Professional Documents
Culture Documents
ISEHV7 Course Calendar
Uploaded by
Appin NitinOriginal Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
ISEHV7 Course Calendar
Uploaded by
Appin NitinCopyright:
Available Formats
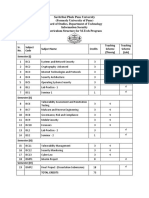
APPIN TECHNOLOGY LAB
FRONT RUNNER DIPLOMA PROGRAM INFORMATION SECURITY AND ETHICAL HACKING V7 Class-wise Course Calendar (2012-2013)
Total Duration Theory Sessions Practical Sessions Project Work 216 Hours (6 months) 72 hours 48 Classes 72 hours 48 Labs 72 hours
S no 1.
2.
3.
4.
Description Class 1 Lab 1 Class 2 Lab 2 Class 3 Lab 3 Class 4 Lab 4 Class 5 Lab 5 Class 6 Lab 6 Class 7 Lab 7 Class 8 Lab 8 Class 9 Lab 9 Class 10 Lab 10 Class 11 Lab 11 Class 12 Lab 12 Class 13 Lab 13 Class 14 Lab 14 Class 15 Lab 15 Class 16 Lab 16
Module
INTRODUCTION TO INFORMATION SECURITY AND ETHICAL HACKING -DODESKTOP AND SERVER SECURITY -DO-DODATA SECURITY -DO-DO-DO-DONETWORK SECURITY -DO-DO-DO-DO-DO-
APPIN TECHNOLOGY LAB
Class 17 Lab 17 Class 18 Lab 18 Class 19 Lab 19 Class 20 Lab 20 Class 21 Lab 21 Class 22 Lab 22 Class 23 Lab 23 Class 24 Lab 24 Class 25 Lab 25 Class 26 Lab 26 Class 27 Lab 27 Class 28 Lab 28 Class 29 Lab 29 Class 30 Lab 30 Class 31 Lab 31 Class 32 Lab 32 Class 33 Lab 33 Class 34 Lab 34 Class 35 Lab 35 Class 36 Lab 36 Class 37 Lab 37 Class 38 Lab 38 Class 39 Lab 39 Class 40 Lab 40 Class 41 Lab 41
-DO-DO-DO-DO-DO-DOWEB SECURITY -DO-DO-DOVAPT -DO-DOHACKING ATTACKS -DO-DOINFORMATION SECURITY MANAGEMENT SYSTEM -DO-DO-DO-DO-DO-DO-DOCYBER LAWS AND IT ACTS
5.
6.
7.
8.
9.
APPIN TECHNOLOGY LAB
10. Class 42 Lab 42 Class 43 Lab 43 Class 44 Lab 44 Class 45 Lab 45 Class 46 Lab 46 Class 47 Lab 47 Class 48 Lab 48
-DOCYBER FORENSICS -DO-DO-DO-DO-DO-
Note: *Class/Lab Session can be taken depending on the availability of faculty/lab/class.
THEORY SESSION: 72 HOURS
MODULE: INTRODUCTION TO INFORMATION SECURITYAND ETHICAL HACKING
Class 1 INFORMATION SECURITY AND HACKING COMBO
ESSENTIAL TERMINOLOGIES SECURITY AND ITS NEED WHY IS IT SECURITY NECESSARY? IT SECURITY SERVICES LIFE CYCLE OPERATING SYSTEM BASICS DATA COMMUNICATION BASICS BASICS OF COMPUTER NETWORKING
1.5 Hours
Class 2
OSI AND TCP/IP MODEL TCP VS UDP TCP FRAME STRUCTURE UDP FRAME STRUCTURE TCP COMMUNICATION FLAGS NETWORKING DEVICES CYBER THREATS AND ISSUES AN APPROACH TOWARDS HACKING PROTECTING YOUR COMPUTER AND NETWORK SOFTWARE SECURITY FOR PORTABLE COMPUTERS DEFENDING AGAINST SOCIAL ENGINEERS AND PHISHERS PROTECTING YOUR PASSWORD AND LOGGING ON SECURELY HOW PASSWORDS GET CRACKED
1.5 Hours
APPIN TECHNOLOGY LAB
TOP 4 METHODS TO HACK FACEBOOK PASSWORD WITHIN 5 MIN SELECTING TOOLS SAFETY RULES
MODULE: DESKTOP AND SERVER SECURITY
UNIT 1: DESKTOP AND SERVER SECURITY Class 3
