Professional Documents
Culture Documents
ALERT+Prevent+Grocer+Malware+Attacks 04112013
Uploaded by
TextbookCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
ALERT+Prevent+Grocer+Malware+Attacks 04112013
Uploaded by
TextbookCopyright:
Available Formats
VIS A D AT A SECUR IT Y ALERT
11 April 2013
Preventing Memory-Parsing Malware Attacks on Grocery Merchants
Since January 2013, Visa has seen an increase in network intrusions involving grocery merchants. Once inside a merchants network, hackers install memory-parsing malware on Windows-based cash register systems or back-ofhouse (BOH) servers to extract full magnetic-stripe data. The malware is configured to hook into certain payment application binaries. These binaries are responsible for processing authorization data, which includes full magnetic-stripe data. When authorization data is processed, the payment application decrypts the transaction on the cash register system or BOH server and stores the authorization data in random access memory (RAM). The data must be decrypted for the authorization to be completed, so hackers are accessing full track data when it is stored in RAM and using malware such as memory-parsers to steal it. Hackers are also using anti-forensic techniques such as tampering with or deleting security event logs, using strong encryption or modifying security applications (e.g., whitelist malware files) to avoid detection. The malware can be configured or compiled to work on merchant segments other than grocery merchants. At this time, it is known to affect only Windows operating systems. Visa is offering guidance to help clients secure their networks and protect their Windows-based point-of-sale (POS) and BOH systems from unauthorized access. A list of malware signatures is included in this article, and Visa highly recommends that clients implement these signatures in their security solutions. Recommended Mitigation Strategies The following mitigation strategies, broken down into four categories, are a defense-in-depth approach to minimizing the possibility of an attack and mitigating the risk of data compromise: Network Security o Review firewall configurations and ensure that only allowed ports, services and Internet protocol (IP) addresses are communicating with your network. This is especially critical for outbound (e.g., egress) firewall rules, in which compromised entities allow ports to communicate to any IP address on the Internet. Hackers leverage this misconfiguration to exfiltrate data to their IP addresses. Segregate payment processing networks from other networks. Apply access control lists (ACLs) on the router configuration to limit unauthorized traffic to payment processing networks. Create strict ACLs segmenting public-facing systems and backend database systems that house payment card data.
o o
Cash Register and POS Security
Implement hardware-based point-to-point encryption. Visa recommends EMV-enabled PIN-entry devices or other credit-only accepting devices that have Secure Reading and Exchange of Data (SRED) capabilities. SRED-approved devices can be found at the Payment Card Industry Security Standards website. Install Payment Application Data Security Standard-compliant payment applications. Deploy the latest version of an operating system and ensure it is up-to-date with security patches, anti-virus software, file integrity monitoring, and a host-based intrusion-detection system. Assign a strong password to security solutions to prevent application modification.
Visa Public 1
o o
o o
Perform a binary or checksum comparison to ensure unauthorized files are not installed. Ensure any automatic updates from third parties are validated. This means performing a checksum comparison on the updates prior to deploying them on POS systems. Visa recommends that merchants work with their POS vendors to obtain signatures and hash values to perform this checksum validation. Disable unnecessary ports and services, null sessions, default users and guests. Enable logging of events and make sure there is a process to monitor logs on a daily basis. Implement least privileges and ACLs on users and applications on the system.
o o o
Administrative Access o Use two-factor authentication when accessing payment processing networks. Even if a virtual private network is used, it is important that two-factor authentication is implemented to help mitigate key-logger or credentialdumping attacks. Limit administrative privileges for users and applications. Periodically review systems (local and domain controllers) for unknown and dormant users.
o o
Incident Response o Deploy a Security Information and Event Management (SIEM), a system that serves as a central point for managing and analyzing events from network devices. A SIEM has two primary responsibilities: o o Aggregates events and logs from network devices and applications. Uses intelligence to analyze and uncover malicious behavior on the network.
Offload logs to a dedicated server in a secure location where unauthorized users cant tamper with them. Invest in a dedicated incident response team (IRT) that has the knowledge, training and certification to respond to a breach. For more information on IRT training, visit the SANS Institute website. Test and document incident-response plans to identify and remediate any gaps prior to an attack. Plans should be updated periodically to address emerging threats.
