Professional Documents
Culture Documents
TP Security
Uploaded by
boukkour0 ratings0% found this document useful (0 votes)
41 views4 pagesPT Activity: Configure IP ACLs to mitigate attacks. You create ACLs on edge routers R1 and R3 to achieve this goal. You then Verify ACL functionality from internal and external hosts.
Original Description:
Copyright
© © All Rights Reserved
Available Formats
DOCX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentPT Activity: Configure IP ACLs to mitigate attacks. You create ACLs on edge routers R1 and R3 to achieve this goal. You then Verify ACL functionality from internal and external hosts.
Copyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
41 views4 pagesTP Security
Uploaded by
boukkourPT Activity: Configure IP ACLs to mitigate attacks. You create ACLs on edge routers R1 and R3 to achieve this goal. You then Verify ACL functionality from internal and external hosts.
Copyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
You are on page 1of 4
All contents are Copyright 1992-2012 Cisco Systems, Inc. All rights reserved.
. This document is Cisco Public Information. Page 1 of 4
PT Activity: Configure IP ACLs to Mitigate Attacks
Instructor Version
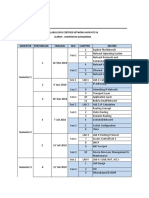
Topology Diagram
Addressing Table
Device Interface IP Address Subnet Mask Default Gateway
R1
Fa0/1 192.168.1.1 255.255.255.0 N/A
S0/0/0 (DCE) 10.1.1.1 255.255.255.252 N/A
R2
S0/0/0 10.1.1.2 255.255.255.252 N/A
S0/0/1(DCE) 10.2.2.2 255.255.255.252 N/A
Lo0 192.168.2.1 255.255.255.0 N/A
R3
Fa0/1 192.168.3.1 255.255.255.0 N/A
S0/0/1 10.2.2.1 255.255.255.252 N/A
PC-A NIC 192.168.1.3 255.255.255.0 192.168.1.1
PC-C NIC 192.168.3.3 255.255.255.0 192.168.3.1
Objectives
Verify connectivity among devices before firewall configuration.
Use ACLs to ensure remote access to the routers is available only from management station PC-C.
Configure ACLs on R1 and R3 to mitigate attacks.
Verify ACL functionality.
CCNA Security
All contents are Copyright 19922012 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information. Page 2 of 4
Introduction
Access to routers R1, R2, and R3 should only be permitted from PC-C, the management station. PC-C is also
used for connectivity testing to PC-A, a server providing DNS, SMTP, FTP, and HTTPS services.
Standard operating procedure is to apply ACLs on edge routers to mitigate common threats based on source
and/or destination IP address. In this activity, you create ACLs on edge routers R1 and R3 to achieve this goal.
You then verify ACL functionality from internal and external hosts.
The routers have been pre-configured with the following:
Enable password: ciscoenpa55
Password for console: ciscoconpa55
Username for VTY lines: SSHadmin
Password for VTY lines: ciscosshpa55
IP addressing
Static routing
Task 1: Verify Basic Network Connectivity
Verify network connectivity prior to configuring the IP ACLs.
Step 1. From the PC-C command prompt, ping the PC-A server.
Step 2. From the PC-C command prompt, SSH to the router R2 Lo0 interface. Exit the SSH session.
Step 3. From PC-C, open a web browser to the PC-A server (using the IP address) to display the web
page. Close the browser on PC-C.
Step 4. From the PC-A server command prompt, ping PC-C.
Task 2: Secure Access to Routers
Step 1. Configure ACL 10 to block all remote access to the routers except from PC-C.
Use the access-list command to create a numbered IP ACL on R1, R2, and R3.
R1(config)# access-list 10 permit 192.168.3.3 0.0.0.0
R2(config)# access-list 10 permit 192.168.3.3 0.0.0.0
R3(config)# access-list 10 permit 192.168.3.3 0.0.0.0
Step 2. Apply ACL 10 to ingress traffic on the VTY lines.
Use the access-class command to apply the access list to incoming traffic on the VTY lines.
R1(config-line)# access-class 10 in
R2(config-line)# access-class 10 in
R3(config-line)# access-class 10 in
Step 3. Verify exclusive access from management station PC-C.
SSH to 192.168.2.1 from PC-C (should be successful). SSH to 192.168.2.1 from PC-A (should fail).
PC> ssh l SSHadmin 192.168.2.1
CCNA Security
All contents are Copyright 19922012 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information. Page 3 of 4
Task 3: Create a Numbered IP ACL 100
On R3, block all packets containing the source IP address from the following pool of addresses: 127.0.0.0/8,
any RFC 1918 private addresses, and any IP multicast address.
