Professional Documents
Culture Documents
Name Netid Group Number: Website Link: Tutorial Details Time Spent On Assignment
Uploaded by
Donna Isabelle Lee0 ratings0% found this document useful (0 votes)
710 views11 pagesThis document outlines a proposal for a fingerprint recognition technology business to address the problem of rising motor vehicle thefts. It discusses the vision, industry analysis, customers and their needs, the fingerprint recognition product and service, suppliers and partners, broad differentiation strategy, procurement as the most important value chain activity, inventory ordering and supply sourcing business processes, and the need for an inventory management system. The goal is to provide superior motor vehicle security and safety for drivers through a personalized fingerprint system.
Original Description:
Infosys 110 D2
Original Title
Deliverable 2
Copyright
© © All Rights Reserved
Available Formats
DOCX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThis document outlines a proposal for a fingerprint recognition technology business to address the problem of rising motor vehicle thefts. It discusses the vision, industry analysis, customers and their needs, the fingerprint recognition product and service, suppliers and partners, broad differentiation strategy, procurement as the most important value chain activity, inventory ordering and supply sourcing business processes, and the need for an inventory management system. The goal is to provide superior motor vehicle security and safety for drivers through a personalized fingerprint system.
Copyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
710 views11 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On Assignment
Uploaded by
Donna Isabelle LeeThis document outlines a proposal for a fingerprint recognition technology business to address the problem of rising motor vehicle thefts. It discusses the vision, industry analysis, customers and their needs, the fingerprint recognition product and service, suppliers and partners, broad differentiation strategy, procurement as the most important value chain activity, inventory ordering and supply sourcing business processes, and the need for an inventory management system. The goal is to provide superior motor vehicle security and safety for drivers through a personalized fingerprint system.
Copyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
You are on page 1of 11
1
INFOSYS.110 BUSINESS SYSTEMS:
DELIVERABLE 2: BUSINESS SECTION
2014
Name Donna Lee
NetID dlee873
Group Number: 246
Website Link: http://infosys110group246.blogspot.co.nz/
Tutorial Details
Tutor: Day: Time:
Johnnie Wednesday 12pm
Time Spent on
Assignment:
30 hours Word Count: 1642
2
2
FINGERPRINT RECOGNITION
TECHNOLOGY
INTRODUCTION
This proposal addresses the problem of rising motor vehicle thefts in New Zealand. There
has been over 48,000 reported motor vehicle thefts in NZ over the past year according to
New Zealand Police statistics. However, this issue is not simply restricted to New Zealand.
According to Interpol statistics, there has been a reported 7.2 million reported stolen motor
vehicles globally from the year 2012 to 2013, with NZ having the highest number of motor
vehicle theft cases among other countries. Therefore, we have come up with fingerprint
recognition technology specifically for motor vehicles to address the problem of poor
security.
3. BUSINESS SECTION
3.1 Vision
To provide motor vehicle security of superior standard and to guarantee the highest level of
safety for motor vehicle owners in order to create a safer and secure world for drivers.
3.2 Industry Analysis: Motor Vehicle Security Industry
Industry: Motor Vehicle Security Industry.
Force: High/Low: Justification:
Buyer power: Low There are few companies operating in the motor
vehicle security industry but most have been
operating for decades and across many countries.
Existing companies are well-established among
car owners. An example is Rapid Radio, New
Zealand's premier car audio and security
3
3
specialist with over three decades in the business,
installing the latest in sound and security
equipment in Auckland since 1978. (Rapid Radio,
2006) Therefore, buyers have few choices in this
industry.
Supplier power: Low There is a range of suppliers for automotive
products e.g. Mongoose Automotive
Technologies offers a range of products
distributed throughout NZ to over 300
authorised dealers. (Mongoose New Zealand
Limited, 2014)
Companies in this industry also outsource their
products. E.g. AVS Car Security (2013) who
sources stock from around the world according
to quality and value from proven manufacturers.
Hence, there is a wide range of suppliers in this
industry locally and internationally.