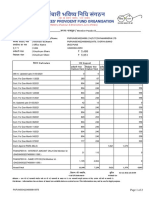
Malware Signatures The following malware signatures were identified during recent grocery store breaches. Merchants should implement these signatures to help detect a potential data breach on their systems. Size (Bytes) 118272 64512 106496 97792 179200 2772
File Name rtcli.dll mstdc.exe mstdc.bak msaudit.dll mn32.exe si.vbs
Description Information stealer / downloader Backdoor Backdoor Memory-parsing malware Prefetch file indicating execution of the malicious code Visual basic script used by hacker to deploy malware onto POS systems Anti-forensic utility to remove malware from POS systems
Visa Public 2
MD5 Hash Value 4bd819d9e75e4e8ecf1a9599f44af12a 57703973ff74503376a650224aa43dfa 67ed156e118b9aa65ed414a79633a3d4 27bfffa7d034a94b79d3e6ffdda50084 89a8844c1214e7fc977f026be675a92a 40efe7632b01116eefaba438c9bcee34
sd32.exe
134000
9c3a1d3829c7a46d42d5a19fe05197f3
73728 TcpAdaptorService.exe Memory-parsing malware 118784 Osql.exe, svchosts.exe oposwin.exe svcmon.exe nYmTxGSJhLLFfagQ.bat tbcsvc.exe mssec.exe msproc.exe Tool used with TcpAdaptorService.exe to send track data to bad IP Memory-parsing malware Memory-parsing malware Batch file used to whitelist malware executables on FIM Performs cryptographic operations Attempts outbound communication via port 443 Malicious unknown purpose 122880 245760 253952 74 293583 135242 184128
cfee737692e65e0b2a358748a39e3bee 85f94d85cfeff32fa18d55491e355d2b 4b9b36800db395d8a95f331c4608e947 3446cd1f4bee2890afc2e8b9e9eb76a2 0fff972080248406103f2093b6892134 eae4718ea5a860cc372b5728e96af656 1aa662d329cc7c51d2e9176024fedee8 d7e5e85ccb6c71a39b99a9228313cc33 2e567707730ed2c76b162a97dcf28c05
To request information or report a data breach, contact Visa Fraud Control: Asia Pacific Region, Central Europe/Middle East/Africa Region: VIFraudControl@visa.com Canada Region, Latin America Region, United States: USFraudControl@visa.com
Visa Public 3
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (890)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (587)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (265)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (72)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (119)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- Aslan 2017Document8 pagesAslan 2017Ana Maria Montoya GomezNo ratings yet
- Indian Construction Company Email ListxlsDocument66 pagesIndian Construction Company Email Listxlstaksh.vadaNo ratings yet
- Answer Key: Outcomes AdvancedDocument2 pagesAnswer Key: Outcomes AdvancedGERESNo ratings yet
- A Study On Hyper-Threading: Vimal Reddy Ambarish Sule Aravindh AnantaramanDocument29 pagesA Study On Hyper-Threading: Vimal Reddy Ambarish Sule Aravindh AnantaramanVijay ShebannavarNo ratings yet
- Roof Mounted Equipement For Washing-MaintenanceDocument10 pagesRoof Mounted Equipement For Washing-MaintenanceGino TironiNo ratings yet
- Unit 5 NotesDocument7 pagesUnit 5 Notesapi-240095195No ratings yet
- Description: Power Distribution Module eQ38XXDocument4 pagesDescription: Power Distribution Module eQ38XXusamakhan20567% (3)
- Kinase InhibitorDocument85 pagesKinase InhibitorSowjanya NekuriNo ratings yet
- International Standard: Specification and Qualification of Welding Procedures For Metallic Materials - General RulesDocument8 pagesInternational Standard: Specification and Qualification of Welding Procedures For Metallic Materials - General RulesRudi DaNo ratings yet
- LNL Iklcqd /: Grand Total 11,109 7,230 5,621 1,379 6,893Document2 pagesLNL Iklcqd /: Grand Total 11,109 7,230 5,621 1,379 6,893Dawood KhanNo ratings yet
- English 8Document8 pagesEnglish 8John Philip PatuñganNo ratings yet
- AW4416 Overall Circuit DiagramDocument154 pagesAW4416 Overall Circuit DiagramCarlosNo ratings yet
- Inquiry Project Process ChartDocument5 pagesInquiry Project Process Chartapi-260189193No ratings yet
- ZXA10 F822 Datasheet: Interface Function Physical PerformanceDocument1 pageZXA10 F822 Datasheet: Interface Function Physical PerformanceyodreshNo ratings yet
- CVD - Deployment Guide For Cisco HyperFlex 2.5 For Virtual Server InfrastructureDocument234 pagesCVD - Deployment Guide For Cisco HyperFlex 2.5 For Virtual Server Infrastructurekinan_kazuki104100% (1)
- Introduction to Essay WritingDocument20 pagesIntroduction to Essay WritingTaiyaki Đậu ĐỏNo ratings yet
- Dynamic and Static Ropes: ManualDocument34 pagesDynamic and Static Ropes: ManualKhomeini AchmadNo ratings yet
- What is a Bull Trap? Detecting False BreakoutsDocument2 pagesWhat is a Bull Trap? Detecting False BreakoutsAli Abdelfatah MahmoudNo ratings yet
- Sustainability Report 2020 ToyotaDocument36 pagesSustainability Report 2020 ToyotaMonicaNo ratings yet
- General Biology Reviewer 2Document4 pagesGeneral Biology Reviewer 2nd555No ratings yet
- E21 Btech Viii 1240Document214 pagesE21 Btech Viii 1240tag slickNo ratings yet
- CV GonzaloValle G-CDocument1 pageCV GonzaloValle G-Cgonzalo valleNo ratings yet
- The Heart's Chambers and ValvesDocument29 pagesThe Heart's Chambers and ValvesomarNo ratings yet
- Manual de Interlock ELEKTADocument448 pagesManual de Interlock ELEKTANicolas RonchiNo ratings yet
- Tổng mạch điện ECU PRO-NEW-3 PDFDocument260 pagesTổng mạch điện ECU PRO-NEW-3 PDFNhật ĐặngNo ratings yet
- Jak1 Aur El DWG A 0 9033 (D)Document1 pageJak1 Aur El DWG A 0 9033 (D)Budi HahnNo ratings yet
- Fun Tricky Riddles For KidsDocument4 pagesFun Tricky Riddles For Kidstauki63100% (1)
- Experimental Investigation of The Stress-Stretch Behavior of EPDM Rubber With Loading Rate EffectsDocument20 pagesExperimental Investigation of The Stress-Stretch Behavior of EPDM Rubber With Loading Rate EffectsPaulo Venicio Alves VieiraNo ratings yet
- ARTIKEL PLP 1 SMKN 1 SRAGEN - PAI31 FIX v2Document24 pagesARTIKEL PLP 1 SMKN 1 SRAGEN - PAI31 FIX v211 Faisa Rafi Ramadhan PAINo ratings yet
- HTAR FormularyDocument204 pagesHTAR FormularyMay TanNo ratings yet