INTRODUCTION SECURING YOUR MIGRATED WINDOWS 7 DESKTOP DESKTOPS: LOCAL RIGHTS AND PRIVILEGES OVERALL DESKTOP SECURITY WHAT IS REGISTRY? REGISTRY EDITING BACKUPS AND RECOVERY POLICY WINDOWS 9X OPERATING SYSTEMS STEPS TO CREATE REGISTRY VALUES SOME OF THE EXAMPLES TO CHANGE THE REGISTRY DEFAULT SETTINGS NT SECURITY THE LOGON PROCESS SECURITY ARCHITECTURE COMPONENTS INTRODUCTION TO SECURING IN NT BOX BACKUPS WINDOWS VULNERABILITIES AND THREATS DETERMINING IF YOU ARE ACTIVELY BEING COMPROMISED
1.5 Hours
Class 4
CLIENT SERVER ARCHITECTURE SERVER SECURITY PRINCIPLES SECURING THE SERVER OPERATING SYSTEM APPLICATIONS AND NETWORK PROTOCOLS CONFIGURE OS USER AUTHENTICATION WINDOWS 8 INTRODUCTION AND SECURITY
1.5 Hours
Class 5 UNIT 2: LINUX SECURITY INTRODUCTION
1.5 Hours
BENEFITS OF LINUX HOW SECURE SHOULD MY LINUX BE? LAYERS OF LINUX/UNIX LINUX DIRECTORY STRUCTURE (FILE SYSTEM STRUCTURE) EXPLAINED WITH EXAMPLES
APPIN TECHNOLOGY LAB
WHY SHADOW YOUR PASSWORD FILE? WHAT IF UNSHADOW PASSWORD? HOW TO SET UP A FIREWALL UNDER LINUX? SECURING AND HARDENING TIPS LINUX SYSTEMS WINDOWS VS. LINUX DESIGN REALISTIC SECURITY AND SEVERITY METRICS CERT VULNERABILITY NOTES DATABASE RESULTS
MODULE: DATA SECURITY
Class 6
INTRODUCTION OVERVIEW DATA SECURITY MANAGEMENT CHARACTERISTICS OF ACCESS SECURITY IN THE SYSTEM DATA SECURITY ISSUES AND SOLUTIONS INTRODUCTION TO CLOUD COMPUTING PROTECTING THE USERS CLOUD COMPUTING IN REAL DOMAIN BENEFITS FROM CLOUD COMPUTING
1. 5 Hours
UNIT 2: DATABACKUP Class 7
DATA BACKUP INTRODUCTION DATA BACKUP STRATEGIES OFFLINE DATA BACKUP ONLINE DATA BACKUP
1. 5 Hours
UNIT 3: CRYPTOGRAPHY Class 8
1.5 Hours
STRENGTH OF THE CRYPTOGRAPHY GOALS OF CRYPTOGRAPHY SOME TECHNICAL TERMS TYPES OF CIPHER TEXT TYPES OF CRYPTOGRAPHY DATA ENCRYPTION STANDARD (DES) IDEA: INTERNATIONAL DATA ENCRYPTION ALGORITHM
Class 9
ASYMMETRIC CRYPTOGRAPHY RSA ALGORITHM
1. 5 Hours
APPIN TECHNOLOGY LAB
HASH FUNCTIONS DIGITAL SIGNATURES DIGITAL CERTIFICATION
UNIT 4: STEANOGRAPHY Class 10
OVERVIEW HOW DOES IT WORK? STEGANOGRAPHY IN IMAGES STEGANOGRAPHY IN AUDIO GENETIC ALGORITHM APPROACH STEGANOGRAPHY IN VIDEO
1. 5 Hours
MODULE: NETWORK SECURITY
UNIT 1: MOBILE SECURITY Class 11
INTRODUCTION WHAT IS MOBILE? ARCHITECTURE OF MOBILE COMMUNICATION MOBILE GENERATION TECHNOLOGY OF MOBILE COMMUNICATION MOBILE PHONE STANDARDS PROTOCOLS USED IN MOBILE INTRODUCTION TO SMS MESSAGING SIM
1. 5 Hours
Class 12
1.5 Hours
INTRODUCTION TO MOBILE OS POPULAR OPERATING SYSTEMS BLACKBERRY OS FROM RIM IOS FROM APPLE INC SYMBIAN OS WINDOWS PHONE OS SAMSUNG BADA WHAT IS NFC, HOW IT WORKS AND WHAT ARE ITS PRACTICAL APPLICATIONS WHY IS MOBILE SECURITY IMPORTANT? MOBILE PLATFORM COMPARISON MOBILE THREATS TRENDS OF MOBILE THREATS WHAT IS BLUETOOTH? & HOW DOES IT WORK?? HOW BLUETOOTH CREATES A CONNECTION BLUETOOTH ATTACKS ON MOBILE PHONES
APPIN TECHNOLOGY LAB
BLUETOOTH WEAKNESSES MOBILE SAFEGUARDS AND SOLUTIONS
UNIT 2: VOICE OVER INTERNET PROTOCOL Class 13
1.5 Hours
DEFINITION & TRENDS SERVICES TYPES OF VOIP COMPONENTS OF VOIP IP TELEPHONY & IP PAGING PROTOCOLS AND ACRONYMS REASONS FOR VOIP PROBLEMS IN VOIP SKYPE VOIP SECURITY SCENARIO HOW DO WE SECURE VOIP?