Threat of new entrants: Low A high level of expertise and broad knowledge in
the IT field is required to start up a business in
this industry. For example Autowatch NZ (2012)
was established in 1985 by a group of engineers
with a strong background in design and
manufacture of military electronics. Therefore, it
is difficult to enter this industry as few people are
highly qualified and experienced in this sector.
Threat of substitutes: Low Currently, there is a small number of leading
motor vehicle security companies operating in
4
4
the New Zealand market. Hence, the availability
of substitute products for motor vehicle security
is low.
Rivalry among existing
competitors:
Low There are a few companies in this industry, hence
rivalry is low. However, due to rising numbers of
car theft in recent years, there is a potential rise
in start-up companies in this industry and an
increasing need to serve the growing Australian
and New Zealand markets (Autowatch NZ,
2012).
Overall attractiveness of the industry: Although there are few motor vehicle security
businesses in NZ, a high level of qualification, skills, expertise, knowledge and experience in
security and IT systems is required in order to start up a business. Hence, there are high
entry barriers to this industry which proves a low overall attractiveness.
3.3 Customers and Thei r Needs
Car owners require safety. According to Automotive Security Systems Ltd (2012), Every day
56 cars are stolen in New Zealand, which builds on the issue of rising numbers of car
thieves. Beside stealing cars, thieves also target items of high prices such as mag
wheels and audio equipment (Warlocks, 2013). Hence, there is a growing need for car
owners to have high quality security for their cars in order to prevent car theft rates from
rising, especially in New Zealand.
3.4 The Product and Service
The fingerprint recognition technology will bring motor vehicle security to the next level.
Since this will be a personalized system, car owners can authorize certain fingerprints to
access their car and to start the car. An optional linked security system can also be installed
where unauthorized fingerprints will trigger an alert on the car owners smartphone. This
provides value-added security to car owners.
5
5
3.5 Suppliers and Partners
Internet service providers enable our company to display our product(s) and handle
transactions online and allows for online communication with customers and other
suppliers. Since some products or components of our product will be outsourced, having an
internet service provider is mandatory in order to facilitate communication and ordering
processes between our business and potential suppliers.
Vehicle security companies such as AVS security and Autowatch NZ are potential partners
for our company. They manufacture and outsource a wide range of vehicle security
products. We aim to source inventory and share IT knowledge and skills with other
companies in the automotive industry to come up with the ideal product for our customers.
3.6 Strategy: Broad Differenti ation
Our business will be targeting a broad market of motor vehicle owners in NZ. Auckland, in
particular, is known as the city of cars, due to a large proportion of car owners. The
fingerprint recognition technology can be used for any motor vehicle.
The technology will be highly priced as compared to current motor vehicle security systems
e.g. motor vehicle locks and alarm systems. A range of prices will also be provided. Our
differentiation is top standard safety and we price our products to target a huge, stratified
audience which are vehicle owners.
The overall strategy is therefore Broad Differentiation.
3.7 Value Chain Activity: Procurement
The most important value chain activity for this business is Procurement.
Our business is looking at outsourcing products and services and finding stock of the highest
quality, which relates to our vision. We are targeting a broad audience and our products are
of high cost. Hence, it is important that we find reliable suppliers who are able to deliver
products and services of top-level standard so that it is worth the price customers pay for. In
6
6
addition, we will be able to co-create value since the fingerprint recognition technology is
personalized and programmed to customers preferences.
3.8 Business Processes
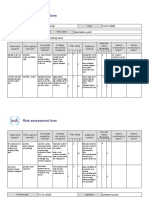
3.8.1. INVENTORY ORDERING PROCESS In relation to procurement, it is important to ensure
that supplier orders are always smoothly carried out. The process starts with submission of
a purchase order followed by receipt and processing of the order. Once the order is
processed, the raw materials will then be shipped. When the raw materials are received and
stored, the supplier issues an invoice which is then followed by payment. Once the payment
is complete, the process concludes with whether or not a new order needs to be placed. If
not, the process is finished and if a new order needs to be placed, it brings us back to the
first step, submitting a purchase order.
