Professional Documents
Culture Documents
Sreenu Java Ieee List
Uploaded by
Saidi ReddyOriginal Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Sreenu Java Ieee List
Uploaded by
Saidi ReddyCopyright:
Available Formats
Regd No: 284/2010 Ph:9959969919
1. A Distributed Protocol to Serve Dynamic 2. A Review of the Applications of Agent TechnologyIn Traffic and Transportation Systems 3. Achieving Network Level Privacy in Wireless Sensor Networks 4. Always Acyclic Distributed Path Computation 5. Bandwidth Recycling in IEEE 802.16 Networks 6. Cooperative Caching in Wireless P2PNetworks to Design,Implementation,And Evaluation 7. Correlation-Based Traffic Analysis Attackson Anonymity Networks 8. Distributed Explicit Rate Schemes in Multi-InputMulti-Output Network Systems 9. Ensuring Data Storage Security in Cloud Computing 10. Host-to-Host Congestion Control for TCP
11. KTR an Efficient Key Management Scheme for Secure Data Access Control in Wireless Broadcast Services 12. Label-Based DV-Hop Localization against Wormhole AttacksIn Wireless Sensor Networks 13. Layered Approach Using Conditional Random Fields for Intrusion Detection
Regd No: 284/2010 Ph:9959969919
14. Mesh Based Multicast Routing in MANET Stable Link Based Approach 15. Modified DSR (Preemptive) to reduce link breakage and routing overhead for MANET using Proactive Route Maintenance (PRM) 16. Multicast Multi-path Power Efficient Routing in Mobile ADHOC networks
Rando
KNOWLEDGE AND DATA ENGINEERING / DATA MINING
Sno
TITLE
Binrank: Scaling Dynamic Authority-Based Search Using Materialized Sub graphs Closeness: A New Privacy Measure For Data Publishing P2p Reputation Management Using Distributed Decentralized Recommendation Chains Identities And
Year
2010
1 2 3 4 5 6 7 8
2010
2010
Managing Multidimensional Historical Aggregate Data In Unstructured P2p Networks Combinatorial Approach for Preventing SQL Injection Attacks(Secure Computing) Truth Discovery With Multiple Conflicting Information Providers On Web Protection Of Database Security Via Collaborative Inference Detection An Efficient Clustering Scheme to Exploit Hierarchical Data in Network Traffic sis
2010
2009 2008 2008 2008
Regd No: 284/2010 Ph:9959969919
Image Processing
9 10
Noise Reduction By Fuzzy Image Filtering(Fuzzy System) Application Of BPCS Steganography To Wavelet Compressed Video 2003 2004
Mobile Computing
11 12 13 14 15 16 17
Intrusion Detection In Homogeneous & Heterogeneous Wireless Sensor Networks Location Based Spatial Query Processing In Wireless Broadcast Environments Bandwidth Estimation For Ieee 802.11 Based Adhoc Network Benefit-Based Data Caching In Ad Hoc Networks Distributed Cache Updating For The Dynamic Source Routing Protocol An Acknowledgment-Based Misbehavior In Mantes Approach For The Detection Of Routing 2008 2008 2008 2008 2006 2007 2007
Detection Of Misbehavior In MANATES
NETWORKING
18 19
On Wireless Scheduling Algorithms For Minimizing The Queue-Overflow Probability Efficient And Dynamic Measurements Routing Topology Inference From End-To-End
2010
2010
Regd No: 284/2010 Ph:9959969919
20 21 22
23 24
Node Isolation Model And Age-Based Neighbor Selection In Unstructured P2p Networks Leveraging Identity-Based Cryptography Structured P2p Systems For Node Id Assignment In
2009
2009
Multiple Routing Configurations For Fast Ip Network Recovery Geometric Approach To Improving Active Packet Loss Measurement Performance Of A Speculative Transmission Scheme For Scheduling Latency Reduction Modeling & Automated Containment Of Worms(Secure Computing With Networking) Constructing Inter-Domain Packet Filters To Control IP Spoofing Based On BGP Updates Dual-Link Failure Resiliency Through Backup Link Mutual Exclusion Security In Large Mediator Protocols A Distributed Database Architecture For Global Roaming In Next-Generation Mobile Networks A Novel Secure Communication Protocol For Ad Hoc Networks [SCP]
2009
2008 2008
25
2008
26 27 28 29 30
2008 2008 2008 2004 2008
SOFTWARE ENGINEERING
31 32