UNIT 3: VIRTUAL PRIVATE NETWORK SECURITY Class 14
INTRODUCTION TO VPN APPLICATION & REQUIREMENTS OF VPN VPN TYPES OPEN VPN
1.5 Hours
Class 15
1.5 Hours
MODELS OF VPN IPSEC VPN VPN SECURITY FRAMEWORK VPN SECURITY ISSUES OTHER VPN THREATS
UNIT 4: WIRELESS LAN Class 16
INTRODUCTION 802.11 STANDARDS OF WLAN BASICS OF WIRELESS LAN ANTENNAS ACCESS POINT POSITIONING ROGUE ACCESS POINT WIRED EQUIVALENT PRIVACY DOS ATTACK
1.5 Hours
APPIN TECHNOLOGY LAB
MAN IN MIDDLE ATTACK (MITM) COUNTERMEASURES FOR WLAN TOOLS WIRELESS INTRUSION DETECTION OPEN SOURCE SCANNING SOFTWARE
UNIT 5: ROUTER SECURITY Class 17
WHAT IS A ROUTER? STATIC AND DYNAMIC ROUTING WORK TO ROUTER KEEPING THE MESSAGES MOVING DIRECTING TRAFFIC TRANSMITTING PACKETS KNOWING WHERE TO SEND DATA MAC ADDRESSES UNDERSTANDING THE PROTOCOLS TRACING THE MESSAGE
1.5 Hours
Class 18
DENIAL OF SERVICE ATTACK CONFIGURATION OF ROUTER PROTOCOLS ON A ROUTER RFC 1483 HANDSHAKE PROTOCOLS NAT (NETWORK ADDRESS TRANSLATION) NAPT SERVICES ADSL DETAILS TROUBLE SHOOTING ROUTING TABLE PROBLEMS VARIOUS TYPES OF ATTACKS SECURING THE ROUTERS
1.5 Hours
UNIT 6: INTRUSION DETECTION AND PREVENTION Class 19
INTRODUCTION INTRUSION DETECTION AND PREVENTION IDS NEED OF IDS COMPONENTS
1.5 Hours
APPIN TECHNOLOGY LAB
TYPES WHAT IS NOT AN IDS?