INVENTORY ORDERING PROCESS MODEL
7
7
Start
Submit purchase
order
Receive and process
order
Ship raw materials
Receive and store
raw materials
Receive invoice
Payment of invoice
New order?
End
Inventory management system
Warehouse
Yes
No
3.8.2. SUPPLY SOURCING PROCESS It is important that our business uses a good
procurement outsourcing strategy. This process ensures that the right suppliers are
selected. It starts off with assessing the vehicle security supplier market. It is mandatory to
8
8
set up a supplier survey to evaluate potential suppliers. The next step is to build a sourcing
strategy which is suitable for our business. This is done based on selection criteria that our
business will draw up. This is then followed by the selection of suppliers and finalization.
SUPPLY SOURCING PROCESS MODEL
Start
Assess supplier
market
Survey suppliers
Build sourcing
strategy
Selection of suppliers
Finalize
supplier?
End
Supply chain
benchmarking system
Yes
No
Purchasing
department
9
9
3.9 Functionalities
3.9.1. INVENTORY ORDERING PROCESS
Create and submit orders
Reporting activities e.g. inventory reports, order reports, invoicing reports
3.9.2. SUPPLY SOURCING PROCESS
Collect and gather supplier information
Communicate with potential suppliers
3.10 Systems
3.10. 1. INVENTORY MANAGEMENT SYSTEM Usually an IT-based system which supports the
inventory ordering process. It simplifies the process and is easy to operate. Besides
managing and processing orders, the system can be used to record and store information
such as inventory levels, order reports, sales data, customer particulars and delivery
information. Inventory management systems are commonly used to avoid product
overstock and outages (Inventory management software, 2014). It also organizes
inventory data and reduces costs through efficient inventory storage and preventing excess
inventory on hand.
3.10. 2. ORDER PROCESSI NG SYSTEM This system ensures a smooth flow from sales quote to
confirmed order, successful order to order fulfillment, and prompt invoicing to payment
(NetSuite Inc., 2014). It consists of order submissions, order processing, shipping of raw
materials, receipt of raw materials, and receipt and payment of invoices. Hence it supports
the functionalities and inventory ordering process. The system is important as it supports
the various procedures associated with procurement.
3.10. 3. SUPPLY CHAIN BENCHMARKING SYSTEM This system compares our business
performance with our competitors and other businesses so as to gauge our position in the
market and help us to improve our strategy. This helps our business analyze and understand
our operational practices and gain competitive advantage. For example, the system could
analyze the supply sourcing processes in place and improve it by changing supplier criteria
to help identify the right suppliers. This also ensures better and more efficent
communication with current and potential suppliers due to increased industry knowledge.
10
10
3.11. Summary Table: Value Chain to Systems
Value Chain
Activity
Processes Functionalities Specific Information
System(s)
Broad Information
System(s)
Procurement
1. Inventory
ordering
process
1. Create and submit orders
2. Reporting activities
Inventory management
system
Order processing system
Supply Chain Management
System
Transaction Processing
System
2. Supply
sourcing
process
1. Collect and gather supplier information
2. Communicate with potential suppliers
Supply chain benchmarking
system
Decision Support System
Supply Chain Management
System
11
11
CONCLUSION
The fingerprint recognition technology is an efficient way of providing motor vehicle owners
with the safety and security they need. Upon analyzing the motor vehicle industry and
identifying our customers, their needs, potential suppliers and partners, we derived a Broad
Differentiation strategy. We have identified inventory ordering and supply sourcing as our
two key business processes relating to procurement. The use of inventory management
systems, order processing systems and supply chain benchmarking systems is beneficial to
our business as it maximizes overall productivity and ensures top quality products.