Step 1. Configure ACL 100 to block all specified traffic from the outside network.
You should also block traffic sourced from your own internal address space if it is not an RFC 1918 address (in
this activity, your internal address space is part of the private address space specified in RFC 1918).
Use the access-list command to create a numbered IP ACL.
R3(config)# access-list 100 deny ip 10.0.0.0 0.255.255.255 any
R3(config)# access-list 100 deny ip 172.16.0.0 0.15.255.255 any
R3(config)# access-list 100 deny ip 192.168.0.0 0.0.255.255 any
R3(config)# access-list 100 deny ip 127.0.0.0 0.255.255.255 any
R3(config)# access-list 100 deny ip 224.0.0.0 15.255.255.255 any
R3(config)# access-list 100 permit ip any any
Step 2. Apply the ACL to interface Serial 0/0/1.
Use the ip access-group command to apply the access list to incoming traffic on interface Serial 0/0/1.
R3(config)# interface s0/0/1
R3(config-if)# ip access-group 100 in
Step 3. Confirm that the specified traffic entering interface Serial 0/0/1 is dropped.
From the PC-C command prompt, ping the PC-A server. The ICMP echo replies are blocked by the ACL since
they are sourced from the 192.168.0.0/16 address space.
Step 4. Remove the ACL from interface Serial 0/0/1.
Remove the ACL. Otherwise, all traffic from the outside network (being addressed with private source IP
addresses) will be denied for the remainder of the PT activity.
Use the no ip access-group command to remove the access list from interface Serial 0/0/1.
R3(config)# interface s0/0/1
R3(config-if)# no ip access-group 100 in
Note: In order for the PT activity to score 100 percent, the ACL needs to be grouped to the interface at the end
of the activity:
R3(config)# interface s0/0/1
R3(config-if)# ip access-group 100 in
Task 4: Create a Numbered IP ACL 110
Deny all outbound packets with source address outside the range of internal IP addresses.
Step 1. Configure ACL 110 to permit only traffic from the inside network.
Use the access-list command to create a numbered IP ACL.
R3(config)# access-list 110 permit ip 192.168.3.0 0.0.0.255 any
CCNA Security
All contents are Copyright 19922012 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information. Page 4 of 4
Step 2. Apply the ACL to interface F0/1.
Use the ip access-group command to apply the access list to incoming traffic on interface F0/1.
R3(config)# interface fa0/1
R3(config-if)# ip access-group 110 in
Create a Numbered IP ACL 120
Permit any outside host to access DNS, SMTP, and FTP services on server PC-A, deny any outside host
access to HTTPS services on PC-A, and permit PC-C to access R1 via SSH.
Step 1. Verify that PC-C can access the PC-A via HTTPS using the web browser.
Be sure to disable HTTP and enable HTTPS on server PC-A.
Step 2. Configure ACL 120 to specifically permit and deny the specified traffic.
Use the access-list command to create a numbered IP ACL.
R1(config)# access-list 120 permit udp any host 192.168.1.3 eq domain
R1(config)# access-list 120 permit tcp any host 192.168.1.3 eq smtp
R1(config)# access-list 120 permit tcp any host 192.168.1.3 eq ftp
R1(config)# access-list 120 deny tcp any host 192.168.1.3 eq 443
R1(config)# access-list 120 permit tcp host 192.168.3.3 host 10.1.1.1 eq 22
Step 3. Apply the ACL to interface S0/0/0.
Use the ip access-group command to apply the access list to incoming traffic on interface S0/0/0.
R1(config)# interface s0/0/0
R1(config-if)# ip access-group 120 in
Step 4. Verify that PC-C cannot access PC-A via HTTPS using the web browser.
Task 5: Modify An Existing ACL
Permit ICMP echo replies and destination unreachable messages from the outside network (relative to R1);
deny all other incoming ICMP packets.
Step 1. Verify that PC-A cannot successfully ping the loopback interface on R2.
Step 2. Make any necessary changes to ACL 120 to permit and deny the specified traffic.
Use the access-list command to create a numbered IP ACL.
R1(config)# access-list 120 permit icmp any any echo-reply
R1(config)# access-list 120 permit icmp any any unreachable
R1(config)# access-list 120 deny icmp any any
R1(config)# access-list 120 permit ip any any
Step 3. Verify that PC-A can successfully ping the loopback interface on R2.