Class 20
DETECTION METHODOLOGIES VARIOUS TOOLS AVAILABLE LIMITATIONS OF IDS INTRUSION PREVENTION SYSTEM TYPES NETWORK BASED IPS COUNTER MEASURES TAKEN BY AN IPS RISKS INVOLVE
1.5 Hours
UNIT 7: ACCESS CONTROL SYSTEM Class 21
INTRODUCTION: WHAT IS ACCESS CONTROL ACCESS CONTROL IN PHYSICAL SECURITY ACCESS CONTROL IN INFORMATION SECURITY NEED OF AN ACCESS CONTROL SYSTEM SOME CONCEPTS RELATED TO ACCESS CONTROL POLICIES, MODELS, AND MECHANISMS
1.5 Hours
Class 22
ACCESS CONTROL TECHNIQUES NON-DISCRETIONARY ACCESS CONTROL MANDATORY ACCESS CONTROL (MAC) ROLE-BASED ACCESS CONTROL LATTICE BASED ACCESS CONTROL TEMPORAL CONSTRAINTS WORKFLOW CHINESE WALL ACCESS CONTROL MODELS ACCESS CONTROL MANAGEMENT INTRODUCTION
1.5 Hours
MODULE: WEB SECURITY
UNIT 1: LAN SECURITY Class 23
THE INITIAL INTERNETTING CONCEPTS INTRODUCTION TO LAN WHY LAN SECURITY IS IMPORTANT LAN/WAN COMPONENTS
1.5 Hours
APPIN TECHNOLOGY LAB
TOPOLOGY PROTOCOLS THREATS OF LAN INAPPROPRIATE ACCESS TO LAN RESOURCES DISCLOSURE OF DATA UNAUTHORIZED MODIFICATION OF DATA AND SOFTWARE DISCLOSURE OF LAN TRAFFIC SPOOFING OF LAN TRAFFIC DISRUPTION OF LAN FUNCTIONS SECURITY SERVICES AND MECHANISMS HACKING MAC ADDRESS NETWORK SCANNERS TYPES OF SCANNING SCANNING METHODOLOGY
UNIT 2: FIREWALL SECURITY Class 24
1.5 Hours
FIREWALLS WORKING OF FIREWALL TYPES OF FIREWALL PROXY SERVER WHY PROXYING? WORKING OF PROXY SERVER ADVANTAGES OF PROXYING DISADVANTAGE OF PROXYING APPLICATIONS OF FIREWALL
UNIT 3: INTERNET SECURITY Class 25
INTRODUCTION SECURITY ATTACKS AND SECURITY PROPERTIES THREATS FACED ON INTERNET INTRODUCTION TO IP ADDRESSES FINDING IP ADDRESS OF A REMOTE SYSTEM HIDING YOUR IDENTITY: ANONYMOUS SURFING PROXIES SERVERS WHAT IS A SOCKS PROXY SERVER?
1.5 Hours
UNIT 4: E-MAIL SECURITY Class 26
INTRODUCTION
1.5 Hours
APPIN TECHNOLOGY LAB
HISTORY OF E-MAIL EMAIL ADDRESSES HOW E-MAIL WORKS? VARIOUS MAIL SERVERS E-MAIL PROTOCOLS ANALYSIS OF EMAIL HEADERS EMAIL TRACKING IP TRACKING USING EMAIL SPAMMING WAYS TO PREVENT SPAM SECURITY THREATS TO YOUR EMAIL COMMUNICATIONS SETUP EMAIL FILTER IN GMAIL, HOTMAIL & YAHOO HOW TO STEAL DATA FROM AN E-MAIL? E-MAIL EXCHANGE SERVER SECURITY VIRUS PROTECTION RPC OVER HTTP PROTECTING FRONT-END SERVERS KEEP EXCHANGE SERVER UP-TO-DATE CYBER LAWS REGARDING SPAMMING SECURITY POLICIES
MODULE: VAPT
UNIT 1: Class 27
INTRODUCTION IMPORTANT TECHNICAL TERMS INFORMATION GATHERING SCANNING AND FINGERPRINTING
1.5 Hours
UNIT 2: VULNERABILITY ASSESSMENT Class 28
1.5 Hours
VULNERABILITIES VULNERABILITY ASSESSMENT PROTECTIVE MEASURES GENERAL APPROACH FOOTPRINTING VULNERABILITY ASSESSMENT: THE RIGHT TOOLS TO PROTECT YOUR CRITICAL DATA TYPES OF VULNERABILITY ASSESSMENT THE CHALLENGES OF VULNERABILITY ASSESSMENTS TOOLS FOR VA NETWORK SECURITY AUDIT CASE STUDY
APPIN TECHNOLOGY LAB
UNIT 3: PENETRATION TESTING Class 29
INTRODUCTION AND METHODOLOGY TYPES OF PENETRATION TESTS METHODOLOGY PENETRATION TESTING APPROACH PENETRATION TESTING VS VULNERABILITY ASSESSMENT HOW VULNERABILITIES ARE IDENTIFIED A SAMPLE PENETRATION TESTING REPORT SECURITY SERVICES SECURITY SERVICES MANAGEMENT TOOLS FIREWALL AUTOMATED VULNERABILITY SCANNING AN APPROACH TO VULNERABILITY SCANNING PASSWORD CRACKING AND BRUTE FORCING DENIAL OF SERVICE (DOS) TESTING PENETRATION TESTING TOOLS ESCALATION OF PRIVILEGES CASE STUDIES
1.5 Hours
MODULE: HACKING ATTACKS
UNIT 1: MALWARES Class 30