REFERENCES
1. Rapid Radio (n.d.). Rapid - car audio, stereos, alarms, speakers, installs.
Retrieved May 23, 2014, from http://www.rapidradio.co.nz/
2. Warlocks (n.d.). WARLOCKS - Car Alarms, Immobilisers, Car Audio and much
more. Retrieved May 23, 2014, from http://www.warlocks.co.nz/about-
warlocks.htm
3. Mongoose New Zealand Limited (n.d.). Mongoose New Zealand - Automotive
Technologies - Home. Retrieved May 23, 2014, from
http://www.mongoose.co.nz/
4. AVS Car Security (n.d.). About us - AVS Car Security - 0800 438 862.
Retrieved May 24, 2014, from http://avscarsecurity.com/about-avs/
5. Autowatch NZ (n.d.). About Us | Autowatch Car Alarm Installers | Nationwide
0800 862862. Retrieved May 24, 2014, from
http://www.autowatch.co.nz/About+Us.html
6. Automotive Security Systems (n.d.). Automotive Security Systems.
Retrieved May 23, 2014, from http://www.caralarm.co.nz
7. Polymathic Computer Corporation (n.d.). Inventory/Order Entry.
Retrieved May 25, 2014, from
http://www.polymathic.com/polysoft/oebpi.htm
8. Supply Management (n.d.). The seven stages of a sourcing strategy | Supply
Management. Retrieved May 25, 2014, from
http://www.supplymanagement.com/resources/2011/the-seven-stages-of-
a-sourcing-strategy
9. Inventory management software - Wikipedia, the free encyclopedia. (n.d.).
Retrieved May 25, 2014, from
http://en.wikipedia.org/wiki/Inventory_management_software
10. NetSuite Inc. (n.d.). Order Management, Order Fulfillment, Order Processing,
Billing Management, Order Fulfillment Software - NetSuite. Retrieved May 25,
2014, from
http://www.netsuite.com/portal/products/netsuite/erp/order.shtml
You might also like
- Risk Assessment Project Iosh - MsDocument2 pagesRisk Assessment Project Iosh - MsSanjeev Kumar75% (32)
- How To Make FireworksDocument14 pagesHow To Make FireworksLeonardo BiancoNo ratings yet
- Security Testing Handbook for Banking ApplicationsFrom EverandSecurity Testing Handbook for Banking ApplicationsRating: 5 out of 5 stars5/5 (1)
- Natural Topography of PakistanDocument25 pagesNatural Topography of Pakistansatayish100% (1)
- CCTV 2010Document68 pagesCCTV 2010Yao Ma100% (3)
- Eric Dollard MWO Update 2012Document21 pagesEric Dollard MWO Update 2012pic2007100% (7)
- Transcendental Meditation (Four Lectures by Silo)Document49 pagesTranscendental Meditation (Four Lectures by Silo)nmjoshi77859100% (2)
- Heating and Cooling Load Calculations-ReportDocument20 pagesHeating and Cooling Load Calculations-ReportEhtisham Tanvir100% (1)
- Ufm Interpretation SynopsisDocument1 pageUfm Interpretation SynopsispipegamoNo ratings yet
- Project Work 2.0Document18 pagesProject Work 2.0PurviNo ratings yet
- INFOSYS110-2014 Deliverable02 Alvin TanDocument10 pagesINFOSYS110-2014 Deliverable02 Alvin TanAlvin TanNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument11 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentMaggieZhouNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument10 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentKenneth CaiNo ratings yet
- Infosys.110 Business Systems: Deliverable 2: Business Section 2014Document9 pagesInfosys.110 Business Systems: Deliverable 2: Business Section 2014songmi0329No ratings yet
- Infosys.110 Business Systems: Deliverable 2: Business Section 2014Document10 pagesInfosys.110 Business Systems: Deliverable 2: Business Section 2014mmck939No ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument13 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentJasonDerulo123No ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument11 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentJasonch26No ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument10 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentShreta MalaNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument11 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On Assignmentsnic529No ratings yet
- D2 Assignment ASPE157Document10 pagesD2 Assignment ASPE157alistairspNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument11 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentJennyLeeNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument10 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentesthernigNo ratings yet
- Infosys 110 Deliverable 2Document11 pagesInfosys 110 Deliverable 2VaisuePalesooNo ratings yet