Step 4. Check results.
Your completion percentage should be 100%. Click Check Results to see feedback and verification of which
required components have been completed.
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5783)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (890)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (587)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (265)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (72)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (119)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- Cisco Discovery Protocol (CDP) : Layer 3 NeighborsDocument3 pagesCisco Discovery Protocol (CDP) : Layer 3 NeighborsAbhishek KunalNo ratings yet
- Pages From Sor PWD WBDocument12 pagesPages From Sor PWD WBUTTAL RAYNo ratings yet
- 58 - Shane R Collins - Ancient Evil in OakvaleDocument1 page58 - Shane R Collins - Ancient Evil in OakvaleОлег КацыNo ratings yet
- Bdix Server ListDocument3 pagesBdix Server ListIftekhar Rahman RihamNo ratings yet
- Devops Tutorial: Complete Beginners TrainingDocument16 pagesDevops Tutorial: Complete Beginners Trainingshradha11100% (2)
- Hospital BedDocument2 pagesHospital BedfrankjparqNo ratings yet
- Trnsys TutorialDocument79 pagesTrnsys TutorialAndré Santos100% (4)
- Engineering Research Journal Brief Overview of Climate Responsive FacadesDocument18 pagesEngineering Research Journal Brief Overview of Climate Responsive FacadesRim ZreikaNo ratings yet
- At5 Ev 1222Document48 pagesAt5 Ev 1222Ashok JangraNo ratings yet
- Contactor: Stage: Completion Date:: Page 1 of 3Document3 pagesContactor: Stage: Completion Date:: Page 1 of 3waheedNo ratings yet
- LogRhythm File Integrity Monitoring Data SheetDocument1 pageLogRhythm File Integrity Monitoring Data SheetjordagroNo ratings yet
- Flash IIP Installation Guide 8-26-14Document10 pagesFlash IIP Installation Guide 8-26-14label engineering companyNo ratings yet
- Mala Noche (1985 Draft Script)Document99 pagesMala Noche (1985 Draft Script)Natalio RuizNo ratings yet
- Cisco CCNA Syllabus Learnit Gunadarma UniversityDocument2 pagesCisco CCNA Syllabus Learnit Gunadarma UniversityIan WidiNo ratings yet
- Dell Storage Compatibility Matrix - July 2014Document67 pagesDell Storage Compatibility Matrix - July 2014Rashedul Islam100% (1)
- 2nd International Congress on Architecture and Gender: MATRICESDocument9 pages2nd International Congress on Architecture and Gender: MATRICESSana TavaresNo ratings yet
- Ebco StockDocument7 pagesEbco StockVIKAS KUMARNo ratings yet
- ENetwork Chapter 9 - CCNA Exploration Network Fundamentals (Version 4.0)Document6 pagesENetwork Chapter 9 - CCNA Exploration Network Fundamentals (Version 4.0)Abdullah Al HawajNo ratings yet
- ISE Tender ReportDocument11 pagesISE Tender ReportMuhammadIqbalMughal100% (1)
- Influence of Silica Fume On High Strength Lightweight ConcreteDocument8 pagesInfluence of Silica Fume On High Strength Lightweight ConcreteIon RusuNo ratings yet
- Window & Door System: Let'S Build A Better FutureDocument4 pagesWindow & Door System: Let'S Build A Better FutureAmir AlićNo ratings yet
- Unit 1Document26 pagesUnit 1Gundrathi Narendra GoudNo ratings yet
- Building Permit FormDocument2 pagesBuilding Permit FormJohnNo ratings yet
- Appendix 7 - Container Roof Storage Calculations PDFDocument11 pagesAppendix 7 - Container Roof Storage Calculations PDFLều Hoàng100% (1)
- Creating LUN in NetApp Using CLIDocument2 pagesCreating LUN in NetApp Using CLIanon_326668689No ratings yet
- D02112 A1 OMC User InterfaceDocument92 pagesD02112 A1 OMC User Interfaceraj1978enatorNo ratings yet
- Seminar on middleware technologiesDocument37 pagesSeminar on middleware technologiesNavigator VickyNo ratings yet
- Module 01 - IntroductionDocument17 pagesModule 01 - IntroductionAnonymous GK9mHwnrNo ratings yet
- Advanced PHP For FlashDocument491 pagesAdvanced PHP For Flashdoru.mioc7445No ratings yet
- Multiprotocol Label SwitchingDocument94 pagesMultiprotocol Label SwitchingSimmhadri Simmi100% (1)