INTRODUCTION TO MALWARES TYPES OF MALWARES INSTALLING BOTS ON TARGET MACHINES ATTACKING METHODS WORKING OF BOTS MALWARE DETECTION TECHNIQUES COUNTER MEASURES
1.5 Hours
UNIT 2: HACKING ATTACKS Class 31
INTRODUCTION TO ATTACKS TYPES OF ATTACKS NON-TECHNICAL ATTACK TABNABBING: A NEW TYPE OF PHISHING ATTACK TECHNICAL ATTACKS PASSWORD ATTACKS BACKTRACK BACKDOOR
1.5 Hours
APPIN TECHNOLOGY LAB
ROOTKITS MALWARE GLOSSARY
UNIT 3: ART OF GOOGLING Class 32
INTRODUCTION THE GOOGLE TOOLBAR SEARCHING TECHNIQUES DIRECTORY LISTING LOCATING CGI-BIN LOCATING ROBOTS.TXT CAMERA HACKING SOME TRICKS THE HARVESTER TOOL ARTICLES
1.5 Hours
MODULE: INFORMATION SECURITY MANAGEMENT SYSTEM
UNIT 1: SECURITY AUDITING Class 33
INTRODUCTION BACKGROUND SECURITY AUDITING OBJECTIVES
1.5 Hours
Class 34
RISK INVOLVED AUDITING STEPS
1.5 Hours
UNIT 2: LEAD AUDITOR: IT (LA-27001 Class 35 To 40
9 Hours
INFORMATION SECURITY AND MANAGEMENT SYSTEM CRITICAL CONTROL: INCIDENT RESPONSE CAPABILITY CRITICAL CONTROL: SECURITY SKILLS ASSESSMENT AND APPROPRIATE TRAINING TO FILL GAPS CRITICAL CONTROL: DATA LOSS PREVENTION CRITICAL CONTROL 14: WIRELESS DEVICE CONTROL MANAGING SECURITY AWARENESS RISK ASSESSMENT, BUSINESS CONTINUITY AND DISASTER SECURITY MANAGEMENT PRACTICES AND FRAMEWORK
MODULE: CYBER LAWS AND IT ACTS
Class 41
INTRODUCTION
1.5 Hours
APPIN TECHNOLOGY LAB
CYBER LAWS: INTERNATIONAL PERSPECTIVE E-GOVERNANCE IMPEDIMENTS IN IMPLEMENTING E-GOVERNANCE PROJECTS FROM LEGAL PERSPECTIVE ANALYSIS OF PROBLEMS REPERCUSSIONS
Class 42
1.5 Hours
RELEVANT LAWS JURISPRUDENCE OF INDIAN CYBER LAW THE INFORMATION TECHNOLOGY ACT, 2000 (SOME LAWS) AMENDMENT TO THE IT ACT 2000 BY ITAA2008 ADVANTAGES OF CYBER LAWS PROSECUTION OF CYBER CRIMES UNDER INDIAN CYBER LAWS (IT ACT, 2000) PROBABLE SOLUTIONS ARTICLES ON CYBER LAWS CASES ON CYBER LAWS
MODULE: CYBER FORENSICS
UNIT 1: CYBER CRIME Class 43
INTRODUCTION TO CYBER FORENSICS FORENSICS PROCEDURES HISTORY OF COMPUTER FORENSICS CYBER SECURITY & FORENSICS WHAT IS CYBER CRIMES? CYBER CRIMINALS MODE AND MANNER OF COMMITTING CYBER CRIME
1.5 Hours
Class 44
1.5 Hours
UNDERSTAND THE FUNDAMENTALS CLASSIFICATION OF CYBER CRIME WHY LEARN ABOUT CYBER CRIME TYPES OF CYBER CRIME CHARACTERISTICS OF COMPUTER CRIME PREVENTION OF CYBER CRIME QUESTIONNAIRE BASED ON RECOMMENDATIONS FROM THE FOURTH MEETING OF GOVERNMENTAL EXPERTS ON CYBER-CRIME
UNIT 2: CYBER FORENSICS Class 45
CYBER FORENSICS: DETAILED VIEW DIGITAL EVIDENCE CHALLENGES OF FORENSIC SCIENCE
1.5 Hours
APPIN TECHNOLOGY LAB
Class 46
FORENSIC METHODOLOGY SOME FORENSIC SOFTWARES/ HARDWARES BASIC APPROACHES FORENSICS TOOLS EXAMPLE
1.5 Hours
UNIT 3: CATCHING CRIMINALS Class 47
CYBER TERRORISM- THE DARK SIDE OF THE WEB WORLD HONEY POTS
1.5 Hours
UNIT 4: MOBILE FORENSICS Class 48
INTRODUCTION TO MOBILE FORENSICS GENERAL PHONES (NOKIA, SAMSUNG, LG) BLACKBERRY DEVICES CHINESE DEVICES EXTRACTION METHODS OF MOBILE FORENSICS MOBILE PHONE CHARACTERISTICS MOBILE FORENSIC ANALYSIS THE CHALLENGES OF MOBILE FORENSICS TOOLS FOR MOBILE FORENSICS FORENSIC TOOLKIT CHECKLIST OF TOOLS FOR CYBER FORENSICS
1.5 Hours
You might also like
- SOC Analyst Cyber Security Intrusion Training From ScratchDocument3 pagesSOC Analyst Cyber Security Intrusion Training From ScratchHitesh RahangdaleNo ratings yet
- Certified Ethical Hacker Cehv12 Course ContentDocument23 pagesCertified Ethical Hacker Cehv12 Course ContentM3iatNo ratings yet