- INFOSYS110 2014 Deliverable 02Document11 pagesINFOSYS110 2014 Deliverable 02gregblackettNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument9 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentTAn WeiiYaooNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument11 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On Assignmentsnic529No ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument12 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentAlexandraWilliamsNo ratings yet
- Assignment D2 Wonwoo, JooDocument9 pagesAssignment D2 Wonwoo, JooWonwooJooNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument9 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentSam TealNo ratings yet
- INFOSYS110 2014 Deliverable 2Document10 pagesINFOSYS110 2014 Deliverable 2cecilialeewardusNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument11 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentBenjamin Tu'itahiNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument10 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On Assignmentnickbnick9No ratings yet
- Name Netid Group Number: Website Link: Tutorial Details: Tanira Fisher-MaramaDocument9 pagesName Netid Group Number: Website Link: Tutorial Details: Tanira Fisher-MaramaTaniraFisher-MaramaNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument10 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentBlairRatuNo ratings yet
- Infosys110 S1 2014 D2Document10 pagesInfosys110 S1 2014 D2Andrea LimNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument11 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On Assignmentskoo437No ratings yet
- Infosys Deliverable 2Document11 pagesInfosys Deliverable 2Warren CorstonNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument9 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentTaniraFisher-MaramaNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument10 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentWillDowdenNo ratings yet
- Business Case TemplateDocument5 pagesBusiness Case TemplateHR AssigmnetsNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument9 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentNeoCraigNo ratings yet
- Name Dayna Rusk Netid Group Number: Website Link:: Drus426 232Document11 pagesName Dayna Rusk Netid Group Number: Website Link:: Drus426 232DaynaRuskNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument9 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentNeoCraigNo ratings yet
- Sams Information Systems Deliverable 2 Group 514Document10 pagesSams Information Systems Deliverable 2 Group 514SamJefferiesNo ratings yet
- Project On Autocop CompanyDocument63 pagesProject On Autocop CompanymamtajeswaniNo ratings yet
- INFOSYS110 2014 Deliverable 2 Annie RenDocument10 pagesINFOSYS110 2014 Deliverable 2 Annie RenAnnie RenNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument11 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentPatrickFaheyNo ratings yet
- Natalies Deliverable 2Document11 pagesNatalies Deliverable 2DuruthuNo ratings yet
- Safe Card: Infosys.110 Business Systems: Deliverable 2: Business Section 2014Document10 pagesSafe Card: Infosys.110 Business Systems: Deliverable 2: Business Section 2014HeidiStrajnarNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument9 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On Assignmentcchi196No ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument12 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On Assignmenthuman360No ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument10 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On Assignmentlee950119No ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument9 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On Assignmentjiewang123No ratings yet
- ABM - Security Insider Mag's "Intelligence and Investigative Software Provider of The Year 2015"Document1 pageABM - Security Insider Mag's "Intelligence and Investigative Software Provider of The Year 2015"softwarecounsellNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument10 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentShioriSaitoNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument12 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentesmeeejNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument8 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentGodinetLouieNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument10 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentLilyKangNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument11 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On Assignmentrkis215No ratings yet