2009
Atomicity Analysis Of Service Composition Across Organizations Using The Conceptual Cohesion Of Classes For Fault Prediction In Object Oriented Systems
2008
Regd No: 284/2010 Ph:9959969919
PARALLEL AND DISTRIBUTED SYSTEMS
33 34 35 36 37 38 39 40 41 42
2009
Dynamic Search Algorithm In Unstructured Peer-To-Peer Networks Flexible Deterministic Packet Marking: an Ip Trace back System to Find the Real Source of Attacks Distributed Algorithms For Constructing Approximate Minimum Spanning Trees In Wireless Sensor Networks A Faithful Distributed Mechanism For Sharing The Cost Of Multicast Transmissions Dynamic Routing With Security Considerations Detecting Malicious Packet Losses Quiver: Consistent Object Sharing For Edge Services An Adaptive Programming Model For Fault-Tolerant Distributed Computing Homogenous Network Control And Implementation A BGP Based Mechanism For Lowest Cost Routing
2009
2009
2009
2009 2009 2008 2007 2007 2005
Regd No: 284/2010 Ph:9959969919
Advance Computing, Secure Computing, JOURNAL AND CONFERENCE PAPERS
43 44 45 46 47 48 49 50
Enhancing Privacy And Authorization Control Scalability In The Grid Through Ontologies Collusive Piracy Prevention In P2p Content Delivery Networks Combinatorial Approach For Preventing Sql Injection Attacks A Precise Termination Algorithm Condition Of The Probalastic Packet Marking
2009
2009 2009
2008
An Adaptive Programming Model For Fault-Tolerant Distributed Computing Hybrid Intrusion Detection With Anomalous Internet Episodes Weighted Signature Generation Over
2007
2007
Network Border Patrol: Preventing Congestion Collapse And Promoting Fairness In The Internet An Algorithmic Approach To Identify Network Link Failures
2004
2004
17.m Access Transport Capacity
You might also like
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5795)
- Synopsis Capital Budgeting Reddy's LabshjklhjlDocument10 pagesSynopsis Capital Budgeting Reddy's LabshjklhjlSaidi ReddyNo ratings yet
- Knowledge Management - Edlogix Synopsis (1) HJKHDocument102 pagesKnowledge Management - Edlogix Synopsis (1) HJKHSaidi ReddyNo ratings yet
- Data Analysis 15 QuefghfstionsDocument35 pagesData Analysis 15 QuefghfstionsSaidi ReddyNo ratings yet
- Saidi BiodataTJTJDocument2 pagesSaidi BiodataTJTJSaidi ReddyNo ratings yet
- Guidelines For Filling Multisource Procedures of Pharmaceutical DrugyitfitygfouyDocument7 pagesGuidelines For Filling Multisource Procedures of Pharmaceutical DrugyitfitygfouySaidi ReddyNo ratings yet
- AWS Course Content MindQfghfgDocument8 pagesAWS Course Content MindQfghfgSaidi Reddy100% (1)
- Industry Profile: CommodityDocument12 pagesIndustry Profile: CommoditySaidi ReddyNo ratings yet
- A Project Report On "Asset & Liability Management" AT Icici BankDocument5 pagesA Project Report On "Asset & Liability Management" AT Icici BankSaidi ReddyNo ratings yet
- Karvy Arada CompletionghjDocument1 pageKarvy Arada CompletionghjSaidi ReddyNo ratings yet
- S.No Hall Ticket No Name of The Candidate 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 Specializatio NDocument8 pagesS.No Hall Ticket No Name of The Candidate 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 Specializatio NSaidi ReddyNo ratings yet
- Synopsis Taxfghfh Saving Mutual FundsDocument8 pagesSynopsis Taxfghfh Saving Mutual FundsSaidi ReddyNo ratings yet
- Movable Watering RobotsyutyDocument1 pageMovable Watering RobotsyutySaidi ReddyNo ratings yet
- Bootyijtyklet WindDocument64 pagesBootyijtyklet WindSaidi ReddyNo ratings yet
- 3 Axix CNC DrillinghjgjDocument1 page3 Axix CNC DrillinghjgjSaidi ReddyNo ratings yet
- India Infoline Vidya RadfgdDocument1 pageIndia Infoline Vidya RadfgdSaidi ReddyNo ratings yet
- Companies List (2pDocument1 pageCompanies List (2pSaidi ReddyNo ratings yet
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (588)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (400)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (345)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (121)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- Sap Education: Sample Questions: C - Tadm55 A - 75Document5 pagesSap Education: Sample Questions: C - Tadm55 A - 75Josimar Canales SalcedoNo ratings yet