- Cpte 2018Document10 pagesCpte 2018Ankit BinjolaNo ratings yet
- (ISC)2 CISSP Certified Information Systems Security Professional Official Study GuideFrom Everand(ISC)2 CISSP Certified Information Systems Security Professional Official Study GuideRating: 2.5 out of 5 stars2.5/5 (2)
- Information Security & Ethical Hacking Course ContentDocument12 pagesInformation Security & Ethical Hacking Course Contentappin_modinagarNo ratings yet
- ISEHV7 Course ContentDocument12 pagesISEHV7 Course ContentAppin NitinNo ratings yet
- Information SecurityDocument11 pagesInformation SecurityAppin Technology LabNo ratings yet
- Course Content - Information Security PDFDocument13 pagesCourse Content - Information Security PDFAvaneet RanjanNo ratings yet
- ISEH FRP Course Curriculumr 2010-11Document9 pagesISEH FRP Course Curriculumr 2010-11darkaj9No ratings yet
- NetworkSecurityISO Lesson Plan1Document3 pagesNetworkSecurityISO Lesson Plan1KarpagamSivakumarNo ratings yet
- CSE Live SyllabusDocument18 pagesCSE Live SyllabusAkbar ShakoorNo ratings yet
- Penetration Testing Professional: The World's Premier Online Penetration Testing CourseDocument55 pagesPenetration Testing Professional: The World's Premier Online Penetration Testing CourseMehmet Emin OzmenNo ratings yet
- CSE2008 SyllabusDocument2 pagesCSE2008 SyllabusABHAY POTLURI 20BCI0017No ratings yet
- Syllabus PTPDocument48 pagesSyllabus PTPkaxamNo ratings yet
- Computer Networks Security From Scratch To Advanced: Dr. Mohammad AdlyDocument14 pagesComputer Networks Security From Scratch To Advanced: Dr. Mohammad AdlyRichthofen Flies Bf109No ratings yet
- Syllabus PTSV3Document21 pagesSyllabus PTSV3Pablito Quispe RuizNo ratings yet
- ECSA Course OutlineDocument27 pagesECSA Course Outlinejeroc84879No ratings yet
- Ec Council Certified Security Analyst Ecsa v8Document5 pagesEc Council Certified Security Analyst Ecsa v8fazli3036No ratings yet
- EC-Council - Certified Security Analyst: Course Introduction Student IntroductionDocument30 pagesEC-Council - Certified Security Analyst: Course Introduction Student IntroductionSalman AslamNo ratings yet
- Cyber Security and ApplicationsDocument4 pagesCyber Security and Applicationssj2100333No ratings yet
- Network CsDocument5 pagesNetwork Csnotsubhash2000No ratings yet
- Pune University IS Tech. SyllabusDocument9 pagesPune University IS Tech. SyllabusPav TechnicalsNo ratings yet
- CSE Flex Syllabus 1Document15 pagesCSE Flex Syllabus 1Zachary CurtisNo ratings yet
- CS8792 Course File FormatDocument93 pagesCS8792 Course File FormatnancypeterNo ratings yet
- CICSA BrochureDocument32 pagesCICSA Brochuregguk zomaro100% (1)
- CT037 3.5 2 Network SecurityDocument6 pagesCT037 3.5 2 Network SecurityYogeswaran NathanNo ratings yet
- Ec Council Certified Security Analyst Ecsa v8Document5 pagesEc Council Certified Security Analyst Ecsa v8CArlos chileNo ratings yet
- C CC C CC C CCCCCCC ! "! #C#CC C$$C%$$%C %&C' ( + (C C CCCC C CDocument24 pagesC CC C CC C CCCCCCC ! "! #C#CC C$$C%$$%C %&C' ( + (C C CCCC C CSyed AshmadNo ratings yet
- Module 1: Cyber Security FundamentalsDocument6 pagesModule 1: Cyber Security FundamentalsAravind VbkNo ratings yet
- 19isdfs KW PresentationDocument22 pages19isdfs KW PresentationMeir ZushnovNo ratings yet
- Hand Out Network SecurityDocument6 pagesHand Out Network SecurityKopparapu SiddarthaNo ratings yet