- UPI Swan294 ID Number 5421939 Group Number 17Document12 pagesUPI Swan294 ID Number 5421939 Group Number 17Suyangzi WangNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument11 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On Assignmentaliu027No ratings yet
- Newslette: Winter 2013 - 14Document2 pagesNewslette: Winter 2013 - 14api-143253491No ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument10 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentclaudiaboottenNo ratings yet
- Name Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentDocument13 pagesName Netid Group Number: Website Link: Tutorial Details Time Spent On AssignmentYanZiyuNo ratings yet
- Title: To Develop Marketing Strategy For The Infrastructure Storage and Security System in Effective MannerDocument16 pagesTitle: To Develop Marketing Strategy For The Infrastructure Storage and Security System in Effective MannerTamil VelanNo ratings yet
- IoT Standards with Blockchain: Enterprise Methodology for Internet of ThingsFrom EverandIoT Standards with Blockchain: Enterprise Methodology for Internet of ThingsNo ratings yet
- Multical® 402: Data SheetDocument20 pagesMultical® 402: Data SheetSundar RamasamyNo ratings yet
- Inventory of Flood Bund PunjabDocument26 pagesInventory of Flood Bund PunjabguildkeyNo ratings yet
- "Chapter 9 - Influence Lines For Statically Determinate Structures" in "Structural Analysis" On Manifold @tupressDocument33 pages"Chapter 9 - Influence Lines For Statically Determinate Structures" in "Structural Analysis" On Manifold @tupressrpsirNo ratings yet
- E2870-13 Standard Test Method For Evaluating RelativDocument6 pagesE2870-13 Standard Test Method For Evaluating RelativA MusaverNo ratings yet
- Schueco+FW+50+SG+ +FW+60+SGDocument1 pageSchueco+FW+50+SG+ +FW+60+SGDaniel Nedelcu100% (1)
- Energy and FluctuationDocument10 pagesEnergy and Fluctuationwalid Ait MazouzNo ratings yet
- Bugreport Dandelion - Eea QP1A.190711.020 2022 02 15 07 45 54Document9,715 pagesBugreport Dandelion - Eea QP1A.190711.020 2022 02 15 07 45 54João Carlos Pereira ChoinasNo ratings yet
- Application of Land Suitability AnalysisDocument16 pagesApplication of Land Suitability AnalysisHải Anh Nguyễn100% (1)
- Tycho BraheDocument3 pagesTycho BraheAienna Lacaya MatabalanNo ratings yet
- The Effective SpanDocument4 pagesThe Effective SpanMohamed FarahNo ratings yet
- Unit-4 - Hypothesis TestingDocument24 pagesUnit-4 - Hypothesis TestingMANTHAN JADHAVNo ratings yet
- Astm D3078-02Document3 pagesAstm D3078-02Geoff EricksonNo ratings yet
- Valvula Reguladoras Pilotados DANFOSSDocument2 pagesValvula Reguladoras Pilotados DANFOSSJurandir Laureano SILVA JUNIORNo ratings yet
- 4 TH Sem UG Osmoregulation in Aquatic VertebratesDocument6 pages4 TH Sem UG Osmoregulation in Aquatic VertebratesBasak ShreyaNo ratings yet
- Kitchen Colour Ide1Document6 pagesKitchen Colour Ide1Kartik KatariaNo ratings yet
- Markov Interest Rate Models - Hagan and WoodwardDocument28 pagesMarkov Interest Rate Models - Hagan and WoodwardlucaliberaceNo ratings yet
- EDO ScriptDocument59 pagesEDO ScriptThais Andrés JiménezNo ratings yet
- Water Treatment Lecture 4Document34 pagesWater Treatment Lecture 4pramudita nadiahNo ratings yet
- Maxon - Gas Electro-Mechanical ValvesDocument4 pagesMaxon - Gas Electro-Mechanical ValvesThiagoNo ratings yet
- X-Ray Radiation and Gamma RadiationDocument13 pagesX-Ray Radiation and Gamma RadiationVence MeraNo ratings yet
- Mucosal Adjuvants: Charles O. Elson Mark T. DertzbaughDocument1 pageMucosal Adjuvants: Charles O. Elson Mark T. DertzbaughPortobello CadısıNo ratings yet
- E2788-11 Standard Specification For Use of Expanded Shale, Clay and Slate (ESCS) As A Mineral Component in The Growing Media and The Drainage Layer For Vegetative (Green) Roof SystemsDocument3 pagesE2788-11 Standard Specification For Use of Expanded Shale, Clay and Slate (ESCS) As A Mineral Component in The Growing Media and The Drainage Layer For Vegetative (Green) Roof SystemsSatya kaliprasad vangaraNo ratings yet
- Grade 7 Information Writing: The Bulldog: A Dog Like No OtherDocument5 pagesGrade 7 Information Writing: The Bulldog: A Dog Like No Otherapi-202727113No ratings yet