2019 Alexandria ESoumitra DasNo ratings yet
- A Novel Retina Based Biometric Privacy Using Visual CryptographyDocument5 pagesA Novel Retina Based Biometric Privacy Using Visual CryptographyJothibasu MarappanNo ratings yet
- Biometrics: Thousands of Years Earlier Physiological Parameters Such As Scars, ComplexionDocument13 pagesBiometrics: Thousands of Years Earlier Physiological Parameters Such As Scars, Complexionvishnuu06No ratings yet
- An Automated Door Control System Using Biometric Technology: IOSR Journal of Computer Engineering July 2017Document7 pagesAn Automated Door Control System Using Biometric Technology: IOSR Journal of Computer Engineering July 2017Fares ChetouhNo ratings yet
- Finger-Vein Based Biometric Security SystemDocument4 pagesFinger-Vein Based Biometric Security SystemInternational Journal of Research in Engineering and TechnologyNo ratings yet
- PR D 18 01654Document24 pagesPR D 18 01654Jose Hernandez PalancarNo ratings yet
- 29 FingerprintDocument11 pages29 FingerprintMoses OrakanyeNo ratings yet
- Technical Seminar SampleDocument15 pagesTechnical Seminar SampleMr.single KANYANo ratings yet
- 19bce2646 VL2021220700729 Pe003Document16 pages19bce2646 VL2021220700729 Pe003Manohar Kumar SinghNo ratings yet
- Fabrication of High Speed Indication and Automatic Pneumatic Braking SystemDocument7 pagesFabrication of High Speed Indication and Automatic Pneumatic Braking Systemseventhsensegroup0% (1)
- Implementation of Single Stage Three Level Power Factor Correction AC-DC Converter With Phase Shift ModulationDocument6 pagesImplementation of Single Stage Three Level Power Factor Correction AC-DC Converter With Phase Shift ModulationseventhsensegroupNo ratings yet
- Design, Development and Performance Evaluation of Solar Dryer With Mirror Booster For Red Chilli (Capsicum Annum)Document7 pagesDesign, Development and Performance Evaluation of Solar Dryer With Mirror Booster For Red Chilli (Capsicum Annum)seventhsensegroupNo ratings yet
- Ijett V5N1P103Document4 pagesIjett V5N1P103Yosy NanaNo ratings yet
- FPGA Based Design and Implementation of Image Edge Detection Using Xilinx System GeneratorDocument4 pagesFPGA Based Design and Implementation of Image Edge Detection Using Xilinx System GeneratorseventhsensegroupNo ratings yet
- An Efficient and Empirical Model of Distributed ClusteringDocument5 pagesAn Efficient and Empirical Model of Distributed ClusteringseventhsensegroupNo ratings yet
- Non-Linear Static Analysis of Multi-Storied BuildingDocument5 pagesNon-Linear Static Analysis of Multi-Storied Buildingseventhsensegroup100% (1)
- Analysis of The Fixed Window Functions in The Fractional Fourier DomainDocument7 pagesAnalysis of The Fixed Window Functions in The Fractional Fourier DomainseventhsensegroupNo ratings yet
- Ijett V4i10p158Document6 pagesIjett V4i10p158pradeepjoshi007No ratings yet
- Design and Implementation of Multiple Output Switch Mode Power SupplyDocument6 pagesDesign and Implementation of Multiple Output Switch Mode Power SupplyseventhsensegroupNo ratings yet
- Experimental Analysis of Tobacco Seed Oil Blends With Diesel in Single Cylinder Ci-EngineDocument5 pagesExperimental Analysis of Tobacco Seed Oil Blends With Diesel in Single Cylinder Ci-EngineseventhsensegroupNo ratings yet
- Computer Virus Class 11 Informatics PracticesDocument12 pagesComputer Virus Class 11 Informatics PracticesAmbharish ArgbsrNo ratings yet
- 3rd Grade Math Teaching Strategies HandoutDocument6 pages3rd Grade Math Teaching Strategies Handoutapi-261391559No ratings yet
- Empowerment 2 NDDocument4 pagesEmpowerment 2 NDJayram JavierNo ratings yet
- Smart Utilities User ManualDocument70 pagesSmart Utilities User Manualkof_007No ratings yet
- Techno TricksDocument14 pagesTechno TricksShiva KumaarNo ratings yet
- E Prison SumDocument63 pagesE Prison SumBrian MPAFENo ratings yet
- Applies To:: FAQ: Account Generator (Doc ID 216831.1)Document4 pagesApplies To:: FAQ: Account Generator (Doc ID 216831.1)zelghorfNo ratings yet
- What Are The Causes of Cybercrime Among Students in Chukwuemeka Odumegwu Ojukwu UniversityDocument29 pagesWhat Are The Causes of Cybercrime Among Students in Chukwuemeka Odumegwu Ojukwu Universityifeme nwachukwuNo ratings yet
- Pontiac Library NewsletterDocument4 pagesPontiac Library Newsletterapi-273158828No ratings yet
- Eur 20823 enDocument197 pagesEur 20823 enDody AdyNo ratings yet
- Components of LaptopDocument7 pagesComponents of LaptopMa Michelle Nica DmNo ratings yet
- AHLEI Supervisor GuideDocument8 pagesAHLEI Supervisor GuideravinramasmyNo ratings yet
- Secure Electronic Lock Based On Bluetooth Based OTP SystemDocument2 pagesSecure Electronic Lock Based On Bluetooth Based OTP SystemElins JournalNo ratings yet
- Release Date: 2012-11-27Document85 pagesRelease Date: 2012-11-27Anonymous ytZsBOVNo ratings yet
- Government of Kerala: Possession CertificateDocument1 pageGovernment of Kerala: Possession CertificatethanseelnnNo ratings yet
- PKK (Uts)Document5 pagesPKK (Uts)Rida RizkitaNo ratings yet
- Cyber Space, Laws and Crimes: Tentative IndexDocument2 pagesCyber Space, Laws and Crimes: Tentative Indexkashif zafar50% (2)
- Cory Doctorow - Overclocked - I Robot-A4Document20 pagesCory Doctorow - Overclocked - I Robot-A4darshantasNo ratings yet
- Fingerprinting Info SheetDocument3 pagesFingerprinting Info Sheetapi-241177893No ratings yet
- HackenbushDocument17 pagesHackenbushOrchid MajumderNo ratings yet
- Confidential Information PolicyDocument4 pagesConfidential Information PolicyDarren CariñoNo ratings yet
- User Access Request Form 05.2013Document3 pagesUser Access Request Form 05.2013Nabeel Adeeb AlshareNo ratings yet
- Ir 4.0Document19 pagesIr 4.0Syaidatul MieraNo ratings yet
- Dilo Project ReportDocument6 pagesDilo Project ReportSana SaraNo ratings yet
- Crypt 1 A AES, IDEA, Blowfish IntroDocument40 pagesCrypt 1 A AES, IDEA, Blowfish Introwest_lmnNo ratings yet
- 11g Transparent Data EncryptionDocument84 pages11g Transparent Data EncryptionTarun ChaudharyNo ratings yet
- Fireeye Malware Protection CloudDocument2 pagesFireeye Malware Protection CloudFireEyeNo ratings yet
- Haier TDC1314SDocument1 pageHaier TDC1314Spepino464No ratings yet
- Double Ur Perfectmoney 100% Working TricksDocument4 pagesDouble Ur Perfectmoney 100% Working Tricksblackhat0637100% (1)