- I.T Engg Sem-VIDocument14 pagesI.T Engg Sem-VIMuvin KoshtiNo ratings yet
- CPENTbrochureDocument9 pagesCPENTbrochuremy lover IamNo ratings yet
- JNCIE SEC v1.3 Workbook 2018Document20 pagesJNCIE SEC v1.3 Workbook 2018Chris Brown100% (1)
- ECSAv4-LPTv4 Instructor GuideDocument19 pagesECSAv4-LPTv4 Instructor GuideShanky Verma SoniNo ratings yet
- Ec Council Certified Security Analyst Ecsa v8Document5 pagesEc Council Certified Security Analyst Ecsa v8Junaid HabibullahaNo ratings yet
- Ec Council Certified Security Analyst Ecsa v8Document5 pagesEc Council Certified Security Analyst Ecsa v8Junaid HabibullahaNo ratings yet
- 5G, 4G, Vonr Premium Program Complete Log Anaylsis + Python AutomaionDocument13 pages5G, 4G, Vonr Premium Program Complete Log Anaylsis + Python Automaionarvind yadav100% (1)
- Netwrk Security - Less PlanDocument19 pagesNetwrk Security - Less PlanPriyaLalNo ratings yet
- Course Number: Cosc377 Course Title: Credit Hours: Prerequisites: Course DescriptionDocument2 pagesCourse Number: Cosc377 Course Title: Credit Hours: Prerequisites: Course DescriptionSamNo ratings yet
- EC-Council CSA PDFDocument4 pagesEC-Council CSA PDFAnkit RohatgiNo ratings yet
- Cyber Security Course in Kerala - C - PENT - Blitz AcademyDocument9 pagesCyber Security Course in Kerala - C - PENT - Blitz Academyamallblitz0No ratings yet
- JNTU Anantapur M.tech Syllabus For Embedded Systems 2009 10Document19 pagesJNTU Anantapur M.tech Syllabus For Embedded Systems 2009 10RajeshNo ratings yet
- Cyber Security and ApplicationsDocument4 pagesCyber Security and ApplicationsVasuki RajkumarNo ratings yet
- Certified Ethical Hacker ProgramsDocument18 pagesCertified Ethical Hacker ProgramsJacques BeaubrunNo ratings yet
- Cyber SecurityDocument11 pagesCyber SecurityGM RajputNo ratings yet
- CSC342 - Network SecurityDocument3 pagesCSC342 - Network SecurityDilawarNo ratings yet
- IS FileDocument67 pagesIS FileDisha BhardwajNo ratings yet
- IT 06 Certificate in Cyber SecurityDocument58 pagesIT 06 Certificate in Cyber SecurityshoaibbhattiNo ratings yet
- HCP Networking Level-1, CONTENTDocument4 pagesHCP Networking Level-1, CONTENTSharukh KhanNo ratings yet
- Infra PentestingDocument13 pagesInfra Pentestingimrankhan78631No ratings yet
- Learning Services Securing Cisco Networks With Sourcefire Intrusion Prevention SystemDocument5 pagesLearning Services Securing Cisco Networks With Sourcefire Intrusion Prevention Systemdexterroot0% (1)
- Internet Security and FirewallDocument23 pagesInternet Security and FirewallchakarpinilNo ratings yet
- PEM FCristian 30441Document4 pagesPEM FCristian 30441farcaspptNo ratings yet
- Iintroduction To Penetration TestingDocument56 pagesIintroduction To Penetration TestingkikeNo ratings yet
- Penetration TestingDocument19 pagesPenetration TestingAkiNiHandiongNo ratings yet
- Sem-6 Syllabus Information Technology (Mumbai University)Document13 pagesSem-6 Syllabus Information Technology (Mumbai University)Ashish LambaNo ratings yet
- Computer and Information Security HandbookFrom EverandComputer and Information Security HandbookRating: 2.5 out of 5 stars2.5/5 (4)
- Plant Intelligent Automation and Digital Transformation: Volume I: Process and Factory AutomationFrom EverandPlant Intelligent Automation and Digital Transformation: Volume I: Process and Factory AutomationNo ratings yet