- System Error Codes (0-499)Document33 pagesSystem Error Codes (0-499)enayuNo ratings yet
- CIVPRO - Case Compilation No. 2Document95 pagesCIVPRO - Case Compilation No. 2Darla GreyNo ratings yet
- Sub Clause 1.15 Limitation of Liability PDFDocument4 pagesSub Clause 1.15 Limitation of Liability PDFBogdanNo ratings yet
- Quick Commerce:: The Real Last MileDocument9 pagesQuick Commerce:: The Real Last MileChhavi KhandujaNo ratings yet
- Apples-to-Apples in Cross-Validation Studies: Pitfalls in Classifier Performance MeasurementDocument9 pagesApples-to-Apples in Cross-Validation Studies: Pitfalls in Classifier Performance MeasurementLuis Martínez RamírezNo ratings yet
- AloraDocument3 pagesAloraTatu AradiNo ratings yet
- Green Tyre TechnologyDocument4 pagesGreen Tyre TechnologyAnuj SharmaNo ratings yet
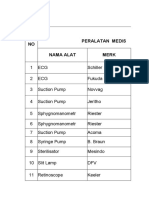
- Daftar Kalibrasi Peralatan MedisDocument34 pagesDaftar Kalibrasi Peralatan Medisdiklat rssnNo ratings yet
- Triptico NIC 16Document3 pagesTriptico NIC 16Brayan HMNo ratings yet
- A Study On Impact of Acne Vulgaris On Quality of LifeDocument7 pagesA Study On Impact of Acne Vulgaris On Quality of LifeIJAR JOURNALNo ratings yet
- BS en 12285-1-2003 (2006)Document162 pagesBS en 12285-1-2003 (2006)dahzahNo ratings yet
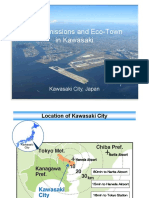
- 03 Zero Emissions and Eco-Town in KawasakiDocument21 pages03 Zero Emissions and Eco-Town in KawasakiAlwi AmarNo ratings yet
- Dahua Video Conferencing SolutionDocument16 pagesDahua Video Conferencing SolutionDennis DubeNo ratings yet
- RMU With Eco-Efficient Gas Mixture-Evaluation After Three Years of Field ExperienceDocument5 pagesRMU With Eco-Efficient Gas Mixture-Evaluation After Three Years of Field ExperienceZineddine BENOUADAHNo ratings yet
- 3500 System Datasheet: Bently Nevada Asset Condition MonitoringDocument11 pages3500 System Datasheet: Bently Nevada Asset Condition MonitoringRujisak MuangsongNo ratings yet
- 6 Elements of A Healthy ChurchDocument2 pages6 Elements of A Healthy ChurchJayhia Malaga JarlegaNo ratings yet
- Corality ModelOff Sample Answer Hard TimesDocument81 pagesCorality ModelOff Sample Answer Hard TimesserpepeNo ratings yet
- Metric MIL-STD-1504C (USAF) 01 March 2007 Supersedes MIL-STD-1504B 8 June 1989Document11 pagesMetric MIL-STD-1504C (USAF) 01 March 2007 Supersedes MIL-STD-1504B 8 June 1989HenryNo ratings yet
- River Planning AetasDocument4 pagesRiver Planning AetasErika ReyesNo ratings yet
- Jurnal Stamina: E-ISSN 2655-2515 P-ISSN 2655-1802Document9 pagesJurnal Stamina: E-ISSN 2655-2515 P-ISSN 2655-1802Yogi TioNo ratings yet
- United States Court of Appeals, Third CircuitDocument18 pagesUnited States Court of Appeals, Third CircuitScribd Government DocsNo ratings yet
- Lust V Animal Logic MSJ OppositionDocument34 pagesLust V Animal Logic MSJ OppositionTHROnlineNo ratings yet
- 1GR FE LubricationDocument19 pages1GR FE LubricationJesus LayaNo ratings yet
- SIConitDocument2 pagesSIConitJosueNo ratings yet
- Eligibility To Become IAS Officer: Career As A IAS Officer About IAS OfficerDocument4 pagesEligibility To Become IAS Officer: Career As A IAS Officer About IAS Officersamiie30No ratings yet
- Vishnu Institute of Technology: V2V CommunicationsDocument22 pagesVishnu Institute of Technology: V2V CommunicationsBhanu PrakashNo ratings yet
- Ebook Principles of Corporate Finance PDF Full Chapter PDFDocument67 pagesEbook Principles of Corporate Finance PDF Full Chapter PDFmichelle.haas303100% (28)
- Project On Brand Awareness of ICICI Prudential by SajadDocument99 pagesProject On Brand Awareness of ICICI Prudential by SajadSajadul Ashraf71% (7)
- SRB 301 Ma Operating Instructions Safety-Monitoring ModulesDocument6 pagesSRB 301 Ma Operating Instructions Safety-Monitoring ModulesMustafa EranpurwalaNo ratings yet