- Ciros Studio Manual 1Document154 pagesCiros Studio Manual 1Samuel Sanchez100% (1)
- ToshibaStorageDiagnosticTool Manual V03 ENG EU 0228Document20 pagesToshibaStorageDiagnosticTool Manual V03 ENG EU 0228anamaya7No ratings yet
- Operating System Security - Paul Hopkins, CGIDocument8 pagesOperating System Security - Paul Hopkins, CGISidharth MalhotraNo ratings yet
- Datastage Interview Questions - Answers - 0516Document29 pagesDatastage Interview Questions - Answers - 0516rachitNo ratings yet
- Air Canvas SynopsisDocument23 pagesAir Canvas SynopsisRahul RajNo ratings yet
- Spesifikasi ACER Travelmate P2-P245Document12 pagesSpesifikasi ACER Travelmate P2-P245Sebastian Fykri AlmuktiNo ratings yet
- D1 - Building Next-Gen Security Analysis Tools With Qiling Framework - Kai Jern Lau & Simone Berni PDFDocument46 pagesD1 - Building Next-Gen Security Analysis Tools With Qiling Framework - Kai Jern Lau & Simone Berni PDFmomoomozNo ratings yet
- Examveda ComputerDocument112 pagesExamveda ComputerSarfraz AhmadNo ratings yet
- Restaurant Reservation SystemDocument15 pagesRestaurant Reservation Systemgoogle lahatNo ratings yet
- Internet of Things A Comparative StudyDocument10 pagesInternet of Things A Comparative StudyِAl TuraihiNo ratings yet
- UtilityDocument275 pagesUtilityGustavo AguirreNo ratings yet
- 3 Level Authentication - TutorialsDuniyaDocument50 pages3 Level Authentication - TutorialsDuniyaMustapha Saidu TatiNo ratings yet
- Cloud Computing NotesDocument21 pagesCloud Computing NotesH117 Survase KrutikaNo ratings yet
- It Policy & Guidelines: Rajiv Gandhi UniversityDocument21 pagesIt Policy & Guidelines: Rajiv Gandhi UniversitykissvineetNo ratings yet
- 20687B ENU TrainerHandbook PDFDocument540 pages20687B ENU TrainerHandbook PDFRodolfo Jose Moncada AriasNo ratings yet
- A Review of Open-Source Discrete Event Simulation Software For Operations ResearchDocument15 pagesA Review of Open-Source Discrete Event Simulation Software For Operations ResearchkhaledNo ratings yet
- Course Outline: School: DepartmentDocument6 pagesCourse Outline: School: DepartmentQifang MaNo ratings yet
- Aegis Padlock DT ManualDocument21 pagesAegis Padlock DT ManualmmarrioNo ratings yet
- FreePascalSquareOne 08-06-2014Document202 pagesFreePascalSquareOne 08-06-2014Agung SusantoNo ratings yet
- Brief History of Java-LectureDocument10 pagesBrief History of Java-LectureMharbse EdzaNo ratings yet
- Apple Platform Security GuideDocument219 pagesApple Platform Security GuideНикита МудрыйNo ratings yet
- MCAScheme Syllabus I IV 22 08 2017Document88 pagesMCAScheme Syllabus I IV 22 08 2017poornasandur18No ratings yet
- Introduction To LinuxDocument26 pagesIntroduction To LinuxBINJADNo ratings yet
- RegextDocument175 pagesRegextManpreet SinghNo ratings yet
- MKTG InstallAdminDocument216 pagesMKTG InstallAdminrammohansiebelNo ratings yet
- Unix MaterialDocument34 pagesUnix MaterialashibekNo ratings yet
- Atos White Paper Mainframes in PerspectiveDocument24 pagesAtos White Paper Mainframes in Perspectiveajman_loverNo ratings yet
- 1.0 Bitrix24 Service - Train1Document288 pages1.0 Bitrix24 Service - Train1Kenn O NdireNo ratings yet
- Pickit Linux Manual UbuntuDocument17 pagesPickit Linux Manual Ubuntukz300No ratings yet
- Cloud Lab ManualDocument61 pagesCloud Lab ManualSathishk1982No ratings yet